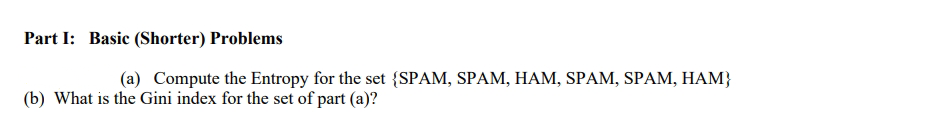
Part I: Basic (Shorter) Problems (a) Compute the Entropy for the set {SPAM, SPAM, HAM, SPAM, SPAM, HAM} (b) What is the Gini index for the set of part (a)?
Q: Explain three frequent issues with concurrent transaction execution and how concurrency control may ...
A: Introduction Explain three frequent issues with concurrent transaction execution and how concurren...
Q: You might be wondering why you'd want to utilise a return statement in a void function.
A: Introduction: You might be wondering why you'd want to utilise a return statement in a void function...
Q: A zero-memory source contains four symbols X = {x1,x2, X3, X4} and their 1 1 4'8'8) probabilities ar...
A: Given symbols are X={x1,X2,X3,x4} Probabilities are P(X) ={1/2,1/4,1/8,1/8}.
Q: 4. computes the standard deviation of numbers. This exercise uses a different but equivalent formula...
A: # Compute the standard deviation of values def deviation(x): sum = 0 for i in range(len(x)): ...
Q: int i; for (i=0;i=2){ GPIOD_ODR &=~(1<<(i-2)); } } At each iteration what is LEDS that will be on fr...
A: According to the question, we have to explain that at each iteration which LED will be ON. In Step 2...
Q: The Turing Machine below starts with the input 1111 with the head on the left most 1. What will be i...
A: According to the question we need to provide solution for:
Q: Nenu: [1] Palindrone [2] Largest Prime You've selected:
A: In this question we are asked to create a program with menu of two choices In 1st choice, user has t...
Q: 8.4 Assume that 10,000 nodes per second can be generated in a breadth-first search. Suppose also tha...
A: A blind search (also called an uninformed search) is a search that has no information about its doma...
Q: 1. Big-O has the highest growth rate. a. 0(2") b. O(n³) c. O(n*) d. O(n°)
A: The answer is
Q: When using public key cryptography, what is the minimal number of keys required?
A: Introduction: In the case of public-key encryption, a pair of keys is employed.
Q: Using a 2x1 MUX and other gates and MSI components of your choice, design a device with the followin...
A: ans is given below
Q: Protocols that function on networks can be classified in a variety of ways.
A: Types of network protocols There are three main types of network protocols, which include network ma...
Q: to be placed to prevent the race condition(s). Could we replace the integer variable: int number_of...
A: given - Consider the code example for allocating and releasing processes shown. Identify the race ...
Q: Write a Java Program to take an int n from the user & print the absolute difference between n and 51...
A: absolute value of the difference of two numbers. 51 is one number and n is another number.
Q: Determine the most important contrast between Internet access and phone service.
A: Introduction: There is a distinction to be made between Internet access and phone service.
Q: Item Counter Assume that a file containing a series of names (as strings) is named names.dat and ex...
A: I give the code in Python as per your requirement along with output and code screenshot
Q: What information is included in a computer printout, and what automated procedures are used?
A: Let us see the answer:- Introduction Explanation for first part:- A document that is printed from a ...
Q: Write a Java program to take an array of ints, print the number of 9's in that array.
A: Step 1 : Start Step 2 : In the main method declare an array of integers with size = 10. Step 3 : Dec...
Q: Make brief notes on a) the World Wide Web
A: Introduction: Tim Berners-Lee is credited with developing the World Wide Web while working at CERN i...
Q: following expresion into Postfix exprensia, 12+L÷344+(10+9) 3 1. covert
A: Find the answer with calculation given as below :
Q: The Turing Machine Below starts with the input 1010 with the head on the left most 1. What will be i...
A: We need to answer for:
Q: MC1. You are asked to design a flashlight that will last at least eight hours without having to be r...
A: We need to answer:
Q: What segment register may not popped from the stack?
