utput should be 3 57 Rembo this should be.
Q: What effects will the Internet of Things have on our daily lives? To prove your idea, provide an…
A: The Internet of Things - (IoT) is a network of real-world objects, or "things," that have been…
Q: What is the name of the integrated memory cache that houses the CPU on the same die?
A: The temporary memory referred to as "CPU cache memory" is called cache. Your computer's chip-based…
Q: What does it mean to be "busy waiting"? What other sorts of waiting are there in an operating…
A: A "busy" waiting procedure regularly checks for a condition.Although it is "busy" hunting for the…
Q: The Common TCP/IP Ports are an example. To correctly design security, businesses must comprehend the…
A: Answer- TCP/IP stands for Transfer Control Protocol/ Information Protocol. During a data transfer,…
Q: 4. Consider the following grammar with terminals [, ], a, b, c, +, and -: a) S→ [SX] | a X +SY | Yb…
A: Dear Student, The detailed solution for your question is given in step 2 and the final table is…
Q: A number is said to be Harshad if it's exactly divisible by the sum of its digits. Create a function…
A: A number is called Harshad if it is exactly divisible by the sum of its digits. logic- return i ==…
Q: What are the two advantages of layered protocols?
A: The question has been answered in step2
Q: What are some of the drawbacks of having pages that are fragmented?
A: Introduction: Fragmentation is an unfortunate issue in the functioning system where the cycles are…
Q: Write a program to generate the following pattern. (Sample input/output given below) Enter number of…
A: As per the requirement program is developed. Algorithm: Step 1: Write the main method Step 2:…
Q: What circumstances make using conventional files for data storage effective?
A: Answer: Conventional files perform effectively for data storage: -> File processing cost less and…
Q: How does the separation between kernel mode and user mode work as a basic security (or protection)…
A: 1) In kernel mode, the program has immediate and unlimited admittance to framework assets. In user…
Q: Why is it necessary to study software engineering fundamentals if you are a programmer?
A: Software Engineering Fundamentals is such topics as software metrics, real-time software design,…
Q: Think about a multiuser, time-sharing, multiprogramming system. Which process protection-related…
A: Consider a multiprogramming or time-sharing system with several users. Which concerns about the…
Q: Think about how cloud computing encourages open innovation.
A: Cloud computing enables a variety of services.This includes consumer services such as Gmail or the…
Q: Question 7: “../info/data.htm" is a(n) A. relative URL B. absolute URL C. none of above
A: In this question a Uniform Resource Locator (URL) is given we need to identify which type of URL is…
Q: What is JVM and is it platform independent?
A: Advantages of the Java object class structure with its instance fields and methods:- A class object…
Q: What possible use may a motherboard power connection in the SATA type serve?
A: It is possible for the power connection for a SATA hard drive to come from the motherboard. This…
Q: Write a program to generate the following pattern. (Sample input/output given below) Enter Odd value…
A: Code: #include<stdio.h> int main() { int n,m=1; char ch='Z'; printf("Enter Odd value…
Q: Does using partitions in Linux make a significant difference?
A: Disk partitioning is the creation of separate divisions of a hard disk drive using partition editors…
Q: Trace each pass of selection, insertion, bubble and quick sort for the list of values below. For…
A: The answer is written in step 2
Q: an to be "busy waiting"? What other sorts of waiting are there in an operating system? Is it…
A: Introduction: As part of a process synchronisation approach known as busy waiting, spinning, or busy…
Q: JAVA Problem Create a function that determines whether elements in an array can be re-arranged to…
A: Algorithm - Take one string as input. Now use the below logic return (arr[arr.length - 1] -…
Q: Why and how do numerous Linux commands behave in the same way on Macs and Linux systems,…
A: The utility of Linux operating system is known as the Linux commands.
Q: ch of the following represents a non-breaking space in html? A. & 3. & C. D.  
A: According to the information given:- We have to choose the correct option to satisfy the statement.
Q: Who are the people involved in the phases of Waterfall Model
A: The above question that is people involved in the waterfall model is answered below step.
Q: explicit, in what ways are t
A: Introduction: In complementary metal-oxide semiconductor (CMOS) memory, the BIOS password is kept.…
Q: A nonpipelined processor has a clock rate of 2.5 GHz and an average CPI (cycles per instruction) of…
A: (a) What is the speedup achieved for a typical program : No. of stages in pipeline( k)=5 SUPPOSE…
Q: How about demonstrating and outlining the actual use of virtual servers and services?
