Which string will you be using: Bixby Here are some examples of string mod. The string: Bixby The size: 5 The string in reverse: ybxiB The string capitalized: BIXBY The string lowercased: bixby Which character in the string do you want to count: b We found 'b' 1 time (s). Erasing string... Here is the string now: Bye!
Which string will you be using: Bixby Here are some examples of string mod. The string: Bixby The size: 5 The string in reverse: ybxiB The string capitalized: BIXBY The string lowercased: bixby Which character in the string do you want to count: b We found 'b' 1 time (s). Erasing string... Here is the string now: Bye!
COMPREHENSIVE MICROSOFT OFFICE 365 EXCE
1st Edition
ISBN:9780357392676
Author:FREUND, Steven
Publisher:FREUND, Steven
Chapter4: Financial Functions, Data Tables, And Amortization Schedules
Section: Chapter Questions
Problem 8AYK
Related questions
Question
In C++
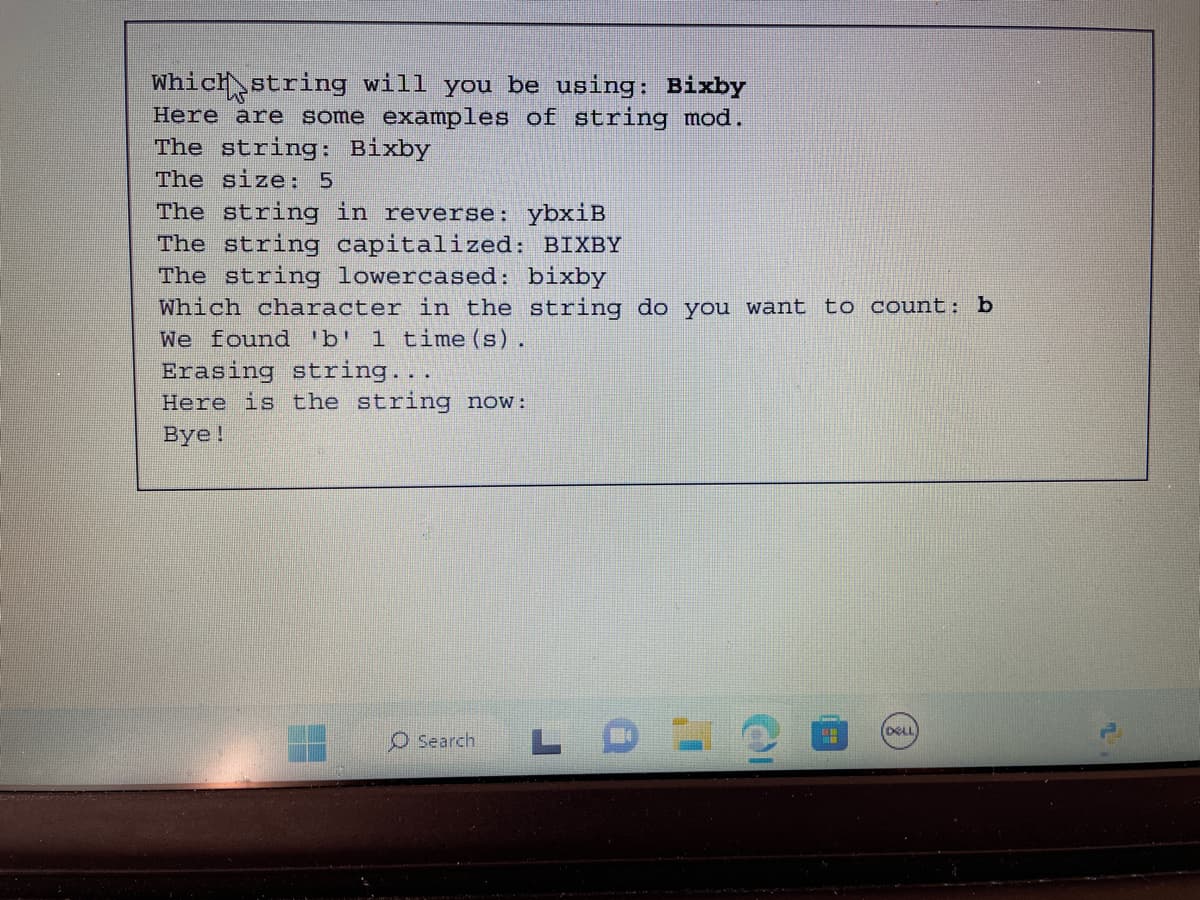
Transcribed Image Text:Which string will you be using: Bixby
Here are some examples of string mod.
The string: Bixby
The size: 5
The string in reverse: ybxiB
The string capitalized: BIXBY
The string lowercased: bixby
Which character in the string do you want to count: b
We found 'b' 1 time(s).
Erasing string...
Here is the string now:
Bye!
O Search L
OI
HH
(DELL
Transcribed Image Text:%
5
-
F5
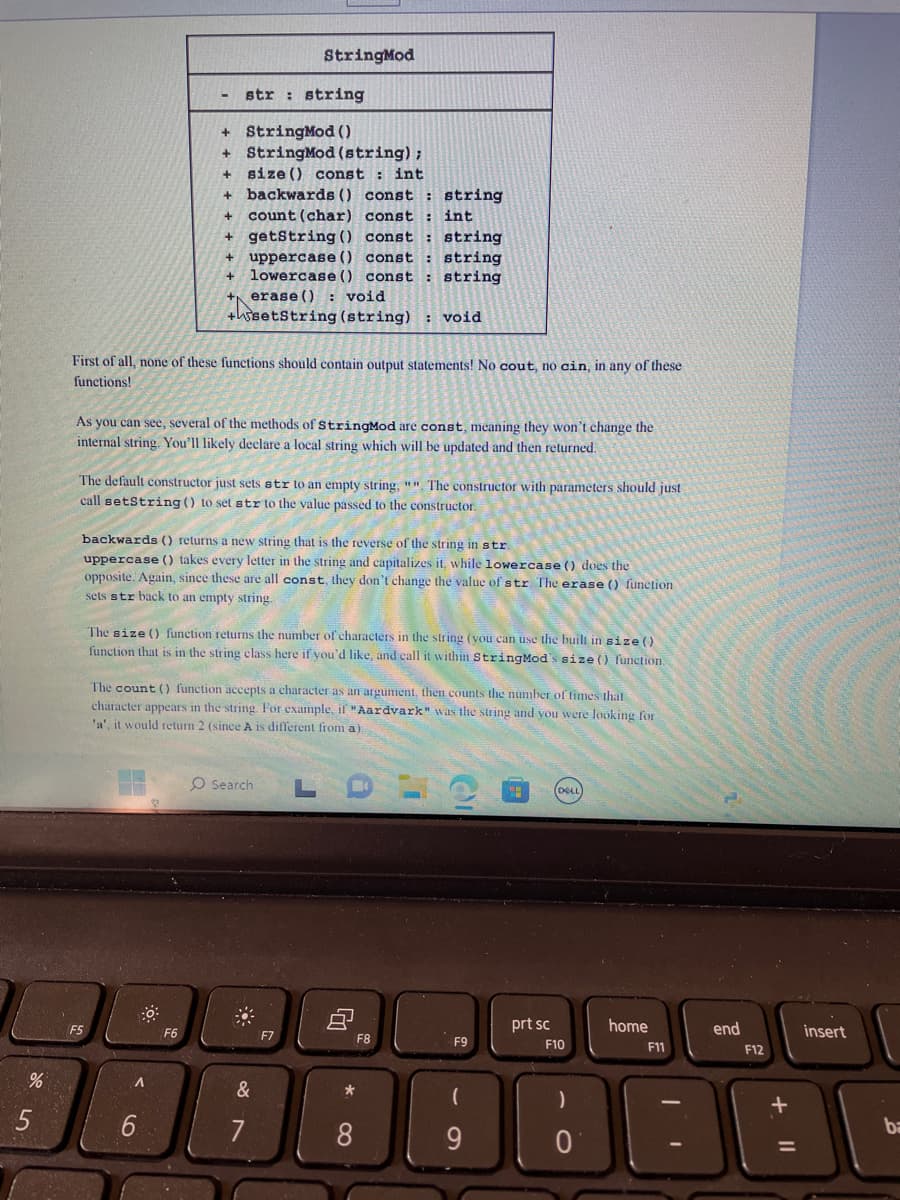
First of all, none of these functions should contain output statements! No cout, no cin, in any of these
functions!
str string
As you can see, several of the methods of StringMod are const, meaning they won't change the
internal string. You'll likely declare a local string which will be updated and then returned.
+ StringMod ()
+ StringMod (string);
+
size () const int
+
backwards () const: string
+ count (char) const
int
+ getString() const
string
+ uppercase () const. : string
+
lowercase () const string
The default constructor just sets str to an empty string, "". The constructor with parameters should just
call setString() to set str to the value passed to the constructor.
A
+ erase (): void
+setString (string): void
backwards () returns a new string that is the reverse of the string in str.
uppercase () takes every letter in the string and capitalizes it, while lowercase () does the
opposite. Again, since these are all const, they don't change the value of str. The erase () function
sets str back to an empty string.
6
StringMod
F6
The size () function returns the number of characters in the string (you can use the built in size ()
function that is in the string class here if you'd like, and call it within StringMod's size () function.
The count() function accepts a character as an argument, then counts the number of times that
character appears in the string. For example, if "Aardvark" was the string and you were looking for
'a', it would return 2 (since A is different from a).
O Search
&
7
F7
8
*
8
F8
F9
(
9
prt sc
(DELL)
F10
)
0
home
F11
end
F12
+
insert
ba
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

COMPREHENSIVE MICROSOFT OFFICE 365 EXCE
Computer Science
ISBN:
9780357392676
Author:
FREUND, Steven
Publisher:
CENGAGE L

Programming with Microsoft Visual Basic 2017
Computer Science
ISBN:
9781337102124
Author:
Diane Zak
Publisher:
Cengage Learning

COMPREHENSIVE MICROSOFT OFFICE 365 EXCE
Computer Science
ISBN:
9780357392676
Author:
FREUND, Steven
Publisher:
CENGAGE L

Programming with Microsoft Visual Basic 2017
Computer Science
ISBN:
9781337102124
Author:
Diane Zak
Publisher:
Cengage Learning