cmpl $4 , %edi movl %edi , %edi jmp .L4(,%rdi,8) .L3: movl $17, %eax ret .L5: movl $3, %eax int A ( int x , int y) { int a ; ret .L6: if ( x else i f ( x else i f ( x == else i f ( x else i f ( x == 4 ) a = 17; ) a 2 ) a 3 ) a == a = movl $20, %eax 3 ; %3D%3D ret 2 0 ; %3D .L7: 2 ; %3D%3D %3D movl $2, %eax 1 ; a = 0; ret else .L8: return a ; movl $1. %eax
cmpl $4 , %edi movl %edi , %edi jmp .L4(,%rdi,8) .L3: movl $17, %eax ret .L5: movl $3, %eax int A ( int x , int y) { int a ; ret .L6: if ( x else i f ( x else i f ( x == else i f ( x else i f ( x == 4 ) a = 17; ) a 2 ) a 3 ) a == a = movl $20, %eax 3 ; %3D%3D ret 2 0 ; %3D .L7: 2 ; %3D%3D %3D movl $2, %eax 1 ; a = 0; ret else .L8: return a ; movl $1. %eax
Chapter4: Processor Technology And Architecture
Section: Chapter Questions
Problem 2PE: If a microprocessor has a cycle time of 0.5 nanoseconds, what’s the processor clock rate? If the...
Related questions
Question
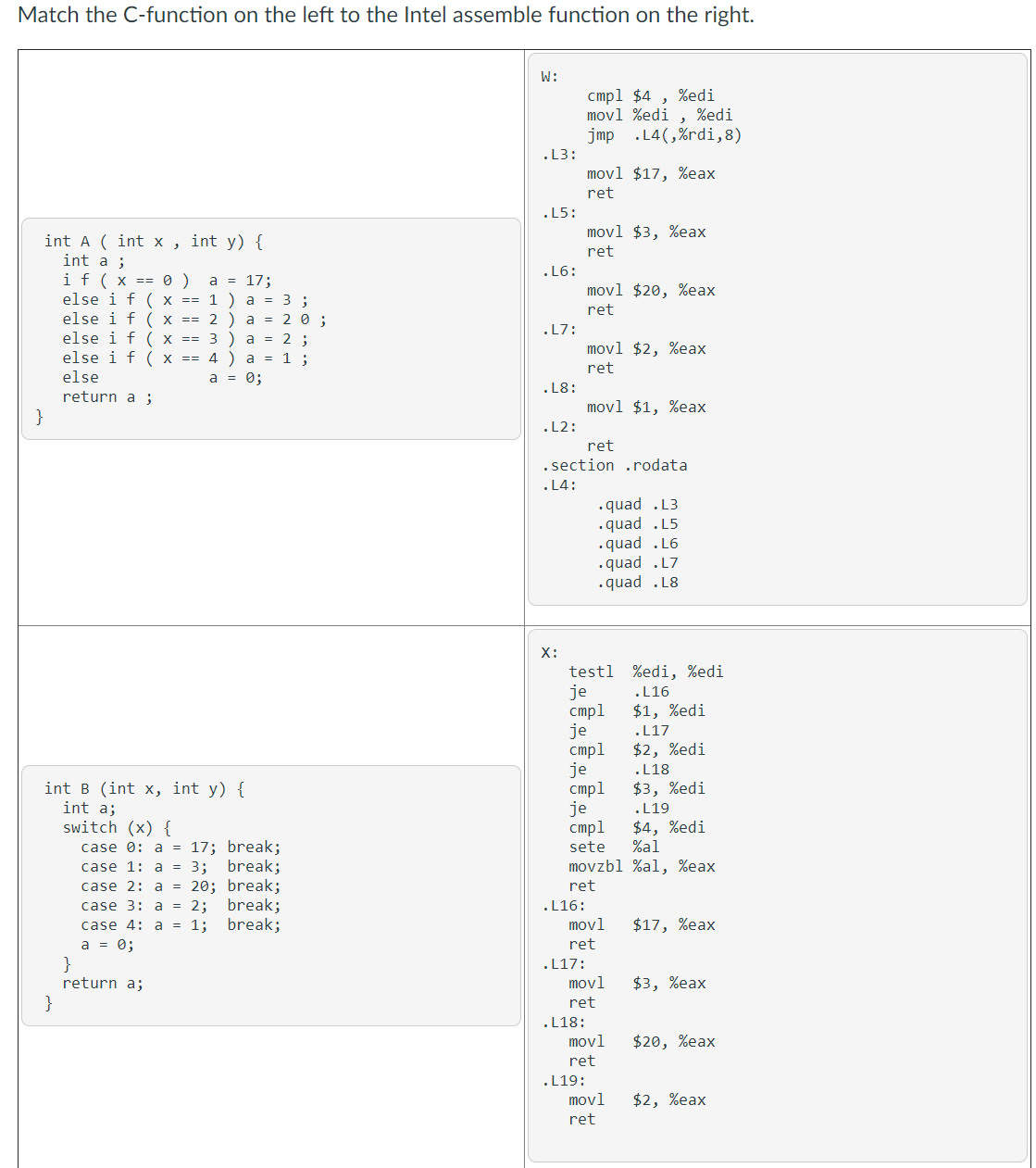
Transcribed Image Text:Match the C-function on the left to the Intel assemble function on the right.
