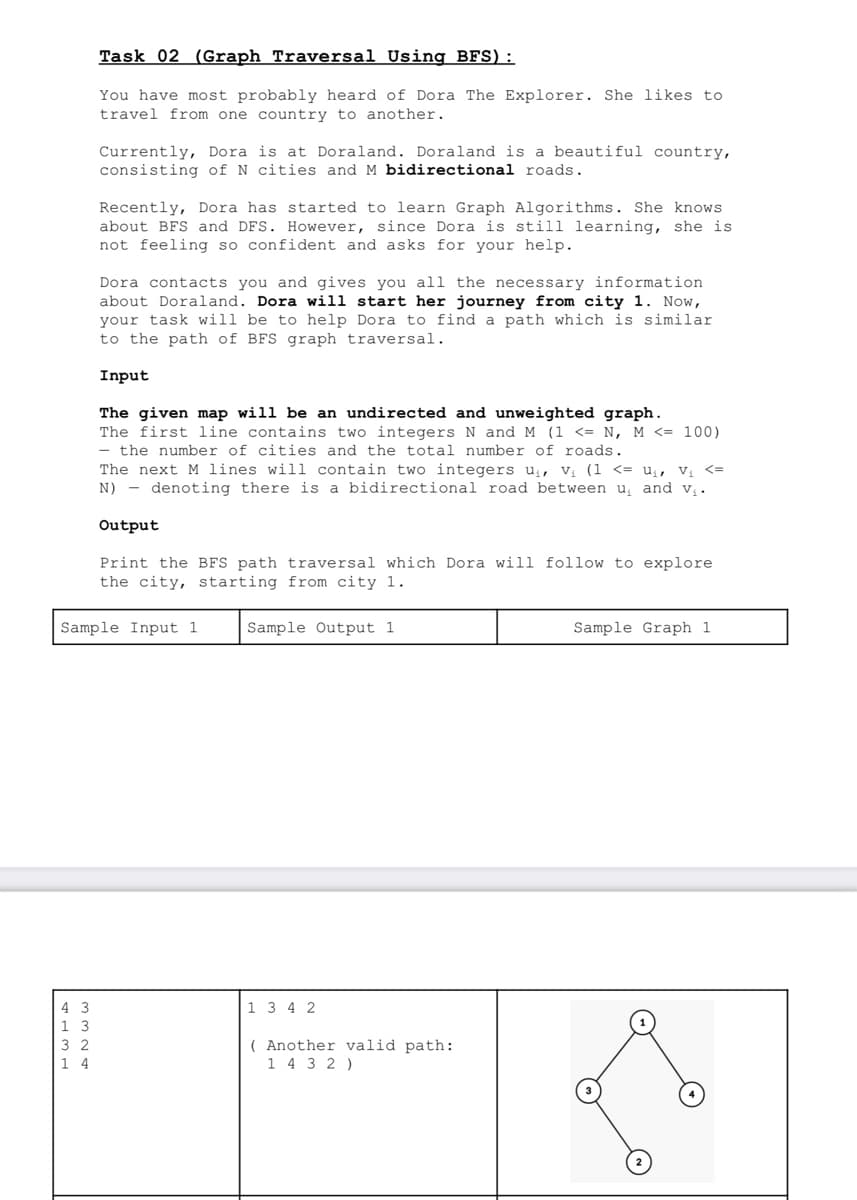
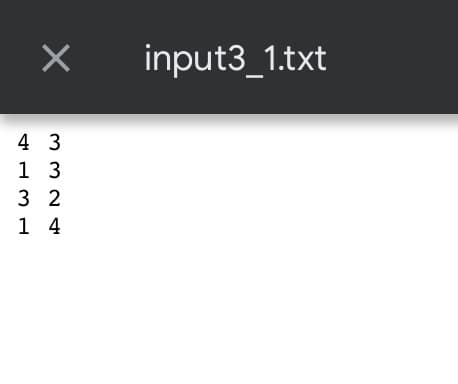
Please use python and python file i/o to solve the problem. Create an input file input3_1.txt as shown below, solve the problem and print the output to output3_1.txt file as shown in the question.
Q: Why does hashing passwords beat encryption?
A: File encryption, which encrypts individual files or file systems with a unique key and limits access…
Q: Expand on the definition and workings of a challenge-response authentication system. Why this…
A: Challenge–response system Often, password-based authentication is employed in client-server systems.…
Q: Header-based vulnerabilities? Three examples?
A: It is also possible to perform high-impact, routing-based SSRF attacks using the Host header. Host…
Q: Evaluate cloud security security risks and advantages. Moving to the cloud is risky and complicated.
A: Cloud security is defined as the collection of procedures and technologies designed to address…
Q: Do you have more information on the CSRF attack?
A: INTRODUCTION: An exploit known as Cross-Site Request Forgery (CSRF) compels authenticated users to…
Q: Interrupt? Explain the various sorts of hardware interruptions in order to demonstrate why none are…
A: Predicting hardware failures by explaining the many types of hardware failures: A hardware interrupt…
Q: What is the purpose of the scientfic method to help with environmental issues?
A: The answer is given in the below step
Q: When do problems arise with the computer's hardware and software?
A: Introduction Computers are extremely complex machines that are prone to having issues with both…
Q: How does Model-View-Controller (MVC) fit into online application development? How may an MVC…
A: Introduction: Model-View-Controller (MVC) is a software design pattern that separates an application…
Q: contains DNS entries, root servers, and iterated and non-iterated searches.
A: The internet's yellow pages are DNS. You used to locate a business' address in the Yellow Pages. DNS…
Q: What kind of effects does a data breach have on the overall security of the cloud? What potential…
A: Answer: Introduction Data breach can certainly affect the cloud security rules. cloud security is…
Q: Learn all there is to know about cloud computing and the related social networking blogs
A: The cloud computing model: Instagram, Facebook, and Tumblr are examples of blogs that give data or…
Q: What makes Interrupt stand apart from a regular interruption is its name. Explain why problems with…
A: Interrupts - Interrupts are basically generated by hardware during program execution. They can…
Q: Blogs about social networking and cloud computing are both major subjects that need your undivided…
A: Inspection: Learn as much as you can about social networking blogs and cloud computing. Using social…
Q: Using your knowledge of Python programming and assuming that the desired output is a 4-bit output F,…
A: To implement the given code in Python using adders, AND, OR, INV, and XOR gates, we need to perform…
Q: The OSI model contends that, with a few notable exceptions, most computer systems don't really need…
A: The OSI is the conceptual framework that outlines how network protocols and communication should…
Q: Do you want to learn more about social networking blogs in addition to cloud computing and other…
A: If you want to learn more about topics like cloud computing and social media, one way to do that is…
Q: What aspects of your job as a developer do you like appreciating the most? Explain the four extra…
A: Description: Metrics for software development are crucial for monitoring software projects'…
Q: Which of the following is NOT a reason to be against using static routing? O. More resources, such…
A: Static routing is a type of routing protocol used in computer networks, where the routing table is…
Q: In order to improve the robustness, performance, availability, and resilience of cloud-based…
A: If they have a device that can connect to the internet, users of cloud computing may access the…
Q: Compiles high-level programs into machine-language. Compilers impact CPU performance. What if so?…
A: The Processor processing time, also known as the CPI, is one metric that can be used to evaluate…
Q: In this day and age of machine learning, are data structures and algorithms considered to be…
A: Data structures and algorithms are heavily used in the era of Machine Learning and are thus not…
Q: Provide session hijacking examples. Such assaults demand strong defense.
A: Introduction: Session hijacking lets an attacker access authorised session connections. This is used…
Q: Using social networking sites and cloud computing may be quite beneficial if you want to better your…
A: Cloud computing is defined as the delivery of various services via the Internet including tools and…
Q: There are a number of things that are required for a virtual machine to work properly. Discuss the…
A: This particular question belongs to Computer Science and Engineering. Computer Science is an…
Q: Improve your knowledge of cloud computing, as well as other pertinent topics, in addition to social…
A: Here are some key points about cloud computing: 1) Definition: Cloud computing is the delivery of…
Q: Create a list of 10 organizations, both regional and national, that are active in the fields of…
A: Association for Computing Machinery (ACM): This organization is popular for its work in the…
Q: A more thorough understanding of the metrics related to the software development process would be…
A: Metrics related to the software development process are crucial for understanding and improving the…
Q: e Prototype Design Pattern and wha
A: The Prototype Design Pattern is a creational pattern in object-oriented programming that allows us…
Q: Contrast abstraction with computer science examples and compare outcomes. To define "abstraction,"…
A: Contrast abstraction with computer science examples and compare outcomes. To define "abstraction,"…
Q: Compiler's stages perform their main functions? Each step should be shown.
A: Introduction: A compiler is a computer program that converts high-level source code written in one…
Q: When keeping passwords in a file, why is hashing better than encryption? ..
A: When it comes to storing passwords in a file, hashing is generally considered to be a better option…
Q: When an organization attempts to transition to a platform that uses cloud computing, they often run…
A: Cloud transfers occur when a company moves all or part of its activities to the cloud. Cloud…
Q: ow would confidentiality, integrity, and availability relate to your bank's website?
A: Banks have a major effect on people's daily lives. A bank acts as a mediator between clients with…
Q: Describe the SETI experiment's usage of distributed computing in general.
A: The SETI (Search for Extraterrestrial Intelligence) experiment is a scientific initiative aimed at…
Q: mple of when one of the four possible access ed. What distinguishes this option from other
A: Introduction: Only the owner and controller of access control controls will have access to this.This…
Q: Study how each team member contributes to Scrum and Extreme Programming.
A: Extreme Programming (XP) is an agile paradigm for software program improvement that aims to provide…
Q: Wireless LAN specifications changed.
A: An analysis of the following aspects of network protocols: With the introduction of the IEEE 802.11…
Q: Postponing execution until one of the two processes finishes. Phase 1 is perhaps more essential than…
A: 1) Process and scheduling are two fundamental concepts in computer science and operating systems. 2)…
Q: Functions are the building blocks of computer programming.
A: One of the fundamental elements of programming is function, which is a collection of statements that…
Q: Infosec Compare these encryption products' CIA ratings (TrueCrypt - CrypTool - CryptoExpert lite).
A: The United States intelligence agency triad, often known as confidentiality, integrity, and…
Q: What was the intention of creating the Bevco.xls file?
A: Explanation: Microsoft created XLS, also known as Binary Exchange File Format, for use with…
Q: Learn more about cloud computing, social networking blogs, and other relevant subjects.
A: Below is the explanation of cloud computing, social networking, and blogs:
Q: Why are TCP Tahoe network configuration packet losses higher at the start of a transmission than…
A: Given that the TCP Tahoe configuration network is being utilized, why are packet losses at the start…
Q: Explain modern "two-tier" and "three-tier" application designs. Which is best for web apps? Why?
A: Modern application design typically consists of separating an application into smaller, more…
Q: How can a compiler automatically construct an Object() method in native code?
A: Introduction: If we don't provide our own Object() [native code] function, the C++ compiler will…
Q: What exactly is an interruption? Demonstrate why there will be no disturbances to the hardware while…
A: Predictions of hardware failures are made by characterising the many types of hardware failures: A…
Q: Define parallel or multiprocessing. co-processing IBM's 1,000-processor Option Blue supercomputers…
A: Introduction: Parallel processing is a computing methodology that allows multiple processors or…
Q: Encryption or encoding? Encrypting data instead of encoding it—when?
A: Data must be transformed into a new format using an encoding strategy. Data can be encoded into a…
Q: All routers participate in these four tasks.