A: Virtual servers mimic the functionality of physical dedicated servers. You can deploy multiple…
Q: Warning: Not copy code again and again. N
A: You did not mention writing a particular programming language so we provide python code for you.…
Q: 5. Creating Lookups 6. Automatic Lookups 7. Geospatial Lookups 8. External Lookups 9. KV Store…
A: 5. Creating lookups: Creating a lookup field not only improves the meaning of the data, but helps…
Q: Dissertate on WebGL and OpenGL ES.
A: OpenGL is just a delivery API and has nothing to do with information, sound, or windowing. WebGL.…
Q: How can a client determine whether or not a server request will be fulfilled?
A: There are two scenarios when a server request will not be fulfilled. When the error arises from the…
Q: A microprocessor provides an instruction capable of moving a string of bytes from one area of memory…
A:
Q: a. If the last operation performed on a computer with an 8-bit word was an addition in which the two…
A: please check the solution below
Q: The reason why it's so important that you comprehend compressed zip files
A: The reason that compressed zip files and directories are so important are as follows:
Q: what use Linux may have in any element of rocket technology.
A: Linux is used extensively in rocket technology. It is used in the development and deployment of…
Q: What circumstances make using conventional files for data storage effective?
A: Data storage which refers to the files and the documents that are used to recorded in the digitally…
Q: A computer consists of a processor and an I/O device D connected to main memory M via a shared bus…
A: Given that, on an average, six cycles are required by the instruction.
Q: Produce a Turing Machine state diagram that decides the following language. You do not need to show…
A: Given: La = {anbn : n>=0} Logic to build turing machine for La is : step1) start reading input,…
Q: Why should we use the OSI Security architecture?
A: What is OSI Security Architecture : The security of an organisation is of the utmost importance to…
Q: Consider the context-free grammar (CFG) G = with production P S do S while S | while S do S | & and…
A: ANSWER:-
Q: Give a brief explanation of what machine language is. What are the causes of the inability of…
A: To Do: To describe machine language. Machine Language: Machine language is a collection of numerical…
Q: Who are the people involved in the phases of Waterfall Model
A: Answer: waterfall models is old method's that is used to sequentially manage the projects. Itis…
Q: 14 Use Gauss-Jordan elimination to solve the following linear system: -3x+4y=-6 5x-y=10 OA (2.0)…
A: According to the information given:- We have to solve and find out the correct option.
Q: Write a program in C to count the total number of alphabets, digits and special characters in a…
A: The program is written in C Language. Check the program screenshot for the correct indentation.…
Q: How should someone continue if they have forgotten both the administrator password and the system's…
A: Remove the CMOS battery to reset your BIOS. This patch causes the computer to forget that you were…
Q: Write some Conclusion of computing department (KMS) Blueprint The CONCLUSION of COMPUTING…
A: The CONCLUSION of COMPUTING DEPARTMENT Knowledge management system. Computing department is the one…
Q: a. Assume that interrupt processing takes about 100 μs (i.e., the time to jump to the interrupt…
A: a) :
Q: igators retrieve dat
A: volatile data: Any data which is put away in a volatile memory like RAM. What is vital to note is…
Q: Show how the following floating-point additions are performed (where significands are truncated to 4…
A: Please check the step 2 for solution
Output should be 3 57
Rembo this should be.
Step by step
Solved in 3 steps with 1 images

- C++ D.S. Malik Exercise 14-4 Write a program that prompts the user to enter time in 12-hour notation. The program then outputs the time in 24-hour notation. Your program must contain three exception classes: invalidHr, invalidMin, and invalidSec. If the user enters an invalid value for hours, then the program should throw and catch an invalidHr object. Follow similar conventions for the invalid values of minutes and seconds.Calculator.java, is a simple command-line calculator. Note the program terminates if any operand is nonnumeric.Write a program with an exception handler that deals with nonnumeric operands;then write another program without using an exception handler to achieve thesame objective. Your program should display a message that informs the user ofthe wrong operand type before exiting20.8 LAB: Exception handling to detect input string vs. integer The given program reads a list of single-word first names and ages (ending with -1), and outputs that list with the age incremented. The program fails and throws an exception if the second input on a line is a string rather than an integer. At FIXME in the code, add try and except blocks to catch the ValueError exception and output 0 for the age. Ex: If the input is: Lee 18 Lua 21 Mary Beth 19 Stu 33 -1 then the output is: Lee 19 Lua 22 Mary 0 Stu 34
