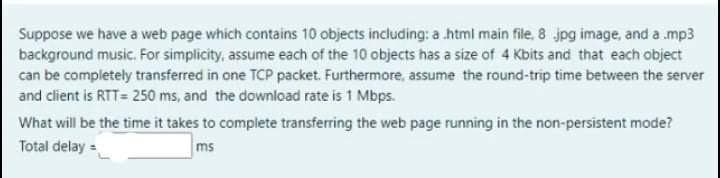
Suppose we have a web page which contains 10 objects including: a html main file, 8 jpg image, and a .mp3 background music. For simplicity, assume each of the 10 objects has a size of 4 Kbits and that each object can be completely transferred in one TCP packet. Furthermore, assume the round-trip time between the server and client is RTT= 250 ms, and the download rate is 1 Mbps. What will be the time it takes to complete transferring the web page running in the non-persistent mode? Total delay = ms
Q: 6c. Utilization. Consider the scenario shown below, with a two clients sending to a server. The…
A: As per given information :- R1 = R2 = 10 Mbps R3 = 100 Mbps
Q: Q. Consider a computer 1 that communicates with a computer 2 via LAN1, router R1, and LAN2. The…
A:
Q: ridges are empty. List all ports on which a packet will be forwarded by bridges B1 and B2 for the…
A: We have a connection of multiple nodes with bridges and hubs. Here we need to find the path of ports…
Q: Consider TCP implements an extension that allows window sizes much larger than 64 KB. Suppose that…
A: Introduction
Q: Suppose Host A wants to send a large 8 million bytes of file to Host B. The path from Host A to Host…
A: Total time required to send file = addition of transmission delay at the 3 links Transmission delay…
Q: Suppose an extension of TCP allows window size much larger than 64 KB. Assume the extended TCP runs…
A: Solution :
Q: The original HTTP protocol used TCP/IP as the underlying network protocol. For each page, graphic,…
A: Hypertext Transfer Protocol is an application-layer protocol for transmitting hypermedia documents…
Q: Consider a network with a ring topology, link bandwidths of 100 Mbps, and propagation speed 2 × 108…
A:
Q: Consider a simple application-level protocol built on top of UDP that allows a client to retrieve a…
A: Here's the solution:
Q: Suppose that a router receives simultaneously 3 packets (pkt1, pkt2, and pkt3) with length L1 = 1…
A: As per bartleby guidelines we have answered three questions and they are as follows.
Q: Consider the scenario in which one computer sends a packet to another computer by using the…
A: The issue at the transport layer concerns the exchange of packets between two computers. A package…
Q: Suppose Alice with a Web-based e-mail account (such as Gmail) sends it message to Bob, who accesses…
A: Alice-> HTTP ->Web-based mail server-> SMTP-> Mail server for Bob ->POP3 ->Bob.
Q: Suppose Host A wants to send a large file to Host B. The path from Host A to Host B has three links,…
A: a) The throughput for the file transfer=min{R1,R2,R3} =min{500 kbps, 2 Mbps, 1 Mbps} =500 kbps…
Q: Consider a short, 10-meter link, over which a sender can transmit at a rate of 150 bits/sec in both…
A: total time for all received objects is given by: (200/150+Tp + 200/150 +Tp + 200/150+Tp +…
Q: Consider the below topology and Implement the given Routing Protocols on the topology using Cisco…
A: Introduction about EIGRP Routing protocol: The Enhanced Interior Gateway Routing Protocol (EIGRP) is…
Q: Consider Figure 2 for which there is an institutional network connected to the Internet. Suppose…
A: The answer has given below:
Q: Consider an IP packet with a data length of 4400 bytes. TCP header is of 40 bytes while that of IPv4…
A: Consider an IP packet with data of 4400 bytes. TCP header is 40 bytes while that of IPv4 reader is…
Q: Consider Figure 2.12, for which there is an institutional network connected to the Internet. Suppose…
A: Introduction Consider Figure 2.12, for which there is an institutional network connected to the…
Q: Consider a short, 10-meter link, over which a sender can transmit at a rate of 150 bits/sec in both…
A:
Q: 2.1 Mbps. Assume that packets are of length 2.0 Kb (Kilobits) and the length of the link is 100Km.…
A: Given Distance = 100KM velocity =? Bandwidth = 2.1Mbps Length of message = 2Kbits = 2*10^3…
Q: 2. Suppose a large file of size F bits is to be sent from host A to host B. There are two links and…
A: Answer: I have given answered in the handwritten format in brief explanation.
Q: we talk about the length of a connection chain containing multiple connections, we use the RTT…
A: It is defined as the duration in milliseconds (ms) it takes for a network request to go from a…
Q: Consider a computer 1 that communicates with a computer 2 via LAN1, router R1, and LAN2. The sending…
A: Answer :
Q: A frame containing http request is sent from Computer (A) [in whichever subnet it is now, make sure…
A: Assuming the switch is AP1, thus the MAC address of the switch is M1. The frame traveling from…
Q: Consider a scenario in which Host A and Host B want to send messages to Host C. Hosts A and C are…
A: ->The sender has sent a message to the recipient many times. In the situation here. The channel…
Q: node called A that sends packets to an adjacent node called B. To control the packet flow to node…
A: It is defined as a small segment of a larger message. Data sent over computer networks, such as the…
Q: Consider the Go-back-N protocol with a sequence number space {0,1,2,3} and a window size N=3, and…
A: In Go-Back-N ARQ,N is the sender's window size. Suppose we say that Go-Back-3, which means that the…
Q: Consider a TCP connection betweek two hosts between A and B. The first data byte sent by A is…
A: Given : First byte received = 1 Last byte received= 500
Q: In the figure below, the routing table of Router A,B and C are given at a single point in time.…
A: Distance vector algorithm is a dynamic routing algorithm and in this the changes are depending on…
Q: Consider the following scenario: rdt 3.0 is operating on a link with bandwidth of 100 Mbps. The…
A: Link utilization = Transmission time/ transmission+propagation time Transmission time = packet size…
Q: The original HTTP protocol used TCP/IP as the underlying network protocol. For each page, graphic,…
A: Transmission Control Protocol (TCP) TCP is a connection-oriented protocol. Connection direction L…
Q: Consider a short, 10-meter link, over which a sender can transmit at a rate of 150 bits/sec in both…
A: Given: The length of the link is 10 meters Bandwidth is 150 bits/sec The size of a data packet…
Q: Consider an HTTP client that wants to retrieve a Web document at a given URL. The IP address of the…
A: For application layer, DNS and HTTP protocols are needed. For transport layer, UDP protocol is…
Q: Registration Number: 193046 Consider a network with 3 hosts and a NAT router. Suppose that the…
A: a) Home address : 192.168.1.1, 192.168.1.2, 192.168.1.3, 192.168.1.4 b) NAT Translation table…
Q: Consider a simple application-level protocol built on top of UDP that allows a client to retrieve a…
A: UDP is acronym as User Datagram protocol. It is a connectionless protocol.A simple application-level…
Q: the UDP server described needed only one socket, whereas the TCP server needed two sockets. Why? If…
A: Sockets in UDP and TCP: The User Datagram Protocol or UDP server needs only one socket, whereas the…
Q: Consider a IP address 201.24.58.69 in classful address, if the number of 1's in directed broadcast…
A: introduction :
Q: Consider an HTTP client that wants to retrieve a Web document at a given URL. The IP address of the…
A: A new document can be retrieved by an HTTP client at a given location or URL initially, HTTP server…
Q: Suppose Host A wants to send a large file to Host B. The path from Host A to Host B has three links,…
A: Consider given data: R1 = 500 kbps, R2 = 2 Mbps, R3 = 1 Mbps The throughput for the file…
Q: Consider the three words in the network A, B, and C. The host sends a 700-bit packet to the host saw…
A: Intro In a network having three hosts A, B, C. the Total end to end delay for transferring a…
Q: Consider sending a large file of F bits from Host A to Host B. There are two links (and one router)…
A: Introduction
Q: Consider taking an HTTP client to look for a web document in a specified URL. Firstly, it is not…
A: HTTP client can fetch a web data at a specified location or URL.HTTP server initially did not know…
Q: Consider two hosts A and B that are quite far apart. They are communicating using Selective Repeat…
A: The solution is given below:
Q: Part C Consider the following network topology, show the routing table of R1. You must show the…
A: Kernel IP routing table Destination Gateway Genmask Flags Metric Ref Use Iface 192.168.0.0 0.0.0.0…
Step by step