A: Router: It's a piece of hardware in a network that moves packets of information along. In other…
Step by step
Solved in 4 steps with 3 images

- Solve problem on 79 Project Euler. This is a Graph problem in disguise, so the key is to figure out what is node and what is an edge. In other words, what are the things that have relationships in this problem and what defines their relationships? Once you figure that out, you can use topological sort to solve the problem. Create an account on the site to confirm your answer. You can do this in any language, but a key to solving the problem is finding the indegree of each node. The indegree of a node in a directed graph is the number of edges that have that node as a destination,1 or the number of edges that lead into the node. JUNG has a built in method for graphs to do this. The other thing to keep in mind for JUNG is that you can’t make two edges with the same value. So if you’re using a String to represent edges, you can’t have two edges with the value of "A". please use java and intellijSolve problem on 79 Project Euler. This is a Graph problem in disguise, so the key is to figure out what is node and what is an edge. In other words, what are the things that have relationships in this problem and what defines their relationships? Once you figure that out, you can use topological sort to solve the problem. Create an account on the site to confirm your answer. You can do this in any language, but a key to solving the problem is finding the indegree of each node. The indegree of a node in a directed graph is the number of edges that have that node as a destination,1 or the number of edges that lead into the node. JUNG has a built in method for graphs to do this. The other thing to keep in mind for JUNG is that you can’t make two edges with the same value. So if you’re using a String to represent edges, you can’t have two edges with the value of "A".Data structure/ C language / Graph / Dijkstra’s algorithm implement a solution of a very common issue: howto get from one town to another using the shortest route.* design a solution that will let you find the shortest paths betweentwo input points in a graph, representing cities and towns, using Dijkstra’salgorithm. Your program should allow the user to enter the input filecontaining information of roads connecting cities/towns. The programshould then construct a graph based on the information provided from thefile. The user should then be able to enter pairs of cities/towns and thealgorithm should compute the shortest path between the two cities/townsentered.Attached a file containing a list of cities/towns with the following data:Field 1: Vertex ID of the 1st end of the segmentField 2: Vertex ID of the 2nd of the segmentField 3: Name of the townField 4: Distance in KilometerPlease note that all roads are two-ways. Meaning, a record may representboth the roads from feild1 to field2…
- PLEASE HELP, PYTHON THANK YOU class Graph(object): def __init__(self, graph_dict=None): ################# # Problem 1: # Check to see if the graph_dict is none # if so, create an empty dictionary and store it in graph_dict ################## #DELETE AND PUT IN THE IF AND ASSIGNMENT STATEMENTS self.__graph_dict = graph_dict ################# # Problem 2: # Create a method called vertices and pass in self as the parameter ################## #DELETE AND PUT IN THE METHOD DEFINITION """ returns the vertices of a graph """ return list(self.__graph_dict.keys()) def edges(self): """ returns the edges of a graph """ ################# # Problem 3: # Return the results of the __generate_edges ################## #DELETE AND PUT IN THE RETURN STATEMENTS1- Create a struct to store the node label and its cost:struct Node{char label;int cost;};SCS214: Data StructuresAssignment-42- Implement a class MinHeap that has the following declaration:3- Create a class WeightedGraph, which stores a graph using an adjacency matrixwith the following declaration:class WeightedGraph{ int** g; int nVertices;public:int getNVertices();//returns the number of vertices int getWeight(char,char);//returns weight of the edge connecting the givenvertices int* returnNeighbors(int v);// returns the indices of the neighbors of the vertexv as an int array int numNeighbors(int v);//returns the number of neighbors of the vertex v void loadGraphFromFile(ifstream&);//allocates the adjacency matrix & initializesedge weights from the specified file void dijkstra(char startVertex, char* prev, Node distances[] );//find the shortestpath from the start vertex to all other vertices, by filling the prev array and thedistances array};class MinHeap{ Node* heap; //an…14.12 NVCC Lab: Count number of subsets of a graph A graph is made up of a set of nodes called vertices and a set of lines called edges that connect the nodes. Informally, a connected component of a graph is a subset in which each pair of nodes is connected with each other via a path. For example, the following graph consists of two connected components (subsets). For this assignment, you are required to find out the number of connected components in a graph as specified below: implement the following method: public static int countConnectedComponents(String fileName): where fileName is the input data file representing a graph: each line in the data file contains two numbers representing a pair of vertices that are connected (an edge between these two nodes exists). For example, given the following data file: 1 2 1 3 2 3 4 5 6 8 6 7 *Code must be written in JAVA