W:
cmpl $4
movl %edi , %edi
jmp .L4(,%rdi,8)
%edi
.L3:
movl $17, %eax
ret
.15:
movl $3, %eax
int A ( int x , int y) {
int a ;
if ( x == 0 )
else i f ( x == 1 ) a = 3 ;
else i f ( x == 2 ) a = 2 0 ;
else i f ( x == 3 ) a = 2 ;
else i f ( x == 4 ) a = 1 ;
ret
.L6:
a = 17;
movl $20, %eax
ret
.L7:
movl $2, %eax
ret
else
a = 0;
.L8:
return a ;
movl $1, %eax
.L2:
ret
. section .rodata
. L4:
.quad .L3
.quad .L5
.quad .L6
.quad .L7
.quad .L8
X:
testl %edi, %edi
je
cmpl
je
cmpl
je
стр1
je
cmpl
.L16
$1, %edi
.L17
$2, %edi
.L18
$3, %edi
int B (int x, int y) {
int a;
switch (x) {
.L19
$4, %edi
%al
movzbl %al, %eax
case 0: a = 17; break;
sete
break;
case 1: a = 3;
case 2: a = 20; break;
case 3: a = 2; break;
case 4: a = 1;
a = 0;
}
return a;
ret
.L16:
break;
movl
$17, %eax
ret
.L17:
movl
$3, %eax
}
ret
.L18:
movl
$20, %eax
ret
.L19:
movl
ret
$2, %eax
![Y:
cmpl %esi, %edi
jge
movl $0, %eax
.L12
.L11:
int c (int x, int y) {
int a = 0;
while (x < y) {
a += x * y;
++x; --y;}
movl %edi, %edx
imull
addl
addl
subl
%esi, %edx
%edx, %eax
$1, %edi
$1, %esi
cmpl %esi, %edi
.L11
return a;
}
jl
ret
.L12:
movl $0, %eax
ret
Z:
cmpl %esi, %edi
jge
pushq %rbx
movl %edi, %ebx
imull %esi, %ebx
subl
addl $1, %edi
call
.L22
int D (int x, int y) {
if (x >= y)
return 0;
else
return (x*y) + D(x+1, y -1);
}
$1, %esi
D
addl %ebx, %eax
jmp
.L21
.L22:
movl
$0, %eax
ret
.L21:
popq %rbx
ret
A
[選択]
В
[選択]
C
[選択]
D
[選択]
>
>
>](/v2/_next/image?url=https%3A%2F%2Fcontent.bartleby.com%2Fqna-images%2Fquestion%2F4cd974de-0ca5-43c4-9c5f-a02c9b7b2d9a%2F73774188-678f-4359-8fdd-85cd155795c6%2Fwb1q92a_processed.png&w=3840&q=75)
Transcribed Image Text:Y:
cmpl %esi, %edi
jge
movl $0, %eax
.L12
.L11:
int c (int x, int y) {
int a = 0;
while (x < y) {
a += x * y;
++x; --y;}
movl %edi, %edx
imull
addl
addl
subl
%esi, %edx
%edx, %eax
$1, %edi
$1, %esi
cmpl %esi, %edi
.L11
return a;
}
jl
ret
.L12:
movl $0, %eax
ret
Z:
cmpl %esi, %edi
jge
pushq %rbx
movl %edi, %ebx
imull %esi, %ebx
subl
addl $1, %edi
call
.L22
int D (int x, int y) {
if (x >= y)
return 0;
else
return (x*y) + D(x+1, y -1);
}
$1, %esi
D
addl %ebx, %eax
jmp
.L21
.L22:
movl
$0, %eax
ret
.L21:
popq %rbx
ret
A
[選択]
В
[選択]
C
[選択]
D
[選択]
>
>
>
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps with 4 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning