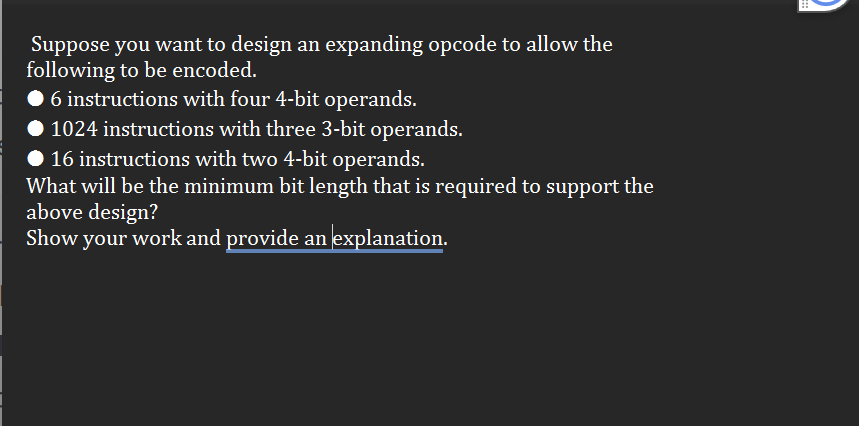
Suppose you want to design an expanding opcode to allow the following to be encoded. 6 instructions with four 4-bit operands. 1024 instructions with three 3-bit operands. ◆ 16 instructions with two 4-bit operands. What will be the minimum bit length that is required to support the above design? Show your work and provide an explanation.
Q: Please provide a solution for the Knapsack Problem using Genetic Algorithm:
A: 1. Encoding the problem and creating an initial populationIn a 0/1 Knapsack problem with a genetic…
Q: Based on the following Jackson network, determine what is the average waiting time for Node C at any…
A: A Jackson network is a queuing network model used in queuing theory, particularly in computer…
Q: Please help me with these questions. I am having trouble understanding what to do Programming…
A: 1. Start2. Enter a positive integer3. Set number = input4. While number > 0 a. digit = number…
Q: = Suppose that we have a B and the size of the search key field V is equal to 10 bytes, the size of…
A: The objective of the question is to calculate the block size (B) for a B-tree given the size of the…
Q: What is the difference between MDB and MIB? Give two examples of managed object.
A: In the context of networking, MIB stands for "Management Information Base," whereas MDB usually…
Q: please help me complete 4.2.1 and 4.2.3. I will like
A: Kindly find the below answer and give helpful rating. Explanation:function [xx, tt] = syn_sin(fk,…
Q: Assume you have three input pins called Pin 1, Pin 2, and Pin 3. Assume you have a single 2-bit…
A: The solution is given in the below step.
Q: Make an ER Diagram based on this information below NYU needs a new system to manage reservations of…
A: The reservation management system proposed for New York University's ULibrary aims to address the…
Q: Can you please help me with question 2.10 because I am struggling, to answer question 2.10 you need…
A: A formal grammar that describes the syntax of programming languages or other formal languages is…
Q: Create empty images for Ix, Iy, Ixx, Iyy, and Ixy (all the same dimensions as your original image)…
A: The "cornerness" values were visualized in the final step, where the lowest value was mapped to…
Q: Let L₁ = {aa, bb}, L₂ = {A, a, aa}, L3 = {x | x = {a,b}* ^ |x| ≤ 3} = {A, a, b, aa, ab, ba, bb, aaa,…
A: The question asks us to evaluate the following expression:(L₁ ∩ L₃) L₂where:L₁ = {aa, bb}L₂ = {Λ, α,…
Q: Python: How do I create a recursive function asterisk with both recursive and base cases? so for…
A: The program defines a recursive function print_asterisks that takes an integer n as input.In the…
Q: The diagram should have a package named Math that includes a class shape which has two subclasses…
A: In this question we have to create UML class diagram based on specific criteria:Math Package: There…
Q: • A constructor that creates a cruise ship with the specified name, the specified year that the ship…
A: Here code has four classes in separate Java files.• TestShips – It is considered as the main class…
Q: 1) What is the difference between a list and a tuple? And when do we use them? 2) What is…
A: Note: According to bartleby rules and guidelines we can only answer first 3 sub questions, please…
Q: ical operator to include all values. Don’t forget to add curly brackets with each condition. Feel…
A: A C program is a collection of commands defined in the C programming language that a computer can…
Q: putStream and DataOutputStream - binary file I/O RandomAccessFile - binary file i/o where every…
A: The term "read and write objects" describes how to serialize and deserialize objects in Java. The…
Q: Throughout, a graph is given as input as an adjacency list. That is, G is a dictionary where the…
A: Pseudocode is a way of describing an algorithm in a human-friendly format that doesn't have to…
Q: What is SSL and TLS? What crypotgraphic tools do they use to protect data?
A: SSL (Secure Sockets Layer) and TLS (Transport Layer Security) are cryptographic protocols designed…
Q: what is python
A: Python is a popular high-level interpreted programming language that is easy to learn and…
Q: I see theres 5 miss and 5 hits. But it says 4 miss. and whats the answer for this: the 2 ends up…
A: A LRU ( least recently used) is a page replacement algorithm that used by the operating system to…
Q: Write a program in JAVA that sorts a Stack of unique Integers using In-Place Selection Sort. The…
A: 1. Main Method: - Create a stack of integers. - Push some integers into the stack. - Print the…
Q: How can you create a Python function named "convert" that utilizes the Haversine formula to…
A: The objective of the question is to create a Python function named 'convert' that uses the Haversine…
Q: Computer Architecture Given the below IEEE single precision FP format: 1-bit Sign 8-bit Biased…
A: A standard for representing and manipulating floating-point values in computer systems is IEEE…
Q: Implement the Function has_error Implement the function according to the specification. Use the…
A: Step-1: StartStep-2: Function has_error(json) Step-2.1: Parse the json Step-2.2: If success is…
Q: Give informal English descriptions of PDAs for the languages in Exercise 2.6. question 2.6 2.6…
A: Context-free grammars (CFGs) are formalisms used to describe languages by generating strings of…
Q: Please help me with these questions. I dont know how to draw these flowchart (Practice Worksheets)…
A: The objective of the question is to understand how to devise algorithms for two specific problems…
Q: Task 2: Secondary Index & Aggregation Query Processing Assume the relation CITIZEN(ID,…
A: The objective of the question is to understand the cost of retrieving data using a secondary index…
Q: Data cleaning occurs at which stage of the data analysis process? Question 4 Answer a . Data editing…
A: Data cleaning, also known as data cleansing or scrubbing, is a crucial process in the data analysis…
Q: Is artifical intelligence the future for industries?
A: The question is asking whether artificial intelligence (AI) will play a significant role in the…
Q: what is python just give it in one line
A: An artificial language used to convey commands to a computer or other computing equipment so that it…
Q: Solve these questions
A: The objective of the question is to estimate the values of the given integrals using the Monte Carlo…
Q: A QUESTION 5 provides a file-system interface that allows clients to create and modify files. OA.…
A: In computing, a filesystem -- every so often written filesystem -- is a logical and physical machine…
Q: Can you please help me with this problem because i am struggling with how to do this because I don't…
A: L={w#x∣w is a substring of x where w,x∈{0,1}∗}:PDA for Checking Substring Relationship:Description:…
Q: Hello, would you mind helping me with question 2.5? In order to tackle it effectively, I'll need the…
A: Context-free languages—including regular languages—are accepted by pushdown automata. No context is…
Q: Write a program in c that has three float variable (place random values in them) and that will call…
A: Please refer to the following for the algorithm of the code =>Start.Initialize three float…
Q: can the performance complexity of the following algorithm be described? for x in…
A: When we talk about an algorithm's complexity in Python, we usually mean its time complexity, which…
Q: x=[20,15,9,7] y=[85,83,80,78] y1=1./(y-x) plot (x,y1)
A: To find the area under the curve defined by the points (x, y) using the trapezoidal rule.Calculating…
Q: (f) A hash table with 6 buckets is initially empty and the hash function is h(k) = k%6. What is the…
A: This is the final state of the hash table after inserting 3, 6, 1, 12, and 7.Bucket 0Bucket 1Bucket…
Q: What are the different use cases to use firewall in computer networks?
A: The objective of the question is to understand the different scenarios or use cases where a firewall…
Q: 2.7 Give informal English descriptions of PDAs for the languages in Exercise 2.6. question 2.6 2.6…
A: Push down automata is used to implement context-free grammar. The three main components of push-down…
Q: List the different network management standards. Which of them is the most widely implemented?
A: In the realm of computer networking, efficient and effective network management is paramount for…
Q: Task: Overriding (Redesign the CanadianAddress class) This task will rewrite the CanadianAddress…
A: Algorithm:Define a class CanadianAddress with private fields for street address, city, province, and…
Q: Which are applications that require a short response time? • client • file • SMTP • OLTP
A: Applications requiring short response times are those that need to quickly process and respond to…
Q: Assume that we have the following 6-tuple represing a finite automaton with output: (Q,2,4,6,4,A)…
A: In the realm of finite automata theory, Mealy and Moore machines are two fundamental types of finite…
Q: The SQL statement below is used to select students with the last name "Smith". What is wrong with…
A: To search for a last name in an SQL query, we can use the WHERE clause along with the LIKE operator…
Q: total wall area total_wall_area = 2 * (length + width) * height # Calculate total area of…
A: A Python programme is a collection of commands run by a Python interpreter and written in the Python…
Q: What is the importance of usability testing in Human-Computer Interaction?
A: The objective of this question is to understand the significance of usability testing in the field…
Q: Create code Using Intellij IDEA (Using Spring intializer, language: java, type: Maven)
A: Developing a Web Application for Hurricanes Soccer AcademyThis guide outlines the steps to build a…
Q: Consider the game tree below. Run the minmax with alpha-beta pruning algorithm on this tree starting…
A: Nodes not explored (pruned): 5Nodes: J, K, L, M, M2Explanation:Step 1: Start at node A. Begin the…
Trending now
This is a popular solution!
Step by step
Solved in 1 steps

- Given 16-bit instructions, is it possible to use expanding opcodes to allow the following to be encoded assuming we have a total of 32 registers? If so, show the encoding. If not, explain why is it not possible.Q. 3 instructions with one 10-bit addressA computer with a 32 bit word uses an instruction format that includes direct and indirect addressing of 8 megabytes and on of 16 registers. The highest order bits are used for the opcode, followed by the bits indicating the register, followed by indirect/direct bit, followed by the bits indicating memory address Draw the instruction word's format, showing how many bits are used for all four fieldsQuestion 1 Let's assume %ecx = 0x000FFD0E and %eax= 0x000FED25 (Hexadecimal representation). What is the value in %ecx after the following instruction? orq %eax, %ecx Provide answer in hexadecimal representation. Acceptable answer format: 000003FD or 0x000003FD Question 2 Let's assume %eax= 0x000FED25 (Hexadecimal representation). What is the value in %eax after the following instruction? salq $4, %eax Provide answer in hexadecimal representation. Acceptable answer format: 000003FD or 0x000003FD
- Our ‘mostly 8-bit’ design has the problem that computed pointers can only range over256 bytes of memory. This makes using the screen difficult (though not impossible!). Howmight you extend the instruction set to make this easier? [Hint: think about spare bits inthe C-instruction.]Determine the machine code of the given instructions. Include operand or address size prefix. For the opcode,d,w, mod, reg, R/M use binary. For displacement and prefix, use hexadecimal. Write the displacement right after the modregR/M. The leftmost column will the If the given values are fewer than needed in the problem, add zero/es to the most significant place.Use single space in between bytes. Parenthesis is considered as bracket. e.g. Given: MOV (SI+12),DI Answer: 1001001 01111100 12 MOV BX, (EDX+(EDI*4)) Blank 1Determine the machine code of the given instructions. Include operand or address size prefix. For the opcode,d,w, mod, reg, R/M use binary. For displacement and prefix, use hexadecimal. Write the displacement right after the modregR/M. The leftmost column will the If the given values are fewer than needed in the problem, add zero/es to the most significant place.Use single space in between bytes. Parenthesis is considered as bracket. e.g. Given: MOV (SI+12),DI Answer: 1001001 01111100 12 MOV DX, (BP+DI) Blank 1
- Determine the machine code of the given instructions. Include operand or address size prefix. For the opcode,d,w, mod, reg, R/M use binary. For displacement and prefix, use hexadecimal. Write the displacement right after the modregR/M. The leftmost column will the If the given values are fewer than needed in the problem, add zero/es to the most significant place.Use single space in between bytes. Parenthesis is considered as bracket. e.g. Given: MOV (SI+12),DI Answer: 1001001 01111100 12 MOV (DI+9DFH), DEFAHFloating Point operations are expensive mainly because they require a separate processing unit which requires overhead to work properly. For these and other reasons, some small processors don't support floating point arithmetic; only fixed point (each register has a "fixed" number of bits and the ALU only supports integer arithmetic). For example, if you were writing a program using a 16 bit processor and needed resolution of 1/32, your algorithm could use 5 "fractional" bits and 10 integer bits (1 bit is needed for the sign bit). Write how you would implement this in your program.A digital computer has a memory unit with 24 bits per word. The instruction set consists of 150 different operations. All instructions have an operation code part (opcode) and an address part (allowing for only one address). Each instruction is stored in one word of memory.Q.) What is the largest unsigned binary number that can be accommodated in one word of memory?
- Most Intel CPUs use the __________, in which each memory address is represented by two integers.Assembly Language Question: You are given the following array in your data segment arr word 0F8h, 16h, 0DBh, 77h write ONE instruction to toggle the least significant bit of the second and third elements in the array(Toggle means to change a 0 to 1 and a 1 to 0), For example, after your instruction executes, the array should have: 0F8h, 17h, 0DAh, 77h.ATTEMPT ONLY IF YOU ARE 100% SURE ...DO NOT COPY FROM OTHER WEBSITES A 12-bit field of a RISC-V instruction contains the value 0x8FF. Provide the correspondent 32-bit value, expressed in hexadecimal, when the 12-bit value is sign extended to 32-bits.