A: segment register may not popped from the stack
Q: 4) A red line on the top edge of the Timeline indicates that that portion of the Timeline needs to b...
A: 4) A red line on the top edge of the Timeline indicates that that portion of the Timeline needs to b...
Q: (RS + R)* RS = (RR*S)* true or false prove and explain
A: Here, we have to check whether given regular expressions are equivalent or not. Using basic regular ...
Q: What exactly is Static text?
A: Text that does not change size or location on the web page when the browser or viewport width change...
Q: Problem Statement: We are going to develop an information system for a vehicle-related business; hav...
A: Algorithm: Start Create a class named Vehicle with modelName, registratioNumber, owner as its attri...
Q: ting
A: NOTE: ACCORDING TO COMPANY POLICY WE CAN SOLVE ONLY 1 QUESTION. YOU CAN RESUBMIT THE QUESTION AGAIN ...
Q: Can you tell the difference between an oblique and an orthogonal projection? graphical design in com...
A: Intro A way of looking at it is that with an orthographic projection, the outlines of the projection...
Q: . Simplify the following Boolean functions, using four-variable Kmaps: (a) F (w, x, y, z) = Σ(1, 4, ...
A: for all three parts , I have provided HAND-WRITTEN solution images---------
Q: C++ Programming Lab Write a C++ program to take a string from the user, print a new string made of e...
A: #include <iostream>using namespace std; string test(string s) { string result...
Q: Discuss the concept of intents and how they are used in Android development. Make certain to highlig...
A: Introduction: Android software development is creating apps for devices that run the Android operati...
Q: Many individuals wait until it's too late to back up their data. They tend to modify their routines ...
A: Intro First of all, this is a nightmare for anyone. The data belonging to anyone contains sometimes ...
Q: What if there was no software engineering? What is the most crucial stage of software development? ...
A: Intro What if No Software engineering was there?We cannot solve every problem by using a computer th...
Q: A weak entity set may be turned to a strong entity set by adding the primary-key attributes of its i...
A: Introduction: Adding the major key characteristics of an identifying entity set to the attributes of...
Q: 13. Give data memory location assigned to PIN registers of Ports A-C for the ATmega32. 14. Give data...
A: The four ports of the AVR ATmega16 are made up of 32 pins. Following is a list of ports to visit: 1....
Q: Simplify the following Boolean expressions to a minimum number of literals: (a + b+ c')(a'b' + c) (a...
A:
Q: 1. How FLIP-FLOPS performed in HDL explain it in detail?
A: Introduction How FLIP-FLOPS performed in HDL explain it in detail?
Q: Write only the class declaration for the Car class. Do not write a main function, and do not write a...
A: *Write only the class declaration for the Car class. Do not write a main function, and do not write ...
Q: Define the circumstance when smart cards are required for authentication but magnetic stripe cards a...
A: Introduction: Data is saved via a tiny microchip implanted in a smart card, which is comparable in s...
Q: What exactly are sponsored links? Could they have an impact on the quality of your search results? H...
A: Intro Sponsored links and the way these links affect the quality of search results: Sponsored link...
Q: The Turing Machine below starts with the input 0101 with the head on the left most O. What will be i...
A:
Q: Users can interact with a telephone menu system by speaking instead of pressing buttons on the dial ...
A: Two arguments in support of speech recognition technology: Talking is faster than typing! Voice com...
Q: What is in the Program.cs file?
A: Intro Program.cs file Program.cs file is a static class file that contains only one static method....
Q: What are your thoughts on the necessity for several addressing modes in any given computer?
A: Intro Addressing modes Addressing modes can be considered as the way in which the operand of an inst...
Q: v) Write a Python program to input two strings s1 and s2 of lengths x1 and x2 respectively. Compute ...
A: Python program to solve the given problem is below.
Q: main.c 2. Capital - Small = ? by Jemar Jude Maranga Given a string that's guaranteed to only have al...
A: Find the required code in C given as below and output:
Q: The Database Administrator or Server Administrator is in charge of making backups of the databases.
A: Introduction: Backup is an essential operation that must be conducted on a regular basis, as we all ...
Q: Problem A Write a class FinancialAidApplicant which describes an applicant for financial aid and wil...
A: If-else if-ladder conditional statement in java program: The multiple if conditions are checked in t...
Q: Consider one dimensional studentsMark array and find maximum and minimum scorer by defining a functi...
A: I have provided C CODE along with CODE SCREENSHOT and OUTPUT SCREENSHOT------------
Step by step
Solved in 2 steps

- The set of letters S consists of 30 As, 6 Bs, 24 Cs, 15 Ds, and 15 Es. The set of letters T consists of 25 As, 20 Bs, 15 Cs, 5 Ds and 35 Es. What is the mutual index of coincidence between sets S and T? Leave your answer as a fraction in lowest termsMany forms of cryptography are based on the following discrete log problem. Choose a cyclic group G (produced by one generator g) with finitely many elements. Alice and Bob want to set up a secret communication and need a secret key for that, which becomes a group element from G. They set up the following exchange (the so-called Diffie-Hellman protocol): 1. Alice chooses a secret group element a and sends unsecured g^a to Bob 2.Bob chooses a secret group element b and sends unsecured g^b to Alice 3. Alice calculates (g^b )^a and keeps this group element secret 4.Bob calculates (g^a )^b and keeps this group element secret Since a cyclic group is abelian, Alice and Bob now share the secret key (g^b )^a=(g^a )^b. The blue group elements are publicly known, the red elements are secret. The discrete log problem presented to an eavesdropper is computing say a from the publicly known data G,g,g^a. The naming of the problem comes from the solution a= glog(ga ) which is generally difficult to…Why does PGP generate a signature before applying compression? How does PGP use the concept of trust? Consider a Diffie-Hellman scheme with a common prime q = 11 and a primitive root α = 2. Show that 2 is a primitive root of 11. If user A has public key YA = 9, what is A’s private key XA? If user B has public key YB = 3, what is the secret key K shared with A?
- Consider a Diffie-Hellman scheme with a common prime q = 17 and a primitive root α = 3. a) If user A has a private key XA=4, what is A’s public key, YA? b) A sends YA to B. If B has a private key XB=6, what is the shared secret key, K that B can calculate and share with A? c) If B computes YB and sends it to A, what is the shared secret Key, K computed by A?Suppose you and your friend would like to use Diffie-Hellman key exchange system to exchange a keyword. Both of you have decided to use the following p = 4138327577, q = 3742197127.If you decide b = 1767005, and your friend has picked a number a that you don’t know. But you havereceived q a mod p from your friend, and the number is 980246808. Find out the common shared key.Consider a Diffie-Hellman scheme with a common prime q = 23 and a generator g = 5. Bob has public key PUB(B) = 8, what is the shared secret key K?
- Discuss the trade-off between fairness and throughput of operations in the readers-writers problem. Propose a method for solving the readers-writers problem without causing starvation.Suppose (X[mX]+Y [mY ]) > 0. What can you infer about each of the four subproblems (namely, (X1, Y1), (X1, Y2), (X2, Y1), and (X2, Y2))? Clearly identify the ones that do not have to solved anymore, and those that still have to be solved. Briefly justify.Consider a Diffie-Hellman scheme with a common prime q = 11 and a primitive root α = 2. Show that 2 is a primitive root of 11. If user A has public key YA = 9, what is A’s private key XA? If user B has public key YB = 3, what is the secret key K shared with A?
- 29. Banker's algorithm deals with a. deadlock prevention b. deadlock avoidance c. deadlock recovery d. mutual exclusion7. For each of the following relations on the set of all real numbers, determine whether it isreflexive, symmetric, antisymmetric, transitive. Here xRy if and only if:(a) x + 2y = 0 (b) x = 2y(c) x − y is a rational number (d) xy = 0(e) xy ≥ 0 (f) x = 1 or y = 1 (f) x = 1 or y = 1(g)x is a multiple of y (h) xy = 1 PS:Please help me by doing all the subparts as it is connected correctly on a word processing document.Is (p ∨ ¨q) ⊕ ¨ (q ∧ p) a tautology, contradiction or contingency?

