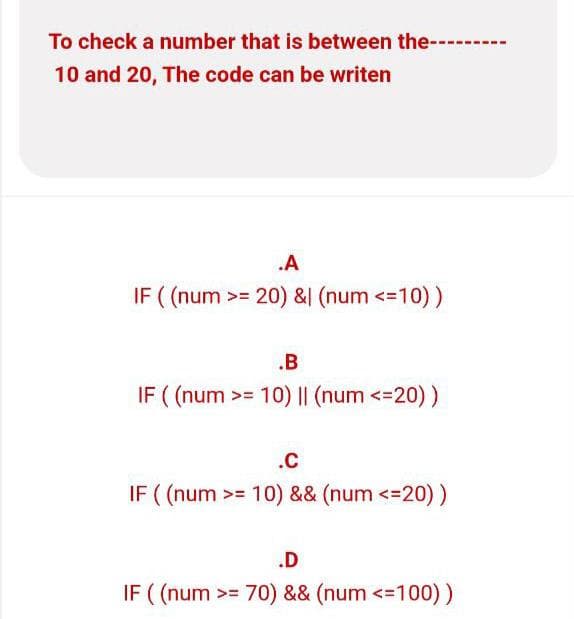
o check a number that is between the------ 0 and 20, The code can be writen
Q: How can we avoid a central processing unit from wasting processing cycles by processing a high…
A: Intro Because of the large number of instructions that are processed by the CPU, there are instances…
Q: IWrite classes based on your smart home simulator design. In methods, just print out something.…
A: Program: class Gettersetter:def __init__(self, age = 0):self._age = age# getter methoddef…
Q: What are the different sorts of transmissions, and can you give an example of each?
A: Introduction: The following are the many modes of transmission: Transmission mediums are classified…
Q: When establishing and managing web applications, what factors should be taken into account?
A: Factors to establish and manage web applications.
Q: What kinds of consequences may an organisation suffer if its cyber security is compromised?
A: Introduction: An information break happens when delicate data that has been put away on a further…
Q: Please show steps on how achieve answer
A: 1 gigabit per second = 2^30 bit 1 megabit = 2^20 bit To convert megabyte to gigabit: 1 gigabit =…
Q: the system that may be used in video games to improve the lighting and shadow effects by mimicking…
A: It is defined as a technique that helps make games more realistic, as it better emulates the way…
Q: What does the term "Hybrid Approach" mean in the context of data warehouses?
A: Introduction A data warehouse is a sort of data management system that is intended to facilitate and…
Q: Why, in your opinion, is requirements discovery required for a system in development? Give an…
A: Introduction: It is imperative that the significance of requirements discovery for a system that is…
Q: Provide three instances of WiFi network vulnerabilities. Determine the kind of attack that might be…
A: There are three possible security issues in Wi-Fi networks: 1) Configuration Issues: Many…
Q: Computer Science Question
A: Using Struct we can solve his problem
Q: Make clear what the back button is for and how it relates to the stack of information at the bottom.
A: Back stack is nothing but a stack used to store various tasks in the memory as per the window open…
Q: Make a distinction between wireless networking issues that might occur when two stations are visible…
A: the hidden node problem or hidden terminal problem In wireless networking, the hidden node issue…
Q: ake up this
A: Distinction between "computer architecture" and "computer organization" has become very fuzzy, if…
Q: Describe why you think a web server is the best solution to use
A: Web server: A description of a web server may be considered the final system. The ultimate system…
Q: When using solid modelling, the designer may shape the thing by moulding and moulding it instead of…
A: Intro The solid modelling approach gives the designer the ability to mold and form an item rather…
Q: How closely are the concepts of object-oriented programming and abstract data types interrelated?…
A: Disagreement on a Contract: Students should remember that understanding is an important underlying…
Q: What potential risks could a server database migration project have?
A: Introduction: Migrations to the cloud come with a number of potential negatives in general that you…
Q: The use of forensic software by investigators is intended to aid them in finding evidence; but, what…
A: Investigators can learn information about computer users, locate deleted data, rebuild artefacts,…
Q: A) Write program in C++ to solve the equation y = [ (x^2 + x + 1) when x values increased 0.2 from…
A: 5 A. Code: #include <iostream>using namespace std;int main() { float x=1.8,y=0; do{…
Q: What happens when people participate in illegal actions online, and how such activities are carried…
A: Introduction: Computers and networks are used in cybercrime. It's possible that a crime was carried…
Q: In order to prevent squandering calculation cycles, a computer processor has to devise a strategy to…
A: Inspection: Practically all projects need them to swap out a CPU calculation and waiting pattern for…
Q: Because rasterizing reduces the visual quality of the output, why do we talk about it?
A: Definition: A vector graphics-based picture is rasterized when it is converted into a raster image.…
Q: Describe the predictive analytics method and offer an example of how it is applied in practise.
A: Intro Predictive analytics is the process of using using the data analytics to make the data…
Q: What is the most important aspect of a data warehouse, and why is it known as MetaData?
A: Introduction: Metadata is data about data or documentation about data that consumers want. Metadata…
Q: Uses of surrogate keys in a data warehouse or data mart are described below.
A: Data Warehouse is a relational database management system construct to meet the requirement of…
Q: Intranets make use of a wide range of Internet technologies, such as web browsers and servers,…
A: Introduction: The ideal match will include all of the intranet's technological resources.…
Q: Explain briefly the measures you would take to secure the organization's network against cyber…
A: The answer is given in the below step
Q: The basic objective of software engineering, if it were to be condensed, how would it look? What led…
A: Answer: Software configuration refers to the process of describing the architecture, components,…
Q: create c# Payroll System (Application of Polymorphism)
A: using System; using System.Text; namespace PayRollSystemManagement { public abstract class…
Q: When it comes to advancing information technology, networking is essential.
A: Let us see the answer below,
Q: What lessons can we draw from cybercrime in terms of counsel and conclusions?
A: Introduction: Cybercrime, often known as computer crime, refers to the act of conducting criminal…
Q: Alternately, would you be able to provide a more comprehensive summary of the metrics that are…
A: As a result: Could you perhaps provide a more detailed description of the metrics used in the…
Q: To round (B) towards minus infinity the function used is roundn(A) O fix (A) O floor(A) O ceil(A) O…
A: The correct answer is :c (floor(A))
Q: Exercise #2: Using for staement. Write a C++ program to find and print the sum of values greater…
A: #include <iostream> using namespace std; int main(){ int arr[100]; int k, size, sum = 0,…
Q: What hardware techniques must be used in order for virtual memory systems to be efficient? Who or…
A: Given: An operating system function called virtual memory enables a computer to make up for a lack…
Q: To check the number is nagative, the-- code can be writen .A if (num == 0) .B if (num > 0) .C if…
A: import java.util.Scanner;public class Main{ public static void main(String[] args) { Scanner sc=new…
Q: Describe two lifelines you can use to get Office 365 tips, help, and support for this discussion…
A: Answer: Microsoft 365, previously Office 365, is a line of membership administrations presented by…
Q: In this aspect, how does the agile methodology vary from a typical SDLC
A: Introduction In agile methodology, we are constantly uncertain and aware of our assumptions (as a…
Q: A system has 1 CPU-bound process and 17 10- bound processes. If the 10-bound processes request an…
A:
Q: What are the most significant differences between the Internet and traditional telephone systems?
A: Given: The telephone network is designed to reliably provide voice connections between two known…
Q: What is Star Topology? What is the drawback of it?
A: Each device is connected to a central hub in a network structure called a star topology, sometimes…
Q: What exactly is meant when we discuss 4G or 5G networks in the context of telecommunications is…
A: Introduction: 5G refers to the fifth generation of mobile networks.
Q: Which of the following would correctly declare and instantiate an array of 5 ints O int[] values =…
A: A array is an assortment of things put away at bordering memory areas. The thought is to store…
Q: True/False Changing the div CSS selector width to 30% makes the resize when the browser width is…
A: Option True is correct choice Use the CSS max-width Essentially use the CSS max-width property to…
Q: There isn't a clue in our brains as to how operating systems work. What does the term "operating…
A: system of operation A computer's user and its hardware are connected through an operating system…
Q: What are the various database MDM techniques? Mobile Device Management (MDM).
