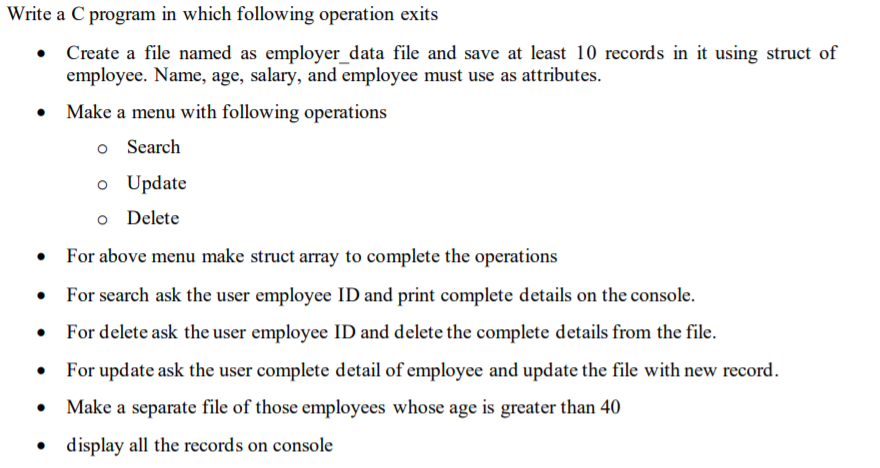
Write a C program in which following operation exits • Create a file named as employer_data file and save at least 10 records in it using struct of employee. Name, age, salary, and employee must use as attributes. Make a menu with following operations O Search o Update o Delete For above menu make struct array to complete the operations . For search ask the user employee ID and print complete details on the console. For delete ask the user employee ID and delete the complete details from the file. For update ask the user complete detail of employee and update the file with new record. • Make a separate file of those employees whose age is greater than 40 display all the records on console
Write a C program in which following operation exits • Create a file named as employer_data file and save at least 10 records in it using struct of employee. Name, age, salary, and employee must use as attributes. Make a menu with following operations O Search o Update o Delete For above menu make struct array to complete the operations . For search ask the user employee ID and print complete details on the console. For delete ask the user employee ID and delete the complete details from the file. For update ask the user complete detail of employee and update the file with new record. • Make a separate file of those employees whose age is greater than 40 display all the records on console
Programming with Microsoft Visual Basic 2017
8th Edition
ISBN:9781337102124
Author:Diane Zak
Publisher:Diane Zak
Chapter8: Arrays
Section: Chapter Questions
Problem 7E
Related questions
Question
Transcribed Image Text:Write
• Create a file named as employer_data file and save at least 10 records in it using struct of
employee. Name, age, salary, and employee must use as attributes.
• Make a menu with following operations
o Search
a C program in which following operation exits
●
For above menu make struct array to complete the operations
For search ask the user employee ID and print complete details on the console.
For delete ask the user employee ID and delete the complete details from the file.
For update ask the user complete detail of employee and update the file with new record.
• Make a separate file of those employees whose age is greater than 40
display all the records on console
●
o Update
o Delete
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Programming with Microsoft Visual Basic 2017
Computer Science
ISBN:
9781337102124
Author:
Diane Zak
Publisher:
Cengage Learning

Programming with Microsoft Visual Basic 2017
Computer Science
ISBN:
9781337102124
Author:
Diane Zak
Publisher:
Cengage Learning