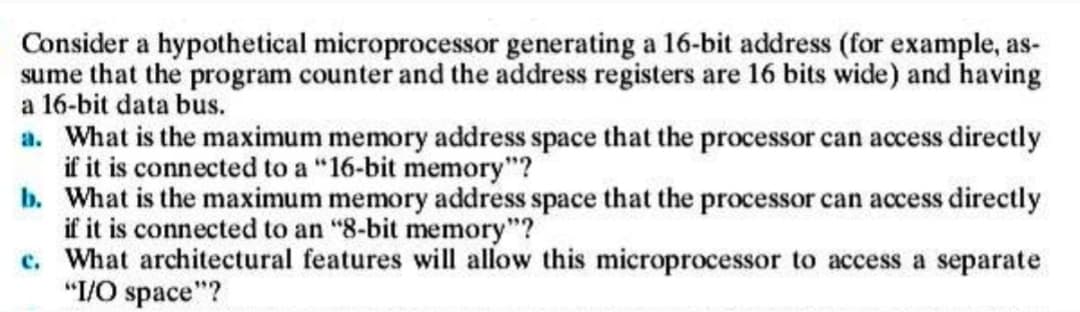
Consider a hypothetical microprocessor generating a 16-bit address (for example, as- sume that the program counter and the address registers are 16 bits wide) and having a 16-bit data bus. a. What is the maximum memory address space that the processor can access directly if it is connected to a "16-bit memory"?
Q: What is boosting? State why it may improve the accuracy of decision tree induction.
A: What is boosting? State why it may improve the accuracy of decision tree induction answer in below…
Q: Do you agree that "there is no idea of client and server sides of a communication session" in a P2P…
A: The following will explain why there is no idea of client and server sides of a communication…
Q: What specific objective are we aiming to fulfill through the use of formal techniques? When creating…
A: Given: Standard assumptions are relied on in Formal Methods. They never change their minds. They are…
Q: Q: Consider an entity moving from location A to B, while passing several intermediate locations…
A: The idea for locating an entity at an intermediate location is to use forwarding pointer.
Q: Define the two main categories of processor registers.
A: Here in this question we have asked to define two main categories of processor register.
Q: Site S, executes the following three steps to invoke mutual exclusion: Step 1: (Request Critical…
A: execution of given steps to invoke mutual exclusive is in next step:
Q: Is there a way to describe how the Ubuntu Linux distribution got its start as a branch?
A: A Linux distribution, sometimes known as "Linux distro," is a packaged version of the open-source…
Q: Three new features have been added to the Linux kernel. Is the release therefore more secure? What…
A: The Linux kernel, an essential component of the Linux operating system, serves as the primary…
Q: Consider a hypothetical microprocessor generating a 16-bit address (for example, as- sume that the…
A: Microprocessor is so called because this device comprises of transistors which are small in size.
Q: What are some of the several ways you may protect your passwords so that nobody else can access…
A: It is impossible to create a password that cannot be broken. Someone who has a great desire for…
Q: First and foremost, why are formal procedures employed? There must be at least four separate…
A: Formal strategies are mathematical techniques for resolving software (and hardware) issues…
Q: Here, we'll talk about the most crucial aspects of descriptive models.
A: A mathematical technique called descriptive modelling describes real events and the connections…
Q: What is file protection, and how is it handled by Linux? (Relating to the computer's operating…
A: Given: What is file protection, and how is it used by Linux? pertaining to system administration
Q: readers. Write a program with two inputs, current price and last month's price (both integers output…
A: Implement this system is given below: 1)Declare variables 3)examine current_price and…
Q: It is necessary to discuss the use of computers, cell phones, and tablets at work.
A: Intro The following are some examples of how tablets and smartphones are used in the workplace:…
Q: Let A₁ = - [14]. Find Answer: nAi Hint: Write you answer in an interval notation such as [a,b],…
A:
Q: A web client must employ native authentication and authorisation services that the server has…
A: The following are some of the security measures: Extended Amount of Freedom It is possible to…
Q: We would much appreciate any ideas for Linux package management solutions that you have used in the…
A: Linux package management Utilizing package management, software updated from characterized Linux…
Q: How workers who don't have internet access may still utilize the system directly
A: As technology develops: An increasing number of businesses are turning to kiosk solutions to meet…
Q: While some Linux variants provide root access, others promote the use of sudo. How are they unique…
A: When working with Linux, there are two methods for running administrative applications. You can…
Q: Compare Ubuntu to other well-known Linux distributions to get a feel of its advantages and…
A: It is quite necessary to make this choice right now. Compared to other well-known choices, Ubuntu…
Q: Rajesh recently revamped its practice page to make it easier for users to identify additional…
A: Program Details The first line of input will contain a single integer T, the number of test cases.…
Q: Considering two processes P, and P₁, there can be two cases: Case 1: P, and P, are not concurrently…
A: algorithm for given data is:
Q: replicated process are
A: TIB/RV is based on a distributed architecture. Theinstallation of TIB/RV resides on each host on the…
Q: Please list three different C++ classes that may be used to create input streams
A: Answer the above question are as follows
Q: What does the StreamWriter object really do
A: Please find the answer below :
Q: What's the difference between downloading and deleting and downloading and keeping while using POP3?
A: Find Your Answer Below
Q: What are two actual world instances of how menus are used in applications? What are the advantages…
A: Menu explained: A menu is a graphical control element that provides access to multiple GUI…
Q: Q: Would it make sense to associate a replication strategy with each Web doc- ument separately, as…
A:
Q: What's the difference between downloading and deleting and downloading and keeping while using POP3?
A: The answer is given below step.
Q: If formal techniques have a purpose, how do they really function? There must be a minimum of four…
A: To Do: Explain the purpose of formal methods. Formal methods are used for the following reasons:…
Q: Would you mind giving an example of parametric polymorphism in
A: Parametric polymorphism is a computer language concept that allows enables for the broad…
Q: Describe the idea of a Linux distribution and list a few of the most well-known ones.
A: Given To know about the Linux distribution.
Q: Assume a process is replicated in a TIB/Rendezvous system. Give two solutions to avoid so that…
A: Downtime for data migration There are times when data migration is needed, whether it's moving from…
Q: Q: Describe a simple scheme for PGM that will allow receivers to detect miss- ing messages, even the…
A: Different solid conventions have been proposed for multicast information conveyance, each with an…
Q: What security measures does Linux This information pertinent to the she
A: Summary Depends on which flavor of Linux you're using. Kali Linux is an open source operating system…
Q: Do you have any ideas on the high-availability DHCP solutions that you believe would be most…
A: Please find the detailed answer in the following steps.
Q: Compare Ubuntu to other Linux distributions to see how it performs. Due to what I think, my idea is…
A: Introduction: Ubuntu is an open-source Linux distribution.Ubuntu is accessible as a desktop, server,…
Q: social
A: There are many privacy issues which we face during the use of social media sites like Facebook or…
Q: Assume a process is replicated in a TIB/Rendezvous system. Give two solutions to avoid so that…
A: Below are the two solutions to avoid so that messages from this replicated process are not published…
Q: Which phase of the software development process, in your opinion, is the most crucial, and why? You…
A: Given: Which of the typical software development process phases, in your opinion, is the most…
Q: What is a reverse shell defined as? What does an attacker do right away when they get a shell prompt…
A: The answer of the question is given below
Q: three
A: Primary form of testing are as follows - 1- Unit Testing - The whole program get submitted to…
Q: a) Assuming a KB page size, what are the page numbers and offsets for the following logical
A: The answer is
Q: Here, software development and academic writing are contrasted to see which approach is more…
A: Introduction: A software developer achieves the goal by developing computer code. The process…
Q: Give an explanation of a few Linux features in your own words. I value any more details you're…
A: Answer is in next step.
Q: What may one, in essence, hope to accomplish via the practice of software engineering? What or…
A: Given: One of the most important goals of software engineering may, in fact, be summed up.
Q: Describe the reasons why using model checking instead of evaluating a program's correctness against…
A: In model checking, systems are described by finite state machines, which are then compared to a…
Q: The most recent iteration has resulted in new functionality being introduced to the Linux Kernel.…
A: The answer of the question is given below
Q: Consider a relation (p, q, r, s, t, u, v) with functional dependencies as given below: p➜q r➜s,t…
A: Given : A relation (p, q, r, s, t, u, v) with functional dependencies as given below:p ⇒ qr ⇒ s, ts…
Step by step
Solved in 2 steps

- Processor R is a 64-bit RISC processor with a 2 GHz clock rate. The average instruction requires one cycle to complete, assuming zero wait state memory accesses. Processor C is a CISC processor with a 1.8 GHz clock rate. The average simple instruction requires one cycle to complete, assuming zero wait state memory accesses. The average complex instruction requires two cycles to complete, assuming zero wait state memory accesses. Processor R can’t directly implement the complex processing instructions of Processor C. Executing an equivalent set of simple instructions requires an average of three cycles to complete, assuming zero wait state memory accesses. Program S contains nothing but simple instructions. Program C executes 70% simple instructions and 30% complex instructions. Which processor will execute program S more quickly? Which processor will execute program C more quickly? At what percentage of complex instructions will the performance of the two processors be equal?_____ is a CPU design technique in which instruction execution is divided into multiple stages and different instructions can execute in different stages simultaneously.Consider a hypothetical microprocessor generating a 16-bit address (e.g., assume the program counter and the address registers are 16 bits wide) and having a 16-bit data bus. What is the maximum memory address space that the processor can access directly if it is connected to a “16-bit memory”? What is the maximum memory address space that the processor can access directly if it is connected to an “8-bit memory”? What architectural features will allow this microprocessor to access a separate “I/O space”? If an input and an output instruction can specify an 8-bit I/O port number, how many 8-bit I/O ports can the microprocessor support? How many 16-bit I/O ports? Explain.
- Consider a hypothetical microprocessor generating a 16-bit address (for example, assume that the program counter and the address registers are 16-bits wide) and having a 16-bit data bus. What is the maximum memory address space that the processor can access directly if it is connected to a “16-bit memory”? What is the maximum memory address space that the processor can access directly if it connected to an “8-bit memory”? What architectural features will allow this microprocessor to access a separate I/O spece? If an input and an output instruction can specify an 8-bit I/O port number, how many 8-bit I/O ports can the microprocessor support? How many 16-bit I/O ports can the microprocessor support? Are the values in d and e the same?Consider a Computer which has a memory which is capable of storing 4096 K words and each word in memory can be of size 32 bits. The computer supports a total of 6 addressingmodes, and it has 60 computer registers. The computer supports instructions, where each instruction consists of following fields: Mode Operation code Register Register Memory AddressGiven that each instruction will be stored in one memory word, discuss with a suitable diagram the format of instruction by specifying number of bits for each field of instruction. Discuss each field of instruction.hi can u anwser this qustion plesc ? Consider a Computer which has a memory which is capable of storing 4096 K words and each word in memory can be of size 32 bits. The computer supports a total of “K” addressing modes, and it has “M” computer registers. The computer supports instructions, where each instruction consists of following fields: Mode Operation code Register Register Memory AddressGiven that each instruction will be stored in one memory word, discuss with a suitable diagram the format of instruction by specifying number of bits for each field of instruction. Discuss each field of instruction.Note: Choose your own values for K (number of addressing modes) and M (number of Registers) k=8 m=50
- Consider a computer which has a memory which is capable of storing 4096 K words and each word in memory can be of size 32 bits. The computer supports a total of “6” addressing modes, and it has “50” computer registers. The computer supports instructions, where each instruction consists of following fields: Mode Operation code Register Register Memory Address Given that each instruction will be stored in one memory word, discuss with a suitable diagram the format of instruction by specifying number of bits for each field of instruction. Discuss each field of instructionConsider a hypothetical microprocessor having 32-bit instructions composed of two fields: the first Byte contains the opcode and the remainder the immediate operand or operand address. What is the maximum directly accessible memory capacity (in Bytes)? Discuss the impact on the system speed if the microprocessor bus has: a 32-bit local address bus and a 16-bit local data bus a 16-bit local address bus and a 16-bit local data busconsider a processor using 32-bit memory addresses, also a 4 KiB (of actual data) direct-mapped cache memory that stores 32 bits of data for each address. The number of index bits is?
- Consider a memory implemented for 8086 microprocessor Draw the memory block diagram. Determine the values for A0 , /BHE ,address lines(A1..A19) and data lines(D0.. D15) in order to access: A byte at odd address [01FF3H] A byte at even address [01FFCH] A word at even address [01FFEH] A word at odd address [01ABFH]Suppose a given processor has access to two levels of memory. Level 1 contains 1000 words and has an access time of 0.01 μs; level 2 contains 100,000 words and has an access time of 0.1 μs. Assume that if a word to be accessed is in level 1, then the processor accesses it directly. If it is in level 2, then the word is first transferred to level 1 and then accessed by the processor. For simplicity, ignore the time required for the processor to determine whether the word is in level 1 or level 2. Suppose 95% of the memory accesses are found in level 1, define the hit ratio (H) and find the average access time.Consider a hypothetical 23-bit processor called HYP23 with all registers, including PC and SP, being 23 bits long. The smallest addressable unit in memory is an 8-bit byte B. Assume that first quarter of the address space (starts at the address 0x00000) is dedicated to HYP23’s RAM memory and the upper half of the address space is reserved for HYP23’s Flash memory. Give address ranges for the RAM and Flash memories. Fill in the table below. What are the sizes of the RAM memory and the Flash memory? Start Byte Address End Byte Address RAM memory Flash memory RAM memory size [Bytes/KiB]:____________________________Flash memory size [bytes/KiB]:____________________________

