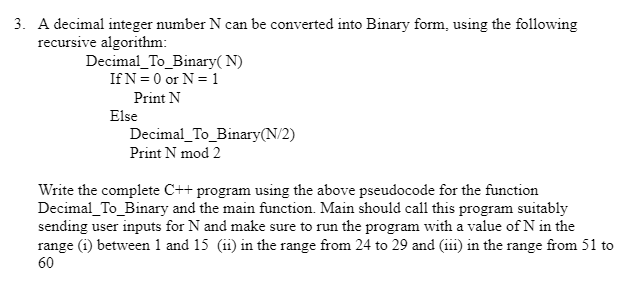
A decimal integer number N can be converted into Binary form, using the following recursive algorithm: Decimal_To_Binary(N) If N = 0 or N = 1 Print N Else Decimal_To_Binary(N/2) Print N mod 2
Q: In an IoT web stack, how important are protocols like UDP and IPV6? What is the difference between a…
A: Introduction: IoT or Internet of Things has revolutionized the way that we interact with devices and…
Q: Let's now split our input data X and labels y into a train and test set using the train_test_split()…
A: Code: from sklearn.model_selection import train_test_split X_train, X_test, y_train, y_test =…
Q: Please define "Semantic augmentation" and offer an example to help me get a handle on the…
A: Context Free Grammar:- Context-free grammar (CFG) is a type of formal grammar in which each…
Q: 6. Initial value of shared variable m is equal to 0 and it is stored at memory address 1100. threads…
A: The operations that the four threads must perform once to result in the value of m being -2 are as…
Q: Detail the many kinds of semantics, when and how they should be used, and the pros and cons of each.
A: Introduction : Semantics is the study of meaning in language. It looks at how the meaning of words,…
Q: 1.6 EXERCISES 1. Suppose an economy has only two sectors, Goods and Ser- vices. Each year, Goods…
A: Disclaimer: "Since you have asked multiple questions, we will solve the first question for you. If…
Q: Why is UDP useful? Perhaps it would have been preferable if IP packets could have been sent directly…
A: Introduction : UDP (User Datagram Protocol) is a communications protocol that is used primarily for…
Q: There are many advantages to cloud computing, but there are also many disadvantages.
A: Simply put, cloud computing is the provision of computing services such as servers, storage,…
Q: A Consider the minimum flow problem shown below, where the source is node A, the sink is node F, and…
A: Answer: We need to write the what will be the maximum flow for the given . so we will see in the…
Q: What is the width of the start bit if the baud rate on a UART
A: Dear Student, The answer to your question with required calculations is given below -
Q: Due to their nature, wireless networks present a number of challenges. Specify the nature of three…
A: Interference, limited range, and security threats negatively impact the user experience by causing…
Q: Is it true that it's always less expensive to prevent a problem than it is to fix it after it's…
A: According to the information given:- We have to define the mentioned statement is true or not.
Q: Now more than ever, wireless networks are crucial in quickly emerging countries like China and…
A: Communication speeds up economic growth. Digital devices that share information constitute a…
Q: For what reasons does modern Internet infrastructure favor TCP over UDP for the transmission of…
A: Explained: Voice and video communication should be delivered via TCP rather than UDP for the…
Q: When will Deadlock Prevention work, and what requirements does it have?
A: An operating system is a programme that runs application programmes and acts as a communication…
Q: Question 9 What cannot be collected by the default Analytics tracking code? A Browser language…
A: The answer is given below step.
Q: What are some of the fundamental concepts of design that underpin the CBSE, with the goal of…
A: The CBSE (Component-Based Software Engineering) is a software development paradigm that focuses on…
Q: In order to catch (and thus handle) a thrown exception, the statement (or statements) that can…
A: Exception Handling is a mechanism where we can handle the exception that may occur during the…
Q: Many of the cornerstones of software engineering are missing. Explain?
A: First, a high-level summary of software development: Software engineering combines software with…
Q: called? b. How does it propagate? c. What does it do to the comput
A: As per the given question, we need to identify 2 malware packages and need to answer the following…
Q: Is it your goal to increase your knowledge of social media blogging, cloud computing, and related…
A: Simply put, cloud computing is the provision of computing services such as servers, storage,…
Q: Problems arise from the inherent characteristics of wireless networks. Is there a way to put into…
A: Introduction: A wireless network is a network that communicates without a connection. The network…
Q: Determine why wireless networks are so important in third world countries. In place of LANs and…
A: Our daily lives are permeated by radio technology, which is employed in short-range gadgets,…
Q: Exactly what is a "digital envelope"?
A: Given: A digital envelope is what? Solution: Electronic envelope: A covering that shields the…
Q: The errors are showing up in the testdriver class. I was wondering what was going on and how I fix…
A: In this question we will basically understand the common reasons which assist what usually be the…
Q: plain Natural Language Toolkit in full description
A: The Natural Language Toolkit (NLTK) is a Python library for working with human language data (text).…
Q: I'm not sure what you mean by "network security." Define how the data encryption standard works.
A: Definition: Network security, in general, refers to the measures taken by any company or…
Q: Question 21 If a user visits a web page with an embedded video, leaves without clicking on anything,…
A: The given mcqs is related to the web page and mobile devices. A web page is a document or resource,…
Q: Give an example of when it would be beneficial to have a data structure that was always the same. In…
A: Introduction Data Structure: A data structure is a methodical approach to arranging information on a…
Q: Exactly what is a "digital envelope"?
A: A digital envelope is a cryptographic technique used to protect data transmission over insecure…
Q: demonstrates the search technique on a skip list S for a key K. The search is carried out using the…
A: Skip list: A skip list is a probabilistic data structure that is used for searching for elements in…
Q: Just what is it that a LAN is
A: Answer: We need to explain the what is the LAN . so we will see in the more details explanation.
Q: Anyone may access the root user on any Linux system, albeit sudo is the recommended method of doing…
A: Introduction: Linux is a free and open-source operating system. An operating system is needed to…
Q: When a deadlock is identified, a strategy has to be developed to break it.
A: When several cycles are delayed down because each interaction is hanging onto an asset while it…
Q: DIRECTION (4-5): One card is drawn from a well-shuffled deck of 52 cards. Find the probability of…
A: '8' of diamond: (C) 1/13 Red ace: (B) 2/26
Q: Please define "Semantic augmentation" and offer an example to help me get a handle on the…
A: Required: Give an explanation of "Semantic augmentation" for CFG (Context Free Grammar) rules and an…
Q: illustrates the algorithm for search procedure on a skip list S for a key K. The algorithm employs…
A: Skip list is a type of data structure which consists of two types of layer which are lowest layer…
Q: How to do the tree method
A: 1. Programming is the process of creating a set of instructions that tells a computer how to perform…
Q: Fill In The Blank The that an ArrayList gets, the more difficult it is for a computer to handle…
A: In Java programming language, Array is a set of elements that elements are homogeneous which means…
Q: If you're going to explain how the internet works, why not go ahead and list all the components that…
A: HOW THE INTERNET WORKS: The computer network known as the internet is described as transmitting…
Q: please code in JAVA Write two formulas. The formulas will be used to separate a series of items…
A: Given a list of items, write a Java program to separate the items into six categories. The program…
Q: The technological advancements of the Internet are open to much debate.
A: Introduction: Technology and science are progressing rapidly. We are surrounded by scientific…
Q: The Traveling Salesman Problem in Paris - An Optimal Tour Considering a Multimodal Transportation…
A: A solid public transportation infrastructure is critical in the development of smart cities,…
Q: We take a look at these cutting-edge features of cloud computing and their implications for…
A: This query provides information about modern cloud computing: The solution is easy: Through the…
Q: An organization's analysts should always present a concise executive summary of their results that…
A: Introduction: I'm drafting the answer to the above inquiry. Below is the written response. Strengths…
Q: In mathematics, the midpoint between the two points (x1, y1) and (x2, y2) is computed by the formula…
A: Step 1: Declare double variables x1, y1, x2, y2, midpoint_x and midpoint_y, and char variables…
Q: Just how unstable is UDP compared to IP? I'm interested in hearing your take on this. What is your…
A: Despite not being equally unstable, UDP and IP are both unreliable. Unlike UDP, which has four…
Q: In case study 1, what are some goals the model was trying to optimize for? There can be more than…
A: The goals of a vaccine distribution model can vary depending on the context and priorities involved.…
Q: Content, accessibility, logical structure, and physical organization are all factors that should be…
A: Database A database is an assortment of effectively accessible information. Data, like deals…
Q: Most individuals don't know about or don't care about cloud computing's limitations, which might be…
A: Introduction Limitations of Cloud ComputingThe limitations of Cloud Computing can be relatively…
I have provided C++ CODE along with CODE SCREENSHOT and OUTPUT SCREENSHOT---------------------------
Step by step
Solved in 4 steps with 3 images

- Write a C++ program that (1) asks the user to input any Arabic number (e.g., 1999), (2)converts this Arabic number into a Roman number (e.g., MCMXCIX), and (c) displays theresultant Roman number.Your program should include at least three functions to do the input, processing(conversion), and output. Also include a loop that will allow the user to repeat the wholeprogram if he wants to. PLEASE add "//" every code wirtten to explain its use in the program. thank you! do the following conditions set and DO IT IN C++Write a program that displays the following two entries: the number 33777 and the ASCII character code ‘X’, in binary, decimal, and hexadecimal. Tip: Use as few variables as possible; use the options provided by the printf function, but you will need to program the conversion to binary. Explain all codes and write program on c language. ThanksQuestion D. Write a C++ program that computes the factorial of a given positive integer (n!). The program must first read the number n from the user. The program will not proceed to the next-step unless a valid non-negative number is entered. Then the program must call a function to achieve the calculation of the n!. The prototype of the function is as follows: int fact(int fac); The sample output of the program is as follows: - C:\Users\Imran\Desktop\Lab111\Debug\Lab111.exe Enter number to find its factorial : 5 Factorial of a given number is = 120 Press any key to continue...
- In C++ just do the problems in simple, not complicated code. Even if a problem does not directly tell you to use a function, you should aim to do so regardless. 1. Create a function that takes in a number n and outputs all the odd numbers from 1 to n. 2. Create a function that takes in a int number and outputs each of the digits backwards 3. Create a function that counts backwards from 100 to 1. 4. If we list all the natural numbers below 10 that are multiples of 3 or 5, we get 3, 5, 6 and 9. The sum of these multiples is 23.Find the sum of all the multiples of 3 or 5 below 1000. Use a function to do this. Return the total to main.NEED CODE IN C++ IN VISUAL STUDIO AND OUTPUT Write a program to print the factorial of a number by defining a function named 'Factorial'. Factorial of any number n is represented by n! and is equal to 1*2*3*....*(n-1)*n. For Example:4! = 1*2*3*4 = 243! = 3*2*1 = 62! = 2*1 = 2Also,1! = 10! = 0PLEASE SOLVE THIS IN C++ CODE ONLY! PLEASE READ AND DO THE PROGRAM WITH ACCORDING TO THE CONDITIONS GIVEN. PLEASE ALSO WRITE THE USE OR FUNCTIONS OF EACH CODE USED BY INSERTING ITS USE EVERY LINE USING "//" A palindrome is a string that reads the same from front to back as it does from back to front, e.g., "racecar", "radar", "21012". Write a program that will identify whether a given line of input is a palindrome or not. Your program must also be able to determine the following sample inputs as palindromes, aside from identifying one-word inputs: Able was I 'ere I saw Elba. Madam, I'm Adam. A man, a plan, a canal, Panama. These samples require that your program must ignore spaces and punctuations, and consider uppercase and lowercase letters to be the same. Include necessary functions in your program to process the input. You can also use existing functions from the string library.
- Write a program in C++ that should calculate the insurnace for a house. use questions below to write your programm. what is your first? what last name? how many people are living in the houes? how much did you bought the house for? how many bedrom does it have? what is the lenght in squre feet? - use Loop so everyone can repeat the programm. use function like "viod" and any other function. and finally use this formula: X/150*y/*50 x is the total price of the house y is the number of bedrooms s is the lenght in square feet.The problem is from Introduction to Programming and Data Structures with C++, 4th edition (Count positive and negative numbers and compute the average of numbers)Write a program that reads an unspecified number of integers, determines how many positive and negative values have been read, and computes the total and average of the input values (not counting zeros). Your program ends with the input 0. Display the average as a floating-point number.If you entire input is 0, display 'No numbers are entered except 0.'Sample Run 1Enter an integer, the input ends if it is 0: 1 2 -1 3 0The number of positives is 3The number of negatives is 1The total is 5The average is 1.25Sample Run 2Enter an integer, the input ends if it is 0: 0No numbers are entered except 0Q NO 1: There are two ways to pass arguments to functions. Pass by value and pass by reference. Let’s suppose you have to write multiplication function which receives two integers (as arguments) given by user from main. The multiplication operation will be carried out through their addresses. Solve this problem by writing a C++ program.
- Write a complete C program to calculate the perimeter and area of a triangle with 3 sides namely a, b, and c. The sides will be given as inputs by the user. The program will be executed at least once, and repeat as long as user wish to calculate again. There are a total of 5 functions: • Function 1: - This function will display the menu options that the user can choose (to calculate perimeter or area of a triangle). • Function 2: - This function will calculate the perimeter of a triangle - Accepts the sides of triangle as parameter - Formula: perimeter = a + b + c - Return the result back to the caller. • Function 3: - This function will calculate the area of a triangle - Accepts the sides of triangle as parameter - Formula: area = Vs (s — a)(s — b)(s — c), where s = (a + b + c)/2 - Return the result back to the caller. • Function 4: - This function will get the sides of triangle from user. - Ask user for option on what s/he would like to calculate. - Based on the option (Use switch…Write code in C++ There are two scientists working on set of numbers. The first person is looking for two numbersspecifically. The second person is responsible for entering all data. Help the first person to know ifthe numbers set entered by the second person includes the two numbers he is looking for!InputThe first person shall enter two numbers. The second person enters set of numbers of any size. S/hecan enter any range of numbers (up to you how to read those numbers).OutputMessage showing if both numbers entered by the first person have been found or not. If one of thenumbers was found show which one has been found. Hint: you may need to use flag-controlled loop.in the following program please use string data types and string functions. use enum types. for loops with enum types, etc. Thank you. Write a C++ program that takes a date in the following format: December 24th, 2021 and extracts the day, month, and year as 3 integers. Your program should have and use at least the following functions: (a) Write a function getDate that prompts a user to enter a date as a string and returns it. (b) Write a function extract that takes as its parameter a date and returns the day, month, and year as 3 integers. (Hint: you can use the function isdigit(c) that returns true if c is a digit character and false otherwise.) (c) Write a function convertDigits that takes as its parameter a string of digits and converts it to an int. (Hint: to convert a digit character to a digit number use static cast (’d’) - static cast(’0’) where d is 0, 1, ..., 9) (d) Write a function convertMonths that takes as its parameter a month as a string and returns a corresponding…

