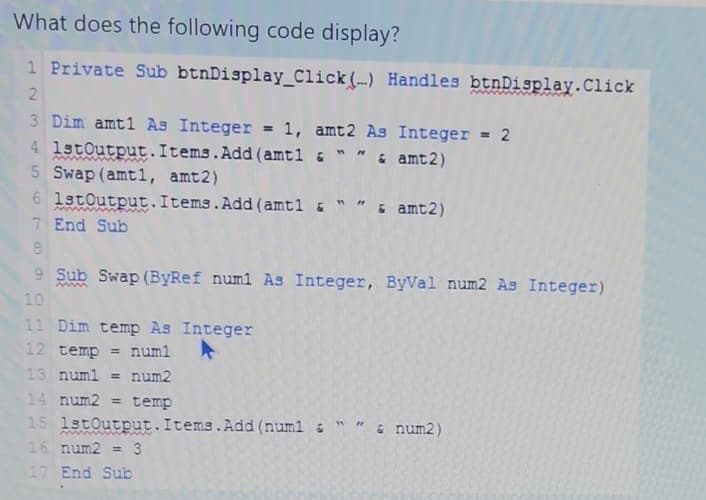
What does the following code display? 1 Private Sub btnDisplay_Click(..) Handles btnDisplay. Click 2 3 Dim amt1 As Integer = 1, amt 2 As Integer = 2 4 1stOutput.Items.Add(amt1 & " " & amt2) 5 Swap (amt1, amt2) 6 1stOutput.Items.Add(amt1 & 7 End Sub 8 11 Dim temp As Integer 12 temp = num1 13 num1 = num2 3 9 Sub Swap (ByRef num1 As Integer, ByVal num2 As Integer) 10 14 num2= temp 15 1stOutput.Items.Add(num1 16 num2=3 17 End Sub 3 & amt2) 2 & num2)
Q: What precisely is meant by the term "routing," and how does the process work? Describe in great…
A: The central point around which: The whole of IP availability revolves is routing. At its most…
Q: Question 1. Convert the RE ((a U b)* U (c U d)*))* into a NFA using the process defined in class.…
A: The answer is written in step 2
Q: Many talented engineers around the world want to contribute to his project. The re-discharge flows…
A: Input and output details: The first line of the input contains a single integer TT denoting the…
Q: Justify the need of using JAD as a requirement elicitation technique for the depth of data selection…
A: Joint application design, often known as JAD, is a method used to collect information about business…
Q: Could you please explain the Write Through method?
A: Here is the example regarding write through:
Q: Verification, validation, and security testing techniques may be used to any development project.
A: Verification and validation, abbreviated as V&V, is used in software project management,…
Q: What will the future of AI be like? Do we have AI software? How scary is AI?
A: AI software: Artificial intelligence is an area of computer science that develops intelligent…
Q: Identify and describe the top three difficulties in implementing Automated Testing Tools (AST).
A: Top Five Test Automation Challenges Effective Team Collaboration and Communication. This may be a…
Q: Exist any noteworthy distinctions between the two varieties of the internet?
A: The answer is written in step 2
Q: Explain the following terms in Excel with Example SumIF SumIFS CountIFS Vlook up…
A: “Since you have posted a question with multiple sub-parts, we will solve first three sub-parts for…
Q: Under what circumstances are threads running at the user level preferable to those running at the…
A: An execution flow across the process code is referred to as a thread. It has its program counter to…
Q: Further details on the metrics used to track software development progress might be provided as…
A: The Software development which refers to a sets of computer activities which are related to the…
Q: It is impossible to rule out the possibility that a problem with an application is the result of an…
A: Effective Problem Solving and Decision Making Types of Decision Makers Problem solving and decision…
Q: Give the order of growth for each of the following: 1. 10n + 100/ lg n
A: As per guidelines I can answer only first question. Thank You.
Q: Roman loves to make software. You have recently created a new open-source project that is gaining…
A: Algorithm: The first line of the input contains a single integer TT denoting the number of test…
Q: Consider a database system that is impenetrable by failures. Do I need a recovery manager to use…
A: Consider a database system that is impenetrable by failures. Do I need a recovery manager to use…
Q: cies needed to adapt in the emerging new age of technology in the 4th industrial revolution era How…
A: Lets see the solution.
Q: Question 4. Consider the language L over the alphabet (a, b, c, d } such that L = {abcd:n> 0, m>0}.…
A: Given: L = {anbncmdm : n > 0, m>0} We have to develop CFG for the language L.
Q: 1. Given the codes below. Draw a memory layout of pointers and variable(i-ii). What is the output…
A: - : Drawing a layout of pointers and variables : - Given x = 11is a variable, y =20 is a…
Q: Defining Question-Answering in AI and demonstrating how it relates to Natural Language Processing is…
A: I offered a resolution: Data recovery originally included question answering, but it has now grown…
Q: In this comparison of multiprogrammed batch processing and time sharing systems, the significant…
A: Below are the differences between time-sharing systems and multi-programmed batch processing: -…
Q: Consider a database system that is impenetrable by failures. Do I need a recovery manager to use…
A: Answer: Yes. Still necessary for this database system is a recovery manager.
