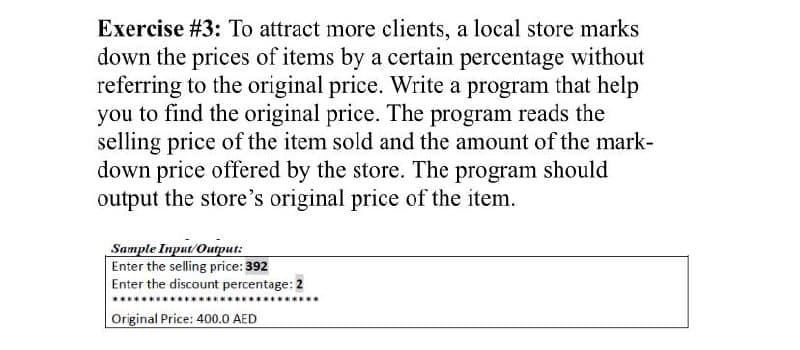
Exercise #3: To attract more clients, a local store marks down the prices of items by a certain percentage without referring to the original price. Write a program that help you to find the original price. The program reads the selling price of the item sold and the amount of the mark- down price offered by the store. The program should output the store's original price of the item. Sample Input/Ouqput: Enter the selling price: 392 Enter the discount percentage: 2 Original Price: 400.0 AED
Q: 47. Answer items a, b, and c below based on the following relation and dependencies.…
A: a. and b. The candidate key of the relation T_Participation is (StudentID,Activity ID) however…
Q: Calculate the following if the computer's memory capacity is 32 kilobytes and the storage location…
A: Introduction: The shelf locations you establish in DFSMSrmm are grouped to form a storage location.…
Q: 3.11 (Modified Account Class) Modify class Account (Fig. 3.8) to provide a method called with- draw…
A: public class Account { private String name; // instance variable private double balance; //…
Q: You can improve only one type of memory: which would it be and why? Semantic memory, episodic…
A: Semantic memory, episodic memory, procedural memories these are the three types of memories and…
Q: The national identity card system's information security Computer science
A: Introduction: Creating a National Identification System: When interoperability is tried in more…
Q: Describe how encryption works.
A: Introduction Encryption: Encryption can help safeguard data sent, received, and stored by a device.…
Q: What strategies and technologies are available for dealing with pre- and post- release defects?
A: The following are examples of software defects: Error in computation: A computation error caused the…
Q: A computer has two parts: the brain and the body.
A: - We have to talk about the two parts of computer in reference to the brain and body.
Q: What element in the IP header can be used to ensure that a packet is forwarded through a maximum of…
A: Introduction: The header includes details such as IP version, source IP address, destination IP…
Q: What operations can a red-black tree execute in O(log n)? All of the above a) Insertion and deletion…
A: The Answer is in step2
Q: What is a good example of python code for creating an application?
A: Introduction: Python is well-known in the coding and data science fields as one of the most popular…
Q: To contrast unstructured versus organized data, use an example.
A: Introduction: Structured data is like extremely particular and is recorded in a set format, while…
Q: What effect does "Race Condition" have on a computer's operating system?
A: Race Condition effect on Operating System.
Q: Vggn
A: VGN stands for video gamer network.
Q: A set of test requirements differs from a set of test criteria in software engineering.
A: Introduction: Test criteria assist the tester in organising the testing process.
Q: Write a note on the softwares used for online education and collaboration with suitable examples
A: Introduction Write a note on the software's used for online education and collaboration with…
Q: What operations can a red-black tree execute in O(log n)? All of the above a) Insertion and deletion…
A: Introduction: For insertion, search, and deletion, red-black trees provide logarithmic average and…
Q: Describe in your own words what is Fizzbuzz programming?
A: Given To know about the Fizzbuzz programming
Q: It is also known as a hub, repeater, firewall, T-connector, or bridge, depending on its function.
A: Network devices are the hardware that permits the connection of many source and destination nodes as…
Q: What is the one-bit half adder's purpose? What is the total number of inputs and outputs? What logic…
A: Introduction: Adder: An adder is a digital circuit that performs number addition.
Q: HOW TO KNOW IF MY INPUT/ STUDENT ID IS VERIFIED AND NOT VERIFIED, IF NOT, ASK THE USER AGAIN TO…
A: Modified code: student_213 = {} # dictionary of student information print…
Q: How many strings of letters from the set {A, B} have length 11 and have exactly 4 A's (repeated…
A: The Answer is given in step-2.
Q: w many ways are there to arrange the letters in the word "ABBCCCDDDD"? now it's not a real word, but…
A: Here in this question we have given a word ABBCCCDDDD and we have asked to find the number of ways…
Q:
A: Begin Take the two values x and y. Compute the sum. Print the sum. End
Q: Controlling Light is defined as follows :
A: The answer of this question is as follows:
Q: Controlling Light is defined as follows:
A: answer is- Light controlling is the ability to regulate the level and quality of light in a given…
Q: Write a C program that inputs number of rows in a class room (r) and number of seats in the row (rs)…
A: Q: Program the given in C language
Q: With respect to the virtual reality e-commerce website, which of the following measurable…
A: The answer for mcq with explanation is given below
Q: Give an example of why a network operator might want one class of packets to be prioritized over…
A: Solution : Packets that are being transmitted contain various sorts of data, and based on the type…
Q: Controlling Light is defined as follows :
A: Introduction: The capacity to manage the amount and quality of light in a particular place for…
Q: What are some of the reasons why website hacking is a problem?
