Write a complete C++ program that takes 10 integers from the user and stores them in an array by uing a for loop. The program should find the sum of the integers at even indexes (including index 0), and then multiply each integer in the array with the sum. The program should then print the new values in the array. Sample run: Enter values: 2 517 346 98 10 Sum of the numbers at even indexes is 20 New values in the array: 40 100 20 140 60 80 120 180 160 200
Write a complete C++ program that takes 10 integers from the user and stores them in an array by uing a for loop. The program should find the sum of the integers at even indexes (including index 0), and then multiply each integer in the array with the sum. The program should then print the new values in the array. Sample run: Enter values: 2 517 346 98 10 Sum of the numbers at even indexes is 20 New values in the array: 40 100 20 140 60 80 120 180 160 200
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter7: Arrays
Section7.3: Declaring And Processing Two-dimensional Arrays
Problem 4E: (Practice) Write a C++ program that adds equivalent elements of the two-dimensional arrays named...
Related questions
Question
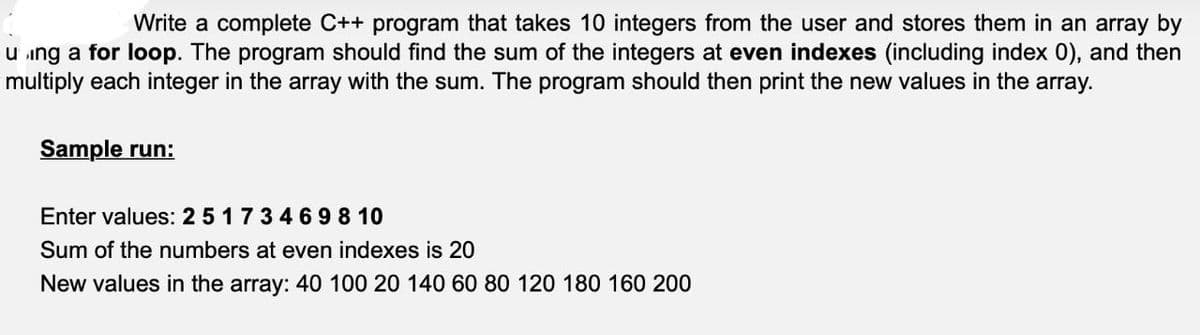
Transcribed Image Text:Write a complete C++ program that takes 10 integers from the user and stores them in an array by
using a for loop. The program should find the sum of the integers at even indexes (including index 0), and then
multiply each integer in the array with the sum. The program should then print the new values in the array.
Sample run:
Enter values: 2 5 1 7 3 4 6 98 10
Sum of the numbers at even indexes is 20
New values in the array: 40 100 20 140 60 80 120 180 160 200
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 4 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning