void foo(int n) { } int i; for (i = 0; i 0) i = 1 / 2;
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter5: Repetition Statements
Section5.5: A Closer Look: Loop Programming Techniques
Problem 12E: (Program) Write a program that tests the effectiveness of the rand() library function. Start by...
Related questions
Question
Give only the correct answer and don't copy
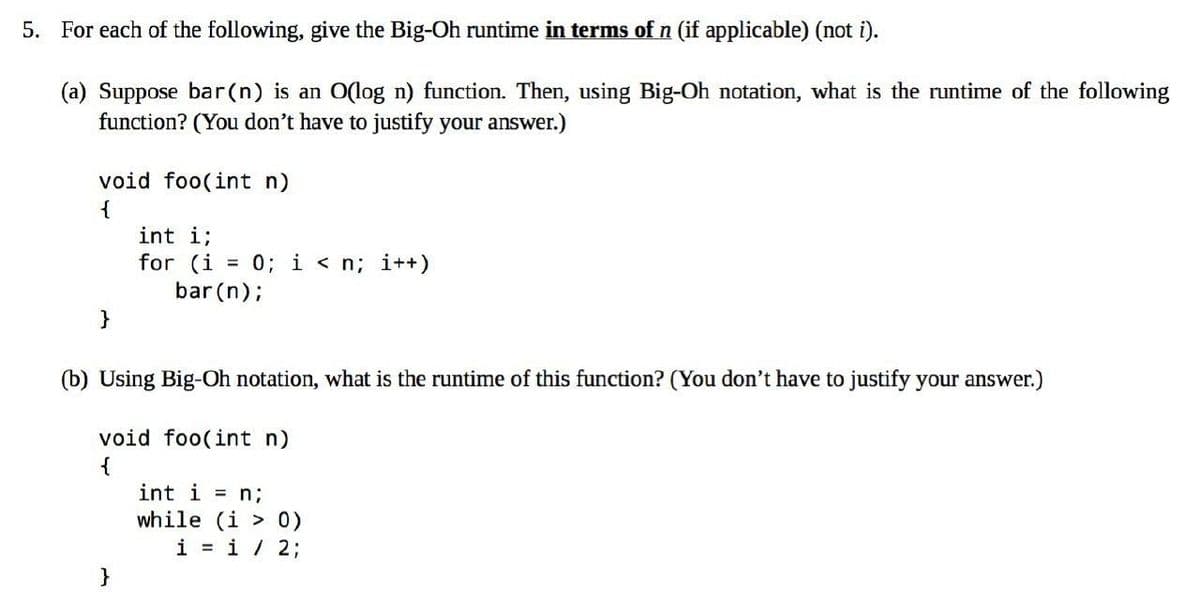
Transcribed Image Text:5. For each of the following, give the Big-Oh runtime in terms of n (if applicable) (not i).
(a) Suppose bar(n) is an O(log n) function. Then, using Big-Oh notation, what is the runtime of the following
function? (You don't have to justify your answer.)
void foo(int n)
{
}
int i;
for (i = 0; i<n; i++)
bar (n);
(b) Using Big-Oh notation, what is the runtime of this function? (You don't have to justify your answer.)
void foo(int n)
{
}
int i = n;
while (i > 0)
i = 1 / 2;
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning