Translate the automaton below into a regular expression using the algorithm described above. Note that the automaton already has a single initial and a single final state. Please draw the automaton after each step. Here a step consists of: • Removing all double arrows in the automaton. • Removing one state. • Again, remove all double arrows. It is important to follow the algorithm closely. The regular expressions have the following syntax: + for union, for concatenation and for Kleene star aor L for A, the language containing only the empty word 0 (zero) for Ø, the empty language can often be left out Example expression: abc*d(a +L + Obc)*c is short for a · b· c* ·d · (a + A + Ø • b· c)* · c. a 1 a 3 a b a
Translate the automaton below into a regular expression using the algorithm described above. Note that the automaton already has a single initial and a single final state. Please draw the automaton after each step. Here a step consists of: • Removing all double arrows in the automaton. • Removing one state. • Again, remove all double arrows. It is important to follow the algorithm closely. The regular expressions have the following syntax: + for union, for concatenation and for Kleene star aor L for A, the language containing only the empty word 0 (zero) for Ø, the empty language can often be left out Example expression: abc*d(a +L + Obc)*c is short for a · b· c* ·d · (a + A + Ø • b· c)* · c. a 1 a 3 a b a
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter10: Classes And Data Abstraction
Section: Chapter Questions
Problem 19PE
Related questions
Question
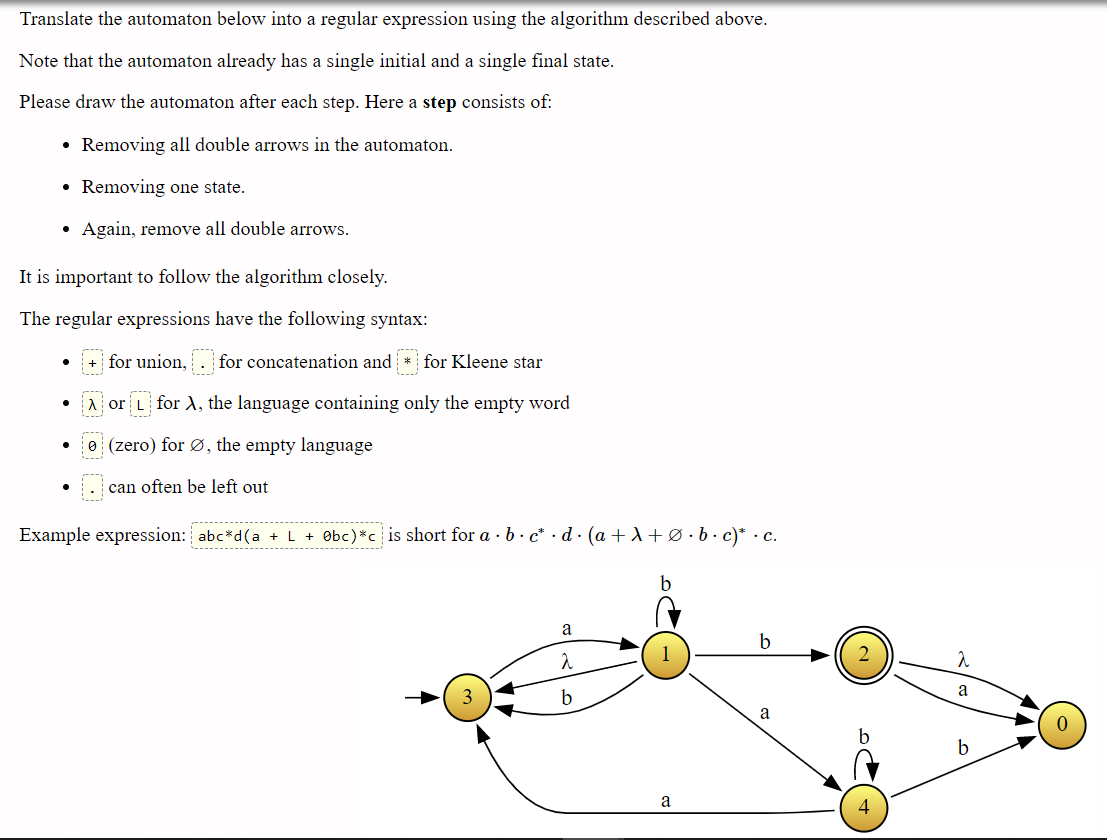
Transcribed Image Text:Translate the automaton below into a regular expression using the algorithm described above.
Note that the automaton already has a single initial and a single final state.
Please draw the automaton after each step. Here a step consists of:
• Removing all double arrows in the automaton.
• Removing one state.
Again, remove all double arrows.
It is important to follow the algorithm closely.
The regular expressions have the following syntax:
+ for union, . for concatenation and * for Kleene star
Aor L for A, the language containing only the empty word
e (zero) for Ø, the empty language
can often be left out
Example expression: abc*d(a +L + Obc)*c is short for a · b · c* · d · (a + A +Ø•b• c)* · c.
------
b
a
b
a
b
b
a
4
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 4 steps with 6 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning