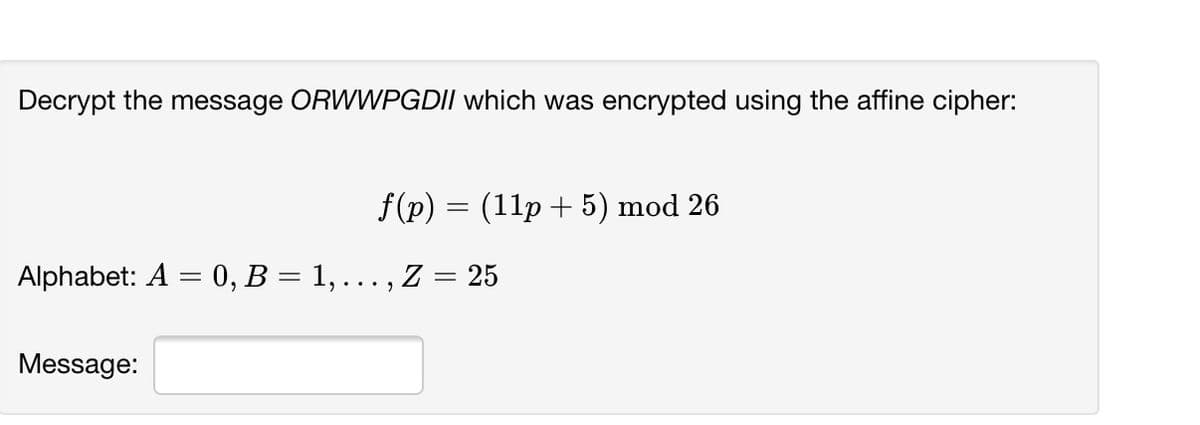
Decrypt the message ORWWPGDII which was encrypted using the affine cipher: f(p) = (11p + 5) mod 26 Alphabet: A = 0, B = 1, ... , Z = 25 Message:
Q: If U is encrypted as B by shift cipher transformation then decrypt the message WMPGLY using the same…
A:
Q: Find the inverse of the congruence 6x = 1 (mod 29) using Euclidean algorithm. (Show your work)
A: The given problem is to solve the given modular equation by find the inverse of congruence using the…
Q: [11 3. Consider the Hill 2-cipher with the encryption matrix decrypt the message you just received…
A: Consider the Hill 2-Cipher with the encryption matrix 11152. The aim is to solve decrypt the message…
Q: b.Given Bob's public key of (85, 7) and private key of (85, 55), show how Alice can encrypt m=5 to…
A: Given: b) Given Bob's public key of (85, 7) and private key of (85, 55), To show how Alice can…
Q: Let's say that Alice and Bob are exchanging keys using Diffie-Hellman key exchange using…
A: Here, we have p=499 (which is a prime number) g=7 a=23 (which is a secret exponent of Alice) and b…
Q: 5. Decrypt these messages encrypted using the shift cipher f(p) = (p + 10) mod 26. a) CEBBOXNOB XYG…
A: The Caesar Cipher is a type of shift cipher. Shift Ciphers work by using the modulo operator to…
Q: Find the greatest common divisor of 26 and 5 using Euclidean algorithm. An encryption function is…
A: Solution is below
Q: Assume you are constructing an RSA algorithm where primes are p=11, q=7 a) Choose a proper public…
A: Use the following formulae, to obtain the required result. n=pqϕn=p-1q-1ed≡1mod ϕny=xe mod nx=yd mod…
Q: Exercise 9.2.26. Given that 3 4 (;). A = and b = 2 3 (a) Use the encryption function f(p) = Ap + b…
A:
Q: 1. A long-winded, encrypted transmission has been intercepted. Frequency analysis of the entire…
A: As per our guidelines we are supposed answer only one question and rest can be reposted
Q: Describe the family of shift ciphers as a cryptosytem.
A:
Q: In a public key cryptosystem using the RSA algorithm, a user uses two prime numbers 11 and 17. He…
A: Given In a public key cryptosystem using the RSA algorithm a user uses two prime number 11 and 17.…
Q: What is the Plaintext of the following Ciphertext, based on Caesar cipher algorithm, if the KEY=5?…
A:
Q: 3. Decrypt the letters XMMIFZXQFLKP if it was encrypted using an alphabetic Caesar shift cipher with…
A:
Q: Encrypt the message ATTACK using the RSA system with n = 43 · 59 and e = 13, translating each letter…
A:
Q: which memory location is assigned by hashing function h(k)=k mod 101 social security number…
A: Which memory locations are assigned by the hashing function h(k) = k mod 101 to the records of…
Q: 2. Decrypt the letters MRYYXHJULYSL if it was encrypted using the alphabetic random substitution…
A: We are asking to decrypt the latter MRYYXHJULYSL by using the given table.
Q: Express the Vigen`ere cipher as a cryptosystem.
A:
Q: a) What is the difference between a public key and a private key cryptosystem? b) Explain why using…
A:
Q: Encrypt the message USE WATER HOSE using blocks of five letters and the transposition cipher based…
A: Encrypt the message USE WATER HOSE using blocks of five letters and the transposition cipher based…
Q: Decrypt the message ''EOXH MHDQV Using the shift cipher f(p)=(p+3)mod26
A: Solution by using shift cipher as follows :
Q: 2. Classify each of the following as a translation cipher, multiplicative cipher, or affine cipher.…
A: (a) f(x) = 4x + 7 is an affine transformation. Hence, f(x) = 4x + 7 (mod 9) is affine cipher.…
Q: Use the Caesar cipher (shift of 3 places) to encrypt BRAVE
A: Since, A=0 O=14B=1 P=15C=2 Q=16D=3 R=17E=4…
Q: Encrypt the message APPLES AND ORANGES using a shift cipher with key k = 13.
A:
Q: 1. Encrypt the message “DISCRETE MATHEMATICS” using the shift cipher with k = 5. 2. Decrypt…
A:
Q: npojd Assume that a person has ElGamal public key (2633, 3, 1138) and private key k = 965. If the…
A:
Q: Let (P, C, K, E, D) be a cryptosystem such that #K = #P = #C. Show that if this cryptosystem has…
A:
Q: Once the length of the key string of a Vig`enere cipher is known, explain how to determine each of…
A: The length of the key's known. Let its k. therefore the text is going to be divided into groups of k…
Q: Jse the RSA cipher with public key (pq, e) = (23 · 31, 43) = (713, 43) and private key (pq, d),…
A: Given pq=713d=307e=43 cipher text 675 001 423
Q: Decrypt the message "WFLRV" which is encrypted by the encryption function f (p) = (3p + 11) mod 26.…
A: Given: Encryption function is f(p)=3p+11mod26. Encrypted message is "WFLRV". For W, P=22.…
Q: The ciphertext OIKYWVHBX was produced by encrypting a plaintext message using the Vigen`ere cipher…
A:
Q: Encrypt the message GRIZZLY BEARS using blocks of five letters and the transposition cipher based on…
A:
Q: Decrypt these messages encrypted using the shift cipher f (p) = (p + 10) mod 26.a) CEBBOXNOB XYGb)…
A:
Q: 2. Assume that the letters of the English alphabet will be converted to numerical forms as follows:…
A: The following steps are used to encrypt a message. Assign numbers to the alphabets. Replace the…
Q: If the given encrypted text is " VTXDUH" then the decrypted text using Caesar cipher will be, O…
A: The correct option is SQUARE. Use the given options to decrypt the given text. All the options has…
Q: (d) Devise a recursive algorithm for computing bn mod m, where b, n, and m are integers with m > 2,…
A:
Q: Which of the following is the decryption function of an RSA cryptosystem having public and private…
A: We Know that, The RSA algorithm can be used for both public key encryption and digital signatures.
Q: If the Caesar cipher produced KDSSB ELUWKGDB, what is the plaintext message?
A: The encrypted message given is "KDSSB ELUWKGDB". Caesar cipher is a method to encrypt messages which…
Q: The ciphertext message produced by the RSA algorithm with key (n, k) = (2573, 1013) is 0464 1472…
A: Given that: The ciphertext message produced by the RSA algorithm with key n,k=2573,1013 is 0464 1472…
Q: 3 . Use the baby-step giant-step algorithm to find h, k such that 2^h ≡ 7 (mod 53), 2^k ≡ 9 (mod…
A:
Q: Ξ. Σ Suppose = {0, 1, 2, 3, ..., 34} is the alphabet for the affine cipher. Find the size of the…
A: Given, ∑=0, 1, 2, 3, . . . ,34 is the alphabet for the affine cipher.
Q: Find the inverse of the congruence 6x = 1 (mod 29) using Euclidean algorithm.
A:
Q: Recall that an affine cipher, fa,b(n) = an + b( mod 26), where a, b ∈ {0, 1, 2, . . . , 25}, is said…
A: For the encryption, use the following conversion table for the English alphabet: 0 1 2 3 4 5 6 7…
Q: Use the RSA cipher with public key n = 713 = 23 · 31 and e = 43. Decrypt the given ciphertext…
A: To decrypt the ciphertext 476 089 048 129 and find the original message. When given n = 713 = 23 ·…
Q: 1. The following sentence was encoded using the Cesar Cipher, your job is to decode it: KRZ DUH BRX.
A: 1. The following table is used to decrypt the message.
Q: In a single-parity-check code, a single parity bit is appended to a block of k message bits (mo, m1,…
A: Answer of above question are as follows :
Q: Decrypt the message EABW EFRO ATMR ASIN, which is the ciphertext produced by encrypting a plaintext…
A:
Q: The following affine cipher with the key k = (a, b) uses only uppercase letters of English alphabet…
A:
Q: a. Given p=23, q=7, and e=5, generate the public key (n,e) and the private key (n,d) using RSA Key…
A:
Step by step
Solved in 2 steps with 2 images

- Suppose that in a long ciphertext message the letter occurred most frequently, followed in frequency by. Using the fact that in the -letter alphabet, described in Example, "blank" occurs most frequently, followed in frequency by, read the portion of the message enciphered using an affine mapping on. Write out the affine mapping and its inverse. Example 2 Translation Cipher Associate the letters of the "alphabet" with the integers. Let and define the mapping by where is the key, the number of positions from the plaintext to the ciphertext. If our alphabet consists of through, in natural order, followed by a blank, then we have "letters" that we associate with the integers as follows:Suppose that in an RSA Public Key Cryptosystem, the public key is e=13,m=77. Encrypt the message "go for it" using two-digit blocks and the 27-letter alphabet A from Example 2. What is the secret key d? Example 2 Translation Cipher Associate the n letters of the "alphabet" with the integers 0,1,2,3.....n1. Let A={ 0,1,2,3.....n-1 } and define the mapping f:AA by f(x)=x+kmodn where k is the key, the number of positions from the plaintext to the ciphertext. If our alphabet consists of a through z, in natural order, followed by a blank, then we have 27 "letters" that we associate with the integers 0,1,2,...,26 as follows: Alphabet:abcdef...vwxyzblankA:012345212223242526Use the alphabet C from the preceding problem and the affine cipher with key a=11andb=7 to decipher the message RRROAWFPHPWSUHIFOAQXZC:Q.ZIFLW/O:NXM and state the inverse mapping that deciphers this ciphertext. Exercise 7: Suppose the alphabet consists of a through z, in natural order, followed by a colon, a period, and then a forward slash. Associate these "letters" with the numbers 0,1,2,...,28, respectively, thus forming a 29-letter alphabet, C. Use the affine cipher with key a=3andb=22 to decipher the message OVVJNTTBBBQ/FDLWLFQ/GATYST and state the inverse mapping that deciphers this ciphertext.
- Suppose that in an RSA Public Key Cryptosystem, the public key is. Encrypt the message "pay me later” using two-digit blocks and the -letter alphabet from Example 2. What is the secret key? Example 2 Translation Cipher Associate the letters of the "alphabet" with the integers. Let and define the mapping by where is the key, the number of positions from the plaintext to the ciphertext. If our alphabet consists of through, in natural order, followed by a blank, then we have "letters" that we associate with the integers as follows:a. Excluding the identity cipher, how many different translation ciphers are there using an alphabet of n "letters"? b. Excluding the identity cipher, how many different affine ciphers are there using an alphabet of n "letters," where n is a prime?Suppose that in an RSA Public Key Cryptosystem. Encrypt the message "algebra" using the -letter alphabet from Example 4. Use two-digit blocks. Use three-digit blocks. What is the secret key?
- Suppose that in a long ciphertext message the letter occurred most frequently, followed in frequency by. Using the fact that in the -letter alphabet, described in Example, occurs most frequently, followed in frequency by, read the portion of the message enciphered using an affine mapping on. Write out the affine mapping and its inverse.In the -letter alphabet described in Example, use the affine cipher with keyto encipher the following message. all systems go What is the inverse mapping that will decipher the ciphertext? Example 2 Translation Cipher Associate the letters of the "alphabet" with the integers. Let and define the mapping by where is the key, the number of positions from the plaintext to the ciphertext. If our alphabet consists of through, in natural order, followed by a blank, then we have "letters" that we associate with the integers as follows:Suppose the alphabet consists of a through, in natural order, followed by a blank, a comma, and a period, in that order. Associate these "letters" with the numbers, respectively, thus forming a -letter alphabet,. Use the affine cipher to decipher the message if you know that the plaintext message begins with "" and ends with ".". Write out the affine mapping and its inverse.
- Suppose that in an RSA Public Key Cryptosystem. Encrypt the message "pascal" using the -letter alphabet from Example 4. Use two-digit blocks. Use three-digit blocks. What is the secret key?What is the decryption function for an affine cipher if the encryption function is c = (15p + 13) mod 26?Suppose that the most common letter and the second most common letter in a long ciphertext produced by encrypting a plaintext using an affine cipher f (p) = (ap + b) mod 26 are Z and J, respectively. What are the most likely values of a and b?