Q: STRUCTURE OF TABLE TREE id INT PRIMARY KEY average_age INT(3) name CHAR(100) which…
A: The above question is solved in step 2 :-
Q: How were metrics of usability and user experience used throughout the evaluation process, and how…
A: Introduction: The quality of the programme has a significant impact on the success of software…
Q: user_num = int(input('Enter integer:\n')) Extend the given program as indicated. Output the user's…
A: Here, after taking input from the user, I have printed the number on the console. Next, I have…
Q: How Does CSS3 Manage to Achieve Greater Flexibility?
A: The above question that is css3 manage to achieve greater flexibility is answered in next step.
Q: Given set A={1,2,3,4}, B={1,2,3,4), and the mapping f: A → B, where f={(1,1), (1,2), (2,1), (3,3),…
A:
Q: When assessing the performance of your model, there are a lot of different elements to consider. How…
A: Introduction: Indeed, there were a great number of considerations to take into account regarding the…
Q: The characteristic that is present on the majority of controls determines, at run time, whether or…
A: Answer:
Q: How important is data modelling to the analytical process? The amount of data we'll need for our…
A: Data modelling: The criteria for employing data in a data modelling process are provided by the…
Q: On the basis of the testing process' maturity, write an essay on three testing goals.
A: Introduction: The use of a testing maturity model provides the twin purpose of identifying present…
Q: Write a short pitch for a game or animated TV show. It would help if you gave some idea of how the…
A: The answer is given below.
Q: Why is it not common practise to write big application programmes in assembly language?
A: Answer:
Q: Which type of IP addressing creates subnets that may be further divided into smaller subnets?
A: Here is the explanation regarding subnetting:
Q: Motion sensors may be used in a variety of ways. The exactness and efficacy of the data.
A: Introduction: Motion sensors contain an optical, microwave, or acoustic sensor, and often, a…
Q: Question 5. Consider the language L over the alphabet (a, b } such that L = {a²b³- n> 0, m>0 }. a)…
A:
Q: Clearly explain the primary differences that exist between multiprogrammed batch processing systems…
A: Introduction: Multitasking, often known as Time-Sharing Systems, is the logical extension of…
Q: How Can I Insert a Page Break After an HTML Element Using CSS?
A: Page Break After: Page-break-after is a feature that can add a page-break after something. Syntax:…
Q: You are a Senior software engineer at a start-up company named InstaSales developing an exciting new…
A: 1) Work from home anywhere The flexibility in office hours which enables to work from anywhere ,…
Q: lement Bubble sort !
A: Given: To write the C Code. Explanation: Algorithm: First input the array. Then, use bubble…
Q: What will be the future influence of artificial intelligence? If yes, what kind of AI-based software…
A: The concept of artificial intelligence: Is no longer limited to works of science fiction literature…
Q: Adding modules from the highest level to the lowest level is known as "top-down programming," and…
A: Likewise called "stepwise refinement," a product improvement method forces a progressive structure…
Q: create a list of guidlines for choosing a windows function for DSP application.
A: The Answer is in step-2.
Q: When it comes to a router's "Data Plane," what is its purpose? The item's function is unclear.
A: The fast path via the router/switch is called the data plane (also known as the forwarding plane).…
Q: What is routing? Describe a router's components and routing method.
A: #Routing:- Network layer devices carry out the operation of routing in order to send packets by…
Q: Investigate the Foursome of Cortez (in software development). What was the impact of GoF on Java…
A: GoF stands for Gang of Four. The four individuals in the group are E.G, R.H, R.J, and J.V. This…
Q: One of the characteristics of big data is the wide range of data types. Explain why it is necessary…
A: Big data refers to enterprises' structured, semi-structured, and unstructured information for…
Q: topic: Restaurant required outputs e. bubble diagram
A: Restaurant required outputs e. bubble diagram.
