Need help solving [Display] Answer: (num) Ounces is (num) grams Choice #5 should end right after choosing the "5. Exit - Do nothing (default) and not ask for "Please enter the value to be converted:" Here is my Code, Please follow and add what is needed to It does not give the ending value answers of 1-4
Need help solving [Display] Answer: (num) Ounces is (num) grams Choice #5 should end right after choosing the "5. Exit - Do nothing (default) and not ask for "Please enter the value to be converted:" Here is my Code, Please follow and add what is needed to It does not give the ending value answers of 1-4
Chapter5: Making Decisions
Section: Chapter Questions
Problem 1GZ
Related questions
Question
Need help solving
[Display] Answer: (num) Ounces is (num) grams
Choice #5 should end right after choosing the "5. Exit - Do nothing (default)
and not ask for "Please enter the value to be converted:"
Here is my Code, Please follow and add what is needed to
It does not give the ending value answers of 1-4
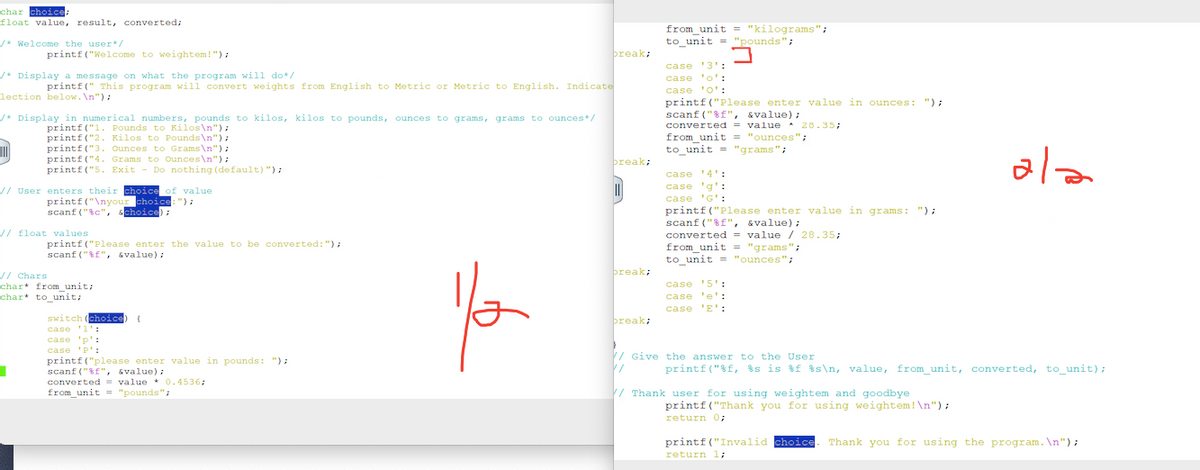
Transcribed Image Text:char choice;
float value, result, converted;
/* Welcome the user*/
printf("Welcome to weightem!");
/* Display a message on what the program will do*/
printf(" This program will convert weights from English to Metric or Metric to English. Indicate
lection below. \n");
/* Display in numerical numbers, pounds to kilos, kilos to pounds, ounces to grams, grams to ounces*/
printf("1. Pounds to Kilos\n");
printf("2. Kilos to Pounds\n");
III
printf("3. Ounces to Grams\n");
printf("4. Grams to Ounces\n");
printf("5. Exit - Do nothing (default) ");
// User enters their choice of value
printf("\nyour choice: ");
scanf("%c", schoice);
// float values
■
printf("Please enter the value to be converted: ");
scanf("%f", &value);
// Chars
char* from_unit;
char* to unit;
switch (choice) (
case '1':
case 'p':
case 'p':
printf("please enter value in pounds: ");
scanf("%f", &value);
converted
value
0.4536;
from_unit = "pounds";
break;
You
break;
||||
break;
break;
from_unit = "kilograms";
to unit "pounds";
J
case '3':
case 'o':
case '0':
printf("Please enter value in ounces: ");
scanf("%f", &value);
converted = value * 28.35;
from_unit = "ounces";
to_unit "grams";
case '4':
case 'g':
case 'G':
printf("Please enter value in grams: ");
scanf("%f", &value);
converted = value / 28.35;
from_unit = "grams";
to_unit = "ounces";
case '5':
case 'e':
case 'E':
// Give the answer to the User
1/
printf("%f, %s is %f %s\n, value, from_unit, converted, to_unit);
// Thank user for using weightem and goodbye
ala
printf("Thank you for using weightem! \n");
return 0;
printf("Invalid choice Thank you for using the program. \n");
return 1;
![s158a12@cisweb:~/p02/ex1
3. Ounces to Grams
4. Grams to Ounces
5. Exit
Do nothing (default)
your choice: 5
Please enter the value to be converted: 4
Thank you for using weightem!
[s158a12@cisweb ex1]$ gcc weightem.c
[s158a12@cisweb ex1]$ a.out weightem.c
0
Welcome to weightem! This program will convert weights from Engli
to Metric or Metric to English. Indicate which conversaion from
e selection below.
1. Pounds to Kilos
