The details of each work out must be stored in a class called WorkOut object shown in the class diagram. Use the class diagram to code the WorkOut object. WorkOut start: DateTime end: DateTime description : string level : integer - points: real numWorkOuts: integer + LOW: integer <=4 + MEDIUM : integer 8 + Constructor (p: real, n:integer) + Constructor (s:string, e:string, d:string, 1:integer) + get Points () : real + getNumWorkOuts (): integer
The details of each work out must be stored in a class called WorkOut object shown in the class diagram. Use the class diagram to code the WorkOut object. WorkOut start: DateTime end: DateTime description : string level : integer - points: real numWorkOuts: integer + LOW: integer <=4 + MEDIUM : integer 8 + Constructor (p: real, n:integer) + Constructor (s:string, e:string, d:string, 1:integer) + get Points () : real + getNumWorkOuts (): integer
Chapter11: Advanced Inheritance Concepts
Section: Chapter Questions
Problem 2PE
Related questions
Question
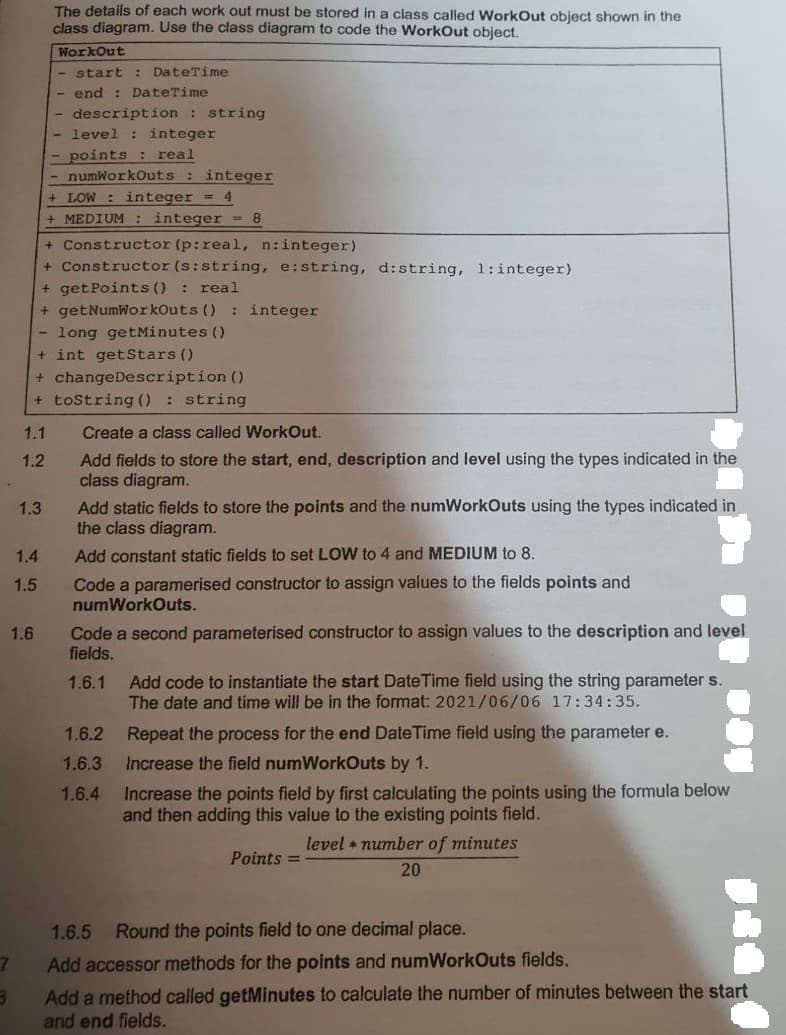
Transcribed Image Text:The details of each work out must be stored in a class called WorkOut object shown in the
class diagram. Use the class diagram to code the WorkOut object.
WorkOut
start: DateTime
- end : DateTime
description : string
level : integer
points: real
numWorkOuts: integer
+ LOW: integer = 4
+ MEDIUM : integer = 8
+ Constructor (p: real, n:integer)
+ Constructor (s: string, e:string, d:string, 1:integer)
+ getPoints(): real
+ getNumWorkOuts (): integer
- long getMinutes ()
+ int getStars ()
+ changeDescription ()
+ toString(): string
1.1
Create a class called WorkOut.
1.2
Add fields to store the start, end, description and level using the types indicated in the
class diagram.
1.3
Add static fields to store the points and the numWorkOuts using the types indicated in
the class diagram.
1.4
Add constant static fields to set LOW to 4 and MEDIUM to 8.
1.5
Code a paramerised constructor to assign values to the fields points and
numWorkOuts.
1.6
Code a second parameterised constructor to assign values to the description and level
fields.
1.6.1 Add code to instantiate the start Date Time field using the string parameter s.
The date and time will be in the format: 2021/06/06 17:34:35.
1.6.2
Repeat the process for the end Date Time field using the parameter e.
Increase the field numWorkOuts by 1.
1.6.3
1.6.4
Increase the points field by first calculating the points using the formula below
and then adding this value to the existing points field.
level number of minutes
Points=
20
1.6.5
Round the points field to one decimal place.
7
Add accessor methods for the points and numWorkOuts fields.
8
Add a method called getMinutes to calculate the number of minutes between the start
and end fields.
NO
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

Programming with Microsoft Visual Basic 2017
Computer Science
ISBN:
9781337102124
Author:
Diane Zak
Publisher:
Cengage Learning