Q: Investigate the Foursome of Cortez (in software development). What was the impact of GoF on Java…
A: Designing object-oriented software is hard, and designing reusable…
Q: In what sense does the term "process control block" come into play. you must use your own words…
A: While creating the process the operating system performs several functions. Process identification…
Step by step
Solved in 2 steps with 1 images

- Please check the instructions on the images given. Sample output are also given on the image while the code for modification is provided below. hash.c #include <stdlib.h>#include <stdio.h> struct Node { int val; struct Node * next;}; struct HashTable { int size; struct Node ** table;}; struct Node * create_node(int val);struct HashTable * create_table(int size);void destroy_table(struct HashTable * h);void display_table(struct HashTable *h);int hash_function(int key, int size);void insert(struct HashTable *h, int val);int search(struct HashTable * h, int val);struct Node * delete(struct HashTable * h, int val); void main(){struct HashTable * h = create_table(8);display_table(h); int val_insert[12] = {12, 31, 45, 83, 72, 29, 84, 39, 61, 24, 10, 50}; for (int i=0; i<12; i++) { insert(h,val_insert[i]);}display_table(h); int val_search[4] = {29, 99, 72, 20};for (int i=0; i<4; i++) { int result = search(h,val_search[i]); printf("Search value %2d:…After the following code executes, what elements will be members of set3? set1 = set([1, 2, 3, 4]) set2 = set([3, 4, 5, 6]) set3 = set1.intersection(set2)After the following statement executes, what elements will be stored in the myset set? myset = set(['www', 'xxx', 'yyy', 'zzz'])
- Please allow the buttons to sort properly the sortByname, sortbywaittime and capacity to all sort please // Constructor that takes a Driver object as input public EntryScreen(Driver reservationlist1) { this.reservationlist1 = reservationlist1; // Initialize the necessary components txttableNumber = new JTextField(20); setTitle("Make a Reservation"); pnlCommand = new JPanel(); pnlDisplay = new JPanel(); String[] columnNames = {"ID", "Name", "Capacity", "Date", "Time"}; tableModel = new DefaultTableModel(columnNames, 0); table = new JTable(tableModel); JScrollPane scrollPane = new JScrollPane(table); add(scrollPane, BorderLayout.NORTH); // create the table and set the model // add the table to a scroll pane and add it to the GUI // add labels and text fields to the display panel pnlDisplay.add(new JLabel("Name:")); txtName = new JTextField(20);…After the following code executes, what elements will be members of set3?set1 = set(['a', 'b', 'c'])set2 = set(['b', 'c', 'd'])set3 = set1.symmetric_difference(set2)/** * Inserts the specified key-value pair into the symbol table while maintaining the * ordering of keys. Overwrites the old value with the new value if the symbol table * already contains the specified key. Deletes the specified key (and its associated * value) from this symbol table if the specified value is {@code null}. * * @param key the key * @param val the value * @throws IllegalArgumentException if {@code key} is {@code null} */ public void put(Key key, Value val) { // TODO // Change this code to make sure the list remains sorted! Also, solve this using recursion. // To do this, you will need to add a recursive helper function that takes the front of a // list (Node) as an argument and returns the front of the modified list (Node). if (key == null) throw new IllegalArgumentException("first argument to put() is null"); if (val == null) { delete(key); return; }…
- //inserts e at index ind publicvoidadd(intind,Te){ //if index is invalid display a message and return //valid index are 0 to size //push all elements up by one all the down to index ind (stop at index ind) //insert e at index ind //increase the size }Q2. Using comments on each line, generate the complete object code for the following SIC-XCprogram. NB: LDX = 04 LDA = 00 LDB = 68 STA = OC ADD = 18 TIX = 2C JLT = 38 RSUB = 4C Label Mnemonic OperandSUM START 0 LDX #0 LDA #0 +LBA #TABLE2 BASE TABLE2LOOP ADD TABLE, X ADD TABLE2, X TIX COUNT JLT LOOP +STA LOOP RSUB COUNT RESW 1TABLE RESW 2000TABLE2 RESW…Please fix this JAVA code so that it will not overwrite the contents of the file every time I click on a row @Overridepublic void valueChanged(ListSelectionEvent event) {File file = new File("sample json file");int row = table.getSelectedRow();JSONObject obj = (JSONObject) jsonArray.get(row);ObjectMapper mapper = new ObjectMapper();mapper.enable(SerializationFeature.INDENT_OUTPUT);try {JsonGenerator g = mapper.getFactory().createGenerator(new FileOutputStream(file));mapper.writeValue(g, obj);g.close();} catch (IOException e) {throw new RuntimeException(e);}}});
- Analyze the following code:int matrix[5][5];for (int column = 0; column < 5; column++);matrix[4][column] = 10; Select the correct option: After the loop, the last row of matrix 10, 10, 10, 10, 10. After the loop, the last row of matrix 0, 0, 0, 0, 0. A syntax error, because column is not defined. After the loop, the last column of matrix 10, 10, 10, 10, 10. After the loop, the last row of matrix 0, 0, 0, 0, 10.After the following statement executes, what elements will be stored in themyset set?myset = set([1, 2, 2, 3, 4, 4, 4])Create Trigger for When a student marks are being inserted, if the marks that are inserted are greater than 50, allow the insertion, but update marks to 50. Marks(Id , Marks) -> Table Fill in the blanks: ___ triggerName Before ___ ON Marks REFERENCING _____ AS nrow FOR EACH ROW WHEN (nrow.marks>50) _____ nrow SET nrow.marks = 50;