Solved in 2 steps

- Consider a web page whose base file is of size S1 = 10 KB. Assume that the web page consists of N = 20 inline objects each of size S2 = 100 KB. Assume that the round-trip time to the web server is T = 100 ms and the bottleneck capacity is C = 10 Mbps. Ignore any packetization delays and header overhead.a. Assuming non-persistent HTTP is used with a single TCP connection, how long does it take to download the web page?b. Assuming non-persistent HTTP is used with 4 parallel TCP connections, how long does it take to download the web page?c. Assuming pipelined, persistent HTTP is used, how long does it take to download the web page? ”Pipelined” means requests for multiple objects can be sent back-to-back on the same connection.d. Assuming non-pipelined, persistent HTTP with 2 parallel TCP connections is used, how long does it take to download the web page? Assume that the 2 parallel connections equally share the total available bandwidth C.We explore whether either UDP or TCP offers any level of end-point authentication in this problem. a. Consider a server that accepts a request via UDP and responds via UDP (for example, as done by a DNS server). Where would the server give its answer if a client with IP address X spoofs it with address Y? b. Assume a server receives a SYN with IP source address Y and responds with SYNACK. The server then receives an ACK with IP source address Y and the right acknowledgmentamount. Assuming the server selects a random initial sequence number and there is no "man-in-the-middle," how can the server be confident that the recipient is really at Y (and not at any other address X that spoofs Y)?Consider a short, 10-meter link, over which a sender can transmit at a rate of 150 bits/sec in both directions. Suppose that packets containing data are 100,000 bits long, and packets containing only control (e.g., ACK or handshaking) are 200 bits long. Assume that N parallel connections each get 1/N of the link bandwidth. Now consider the HTTP protocol, and suppose that each downloaded object is 100 Kbits long, and that the initial downloaded object contains 10 referenced objects from the same sender. Would parallel downloads via parallel instances of non-persistent HTTP make sense in this case? Now consider persistent HTTP. Do you expect significant gains over the non-persistent case? Justify and explain your answer
- Consider a node called A that sends packets to an adjacent node called B. To control the packet flow to node B, node A employs a credit manager scheme in which parameters C=3(credits), C_max=4(credits) and \tao=6(msec), respectively. node A has an infinite buffer to temporarily store packets. When a packet arrives at node A, node A stores the packet at the bottom of the buffer. Node A also has a single server (transmitter). As soon as the server becomes idle, the server picks up a packet at the head of the buffer, if any, and serves the packet for packet transmission time T_p as far as there remains a credit. (The packet transmission time T_p = 4 (msec).) We observed the arrival times of the first 12 packets, denoted by aA(1)⋯A(12), which were as follows: n A(n) 1 0.5 msec 2 1.0 3 1.5 4 2.0 5 4.5 6 5.5 7 6.5 8 12.5 9 13.0 10 13.5 11 14.0 12 14.6 1. Let R(n) denote the departure time of the n th packet from the buffer for n∈{1,2,...}. Find R(n) for…Consider Figure 2.12, for which there is an institutional network connected to the Internet. Suppose that the average object size is 1,000,000 bits and that the average request rate from the institution’s browsers to the origin servers is 16 requests per second. Also suppose that the amount of time it takes from when the router on the Internet side of the access link forwards an HTTP request until it receives the response is three seconds on average (see Section 2.2.5). Model the total average response time as the sum of the average access delay (that is, the delay from Internet router to institution router) and the average Internet delay. For the average access delay, use ∆/(1 - ∆b), where ∆ is the average time required to send an object over the access link and b is the arrival rate of objects to the access link. Find the total average response time. I get ∆=1000000/15000000= 1/15, then ∆/(1 - ∆b)= (1/15)/(1-(1/15)*16)=-1, so the finally answer is : 