- Instructions: Exception handing Add exception handling to this game (try, catch, throw). You are expected to use the standard exception classes to try functions, throw objects, and catch those objects when problems occur. At a minimum, you should have your code throw an invalid_argument object when data from the user is wrong. File GamePurse.h: class GamePurse { // data int purseAmount; public: // public functions GamePurse(int); void Win(int); void Loose(int); int GetAmount(); }; File GamePurse.cpp: #include "GamePurse.h" // constructor initilaizes the purseAmount variable GamePurse::GamePurse(int amount){ purseAmount = amount; } // function definations // add a winning amount to the purseAmount void GamePurse:: Win(int amount){ purseAmount+= amount; } // deduct an amount from the purseAmount. void GamePurse:: Loose(int amount){ purseAmount-= amount; } // return the value of purseAmount. int GamePurse::GetAmount(){ return purseAmount; } File…Note: you must use exceptions and try-catch blocksException Code Put this code in a try-catch block. You will need to handle exceptions for DividebyZero, Array error, and general error . In your catches, you may simply just print out an error message: x = car[x] / bar[y];
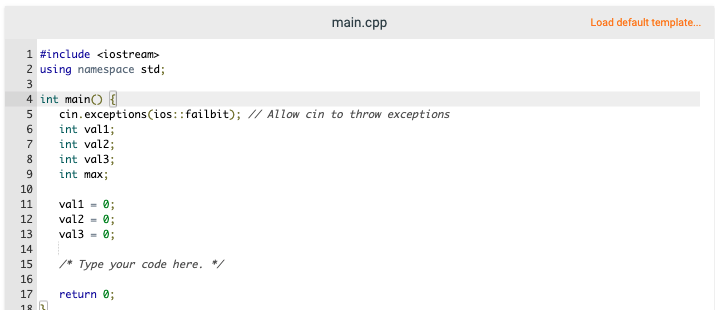
- Exception handling to detect input string vs. int C++ The given program reads a list of single-word first names and ages (ending with -1), and outputs that list with the age incremented. The program fails and throws an exception if the second input on a line is a string rather than an int. At FIXME in the code, add a try/catch statement to catch ios_base::failure, and output 0 for the age. Ex: If the input is: Lee 18 Lua 21 Mary Beth 19 Stu 33 -1 then the output is: Lee 19 Lua 22 Mary 0 Stu 34 #include <string>#include <iostream> using namespace std; int main() { string inputName; int age; // Set exception mask for cin stream cin.exceptions(ios::failbit); cin >> inputName; while(inputName != "-1") { // FIXME: The following line will throw an ios_base::failure. // Insert a try/catch statement to catch the exception. // Clear cin's failbit to put cin in a useable state. cin >> age; cout << inputName…Problem Statement:The purpose of this lab assignment is to gain experience in python’s Exception handling. In thisassignment, you will write a program for .edu email address validation system. Problem Design: The program will take an email address from user and check if it contains thefollowing:a. Address must contain at least an ‘@’ symbolb. Address must contain at least a ‘.edu’ suffixc. Length must contain at least 12 characters.d. Address must contain at least one digit 2. Helper functions to check if an address has at least one digit is provided. Docstring arealso given in the template file. This function returns True if condition satisfies otherwisereturns False. 3. Your task: Design a base class (Invalid Address) and child exception classes(InsufficientLength, NoDigit, NoEdu, NoAtSymbol ) to raise the exception when theconditions are not met. 4. Design a simple user menu to ask for the address as long as the user does not enter a validaddress. 5. The menu should also make a…(Uncaught Exceptions) Write a program that illustrates that a function with its own tryblock does not have to catch every possible error generated within the try. Some exceptions can slipthrough to, and be handled in, outer scopes.
- Explain Rethrow (propagate) exception with help of code.The problem comes from Introduction to C++ Programming and Data Structures, 4th Edition (HexFormatException)Implement the hex2Dec function in Programming Exercise 16.1 to throw a HexFormatException if the string is not a hex string .Define a custom exception class named HexFormatException. Write a test program that prompts the user to enter a hex number as a string and displays the number in decimal. If the function throws an exception, display "Not a hex number".Suppose you have a dictionary named my_dictionary containing the name of some groceries and their prices.my_dictionary={“Potato”:12, “Onion”:16, “Ginger”:15, “Garlic”:12, “Tomato”:15} Now write a python program that takes the grocerie names as input from the users and shows the total price of the groceries. Some exceptions to handle: Handle the exception when the given key is not present in the dictionary. Handle the exception when the summation variable is not initialized. (the variable to store the total price has been initialized at 0 or not) ============================= Example 1:Input:Potato,Onion,GingerOutput:43 ============================= Example 2:Input:Potato,Onion,Ginger,BeefOutput:Some groceries are not available in the dictionary.