2. Kilos to Pounds
3. Ounces to Grams
4. Grams to Ounces
5. Exit
your choice: 3
Do nothing (default)
Please enter the value to be converted: 5.25
Please enter value in ounces: Should display "Answer 5.25 ounces
148.83 grams"
PRO MANAGE
Bhaiy
Welcome to weightem! This program will convert weights from Eng
e selection below.
1. Pounds to Kilos
2. Kilos to Pounds
3. Ounces to Grams
4. Grams to Ounces
5. Exit - Do nothing (default)
your choice: 5
Please enter the value to be converted:4
Thank you for using weightem!
Welcome to weightem. The program will convert weights from English to Metric or Metric to
English. Indicate which conversion from the selection below.
1. Pounds to Kilos
2. Kilos to Pounds
Ounces to Grams.
3.
4. Grams to Ounces
5. Exit - Do nothing (default)
Your choice: 3 User entered value is 3
Enter the number of ounces to convert: 5.25 User entered value is 5.25
Answer: 5.25 ounces is 148.83 grams
Thank you for using weightem. Bye!
← Make sure to use the correct conversion and labels](/v2/_next/image?url=https%3A%2F%2Fcontent.bartleby.com%2Fqna-images%2Fquestion%2Fbdec1793-1941-41c5-8d1b-173e4483cc10%2Faefe6867-a463-4393-80a8-f7ca40f795eb%2Fpmkezs_processed.png&w=3840&q=75)
Transcribed Image Text:s158a12@cisweb:~/p02/ex1
3. Ounces to Grams
4. Grams to Ounces
5. Exit
Do nothing (default)
your choice: 5
Please enter the value to be converted: 4
Thank you for using weightem!
[s158a12@cisweb ex1]$ gcc weightem.c
[s158a12@cisweb ex1]$ a.out weightem.c
0
Welcome to weightem! This program will convert weights from Engli
to Metric or Metric to English. Indicate which conversaion from
e selection below.
1. Pounds to Kilos
2. Kilos to Pounds
3. Ounces to Grams
4. Grams to Ounces
5. Exit
your choice: 3
Do nothing (default)
Please enter the value to be converted: 5.25
Please enter value in ounces: Should display "Answer 5.25 ounces
148.83 grams"
PRO MANAGE
Bhaiy
Welcome to weightem! This program will convert weights from Eng
e selection below.
1. Pounds to Kilos
2. Kilos to Pounds
3. Ounces to Grams
4. Grams to Ounces
5. Exit - Do nothing (default)
your choice: 5
Please enter the value to be converted:4
Thank you for using weightem!
Welcome to weightem. The program will convert weights from English to Metric or Metric to
English. Indicate which conversion from the selection below.
1. Pounds to Kilos
2. Kilos to Pounds
Ounces to Grams.
3.
4. Grams to Ounces
5. Exit - Do nothing (default)
Your choice: 3 User entered value is 3
Enter the number of ounces to convert: 5.25 User entered value is 5.25
Answer: 5.25 ounces is 148.83 grams
Thank you for using weightem. Bye!
← Make sure to use the correct conversion and labels
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 4 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

Programming with Microsoft Visual Basic 2017
Computer Science
ISBN:
9781337102124
Author:
Diane Zak
Publisher:
Cengage Learning

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

Programming with Microsoft Visual Basic 2017
Computer Science
ISBN:
9781337102124
Author:
Diane Zak
Publisher:
Cengage Learning

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,