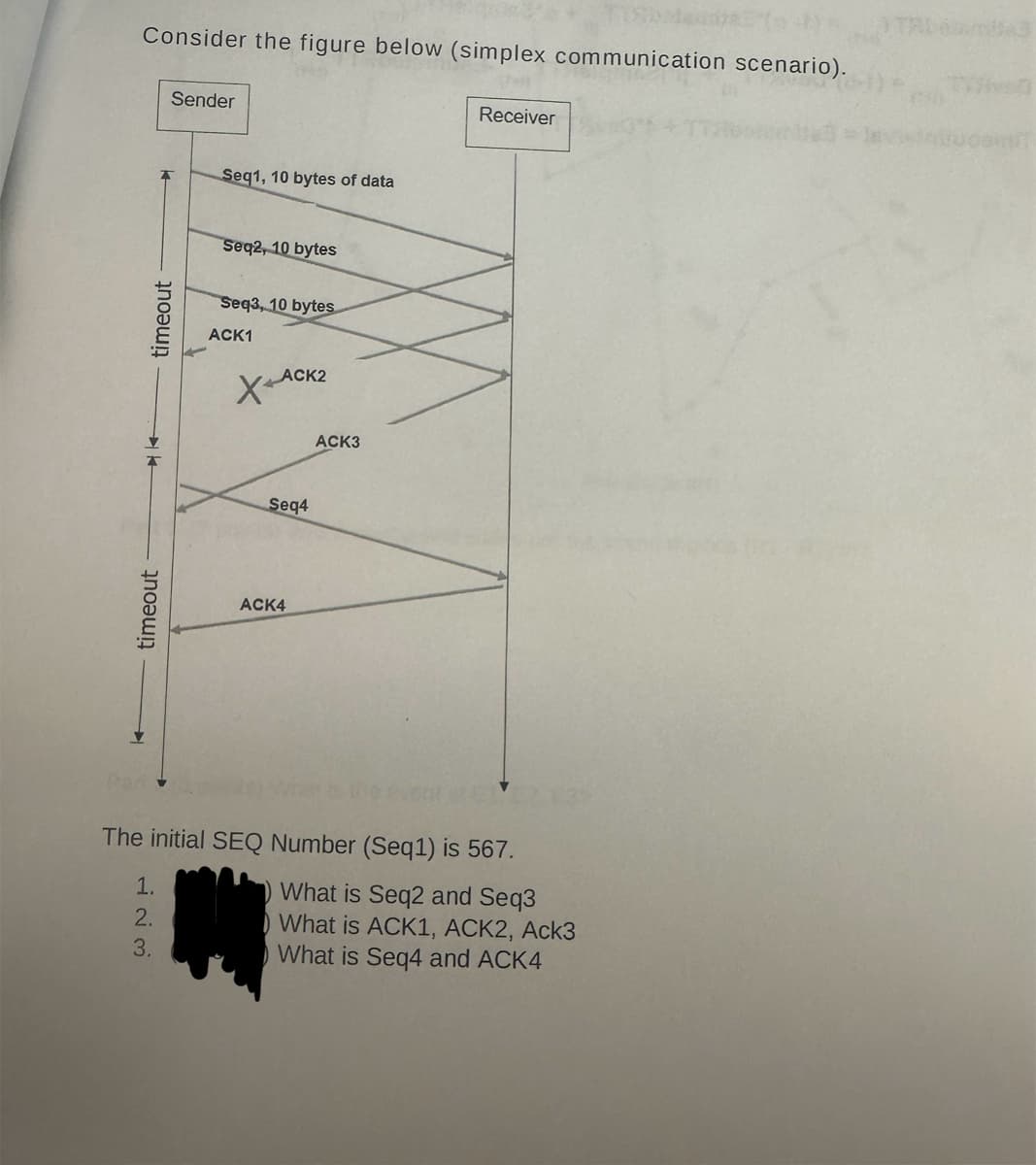
timeout timeout Sender Consider the figure below (simplex communication scenario). 23 Seq1, 10 bytes of data Seq2, 10 bytes Seq3, 10 bytes ACK1 ACK2 XA ACK4 Seq4 ACK3 The initial SEQ Number (Seq1) is 567. 1. 123 2. 3. What is Seq2 and Seq3 What is ACK1, ACK2, Ack3 What is Seq4 and ACK4 Receiver 3
Q: Hi there, could you kindly walk through this problem, breaking it down step by step? Additionally,…
A: Basics of Boolean algebra used to do the problem given: Detailed explanation: (A) (B) (C) (D)…
Q: For the given red-black tree: Add node 94 Remove node 51 0007 0002 0015 0027 0049 0001 0063 Remove…
A:
Q: The answer to c for me was: F(x,y,z) = y -(over the y) z + xyz
A: To simplify the expression F(x, y, z) = y - (over the y) z + xyz, let's apply Boolean algebra and…
Q: Please check the following requirements below, please produce the state transition diagram of a UML…
A: The objective of the question is to create a state transition diagram for a UML state machine. The…
Q: | The code in Part 1 counts the crossings and nestings for a given matching. We now want to use this…
A: Implement the random_matching function as described, generating matchings with 100 arcs (or 200…
Q: Please solve number 2 (1) and show all steps
A: Step 1:a) A + B, where A = 7, B = 6.Step 2:Convert A and B to binary. A = 7 in binary is 0111. B = 6…
Q: Refer to the screenshot to solve the questions on MIPS / PIPELINING:
A: a) Data dependencies:- 3 depends on 1 ($s2)- 4 depends on 1 ($s2)- 5 depends on 4 ($s6)- 6 depends…
Q: Method 2: Minimise the follow Boolean expression using Karnaugh Maps Y = ABC + ABC + ABC + ABC
A: If have any doubt feel free to ask.
Q: Alert dont submit AI generated answer. m68k assembly. Correct answer is written. Please explain it…
A: The objective of the question is to understand the m68k assembly code that controls the LED lights…
Q: question 3
A: Detailed explanation:(a) Transition graph of MACHINE:Here's a description of the transition…
Q: Q2- Reset bits 1,4,6 of A and set bits 3,5 when A=03BH Instruction MVI A,4E MVI D,20 ORA D ANI 16…
A: Sure, The image you sent me shows a circuit with several components, including resistors,…
Q: In a recent class, we utilized the Turtle module to create a variety of shapes, including a…
A: I have provided the explanation in comments.Figure:The code imports the Turtle module and creates a…
Q: Write a client program and server program. The server uses a socket connection to allow a client to…
A: The objective of the question is to create a client-server program where the client sends a filename…
Q: Suppose a program have 40% of its code enhanced to yield a system speedup of 4.3 times faster. What…
A: Approach to solving the question: Detailed explanation: Examples: Key references: computer science
Q: Please use MATLAB to solve this. Provide screenshots and explainnations please. The equation for a…
A: To find the equation of the lemniscate in terms of Cartesian coordinates (x, y), we can substitute…
Q: Which of the following describes the operation of a positive edge-triggered D flip-flop? The input…
A: Step 1: Question 1)Answer : CThe output will follow the input on the leading edge of the clock…
Q: Consider the same Simulated Annealing problem as the previous question. Pick the statement that best…
A: The most likely scenario in the next iteration of the Simulated Annealing algorithm is:s3, s4, and…
Q: In a 6-nodes network, what is the size of LSDB in terms of routing cost entries assuming duplex…
A: FEEL FREE TO ASK FOR CLARIFICATIONS
Q: In as much detail as possible answer the following question: The CEO of a software company is…
A: Migrating from an on-premises legacy environment to the cloud represents a significant paradigm…
Q: 1. Explain how a condition referred to as overflow occurs. 2. Explain two encoding techniques used…
A: In conclusion, building a solid foundation in programming and computational thinking requires an…
Q: 8. Please write in complete sentences and in as much detail as possible What is the principal…
A: Unveiling the Depths of Network Traffic: RMON2's Layer 2 ProwessRemote Network Monitoring (RMON) has…
Q: 2. Assume a declarative interface where n and max are constant integers, and A is an array of…
A: Approach to solving the question (a):Analyze the provided correctness statement and code snippet to…
Q: C f(x,1,2) = x² + x y z + x y z = 72(x+x) + xyz Inverse law: x + x = 1 = 72 (1) + xyz Z Identity law…
A: To simplify the expression �(�,�,�)=�2+2+��2+2(�+�)+���F(x,y,z)=x 2+2+xy 2+2(x+x)+xyz, let's break…
Q: 11100000 01000000 ******** ******** 1110000* ******** ******** ******** 11100001 1******* ********…
A: To determine the interface for each address, we match the first bits of the address with the…
Q: Please help. Please show work
A: The objective of the question is to prove that the logarithm base 2 of n factorial (log2 n!) is in…
Q: Provide the full C++ main.cpp, fraction.h, and fraction.cpp Output is included below: ----- Testing…
A: Approach to solving the question:To approach solving the question, follow these steps:Understand the…
Q: a Java method that will take in a double array as its sole parameter and return the difference…
A: Read the explanation (comment lines that start with //) in the above code to understand the purpose…
Q: Make the image below using html, css, and js
A: Here's how you can create a mock exam paper using HTML, CSS, and JavaScript: HTML <!DOCTYPE…
Q: State and explain three types of float in network analysis
A: The objective of the question is to understand and explain the three types of float in network…
Q: 1. Show the results of the following operations. Write your final answer in hexadecimals. [(AB)16…
A: Answer 1)To compute the XOR operation between hexadecimal numbers, we first convert them to binary,…
Q: Write a java program that Create a generic class AnimalList that has a type parameter T. It should…
A: The objective of the question is to create a generic class, superclass, subclasses, and a separate…
Q: Can you provide the code and comment for this question.
