Write a Python function
Q: Consider the evolution of the internet throughout time as well as the present technological…
A: The current objective is to outline the growth of the Internet. In 1965, two computers at MIT…
Q: What are some of the most significant distinctions between the Internet and the World Wide Web (WWW)…
A: The Answer is biggest but you can understand shortly like this :-
Q: When converting from on-premises servers to an laaS design, are there any governance challenges?
A: Architecture for IaaS: With the IaaS model, cloud a providers host infrastructure such servers,…
Q: ADD reg, reg ;3 clock cycles ADD reg, immed; 2 clock cycles LOOP_LabelName; 8 clock cycles Assume…
A: The answer is
Q: Consider the evolution of the internet throughout time as well as the present technological…
A: The current mission at hand is to provide a history of the evolution of the Internet. In 1965, two…
Q: the operating system's capabilities on a desktop computer
A: Introduction: Mobile computing allows us to access information and data via a mobile device, whereas…
Q: What are some of the most significant distinctions between the Internet and the World Wide Web (WWW)…
A: When compared to one another, this question demonstrates how the World Wide Web differs from the…
Q: What string is the longest contiguous sequence fo the following strings (Note: not the number but…
A: As the programming language is not mentioned here, we are using JAVA The code is given below with…
Q: how to use and get access to programmes and services housed in the cloud.
A: According to the information given:- We have to define the use and get access to programs and…
Q: Which of the following ports provide power to the Raspberry Pi? Is it an HDMI port, a Micro USB…
A: A raspberry pi has many ports in it for various functions.
Q: le container in our inferior hash map (that is, they are all in the same LinkedList). The goal of a…
A: Introduction: Hash tables are groups of things in an order that allows them to be easily found after…
Q: When building an open hash table with usable functionality, you should take the following factors…
A: Hashtable hash A hash table represents hashed data as an array with each element carrying a distinct…
Q: Which firewall construction style has emerged as the de facto norm for companies operating in the…
A: Introduction: With DMZ, screened subnet firewall: screened subnet firewallNowadays, the firewalls…
Q: Which firewall setup is now most common among companies? Why? Explain.
A: Firewall: It is a network security appliance that monitors and filters incoming and outgoing…
Q: When shifting your IT operations to the cloud, where should you look for governance issues?
A: According to the information given:- We have to describe when shifting your IT operations to the…
Q: Using examples from the actual world, discuss the variations between a web server and web client…
A: The variations between web server and web client software is given below with actual world examples
Q: Has the transition from on-premise servers to an laaS architecture raised any governance concerns?
A: The charity administration employs the infrastructure as a service (IaaS) deployment paradigm to…
Q: Explain briefly why non-formal standard software development methodologies won't be useful for…
A: Definition A non-formal technique of software development is one that relies on the opinions of many…
Q: Which of the following code snippets represents well-written code and the best desi problem (assume…
A: For the given all the code Ans (B) is correct ans
Q: Memory is divided into two categories: RAM and Register
A: Introduction RAM and Registers area unit differing types of memory.RAM :Random Access Memory(RAM)…
Q: When moving from on-premises servers to an IaaS architecture, what governance concerns should you be…
A: IaaS Architecture: With the IaaS model, cloud providers host servers, storage, networking, and…
Q: A file manager is what? Describe the Windows Explorer software in detail. Include a few places for…
A: The Answer is :-
Q: Which of the following ports provide power to the Raspberry Pi? Is it an HDMI port, a Micro USB…
A: The answer of the question is given below
Q: How does virtualization operate when used with cloud computing
A: How does virtualization operate when used with cloud computing? What precisely is it?
Q: How does SOA work and what exactly is it?
A: We need to discuss soa and its work.
Q: What improvements and alterations have been made to each new generation of networking technology,…
A: Technology 1G: the first generation, or 1G. It may function as a separate carrier in mobile phones.…
Q: How can a network prosper and reach its potential if these three requirements are not met? In as few…
A: Introduction: Genuine interest in their connections is shown in successful networking relationships,…
Q: How many IPv4 addresses are there in total? The IPv4 address's lifespan has been extended through…
A: We need to write the number of IPv4 addresses in total. Then, we need to discuss if we need to…
Q: How can the effects of cross-level moderating be investigated using formative scales?
A: Introduction: The cross-level moderating effect is comprised of two types of levels. Individual and…
Q: Compiler and interpreter comparison
A: Compiler: Compilers are software tools that convert high-level programming language code into…
Q: If you accidentally delete a file and then decide you want it to be restored, what should you do
A: If you accidentally delete a file and then decide you want it to be restored, you should use a file…
Q: for the first time but don't see any indicator lights or hear the sound of a spinning disk, does it…
A: the problem is in a hardware side
Q: Create a program in Python that will simulate the BST Inorder Traversal using the given tree: 2 7 o…
A: Here is the python code. see below step for code.
Q: Q2: Complete the main programs and writing its functions, classes and find the Area for each shape:…
A: The following steps need to be taken for the given program: Create a Triangle class with a…
Q: in cryptocurrency! Unfortunately, its value is tanking and decreasing in value at an annual rate of…
A: the code is an given below :
Q: What does "parallel processing" really imply when it is used?
A: Parallel processing - In computing, parallel processing refers to the use of two or more processors…
Q: The sequencing of assembly language instructions may be designed into compilers and assemblers to…
A: Introduction: The device does not support certain combinations of instructions (two instructions in…
Q: flat-curved screen's form on an LCD-based computer mon
A: Explaining the flat design of the LCD monitor screen used in computers These monitors are extremely…
Q: How does virtualization operate when used with cloud computing? What precisely is it
A: Virtualization is known to create a virtual (rather than actual) version of something, such as a…
Q: The benefits and drawbacks of magnetic and solid-state secondary storage systems should be compared…
A: Secondary storage systems use various kind of mechanisms to store data in them.
Q: Which of the following, in the Internet of Things, converts an electrical signal into a physical…
A: The answer is given below step.
Q: Multiprocessor systems provide more versatility in addition to other advantages. This advantage…
A: introduction: Two-dimensional materials may be less brittle because of their flexibility since they…
Q: Can the terms "Internet" and "World Wide Web" be distinguished from one another?
A: According to the information given:- We have to distinguished the terms "Internet" and "World Wide…
Q: Review these A reference is another name given to a variable in memory of the same data type A…
A: I am writing in comments how each code is executed and finally getting output.
Q: One of its key benefits is the availability of customizable multiprocessor systems. Despite its…
A: Symmetric multiprocessing: Multiple processors share a single operating system and memory in…
Q: Identify the relational keys for each table. List each relational key in a separate line. Candidate…
A: A column or group of columns known as a scorecard is a key in a database which identifies the…
Q: Why is it so important to have a repair manual on hand while disassembling a notebook?
A: Repair manual is a guide book which is given my the manufacturer with the laptop/pc/notebook which…
Q: Define a function called get_predecessor() which takes a Node object and a value as parameters. The…
A: Here is the python code: See below for code:
Q: Using conditional operators to determine whether a year is a leap year or not. All years earlier…
A: I give the code in c# along with output and code screenshot
Q: What sorts of technological systems exist and how far has technology advanced recently?
A: How far technology has advanced: If innovation is not employed, the world has really changed into an…
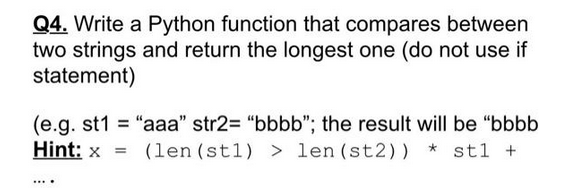
Step by step
Solved in 2 steps with 1 images

- 0_2. 4.Write a python program that takes an input from a user which is a sequence of any characters. Pass the input as an argument to a function. Your function should modify the given string by the user in such a way that a character does not exist in the string consecutively for more than 3 times and then return the modified string.Sample 1 input:aaaaabbbbccsshak,ckaSample output 1:aaabbbccsshak,cka..Write a function called repeater(s1, s2, n) that given two strings s1 and s2 and an integer n returns a string that starts with an underscore ('_'), then s1 and s2 alternate n times, then ends with an underscore. Please do not use loops.Please implement the function both_ends(s). Given a string s, return a string made of the first 2 and the last 2 chars of the original string, so 'employee' yields 'emee', and ’er’ yields 'erer' (since the first 2 and the last 2 chars are both 'er') However, if the string length is less than 2, return instead the empty string. The function takes a string s as its argument. Please write python code
- with Python Write a function that will allow the user to scramble a sentence given a stride, take the first portion for the stride, then the next portion for the given stride.... for example, Eric Charnesky with stride 4 #e rkrcnyihecas #'e r i c c h a r n e s k y' # 0 1 2 3 4 5 6 7 8 9 10 11 12 13Write a short Python function, first_and_last(data), that takes a sequence of one or more strings, and returns the first and last string lexicographically, in the form of a tuple of length two. Do not any built-in functions for your comparisons/determination of string ordering.Write a Python function called is_palindrome that takes a string as input and returns True if the supplied string is a palindrome or False if not. For our purposes, a palindrome is any string that: ● reads the same backwards and forwards, ignoring letter case and spaces*, and ● is at least 2 characters** in length. *For example, “Radar” is a palindrome even though the first letter is uppercase but the last letter is lowercase. The phrase “taco cat” should also be considered a palindrome because it reads the same backwards and forwards when the space is ignored. **This includes non-letters, such as punctuation and numbers. For example, “!radar!” would be considered a palindrome. Example function output: is_palindrome(“madam Im adam”) # True is_palindrome(“a”) # False is_palindrome(“RADar”) # True
- Write a function that keeps computing the sum of the digits of x^n, until there is only one digit left. For example, sumOfDigits(2,5) returns 5, because 2 ^ 5 = 32 = 3 + 2 = 5 Another example, sumOfDigits(2,8) returns 4, because 2 ^ 8 = 128 = 1 + 2 + 8 = 13 = 1 + 3 = 4Please answer it in python write a function Tuesday, words of even length must be repeated 6 times, separated by a dash, while thewords of odd length should be repeated 3 times, separated by commas. Write the function tuesday thattakes a word as an argument and returns the string according to the Tuesday rule. (lengthof a character string is given by len(string).Write a function that adds two digit-strings in base b, where 2 <= b <= 10. Each string may be as long as one million digits, and strings must be of equal length. Return the sum in a string that uses the same number base. Preferred: C++
- In Python, write a function named cipher that takes a string. The function returns that string in a ciphered form by using the ord of the first letter of the string to cipher each letter including the first letter. Hence for abc, use the ord of 'a', and add it to the ord of 'a' and convert that result to a character use the chr function. This character should be concatenated to the same action on the letter b and so on. Hence the function returns: chr(ord('a')+ord('a')) + chr(ord('a')+ord('b')) + chr(ord('a')+ord('c')).Obviously you need a loop to iterate on each letter. Write another function to decipher (do the opposite of the previous function), given a string and returns the deciphered string. Obviously, the first letter's ord is halved to find the first letter, and that value is used to decipher the remaining letters. From main, write code to get a string, as input, then call the cipher function and print its output.Then call the decipher function and display its output. The…In Python, Create a function that accepts a string as input. The function will take the initial character in a string and replace it with @ for all subsequent characters that match it (except the first character.) The new string will be printed by the function. Sample String: : ‘character’, ‘babble’, ‘sassy’ Sample Output: 'chara@ter’, ‘ba@@le’, ‘sa@@y’Write a python function that takes a string as a parameter. Then your function will check the ascii value of each character present in the string and form a new string containing only the EVEN valued characters. Then, return the newly formed string and finally print the returned value in the function call.Here, an even valued character is a character whose ascii value%length of the string is even.================================================Sample Input 1:holaSample Function Call 1:function_name("hola")Sample Output 1:hlExplanation 1:Length of "hola" is 4.ASCII of ‘h’ is 104. So, 104%4=0 which is even. So, add it to the new string.ASCII of ‘o’ is 111. So, 111%4=3 which is odd. So, do not add it to the new string.ASCII of ‘l’ is 108. So, 108%4=0 which is even .So, add it to the new string.ASCII of ‘a’ is 97. So, 97%4=1 which is odd. So, do not add it to the new string.================================================Sample Input 2:"bye"Sample Function Call…



