Show that in every stable matching, m₁, m₂ are matched to w₁, w₁, i.e., (m₁,w₁), (m₂, w₂) or (m₁,w₂), (m₂, w₁) must be part of any stable matching.
Show that in every stable matching, m₁, m₂ are matched to w₁, w₁, i.e., (m₁,w₁), (m₂, w₂) or (m₁,w₂), (m₂, w₁) must be part of any stable matching.
Operations Research : Applications and Algorithms
4th Edition
ISBN:9780534380588
Author:Wayne L. Winston
Publisher:Wayne L. Winston
Chapter15: Deterministic Eoq Inventory Models
Section15.2: The Basic Economic Order Quantity Model
Problem 15P
Related questions
Question
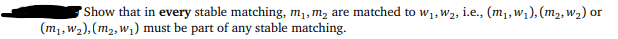
Transcribed Image Text:Show that in every stable matching, m₁, m₂ are matched to w₁, W₂, i.e., (m₁,w₁), (m₂, W₂) or
(m₁,w₂), (m₂,w₁) must be part of any stable matching.
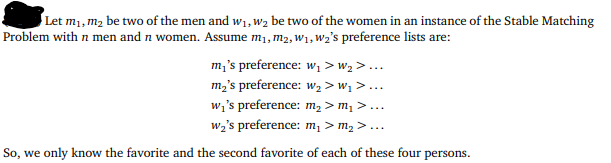
Transcribed Image Text:Let m₁, m₂ be two of the men and w₁, W₂ be two of the women in an instance of the Stable Matching
Problem with n men and n women. Assume m₁, M₂, W₁, W₂'s preference lists are:
m₁'s preference: w₁ > W₂ >...
m₂'s preference: W₂ > W₁ >...
w₁'s preference: m₂ > m₁ >...
w₂'s preference: m₁ > m₂ >...
So, we only know the favorite and the second favorite of each of these four persons.
Expert Solution
Step 1
Given
m1, m2 be two of the men, and w1, w2 be two of the women
The preference lists of m1, m2, w1, w2 are:
m₁'s preference: w1> w2 >...
m2's preference: w2> w1 >...
w1's preference: m2> m1 >...
w2's preference: m1> m2 >...
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole