() Suppose network 210.1.2.0/24 is subnetted with prefix length /29, the subnets are shown in the table below. What are the values labelled A1 to A6 in the table below? Subnet Subnet address Usable host range Broadcast address 210.1.20 A1 A2 A3 20 A4 to A5 Last A6 A1:210.1.2 A2:210.1.2 A3:210.1.2 A4:210.1.2 A5:210.1.2 A6:210.1.2 (1) The department of HR uses subnet 10, the first usable IP address of which is assigned to the subnet default gateway. Suggest IP address configuration for a PC in department of HR. IP address 210.1.2 Subnet mask 255.255.255. Default gateway 210.1.2
() Suppose network 210.1.2.0/24 is subnetted with prefix length /29, the subnets are shown in the table below. What are the values labelled A1 to A6 in the table below? Subnet Subnet address Usable host range Broadcast address 210.1.20 A1 A2 A3 20 A4 to A5 Last A6 A1:210.1.2 A2:210.1.2 A3:210.1.2 A4:210.1.2 A5:210.1.2 A6:210.1.2 (1) The department of HR uses subnet 10, the first usable IP address of which is assigned to the subnet default gateway. Suggest IP address configuration for a PC in department of HR. IP address 210.1.2 Subnet mask 255.255.255. Default gateway 210.1.2
Operations Research : Applications and Algorithms
4th Edition
ISBN:9780534380588
Author:Wayne L. Winston
Publisher:Wayne L. Winston
Chapter20: Queuing Theory
Section20.10: Exponential Queues In Series And Open Queuing Networks
Problem 8P
Related questions
Question
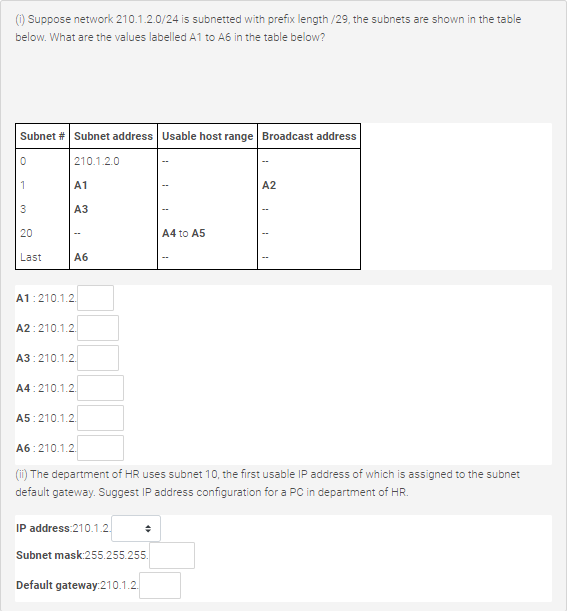
Transcribed Image Text:() Suppose network 210.1.2.0/24 is subnetted with prefix length /29, the subnets are shown in the table
below. What are the values labelled A1 to A6 in the table below?
Subnet # Subnet address Usable host range Broadcast address
| 210.1.2.0
1
A1
A2
АЗ
20
A4 to A5
Last
Аб
A1:210.1.2.
A2:210.1.2.
A3:210.1.2.
A4:210.1.2.
A5:210.1.2.
A6:210.1.2.
(ii) The department of HR uses subnet 10, the first usable IP address of which is assigned to the subnet
default gateway. Suggest IP address configuration for a PC in department of HR.
IP address:210.1.2.
Subnet mask:255.255.255.
Default gateway:210.1.2.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole