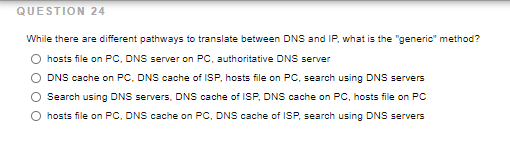
While there are different pathways to translate between DNS and IP, what is the "generic" method? hosts file on PC. DNS server on PC, authoritative DNS server DNS cache on PC. DNS cache of ISP, hosts file on PC, search using DNS servers Search using DNS servers. DNS cache of ISP, DNS cache on PC, hosts file on PC hosts file on PC, DNS cache on PC, DNS cache of ISP, search using DNS servers
Q: Assume Host C is running a Web server on port 80. Assume that Hosts A and B are currently submitting…
A: A web server processes and replies to HTTP and other client requests. The primary function of a web…
Q: What does a cybersecurity analyst know about their target if they receive a RST packet back from a…
A: 1. The target is active but the port is closed if you get an RST (reset) packet back from it. If no…
Q: Each of the following is true regarding TCP SYN port scanning except_______. a. it uses FIN…
A: To be determine: Select right option
Q: While there are different pathways to translate between DNS and IP, what is the "generic" method? O…
A: Domain Name System(DNS) is just as important as fast content. DNS translates the common domain name…
Q: Question 1: Which of the followings are characteristics for RADIUS or TACACS+ servers? It uses TCP…
A: Below I have provided the solution of both 1 and 2 questions
Q: Assume that routing works in the diagram shown below. PC1 sends an ICMP ECHO request to PC2. Which…
A: For sending data packets from one system to another system, intermediate routers are used. These…
Q: Why can traditional networking security devices NOT be used to block Web application attacks? a.…
A: To be determine: Select right option
Q: As shown in the figure below, computer A will send a data packet to computer B, which is in a…
A: Given network diagram contains 2 different networks which are connected through a Router R and each…
Q: a- Given the following screenshot, some errors are preventing PC-C from accessing the Redundant…
A: Introduction: In part a we are provided with few lines of code and we have to remove errors from it.…
Q: the number of available addresses on a network by the Supernetting hosts ID. 16 Choose one a.…
A: Supernetting is a process of combining small networks into big networks. It is also called as…
Q: Suppose the destination not stored in the MAC table, what wvill happen no option is correct the…
A: The correct option is option c) the switch will send request to all except the port that is came…
Q: Face Pal FTP Fa SMARTPHONEFT PC The network address 172.30.10.0/24 is given. You need to design the…
A: Answer:- VLAN10[Students] Subnet Address First usable address Second usable address Subnet…
Q: Since a gateway (NAT) router only has one public IP address, but may forward packets from many…
A: We are going to understand how NAT works and how NAT could remember these many IP addresses to…
Q: Consider the following topology. iMac2 wants to send a file to iMac3. iMac2 knows the destination IP…
A: Each device that is integrated into a computer network requires a network adaptor. This adapter…
Q: Which Scopes is used to assign IPV4 address pools for Class A, B, and C networks in a DHCP Server,…
A: Normal Scope - Allows A, B and C Class IP address ranges to be specified including subnet masks,…
Q: Godwin Pharmaceuticals has a private web server for its corporate network that runs on a Linux…
A: Let's understand step by step : (1) SSH SSH stands for Secure Socket Shell which provides a…
Q: nswer the following questions and show the calculations 1. Host-A has the IPV4 address and subnet…
A: The solution is given in next step:-
Q: Which of the following is the main difference between TCP and UDP? O UDP is slower because it has…
A: EXPLANATION: TCP is slower than UDP, which is one of the main differences between the two…
Q: plement a network service involving sockets where servers and clients authenticate themselves and…
A: This module provides access to the encryption and peer authentication functions of Transport Layer…
Q: Attempt all Questions:- Part 1) Assign IP address configuration to the S2 server: part 1 question)…
A: According to the information given:- We have to follow the instruction in order to assign address…
Q: PC1 PC2 S1 GO/0/0 GO/0/1 S2 .1 Looking for a DHCPV4 server. I cannot forward broadcasts between…
A: Given: To configure interface in VLAN
Q: Choose the resource record of DNS Server which represents the IPV6 address 2005:1421:34:56D::5 in…
A: Hey there, I am writing the required solution based on the above given question. Please do find the…
Q: What would the command route del default gw 192.168.5.1 eth1 accomplish on your Linux workstation?…
A: The command route del default gw 192.168.5.1 eth1 do Remove the workstation's route to the default…
Q: Your company has been assigned the following IP address by IANA: 135.120.0.0. Design a network…
A: The number of bits required so that each host has at least 60 hosts are 2^6 -2 = 62, so at least 6…
Q: Figure 3 shows a LAN topology. Assume that no port security implemented on both switches. The…
A: Below I have provided the answer to the given LAN Topology.