- PLEASE HELP, PYTHON THANK YOU def add_vertex(self, vertex): if vertex not in self.__graph_dict: self.__graph_dict[vertex] = [] def add_edge(self, edge): edge = set(edge) (vertex1, vertex2) = tuple(edge) ################# # Problem 4: # Check to see if vertex1 is in the current graph dictionary ################## #DELETE AND PUT IN THE IF STATEMENTS self.__graph_dict[vertex1].append(vertex2) else: self.__graph_dict[vertex1] = [vertex2] def __generate_edges(self): edges = [] ################# # Problem 5: # Loop through all of the data in the graph dictionary and use the variable vertex for the loop'ed data ################## #DELETE AND PUT IN THE LOOP STATEMENTS for neighbour in self.__graph_dict[vertex]: if {neighbour, vertex} not in edges: edges.append({vertex, neighbour}) return edges…Problem Statement: Write a program which should create a weighted graph of the values entered by the user and then write functions that perform the following: 1. Depth first search of source and destination vertex 2. Breadth first search of source and destination vertex 3. Shortest path search of source and all destination vertices (Dijkstra's algorithm) 4. Shortest path search of source and destination vertex (Dijkstra's algorithm) The program should present a menu of the options and should run until the user opts to quit.C++, void traverseWithDijkstra(string start); ➔Use Dijkstra's algorithm to compute the single source shortest path in the graph from the start city to all other nodes in its component. ➔You don’t print anything in this function. Storing the distance associated with every node relative to the start node is enough. .hpp #ifndef GRAPH_H #define GRAPH_H #include<vector> #include<iostream> using namespace std; struct vertex; struct adjVertex{ vertex *v; int weight; }; struct vertex{ vertex() { this->visited = false; this->distance = 0; this->pred = NULL; } string name; bool visited; int distance; vertex *pred; vector<adjVertex> adj; }; class Graph { public: void createEdge(string v1, string v2, int num); void insertVertex(string name); void displayEdges(); void depthFirstTraversal(string sourceVertex); void traverseWithDijkstra(string sourceVertex); void minDistPath(string start, string end); private: vector<vertex*> vertices; };
- Application: Apply Algorithm (Q5 – Q7) The following questions ask you to manually apply an algorithm introduced in the lecture and demonstrate your understanding by describing intermediate states of the computation. Question 5 (Sorting) Write down the list content at the end of each iteration of the main loop (ie. end of each pass) of Insertion Sort for the following list: [14,12,7,4,18,9] Use one line for each pass. Question 6 (Graph Traversal) Apply Depth First Search (DFS) to traverse the following graph. Start your traversal from vertex 0, and write down the order in which vertices will be visited during the traversal. (image for this question also attached) Question 7 (Gaussian elimination) (image for this question also attached) Apply forward elimination to this system of linear equations to put it into the upper triangular form. ⎛⎝⎜⎜1 1 2225−12−1⎞⎠⎟⎟⎛⎝⎜⎜? ? ?⎞⎠⎟⎟=⎛⎝⎜⎜6 3 13⎞⎠⎟⎟(12−1 122 25−1)(� � �)=(6 3 13) Write each row operation you use to solve the problem. Find…Graphs: Depth First Traversal Starting with the same graph program as last assignment, implement a depth first traversal method. Test iy on nodes 1, 2, and 3 as start nodes. Graph program: #include <iostream>#include <vector>#include <string>using namespace std; class Edge;//-------------------------------------------------------------////class Node{public:Node(string iname){name = iname;}string name;int in_count = 0;bool visited = false; vector<Edge *> out_edge_list;};//-------------------------------------------------------------////class Edge{public:Edge(string iname, double iweight, Node *ifrom, Node *ito){name = iname;weight = iweight;from = ifrom;to = ito;} string name;double weight;Node *from;Node *to;bool visited = false;}; //-------------------------------------------------------------////class Graph{public:vector<Node *> node_list;vector<Edge *> edge_list; //----------------------------------------------------------//Node*…A graph file is provided below. What is the total number of fan-in and fan-out of vertex 4? # Graph example 5 # Number of vertices D # Directed graph 0 1 10 # List of edges 0 3 20 1 3 5 0 2 3 2 1 2 2 4 15 3 4 11

