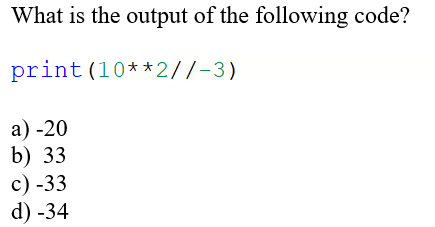
What is the output of the following code? print (10**2//-3) a) -20 b) 33 c) -33 d) -34
Q: Discuss the similarities and differences between recursive descent and top-down table parsing.
A: Analyze how recursive descent and table-driven top-down parsing are similar to one another and how…
Q: security precautions for private data Which properties of a database are regarded as being its most…
A: What is Database? An organized collection of data is, in the broadest terms, a database (DB). An…
Q: Describe the activities done by the driver of a bottom-up parser.
A: actions performed by a bottom-up program's driver. Loop searches the second table for action.…
Q: I would really appreciate it if you could give a description of the that are often associated with…
A: Database administrator (DBA) A DBA manages, maintains, coordinates, and operates a database…
Q: Please describe the routine tasks that are connected to the design and execution services offered by…
A: The term DBA is used to refer to a database administrator. in the introduction. A database…
Q: Is it possible to raise the standard of the methods used in healthcare by collaborating with the…
A: The question has been answered in step2
Q: There are benefits and drawbacks to starting software from a DVD vs downloading it from the…
A: DVD is an abbreviation for Digital Versatile Disk or Digital Video Disk. Because of the great…
Q: Based on yearly polls and surveys paid by businesses who provide agile solutions, provide an…
A: The Agile paradigm supports continuous testing and iteration throughout a project's Software…
Q: When a child process utilizes unnamed pipes to read the parent's message buffer, what happens…
A: According to the information given:- We have to describe the mentioned scenario when a child process…
Q: In order to provide a general picture of the use of agile methodology, analyze the findings of…
A: Given:- The Agile paradigm encourages continual testing and iteration throughout a project's…
Q: Contains annual research and polls on the use of agile approach funded by companies who provide…
A: Explanation of agile approach : Agile approach is an iterative approach to project management and…
Q: What benefits can platform-independent operating systems offer?
A: Definition: The advantages of platform-independent operating systems are discussed in this query. In…
Q: Could you kindly provide an example and a description of "Semantic augmentation" so that we may…
A: Required: Give an example of 'Semantic Augmentation' for CFG (Context Free Grammar) rules. Semantic…
Q: There is disagreement about how to assess which processes in the supply chain are most crucial.
A: Introduction Logistics planning, product planning, demand planning, sales and operations planning,…
Q: Why would you choose a binary or sequential search algorithm? What are the best procedures for…
A: The sequential search algorithm visits each element in the element list and checks if there is a…
Q: The computer's communication system is made up of six parts. Write a brief explanation of how each…
A:
Q: Understanding how a software product's settings are defined is crucial. What is known about the…
A: The configuration of a software product is the procedure through which the product is tailored to…
Q: Write psuedo code searches for a key & in a chain and returns true if the key is found and false,…
A: A code fragment illustrating the merging of two sorted lists is shown below with explaination:
Q: How does an object get serialized in Java?
A: Java is a widely-used programming language for coding web applications.
Q: What is artificial intelligence's (Al) ultimate goal? Give two instances for each of the main…
A: Introduction In contrast to the natural intelligence displayed by animals like humans, artificial…
Q: The user recycles broken computers in an eco-friendly way. Which stage of the hardware lifecycle…
A: 1) Hardware Lifecycle Management is a approach to managing the total useful life of IT hardware to…
Q: What happens if you input a command at the MS-DOS prompt that isn't an internal MS-DOS command?
A:
Q: ous thinking involves some degree of ambiguity and incompleteness.
A: Drawing logical conclusions and generating predictions based on the facts, beliefs, and information…
Q: Please describe the routine tasks that are connected to the design and execution services offered by…
A: The term "database administrator" (abbreviated "DBA") is often used to describe this kind of…
Q: Talk about a problem that a system's concurrent processing causes.