3+(-1)=2s or 3+0=3s?Consider the three-node network below, that uses flow-based generalized forwarding (e.g., as in OpenFlow) in the network's routers. In the question below, we'll want to create match+action entries in the flow table at router r2, with three ports labelled 1,2,3 (in black). In the question, matches are constrained to be over only four fields: the IP source address, the IP destination address, the upper-layer protocol field of the IP datagram, and the destination port number of the transport-layer segment. The actions are either to drop or to forward(i), that is, to forward a matching packet on port i. The default action (unless stated otherwise) is that if a packet doesn't match a rule, it will be dropped.Question: Suppose we want to implement the following rule: r2 should act as a firewall, only allowing TCP traffic into the 22.33/16 network from any network. Specify a single flow table row entry to implement this rule, indicating the column entries for the row below. The * is a…
- Suppose Alice, with a Web-based e-mail account (such as Hotmail or Gmail), sends a message to Bob, who accesses his mail from his mail server using POP3. Discuss how the message gets from Alice’s host to Bob’s host. Be sure to list the series of application-layer protocols that are used to move the message between the two hosts.Suppose Alice with a Web-based e-mail account (such as Gmail) sends it message to Bob, who accesses his mail from his mail server using POP3. Discuss how the message gets from Alice's host to Bob's host. Be sure to list the series of application -layer protocols that are used to movethe message between the two hosts.Suppose within your Web browser you click on a link to obtain a Web page. The IP address for the associated URL is not cached in your localhost, so a DNS lookup is necessary to obtain the IP address. Suppose that n DNS servers are visited before your host receives the IP address from DNS; the successive visits incur an RTT of RTT1, . . ., RTTn. Further suppose that the Web page associated with the link contains exactly one object, consisting of a small amount of HTML text. Let RTT0 denote the RTT between the local host and the server containing the object. Assuming zero transmission time of the object, how much time elapses from when the client clicks on the link until the client receives the object? Justify your answer.
- Consider an HTTP client that wants to retrieve a Web document at a given URL. The IP address of the HTTP server is initially unknown. What transport and application-layer protocols besides HTTP are needed in this scenario?so given two printer, one of IP address is 200.23.16.202 and subnet mask is 255.255.255.224, and other one IP address is 200.23.16.170 and subnet mask is 255.255.255.224. Suppose the network that hosts the above printer is re-configured with other networks in the building. After re-configuration, the printer's IP address would remain the same but its network is changed with a new subnet mask, which is changed to 255.255.255.128. This means, even the printer's IP address looks the same, its network ID and host ID are different from those before re-configuration. Find the new network ID and host ID of this printer. You must write both in the standard dot-decimal format without attaching the subnet mask.In this programming assignment, you will implement a decentralized peer-to-peer network architec-ture (P2P), including the basic implementation of the BitTorrent protocol (BTP). General P2P architec-tures can be classified into centralized and decentralized, In P2P centralized architectures, new peers senda request to the Traker (normally done via HTTP) requesting a list containing all the IP addresses ofthe peers that are already connected to the P2P network sharing the same file. The tracker then, replieswith a response containing such list. In P2P decentralized architecture, each peer is also a Traker, and itcan share only limited resources because it only sees the partial network. On the other hand, P2P decen-tralized networks avoid single point of failure since they do not depend of centralized trackers. Examplesof P2P applications that are/were implementing centralizing architectures are Nasper, the Berkeley OpenNetwork Infrastructure (BOINC) and some versions of BitTorrent.…