A: Let's delve into the code and the concepts involved in more detail.Understanding the Problem:The…
Q: Provide the full C++ main.cpp, mystring.h and mystring.cpp The output is included in one of the…
A: Detailed explanation:mystring.h #ifndef MYSTRING_H #define MYSTRING_H #include <iostream>…
Q: In Python, generate a random matrix A with 100 entries each of which is an independent…
A: The objective of the question is to generate a random matrix, perform certain operations on it, and…
Q: Please help me with these question. SHow all you work. Thank you 1. Prove that∀k ∈ N, 1k + 2k + · ·…
A: The first question is asking to prove that the sum of the kth powers of the first n natural numbers…
Q: The three values the sequence counter (SC) cycle through the FETCH portion of the RSC instruction…
A: Increment:The sequence counter (SC) is initially set to point to the memory address of the next…
Q: Suppose we have the instruction Load 1000. Given memory and register R1 contain the values below:…
A: To determine the value loaded into the accumulator (AC) when using indexed addressing mode with the…
Q: we are given a text file of 1000 points of data. Please write code that can take that data and put…
A: To solve this problem, we will develop a Python script that processes a text file containing 1000…
Q: Respond to the following in a minimum of 175 words: Identify 1 CRM, HRM, or ERP system you interact…
A: The objective of the question is to identify a CRM (Customer Relationship Management), HRM (Human…
Q: Karnaugh Map And Circuit Designing – 4 Bits Plus Or Minus 1Design a circuit with inputs x, y, z and…
A: Step 1/5Understand the Problem The problem requires designing a circuit with four inputs (x, y, z,…
Q: Perl Programming Consider the derived class stu of the main class person. Prepare the program that…
A: Here's the Perl program that demonstrates using AUTOLOAD for id and registration_year in a derived…
Q: Refer to the screenshot to solve the question on MIPS pipelining:
A: a) Non-pipelined ProcessorInstruction Latency: 1700 psClock Rate: Approximately 1.82 GHz (calculated…
Q: 2^-7 multiply by 101,000101 answer in binary
A: Convert Binary Number to Decimal:The binary number given is 101000101101000101. To convert this to…
Q: For a tree which uses lazy deletion, implement a function which counts the # of deleted nodes.
A: TreeNode class: Defines a class representing a node in the binary search tree. Each node has…
Q: Hello, can you please help me with part e and f because i am struggling with these two parts that I…
A:
Q: Make a Python Program (Involves Probability) That Accomplishes the Following Three Parts Based on…
A: from collections import Counter from scipy.stats import binom # Part A: Find the 7 most common…
Q: Refer to image and provide detailed answers! Computer networks!
A: 1. Key Requirements for a routing function in Packet-Switching NetworksCorrectness ensures that the…
Q: I need help with this Java problem to output as it's explained in this image below: This part…
A: Source code screenshots for reference: Output screenshot: Code explanation walkthrough:…
Q: I need help regardign this question and please dont use AI
A: Approach to solving the question:To approach solving this question, you can follow these…
Step by step
Solved in 2 steps

- Compute CBC-MAC for a message of 16 bits, “ABCD” (in Hexa). Assume a block size of 8 bits with an IV=C9 (in hexa). For simplicity, assume the encryption to be a simple XOR of the key with the plaintext. Let the encryption key be D8 (in Hexa). (Hint: Divide the message into blocks of 8 bits each; XOR each block with the previous cipher output; then encrypt this with the key. For the first block, XOR it with IV.This is what my professor said: Items are 4 bytes, pages are 2k, so ~512 items fit on a page. Even if we start in the beginning of a page, the first access will be a miss followed by ~200 hits, then a TLB miss followed by ~500 hits, so the hit rate is ~100%5. Page size 512 means 9 bits of offset and 7 bits of VPN. The offset is just the decimal version of 1 0111 0111 [unsigned] which is 375The offset is 0011 100 which is 28. Is he correct?Computer Science To answer this question, you may need to write a small program. Consider the following case: current cwnd value is 1000 bytes and 1 MSS is 10 bytes (=1 TCP packet carries 10 bytes of payload). With the basic formula, after 1 RTT, the congestion window would be updated to 1010 bytes (1000 + 10). What would be the value of window if ACK clocking is used? It would be a non-integer number, so give value including only two digits after comma