A: Concurrent processing is a kind of processing that involves many processors cooperating to carry out…
Q: Sequential search provides a variety of advantages over binary search, but what criteria should be…
A: A algorithm is, truth be told, a successive interaction. A sequential search goes through a rundown…
Q: Do authoritative and root servers, DNS records, iterated and non-iterated queries, and DNS records…
A: The domain name server (DNS) is the server that keeps the IP address of a website that corresponds…
Q: You've been tasked with examining a railway reservation and booking website. What testing techniques…
A: The system development life cycle is a project management strategy that specifies the phases…
Q: Consider the count-to-infinity issue in the distance vector routing. Can the count-to-infinity issue…
A: The crux of the Count to Infinity problem is that if node A informs node B that it has a path…
Q: How may the difference between the structure of a file and the structure of storage be explained?
A: Introduction: The file structure has several files, each of which is organized into many blocks.…
Q: Is it feasible to distinguish between a prescriptive and a descriptive model by comparing their…
A: Introduction: An explanation of the interaction between a system or other entity and its environment…
Q: Which system kinds, which may be categorized in a variety of ways, are included in this list?
A: The correct answer for the above mentioned question is given in the following steps.
Q: Solution in JS Taking each four digit number of an array in turn, return the number that you are on…
A: Algorithm - Take input from user. Now use the below logic - for (let n of nums) { for (let d…
Q: The communication system of the computer is made up of six parts. Describe, in your own words, how…
A: Elements of a Computer System: (i) Hardware, (ii) Software, (iii) People, (iv) Procedures, (v) Data…
Q: Are the supply chain KPIs and the operations that generate that data related?
A: Production chain management, which comprises supply planning, product planning, demand planning,…
Q: Discuss the similarities and differences between recursive descent and top-down table parsing.
A: Given: We have to discuss the similarities and differences between recursive descent and top-down…
Q: A good instruction set design must be able to survive quick changes in computer hardware and…
A: A. Name the four ground-breaking computer technologies. 1. Pentium chip Most of us probably…
Q: In terms of computer science, what is the distinction between polymorphism and abstraction?
A: Abstraction and polymorphism are very closely related and understanding the difference between them…
Q: Reviewing a railway reservation and booking website has been assigned to you. What testing…
A: Current Problem with railway reservation :- The current state of railway reservation technology…
Q: What use does DNS serve? Describe the routing of a new client request to www.example.co.uk through…
A: The Domain Name System (DNS) is the phonebook of the Internet. Humans access information online…
Q: Please describe the routine tasks that are connected to the design and execution services offered by…
A: A database administrator is referred to as a DBA in the introduction. A database management system's…
Q: Why don't embedded systems make use of virtual memory?
A: Virtual Memory: Usually employed in operating systems, virtual memory is a kind of memory management…
Q: Can you provide a subprogram example of parametric polymorphism?
A: The method of parametric polymorphism in programming languages makes it possible to define functions…
Q: 1. Explicitly calculate the first six val- ues of the factorial sequence using the formula 90 = 1…
A: The above question is solved in step 2:-
Q: Talk about a problem that a system's concurrent processing causes.
A: Concurrent operation: In order to improve efficiency and performance, concurrent processing entails…
Q: On the basis of your own experience, provide some instances of various physical education exercises.…
A: Physical effort is defined as any movement that causes your heart rate and respiration to increase.…
Q: List one advantage and one disadvantage of the Microkernel OS design vs the Monolithic OS design.…
A: List one advantage and one disadvantage of the Microkernel OS design vs the Monolithic OS design.…
Q: In order to provide a general picture of the use of agile methodology,
A: Answer in Step 2
Q: 235 U as The material that formed the earth was created in a supernova explosion approximately 6…
A:
Q: In order to provide a general picture of the use of agile methodology, analyze the findings of…
A: Given: The Agile paradigm encourages continual testing and iteration throughout a project's Software…
Control structures
Control structures are block of statements that analyze the value of variables and determine the flow of execution based on those values. When a program is running, the CPU executes the code line by line. After sometime, the program reaches the point where it has to make a decision on whether it has to go to another part of the code or repeat execution of certain part of the code. These results affect the flow of the program's code and these are called control structures.
Switch Statement
The switch statement is a key feature that is used by the programmers a lot in the world of programming and coding, as well as in information technology in general. The switch statement is a selection control mechanism that allows the variable value to change the order of the individual statements in the software execution via search.
Step by step
Solved in 5 steps with 2 images

- 1. Examine the following code segment. What will be printed?If there are any errors indicate the nature of each error.int a[7] = { 31, 12, 32, 14, 25, 16, 27 };int *ptr ;ptr = & a[ 2 ] ;for( i = 1; i <= 5; i = i + 2)cout << *( ptr + i ) ;cout << a[0] << *ptr << *ptr - 2 << *(ptr - 1)) << endl;Code (C++) that will print the message17.54 PRACTICE: Functions***: Output guitar tabs C++ An earlier problem introduced guitar tabs. In this problem, the user can enter a sequence of chords, and the program should output the tabs in sequence. The first input is the number of chords to follow. If the input is 4 G C G D, the output should be: e|-3-0-3-2- B|-0-1-0-3- G|-0-0-0-2- D|-0-2-0-0- A|-2-3-2--- E|-3---3--- Hints: Use 6 C++ strings, one for each guitar string ("string" below will mean C++ string unless otherwise noted). Start by the e string with "e|-", the B string with "B|-", etc. For each user chord, append (using append()) to each string the appropriate item (a number or -) plus -, like "2-". When done, print the 6 strings one at a time separated by newlines.
- 1. Examine the following code segment. What will be printed?If there are any errors indicate the nature of the error. int a[8] ={16, 12, 10, 7, 15, 18, 17, 29}; int *ptr ; ptr = & a[ 5 ] ; for(int i = 0; i<= 4; i = i + 2) cout<<a[i]<<*( ptr + i )<<endl; cout<<” ”<<a[1]<<” ”<<*ptr<<” ”<<*ptr + 2<<” ”<<*(ptr + 3);3.27 LAB: Login name Write a program that creates a login name for a user, given the user's first name, last name, and a four-digit integer as input. Output the login name, which is made up of the first six letters of the first name, followed by the first letter of the last name, an underscore (_), and then the last digit of the number (use the % operator). If the first name has less than six letters, then use all letters of the first name. Ex: If the input is: Michael Jordan 1991 the output is: Your login name: MichaeJ_1 Ex: If the input is: Nicole Smith 2024 the output is: Your login name: NicoleS_4Q#05: Write output of the following program and remove error if you find any#include <iostream>using namespace std;int main() {int numbers[5] = {7, 5, 6, 12, 35};cout << "The numbers are: ";for (i=1;;) {cout << n << " ";}cout << "\nThe numbers are: ";for (int i = 0; i < 5; ++i) {cout << " ";}return 0;}
- Write a10.25 LAB: Quadratic formula Implement the quadratic_formula() function. The function takes 3 arguments, a, b, and c, and computes the two results of the quadratic formula: x1=−b+b2−4ac2a x2=−b−b2−4ac2a The quadratic_formula() function returns the tuple (x1, x2). Ex: When a = 1, b = -5, and c = 6, quadratic_formula() returns (3, 2). Code provided in main.py reads a single input line containing values for a, b, and c, separated by spaces. Each input is converted to a float and passed to the quadratic_formula() function. Ex: If the input is: 2 -3 -77 the output is: Solutions to 2x^2 + -3x + -77 = 0 x1 = 7 x2 = -5.5021.7 LAB: Login name (Use python) Write a program that creates a login name for a user, given the user's first name, last name, and a four-digit integer as input. Output the login name, which is made up of the first five letters of the last name, followed by the first letter of the first name, and then the last two digits of the number (use the % operator). If the last name has less than five letters, then use all letters of the last name. Ex: If the input is: Michael Jordan 1991 the output is: Your login name: JordaM91 Ex: If the input is: Kanye West 2024 the output is: Your login name: WestK24
- Identify and correct the error int main(void) { double x = 12.8 double y Follow the code.6.23 LAB - Flip a coin Define a function named CoinFlip that returns "Heads" or "Tails" according to a random value 1 or 0. Assume the value 1 represents "Heads" and 0 represents "Tails". Then, write a main program that reads the desired number of coin flips as an input, calls function CoinFlip() repeatedly according to the number of coin flips, and outputs the results. Assume the input is a value greater than 0. Output the total number of 'Heads' and 'Tails' Hint: Use the modulo operator (%) to limit the random integers to 0 and 1. Ex: If the random seed value is 2 and the input is: 3 the output is: Tails Heads Tails Total Heads: 1 Total Tails: 2 Note: For testing purposes, a pseudo-random number generator with a fixed seed value is used in the program. The program uses a seed value of 2 during development, but when submitted, a different seed value may be used for each test case. The program must define and call the following function:string CoinFlip() Do Not Delete Any Existing…_code to be write:1.

