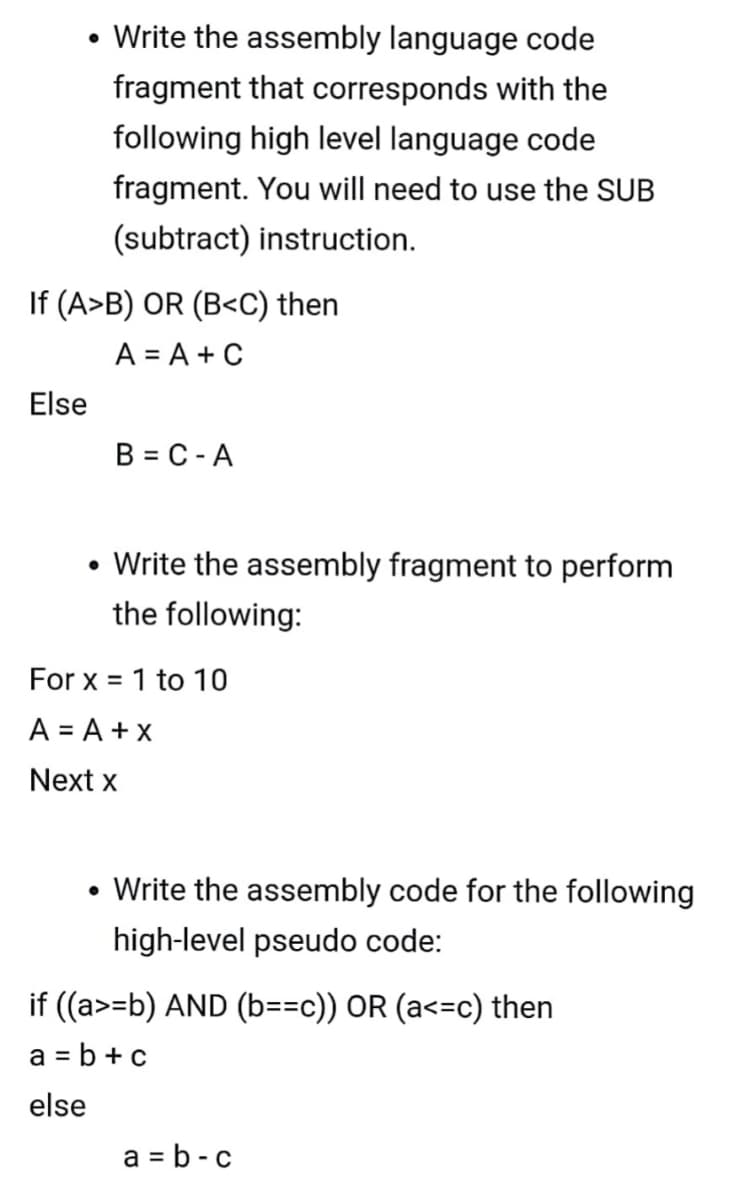
• Write the assembly language code fragment that corresponds with the following high level language code fragment. You will need to use the SUB (subtract) instruction. If (A>B) OR (B=b) AND (b==c)) OR (a<=c) then a = b +c else a = b - c
Q: Is moving to a cloud-based platform difficult for businesses? What are the risks and rewards of…
A: A cloud platform is a server's operating system and hardware that is physically located in a data…
Q: Discuss the social and ethical aspects of using and deploying information technology. Computer…
A: Answer: How Information technology achieves a competitive edge, both personally and…
Q: What can you do as a system administrator to protect the safety of your data?
A: System Administrator: A system administrator, often known as a sysadmin or admin, is a person who is…
Q: Descriptive models possess many critical characteristics and behaviors, which we shall describe in…
A: DESCRIPTIVE MODEL - Descriptive research is a type of research approach that explains all of the…
Q: What is one critical point to remember while removing rows, columns, and tables?
A: When Ethernet was first introduced, Originally using coaxial cable as a transmission medium,…
Q: A common practice was to aggregate large volumes of ungrouped data into intervals of our own design.…
A: Given: - Working in a group vs working alone has both benefits and downsides. Working in a group is…
Q: Vhy is automation dependent on knowledge information technology?
A: Computers and telecommunication are used to store and share information in information technology.…
Q: WorkArea Results Given an int variable k that has already been declared, write some code that uses a…
A: As I am writing the code in my local system, so I have first of all declared a variable k. Next, I…
Q: What techniques do social engineering hackers employ in order to obtain knowledge about a user's…
A: Introduction: Social engineering (sometimes known as social engineering) is a method of deceiving…
Q: What does the word "security" mean in terms of technology? When it comes to present day physical…
A: Thus, security in technology entails safeguarding all of our data against outsiders.Information…
Q: The Agile Manifesto guides the Agile Group of Software Engineers. Make mention of the Agile…
A: Introduction: When it comes to software development, the Agile Manifesto is made of four basic…
Q: What is the significance of fine-grained multithreading?
A: Introduction: What is the significance of fine-grained multithreading?
Q: Examine the opposing viewpoints on how to define "information technology." Which of them (in terms…
A: Informatics, often known as information technology, uses computers and telecommunications systems to…
Q: The document used to propose the hardware and software requirements for a new system is known as?
A: Intro There is one particular document which is used for proposing the hardware and software…
Q: A well-designed algorithm should be free of ambiguity." briefly describe
A: Algorithm: The algorithm is a step-by-step process. Given that A well-designed algorithm should be…
Q: "In formation technology is a benefit," compose a brief paragraph.
A: Information technology: Information technology (IT) is the creation, processing, storage, security,…
Q: Is AWS superior than a server, and if so, why?
A: Intro Reliability. AWS and dedicated servers are each reliable. AWS may be a cloud computing…
Q: What role does a TPM play when it comes to whole-disk encryption?
A: Answer: TPM: Trusted Platform Module (TPM) technology is intended to provide hardware-based security…
Q: Explain the hosting of cloud-based network services and applications.
A: Introduction: Cloud computing is a type of cloud computing in which multiple servers are joined…
Q: What exactly is data communication? What are the essential elements of a data communication system…
A: Introduction Data is made up of basic facts that are processed to provide information. Text,…
Q: I will address the present state of computer use in Kenyan health care in this post.
A: Computers assist in keeping track of a patient's medical history, medication stock, purchases and…
Q: Analyze the benefits of agile development in comparison to more conventional, structured development…
A: Answers: Advantages of agile development versus traditional: Agile methods should be more precise…
Q: What is the database's security level? What are two database security solutions you could talk…
A: Introduction: The vast majority of businesses make considerable financial investments in database…
Q: You may define "cursor" in your own unique way.
A: Given: 1) A cursor is a location indication on a computer display that allows a user to enter…
Q: Suppose that you have a computer with a memory unit of 24 bits per word. In this computer, the…
A:
Q: What are the key differences between services and software components?
A: Intro According to the question we need to context the most important distinctions between services…
Q: Include four distinct kinds of external disk interfaces in your list.
A: Four distinct external disk interface
Q: Why would it be beneficial to reduce the number of support structures for students, administrators,…
A: INTRODUCTION: Here we need to tell Why would it be beneficial to reduce the number of support…
Q: Use: 8086 Assembler, Code a program that will form a trees, use the word below. with different color…
A:
Q: Detail the relationship between user-centered design concepts and the software development…
A: Introduction: Software life cycle models provide visual and diagrammatic representations of the…
Q: 5- Which one of the following is not a network topology?" O All options O Bus O Client Server O Star
A: In the given question types of topology are bus topology, ring topology, star topology, mesh…
Q: X++ symbolizes a prefix increment. * True O False In for loop, the initialization expression is…
A: ++ operator is known as increment operator. It increases the value by 1. It can be used as prefix…
Q: If you were in charge of designing a new operating system, what features would you include? Please…
A: Own operating system: Few programmers try to create an operating system, and many of those who do…
Q: List and compare two types of intrusion detection and prevention systems in terms of detection…
A: Answer: The IDPs is that type of methodology that will be giving a pre-call from any cyber threats…
Q: Which architecture is most commonly used in organisations nowadays to construct a firewall? Why?…
A: SCREENED SUBNET FIREWALL (WITH DMZ): SCREENED SUBNET FIREWALL The Screened Subnet Firewalls are the…
Q: Information technology Privileged Credentials: What Are They?
A: Answer: Privileged credentials are also known as privileged passwords and it is a set of credits…
Q: In Java, what are the general advantages, disadvantages, and speed of the following data structures?…
A: A binary search tree, also known as an ordered binary tree, is a node-based data structure in which…
Q: What are the advantages and disadvantages of using a relational database management system?
A: Introduction: An examination of the benefits and drawbacks of a relational database management…
Q: There is no doubt that the Big Data Cluster's design relies heavily on cloud computing. For our…
A: Introduction: Big data refers to diversified, vast, amounts of data that are growing at an…
Q: When it comes to popularity, Cloud Computing and the so-called Big Data Cluster are swiftly grabbing…
A: Big data advantages in the cloud: the following are the benefits or advantages of big data in the…
Q: Cloud computing has already outpaced even traditional on-premise infrastructure when it comes to…
A: Cloud Computing: Modern data centers are very different from those of recent years. Virtual networks…
Q: What exactly is gradual development?
A: Introduction: The Process of Incremental Development
Q: What is the role of software engineering in software development?
A: The Answer is in step-2.
Q: There are two kinds of memory addresses. Instead of placing all of the data in memory, why not…
A: Introduction: The central processing unit (CPU) has a close relationship with primary storage, also…
Q: What is the overarching issue with static scoping?
A: Introduction: The overarching issue with static scoping are :
Q: Assume a computer transmits a packet to another computer on the Internet at the network layer. The…
A: As per given information:- If the packet's logical destination address has been corrupted, the…
Q: Step-by-step instructions for converting RGB to HIS colour.
A: RGB to HIS color transformation 1. Read the RGB image using the ‘imread’ function.2. Each RGB…
Q: Discuss briefly any four user-initiated actions that can be accomplished using a graphical user…
A: Introduction: GUI is an abbreviation for Graphical User Interface. It is the interface in which…
Q: Is there a certain point in startup time when antivirus software starts loading?
A: Start: The reason for this is because ACK packets do not need sequence numbers. protocol rdt:…
Q: Discuss a systematic approach to enhancing the security of a Linux computer.
A: There are 5 steps which are used to enhance our link operating system. 1. BY CHOOSING FULL DISK…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 2 images

- Write an armv7 assembly program that uses SUBROUTINE CALLING to compute the n-th term of the fibonacci sequence. The program must use recursive function calls. Here is the code in C associated to the function required to be implemented in armv7: int fibbonacci(int n) { if(n == 0){ return 0; } else if(n == 1) { return 1; } else { return (fibbonacci(n-1) + fibbonacci(n-2)); } } Pls comment your code as possible explaining exactly what happens. Thanks!Microprocessor lab tasks - Solve the problems in assembly language using emu8086 solution format .MODEL SMALL .STACK 100H .DATA ; DEFINE YOUR VARIABLES HERE .CODE MAIN PROC MOV AX, @DATA MOV DS, AX ; YOUR CODE STARTS HERE ; YOUR CODE ENDS HERE MOV AX, 4C00H INT 21H MAIN ENDP END MAIN Collapse :white_tick: 1 Problems : Task 01 a program that takes in 3 digits as input from the user and finds the maximum Sample input: 1st input: 1 2nd input: 2 3rd input: 3 Sample Output: 3 Task 02 Take two digits as input from the user and multiply them. If the result is divisible by 2 and 3 both, print "Divisible". Otherwise, print "Not divisible" Sample input: 1st input: 5 2nd input: 6 Result is 30 Sample Output: Divisible Sample input: 1st input: 5 2nd input: 2 Result is 10 Sample Output: Not divisibleFor a scenario of four floor lift write an assembly language code such that when user press any key from [1 till 4] lift should move to the corresponding floor. Code in assembly language microprocessor