A: Intro Mobile Device Management (MDM) is the method of developing corporate data security by…
Q: Python Programming How to delete multiple elements in list? Example: list = [1, 2, 3, 4, 5, 6,…
A: The python code for deleting the multiple element from the list is given below..
Q: Create a program in C++ that accepts sales for the week ( Monday - Friday ) and display the highest…
A: C++ Program: #include <iostream>using namespace std; // function for lowest Salesfloat…
Q: Java
A: Introduction Java is a kind of programming language that is an oriented object-based language that…
Control structures
Control structures are block of statements that analyze the value of variables and determine the flow of execution based on those values. When a program is running, the CPU executes the code line by line. After sometime, the program reaches the point where it has to make a decision on whether it has to go to another part of the code or repeat execution of certain part of the code. These results affect the flow of the program's code and these are called control structures.
Switch Statement
The switch statement is a key feature that is used by the programmers a lot in the world of programming and coding, as well as in information technology in general. The switch statement is a selection control mechanism that allows the variable value to change the order of the individual statements in the software execution via search.
Step by step
Solved in 3 steps with 1 images

- java c++ here is my question (Evaluate expression) Modify Listing 20.12, EvaluateExpression.java, to add operators ^ for exponent and % for remainder. For example, 3 ^ 2 is 9 and 3 % 2 is 1. The ^ operator has the highest precedence and the % operator has the same precedence as the * and / operators. Your program should prompt the user to enter an expression. Here is a sample run of the program Enter an expression: (5 * 2 ^ 3 + 2 * 3 % 2) * 4(5 * 2 ^ 3 + 2 * 3 % 2) * 4 = 160Nice Number Programming: Nice program ask user to enter three integers from keyboard (java console), the three integers represent left bound, right bound and arbitrary digit 'm', where left bound is less than right bound. Program should print all nice numbers in the given range that doesn't contain digit 'm'. The number is nice if its every digit is larger than the sum of digits which are on the right side of that digit. For example 741 is a nice number since 4> 1, and 7> 4+1. with digit m=2. Write a complete program in Java that Call only One method (niceNumbers method) that will print all nice numbers excluding a given digit 'm' that also entered by user?C Programming Write a program that reads an integer from the user (keyboard), namely n. Yourprogram should print all positive numbers that are smaller than n and whosedigits sum up to a perfect square number.(An integer is a perfect square if it hasan integer square-root for example 25) You should print the numbers in ascendingorder and print their digits separated by “:“ symbol from the least significant digitto the most significant digit on the same line as the number. At the end of eachline you should also print the sum of the digits of the number. Example:If the user enters n : 30, then the output should be as follows:1 1 14 4 49 9 910 0:1 113 3:1 418 8:1 922 2:2 427 7:2 9
- Number guessing Game Write a C program that implements the “guess my number” game. The computer chooses a random number using the following random generator function srand(time(NULL)); int r = rand() % 100 + 1; that creates a random number between 1 and 100 and puts it in the variable r. (Note that you have to include <time.h>) Then it asks the user to make a guess. Each time the user makes a guess, the program tells the user if the entered number is larger or smaller than its number. The user then keeps guessing till he/she finds the number. If the user doesn’t find the number after 10 guesses, a proper game over message will be shown and the actual guess is revealed. If the user makes a correct guess in its allowed 10 guesses, then a proper message will be shown and the number of guesses the user made to get the correct answer is also printed. After each correct guess or game over, the user decides to play again or quit and based on the user choice, the computer will make…TotalPayAA.java Write a program that will calculate an employee’s total pay for a week (hourly pay + commission). Your program should ask the user how many hours they work and then their total sales amount. Hourly Wage - Their hourly wage is $11.50 for the first 40 hours and then time-and-a-half ($11.50 * 1.5) for anything over 40 hours. Commission - Commission is a small percentage of total sales that the employee earns. Total Pay – Total hourly wages + commission Commission for sales is shown: Sales Commission $0.00 - $99.99 5% of total sales $100.00-$299.99 10% of total sales $300.00+ 15% of total sales Make sure you print back to the user their total pay for the week. Money values should be formatted appropriately and your output should be descriptive as in the example. Test values: 10 hours + $10 sales =…Write a code snippet that can arrange the alphabets of a name entered by user in alternate cases .Note: Ignore white spaces . Implement this code in C language. Input string: Timothy Olyphant Output string: TiMoThY OLyPhAnT Input string: Olga Kurylenko Output string: OlGa KuRyLeNkO
- A Palindromic prime is a prime number that is also a palindromic number. Write a C++ program that displays all the palindromic prime numbers between 100 and 999 without using pointers.For example: These are 14 palindromic prime numbers smaller than 500:2,3,5,7,11,101,131,151,181,191,313,353,373,383.-scripting language Write a program that randomly generates a lottery between 100 and 999 (random.randint(100, 999)), prompts the user to enter a number in the same range, and determines whether the user wins according to the following rule: (1) If the user input matches the lottery in exact order, print "the award is $10,000". E.g., lottery = 123, input = 123(2) If the user input matches the lottery, but in wrong order, print "the award is $6,000". E.g., lottery = 123, input = 321(3) If two digits in the user input matches a digit in the lottery, print "the award is $3,000". E.g., lottery = 123, input = 612(4) If one digit in the user input matches a digit in the lottery, print "the award is $1,000". E.g., lottery = 123, input = 289(5) If none of the digits is matched, print "thank you".Write a program in c++ to generate a random number between 1 - 100, and then display which quartile the number falls in. First quartile is 1 - 25 Second quartile is 26 - 50 Third quartile is 51 - 75 Fourth quartile is 76 - 100 The following program shows how to get a random integer between 1 - 100. Use the code as an example for your own program. SAMPLE PROGRAM// This program displays a random number between 1 - 100#include <iostream> // for input and output#include <cstdlib> // for rand() and srand()#include <ctime> // for time()using namespace std;int main(){ //constantsconst int MIN_VALUE = 1;const int MAX_VALUE = 100;//get system time and seed random number generatorunsigned seed = time(0);srand(seed);//get random number between 1 - 100int num = (rand() % (MAX_VALUE - MIN_VALUE + 1)) + MIN_VALUE;cout << num << endl;return 0;} Your program should: contain header comments as shown in class display a "hello" message generate a random number…
- Using C Language: Write a program that consists of 2 guessing game. The first game: It is a guessing game in which the computer picks a specific number from 1 to 10, then the user guesses the number chosen by the computer and has ten attempts, and in each attempt the chosen number by the computer changes. The second game: A guessing game. The computer also chooses a three-digit number, for example: 950 and you have ten attempts to predict the number chosen by the computer. For example, the user types 390, the computer will tell him that the first digit is wrong, the second digit is correct, but it is not in the correct location, and the last digit, which is 0, is correct. And the user makes repeated attempts to find the correct whole numberA prime number is called a Mersenne prime if it can be writtenin the form 2p - 1 for some positive integer p. Write a program that findsall Mersenne primes with p ≤100 and displays the output as shown below.(Hint: You have to use BigInteger to store the number because it is too big tobe stored in long. Your program may take several hours to run.) p 2^p – 1---------------------2 33 75 31...ample code for the reader-writer: #include <pthread.h>#include <semaphore.h>#include <stdio.h> /*This program provides a possible solution for first readers writers problem using mutex and semaphore.I have used 10 readers and 5 producers to demonstrate the solution. You can always play with these values.*/ sem_t wrt;pthread_mutex_t mutex;int cnt = 1;int numreader = 0; void *writer(void *wno){ sem_wait(&wrt);cnt = cnt*2;printf("Writer %d modified cnt to %d\n",(*((int *)wno)),cnt);sem_post(&wrt); }void *reader(void *rno){ // Reader acquire the lock before modifying numreaderpthread_mutex_lock(&mutex);numreader++;if(numreader == 1) {sem_wait(&wrt); // If this id the first reader, then it will block the writer}pthread_mutex_unlock(&mutex);// Reading Sectionprintf("Reader %d: read cnt as %d\n",*((int *)rno),cnt); // Reader acquire the lock before modifying numreaderpthread_mutex_lock(&mutex);numreader--;if(numreader == 0) {sem_post(&wrt); //…