- Consider the following page address stream: 2 1 4 3 5 3 2 4 5 2 1 2 4 3 1 Which of the following causes the most page faults to occur on a machine with 3 frames? Scheme that causes the most faults: a) First in First out b) LRU and FIFO are the same number of faults c) FIFO and Opitimal are the same number of faults d) All have the same number of faults e) Least Recently Used f) No faults occurs g) LRU and Optimal are the same number of faults h) Optimal NUMBER OF FAULTS CAUSED: a)10. The technique of temporarily delaying outgoing acknowledgements so that they can be hooked onto the next outgoing data frame is known as a. Bit stuffing b. Piggy backing c. Pipelining d. BroadcastingAssume you are using any correct plaintext padding method, such as those described in lecture, with a 128-bit (16-byte) block cipher. If you are sending a message that is 184 bytes long, how many padding bytes would you need to add? Justify your answer. For the remaining questions, consider a 4-bit block cipher, described in hexadecimal by the following table: Plaintext Ciphertext Plaintext Ciphertext 0 a 8 e 1 c 9 d 2 f a 0 3 6 b 7 4 3 c 5 5 8 d b 6 4 e 9 7 2 f 1 You can think of this as a simple substitution cipher for hexadecimal digits. There is no “key” other than the table itself.
- Given the logical address 0x 69656, what will be the logical page number issued by a process P? OxD What is the corresponding physical frame number? 15 What is the hexadecimal physical address? I am having trouble to understand how you get hexadecimal physical address answer OxA9656 Your responses should be given in hexadecimal format!a. Compute CBC-MAC for a message of 16 bits, “8642” (in Hexa). Assume a block size of 8 bits with an IV=F1 (in hexa). For simplicity, assume the encryption to be a simple XOR of the key with the plaintext. Let the encryption key be B4 (in Hexa).Suppose the Vole communicates with a printer using the technique of memory-mapped I/O. Suppose also thataddress 0xFF is used to send characters to the printer, and address 0xFE is used to receive information about theprinter’s status. In particular, suppose the least significant bit at the address 0xFE indicates whether the printeris ready to receive another character (with a 0 indicating “not ready” and a 1 indicating “ready”). Starting ataddress 0x00, write a machine language routine that waits until the printer is ready for another character and thensends the character represented by the bit pattern in register 0x5 to the printer.
- **Please do C****C IS different from B** a. Compute CBC-MAC for a message of 16 bits, “8642” (in Hexa). Assume a block size of 8 bits with an IV=F1 (in hexa). For simplicity, assume the encryption to be a simple XOR of the key with the plaintext. Let the encryption key be B4 (in Hexa). (Hint: Divide the message into blocks of 8 bits each; XOR each block with the previous cipher output; then encrypt this with the key. For the first block, XOR it with IV. Details in pages 325-326 Ch.12 of the textbook) b. Suppose Alice computes the Secret prefix MAC (page 322: secret prefix MAC(x) = h(key || x)) for the message ”AM” (in ASCII) with key “G” (in ASCII) that both Alice and Bob know. The hash function that is used is h(x1x2x3)= g(g(x1 XOR x2) XOR x3 ) where each xi is a character represented as 8 bits, and g(x) is a 8-bit string that is equal to the complement of bits in x. For example, g(10110011) = 01001100. The MAC is 8 bits. (8-bit ASCII representation of the characters is given…This question was already asked on Bartleby however the two level table was not created. A computer system uses 16-bit addresses for virtual and physical addresses, and each page and frame has a size of 256 bytes. 1. suppose that the OS uses a two-level page table. Draw the page table using the same structure and logic as the image provided, from an article found online this logic can be anazyed through the link https://sonsh0824.tistory.com/entry/MultiLevel-Page-Table . (Assume that frames 7 through 221 are free, so you can allocate space for the page table there.) In addition, suppose that the page-table directory storage comprises a whole number of consecutive full frames. (For examples: if the directory entry is 2 bytes, the entry’s storage comprises 1 frame; if the directory entry is 260 bytes, the entry’s storage comprises 2 consecutive frames.) 2. What is the size of the two-level page table given in question I(f)? 3. Now, translate the virtual addresses to physical…Q: Consider a system which has Logical Address = 4 GB, Physical Address PA= 64 MB, Page Size = 4 KB, then calculate Number of pages =? Number of frames =? Number of entries in Page Table =? Size of Page Table =?