- Convert the given code fragment to assembly code fragment, using only instructions of the following types. These instructions are generally discussed in class. Here X,Y,Z are any memory locations; R, R1, R2 are any general registers; L is a label in the code (you can use any names as labels, ex. L, L1, L2 etc. ). load X, R //copy contents of memory location X into R. store R, X //Store contents of R into Mem location X cmp R1, R2 //Compute R1-R2 and update condition codes; //throw away result of subtraction. jmp L //Jump to location L in the code. jmpp L //If P bit is 1, Jump to location L in the code add X, R //Add contents of X,R and store result in R; //Also update the condition codes. Be careful about what type of argument is allowed in the instruction (Memory or Register). Ex. the first argument of ADD instruction is memory, not register. Do Not…For the (pseudo) assembly code below, replace X, Y, P, and Q with thesmallest set of instructions to save/restore values on the stack and update the stackpointer. Assume that procA and procB were written independently by two differentprogrammers who are following the MIPS guidelines for caller-saved and callee-savedregisters. In other words, the two programmers agree on the input arguments andreturn value of procB, but they can't see the code written by the other person. procA:$s0 = ...$s1 = ...$s2 = ...$t0 = ...$t1 = ...$t2 = ...X$a0 = ...$a1 = ...jal procBY... = $s1... = $t0... = $t1... = $a0jr $raprocB:P... = $a0... = $a1$s2 = ...$t0 = ...Qjr $raturn this c code into assembly language in optimized and unoptimized mode. /* Project 2 */ /* GCC *//* gcc -Wa,-adhln -g -masm=intel -m32 "Project 2.c" > "Project 2-g.asm" *//* gcc -Wa,-adhln -O -masm=intel -m32 "Project 2.c" > "Project 2-o.asm" */ #include <stdio.h> #define NOINLINE __attribute__ ((noinline)) static NOINLINE int function1(int x, int y){ int i; int sum; int values[10]; sum = 0; for (i = 0; i < 10; i++) { values[i] = 10 * i + x * y; sum += values[i]; } return (sum); } static int NOINLINE function2(int *values, int valuesLen){ int i; int sum; sum = 0; for (i = 0; i < valuesLen; i++) { sum += values[i]; } return (sum); } static NOINLINE int function3(int x){ int y; y = x / 10; return (y); } static NOINLINE int function4(int a, int b, int c, int d){ int r; if (a > b) r = a; else if (a > c) r = 2 * a; else if (a > d)…
- What are three applications of the.EQUATE instruction in Pep/9 assembly language? (explain briefly - each phrase should be one sentence) The.EQUATE command generates code for which of these three purposes?2- What is the 8085 Assembly Language Instruction That do the follwing INITIALISE STACK pointer SP with value 250Computer Science A[10] = x; Let x is saved in the register ($s0) and the base address of array A is saved in register ($s3). What is the equivalent MIPS instruction of this high-level language?
- Write and simulate a MIPS assembly-language routine that: 1. Prints your group number, for example “Group 1”, 2. Computes the dot product of two vectors, A_vec and B_vec, as described in Lab 4 of the Lab Manual, 3. Stores the result at memory word DOTPROD, and 4. Prints the result preceded by the phrase: “The result of the dot product is: “. Your data segment should look like the following: .data group: .asciiz “\nGroup x” msg: .asciiz "\nThe result of the dot product is: " A_vec: .word x, 4, 20, 13, 3, 10, 5 B_vec: .word 4, 2, 1, 2, 5, 2, 4 n: .word 7 DOTPROD: .word 0 Replace each “x” with your group number.Generate a listing file for AddTwoSum.asm(in 3.4.3 of the text) and write a description of the machine code bytes generated for each instruction. You can write your descriptions directly over the .lst file. You might have to guess at some of the meanings of the byte values. ; AddTwoSum.asm - Chapter 3 example. .386.model flat,stdcall.stack 4096ExitProcess proto,dwExitCode:dword .datasum dword 0 .codemain proc mov eax,5 add eax,6 mov sum,eax invoke ExitProcess,0main endpend mainI would appreciate it if you could clarify the terms "subroutine" and "stack" to me. Who makes use of the stack during calls to subroutines? The concept of calling and using subroutines, as well as the subsequent changes to the sequence in which programmes are performed, may be shown with the use of an example involving an 8085 microprocessor.