Q: Lab - Build a Simple Network Topology Addressing Table Device Interface IP Address…
A: Given The answer is given below.
Q: Host A sends a UDP datagram containing 8880 bytes of user data to host B over an Ethernet LAN.…
A: The Answer is in Below steps
Q: Dont copy from any source and also from internet I will surely downvote the answer only answer if…
A: The answer is..
Q: The maximum value of a TTL for a DNS resource record (RR) is 2147483647 seconds. What is the primary…
A: The answer is
Q: IV-Refer to the below exhibit. a- Using 172.16.0.0/16 network address, can we allocate IP's using…
A:
Q: Host A sends a UDP datagram containing 8880 bytes of user data to host B over an Ethernet LAN.…
A: The Answer is
Q: Provide a filter table (similar to table 8.6 in lecture notes 32) that is as restrictive as possible…
A: Filter table: The filter table is used to accept all internal users to establish SSH sessions with…
Q: What is one advantage offered by VDI over RDS and VNC? Offers access to multiple OSs in VMs…
A: 4. Provides open source flexibility VDI offers us an option to Bring Your Own Device (BYOD), also…
Q: MCQ: Which of the following is a better solution to defend DoS attack in a network? a. Packet…
A: Better solution to defend DoS attack in a network
Q: Question 1: Which of the followings are characteristics for RADIUS or TACACS+ servers? It uses TCP…
A: Question 1 and Question 2 answers are given below
Q: a- Given the following screenshot, some errors are preventing PC-C from accessing the Redundant…
A: Introduction: In part a we are provided with few lines of code and we have to remove errors from it.…
Q: You are creating a VPN infrastructure in a test lab to use only L2TP for VPN server running on…
A: Here's the solution:
Q: VLANs exhibit which of the following features? (Choose two.) One VLAN is a single broadcast domain.…
A: VLAN stands for Virtual Local Area Network and it is a subnetwork which groups the collection of…
Q: In the context of DHCP what is the purpose of an IP helper address? a. The gateway for the…
A: In the context of DHCP what is the purpose of an IP helper address is below explained.
Q: ***** When the load is greater than the capacity, the delay.. b. Increases linearly c. Goes to…
A: 1) C option is correct that is: Goes to infinity Explanation: Packets become blocked at nodes when…
Q: Should DHCP be used to set up server ip? True False QUESTION 17 RSA is a public cryptography…
A: NOTE: SINCE THE QUESTION IS MULTIPART WE ARE ADVISED TO DO ONLY FIRST THREE PARTS: 1. The statement…
Q: Suppose you are the network security administrator of a well-known company. Your boss has…
A: 1. Do you think it is feasible to implement a VPN between the two companies having multiple sites?…
Q: A DNS zone transfer occurs over which of the following ports? UDP 67 O UDP 123 О ТСР 53 O TCP 110…
A: The solution is given in next step
Q: Question 6 Which of the following statement is true regarding ARP protocol? A) Host A can use ARP to…
A: The solution to the given problem is below.
Q: Dont copy from any other source or internet I Will Surely downvote answer only if you have…
A: The answer is..
Q: 1.What does the traceroute command show? Group of answer choices A. The path taken by packets to its…
A: Answer the above questions are as follows:
please answer question
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- THINKING CRITICALLY Which of the following hosts on a corporate intranet are on the same subnet? a. b. c. d.In what ways might DNS tunneling be blocked? How can you recognize port scanning attempts and block them? DDoS and Mitigation Strategies: Encryption vs. Hashing What is TCP/IP? To what end should DNS be watched? Why is TCP/IP related to MAC addresses and ARP? WAF? Distinctions in policy, procedure, and guidelines Inquire about and propose the following IOCs:1. What is the purpose of implementing a DHCP server on a network? [Choose all that apply] Automatically assign a DNS server address to a host Let a host automatically connect to resources on the network Dynamically allocate IP addresses to hosts on the network Resolve IP addresses to hostnames Automatically join a host to the domain 2. After installation of the DHCP server role, why is it necessary to restart the DHCP service? a. To ensure the role was successfully installed b. To ensure the credentials that were stipulated is applied c. To ensure the DHCP service is running d. To assign IP addresses to hosts 3. On which server will the DHCP server role normally be installed? a. Domain Webserver b. Domain Controller c. Domain Member Server d. Domain Client
- dont answer copying from another source or internet I will downvote for sure in that case Answer only you have accurate knowledge Otherwise will surely downvote Host A (with IP address 172.16.2.4) wants to communicate with Host B (with IP address 172.16.3.5). If the subnet mask for Host A is 255.255.0.0, will the hosts communicate using local transmissions or will they send information to the default gateway? Show the workings for the ANDing process below. Host A (with IP address 172.16.2.4) wants to communicate with Host B (with IP address 172.16.3.5). If the subnet mask for Host A is 255.255.0.0, will the hosts communicate using local transmissions or will they send information to the default gateway? Show the workings for the ANDing process below. Source IP Source Subnet Mask AND Result Destination IP Source Subnet Mask AND ResultDont copy from any other source or internet I Will Surely downvote answer only if you have accurate knowledge otherwise dont answer other wise will receive surely downvote Host A (with IP address 192.168.0.10) wants to communicate with Host B (with IP address 192.168.20.2). If the subnet mask for Host A is 255.255.255.0, will the hosts communicate using local transmissions or will they send information to the default gateway? Show the workings for the ANDing process below. Host A (with IP address 192.168.0.10) wants to communicate with Host B (with IP address 192.168.20.2). If the subnet mask for Host A is 255.255.255.0, will the hosts communicate using local transmissions or will they send information to the default gateway? Show the workings for the ANDing process below. Source IP Source Subnet Mask AND Result Destination IP Source Subnet Mask AND ResultAttempt all Questions:- Part 1) Assign IP address configuration to the S2 server: part 1 question) Write IP-Address, Net mask and Default gateway. Part 2) To assign an IP address to the subnet A and to the subnet B you to have subdivide the network 169.1.96.0/19. Please choose a new netmask that subdivide the given network into atleast 3 (one for future use) subnetworks. You want to have a maximum amount of computer in each subnetwork. part 2 question) Write Net-mask (decimal dotted notation), your subnet A IP Address, Your subnet B IP Address, IP address R2 eth1 and IP Address R2 eth2. Part 3) Write down routing table of R1 (Routing table should include Destination, Next hoop and interface) Part 4) Write down routing table of R3 (Routing table should include Destination, Next hoop and interface) You are planning the network of a small company. The network has the address \( 169.1 .0 .0 / 16 . \) T some structure subnet
- Just need answer, no explanation: 1) SSL/TLS encrypts communications at which layer? Network layer Physical layer Application layer Transport layer 2) When using HTTPS, the source and destination IP addresses are encrypted. True False 3) Which Phase of the SSL/TLS Handshake is optional? Phase 2: Server Authentication and Key Exchange Phase 1: Client and Server Hello Phase 4: Wrap-up Phase 3: Client Authentication and Key Exchange 4) The HSTS flag is used to protect against which type of threat? A man-in-the-middle attacker who intercepts HTTPS requests and rewrites them as HTTP requests A phishing attacker who impersonates a legitimate website A man-in-the-middle attacker who presents forged SSL certificates in order to intercept communications A man-in-the-middle attacker who forces downgrades to outdated encryption versions used in TLSGiven an IP address 94.0.0.0/20, answer the following questions: I. What is the IP address class? II. Netid and hosted? III. Number of bits borrows? IV. Number of total subnets created? V. Number of bits left? VI. Number of host per subnet? VII. Total of host for all subnets? VIII. The new subnet mask? (after subnetting) IX. Show the subnet address, host range and broadcast address of the first and the last block of the subnet created.QUESTION 25 As a network administrator, Joshua is helping a nearby library set up a local network. He manually assigns an IPv6 address, as well as a default gateway and DNS server, to each Windows 10 computer using the Network and Sharing Center. Which of the following is true of this configuration? a. Script commands were used to configure the IPv6 settings. b. The network interface in each computer is assigned a link-local unicast address. c. It is a stateless automatic address configuration. d. Each computer in the network is assigned a static IP address.
- Correct and detailed answer will be Upvoted else downvoted Host A sends a UDP datagram containing 8880 bytes of user data to host B over an Ethernet LAN. Ethernet frames may carry data up to 1500 bytes (i.e. MTU = 1500 bytes).Size of UDP header is 8 bytes and size of IP header is 20 bytes.There is no option field in IP header. How may total number of IP fragments will be transmitted and what will be the contents of offset field in the last fragment?Dont copy from any source and also from internet I will surely downvote the answer only answer if you have accurate knowledge otherwise i will surely downvote Host A (with IP address 172.16.2.4) wants to communicate with Host B (with IP address 172.16.3.5). If the subnet mask for Host A is 255.255.0.0, will the hosts communicate using local transmissions or will they send information to the default gateway? Show the workings for the ANDing process below. Host A (with IP address 172.16.2.4) wants to communicate with Host B (with IP address 172.16.3.5). If the subnet mask for Host A is 255.255.0.0, will the hosts communicate using local transmissions or will they send information to the default gateway? Show the workings for the ANDing process below. Source IP Source Subnet Mask AND Result Destination IP Source Subnet Mask AND ResultUsing the Nmap tool complete the following tasks and store the outcome into a text file: Scan the open ports of an IP in your network domain (for 192.168.1.102) Scan all the machines in your network and list the available open ports. Create a list of target IP and scan these IP address for open ports and Operating System (OS) details.