A: The solution is as follows: There are many reasons why hacking a website is a concern.Because of a…
Q: What exactly is a reverse proxy server, and why would you want to use one in your network…
A: Introduction : Server for Reverse Proxy : It manages traffic flowing from the external network or…
Q: Can someone tell me why the program is skipping my code, it is just executing the first prompt.…
A: 1) Below is your updated program which fixes the issue in your program. 2) In you program scanf…
Q: What are the most important competitive advantages of Big Data?
A: Introduction: Massive, difficult-to-manage data quantities — organised and unstructured – regularly…
Q: Design a 512 MByte memory using 64M*4 chips, with 8-bit read/write operations and byte…
A: Read/Write operation: Memory unit consists of two types of operation i.e read and write operation.…
Q: Explain the significance of the Software Requirement Specification Document and the components of…
A: - We have to talk about the use and parts of SRS.
Q: Explain, in 20 words or less, how you would define a heuristic function for the situation you choose…
A: Introduction: A heuristic function (algorithm), often known as a heuristic, is a shortcut to solving…
Q: Which memory type is utilized for primary storage?
A:
Q: WHY DO STORAGE FACILITIES AUCTION LOCKERS WITHOUT FIRST
A: Introduction
Q: tes 4 by 4 matrices with random integers and generate two matrices called A and B. Write two other…
A: Given: Write a function that generates 4 by 4 matrices with random integers and generate two…
Q: Explain the weiler-Atherton algorithm in the context of a polygon. Give an example of the…
A: The wailer – Atherton method is a polygon clipping technique that is utilized in a variety of fields…
Q: Job portal system: This system allows the students to search and apply for jobs etc. online. The…
A: Introduction Job portal system: This system allows the students to search and apply for jobs etc.…
Q: What exactly is a data mart? What is the purpose of a data mart?
A: Introduction: A data mart is a basic data ware house that is focuses on a particular topic or…
Q: It is important to understand the difference between RIP and EIGRP.
A: Introduction: 1. Routing Information Protocol (RIP): For data/packet transfer, RIP employs the…
Q: What is the significance of following a name convention?
A: INTRODUCTION: A naming convention is a set of standards used in programming to determine the…
Q: Q3| EVALUATIONS: Memory at address 0x00100250 contains the following 16 bytes of data: 00100250 58…
A: Please find below your answer in second step:
Q: What does it mean to say that a programming language is machine independent?
A: Introduction: Software that is not dependent on the characteristics of a particular system and may…
Q: What is the impact of a data leak on cloud security? What are some of the possible countermeasures?
A: Breach of data in the cloud The purposeful or inadvertent leaking of secure/confidential information…
Q: Transform the table into 1NF, 2NF, and 3NF. Create a database diagram afterward. program subject…
A:
Q: What are the advantages and disadvantages of formal methods? There should be at least four…
A: Introduction: To provide an explanation of the purpose of formal approaches.
Step by step
Solved in 4 steps with 2 images

- The client wants to be able to downgrade all employee’s security levels, if the employee has a specific role.Only an employee with a role of Security should be able to downgrade all employee’s security levels basedon their role.For example the client decides that all employees with a role of Scientist should no longer have access tosecurity level 2 rooms and wants to be able to downgrade their security level from 2 to 1. An employeewith the role of Security will then execute this program to downgrade all employees security level’s withthe role of Scientist. An employee’s security level should never be below 1. If an employee tries to executethis program with a role that is not Security then security should be alerted with the employee’s name.Again, I was unsure how to achieve this, but I have started a flowchart. Could you please finish theflowchart so that I can implement this within a programming language.Implement a program that calculates the bill of a sandwich stand. The program should ask theuser to enter the quantity of each of the items. Then compute 13% GST on the total amountand generate a bill with items, their quantity along with price of each item and the total(inclusive GST). The stand has the following items:- Petti for $2.50- Drink for $1.25- Extra cheese topping for $1.25Programming in Python Unit 3 Assignment2InstructionsWrite a program to simulate a bank transaction. There are two bank accounts: checking and savings.First, ask for the initial balances of the bank accounts; reject negative balances and set to zero. Then askfor the transaction; options are deposit, withdrawal, and transfer. Then ask for the account; options arechecking and savings. Then ask for the amount; reject transactions that overdraw an account. At theend, print the balances of both accounts.
- Write a program that will send notification to Warehouse Manger when the inventory of an item become less than 2. If the quantity of the item is greater than 2 then it will display a message of "It's sufficient! Number of items is ", if not, it will send a notification "Need to purchase , quantity is low!". Sample 1: Enter the product name: Mechanical Pen Number of items in inventory: 2 Notification: Need to purchase " Mechanical pen", quantity is low!Suppose you save $100 each monthin a savings account with annual interest rate 3.75%. The monthly interest rateis 0.0375 / 12 = 0.003125. After the first month, the value in the accountbecomes100 * (1 + 0.003125) = 100.3125After the second month, the value in the account becomes100 + 100.3125) * (1 + 0.003125) = 200.938After the third month, the value in the account becomes(100 + 200.938) * (1 + 0.003125) = 301.878and so on.Write a program that prompts the user to enter an amount (e.g., 100), the annualinterest rate (e.g., 3.75), and the number of months (e.g., 6) and displays theamount in the savings account after the given month.Convert the Java program below into an algorithm: package classProg; import java.util.Scanner; class Client { String name; int amount; Client(String name, int amount) { this.name = name; this.amount = amount; } public String toString() { return "\n Customer: \n" + name + " " + amount + " cents"; } } public class Main { Client client[]; static Scanner sc = new Scanner(System.in); int totalFifty, totalTen, totalFive; int currentIndex; Main(int no) { client = new Client[no]; currentIndex = 0; totalFifty = totalTen = totalFive = 0; } /** * Method to search a client name in the array of object * @param name - name to search * @return * If found returns the found index position * If not found returns -1 */ int findClient(String name) { for(int c = 0; c < currentIndex; c++) if(client[c].name.equalsIgnoreCase(name)) return c; return -1; } /** * Method to add a client to array of…
- Write a program that converts a time from 24-hour notation to 12-hour notation. The following is a sample interactionbetween the user and the program. Enter time in 24-hour notation:13:07That is the same as 1.07 PMAgain? (y/n)y Enter time in 24-hour notation:10:15That is the same as 10:15 AMAgain? (y/n)y Enter time in 24-hour notation:10:65There is no such time as 10:65Try again:Enter time in 24-hour notation:16:05That is the same as 4.05 PMAgain? (y/n)nEnd of program Define an exception class called TimeFormartException. If the user enters an illegal time, like 10:65or even gibberish like &&*68, your program should throw and handle a TimeFormatException.I am writing this program that gives the user options. When I choose "make a deposit" and "then see balance" the amount entered is not accumulating and printing as Ending balance. How can I do that? how can I acculmualte all the money entered ? a lot of times and them print whenever I ask for? I copied it here and attached pictures import java.util.*; public class AccountTransactionAssignment { public static void main(String[] args) { Scanner console= new Scanner(System.in); welcomeMenu(); differentOperations(); } public static void displayMenu() { System.out.println(); System.out.println("Enter your choice: "); System.out.println("\tB See Balance"); System.out.println("\tD Make Deposit"); System.out.println("\tW Make a Withdrawal"); System.out.println("\tQ Quit "); } public static char getInput() { Scanner console= new Scanner(System.in); String temp= console.next().toUpperCase(); returntemp.charAt(0); } public static void welcomeMenu() { Scanner console= new…Correct answer will be upvoted else Multiple Downvoted. Don't submit random answer. Computer science. How about we characterize a casualty substance: a casualty has a name (not really extraordinary) that comprises just of lowercase Latin letters and an integer doubt esteem. Toward the beginning of the program the client enters a rundown of n casualty names into an information base, every doubt esteem is set to 0. Then, at that point, the client makes questions of two sorts: 1 I x — set the doubt worth of the I-th casualty to x; 2 q — given a string q observe the most extreme doubt worth of a casualty whose name is a coterminous substring of q. Just to remind you, this program doesn't eliminate individuals, it just assists with looking for the names to record in a genuine scratch pad. Consequently, the rundown of the casualties in the data set doesn't change all through the questions. What are you sitting tight for? Compose that program now! Input The main line…
- Create a java program that will record 5 purchases, for two clients at store B, separately. The program should only include purchases above 100 rand and bellow 200 rand. Furter, the program should compare the purchases of the two clients and give 10 percent discount on the total amount paid by the client and reimburse the client.MastermindIn this assignment, you will program the well-known game Mastermind. In Mastermind, player 1creates a pattern consisting of a pre-approved number of colored pins. Then player 2 has to guessthis pattern in as few turns as possible. Each turn, player 2 can guess what the pattern mightbe. Player 1 will then tell player 2 how many correct colors were guessed, and how many of thosecorrectly guessed colors were guessed in the right place. Player 2 can then use this information toimprove their guess for the next turn. When player 2 guesses the correct pattern, the game ends.Write a program that acts as player 1 of the Mastermind game. This program will generate a(random) pattern, and will play according to the game’s rules, with a human acting as player 2.The program should stop when the user guesses the pattern.Additionally, the program has to conform with the following specifications:1. Because of practical reasons, the pattern will consist of capital letters instead of colors.2.…Write a program to simulate a Banking Application with the following functionality: Setup an Account Holders Profile with Name, Address, phone number and e-mail as user inputs Open an account - Checking and Savings Deposit Money into Checking or Savings account as per users preference Withdraw Money from Checking or Savings account as per users preference Technical Requirements: Use I/O methods, if statements, switch statements, while, do-while and for loops, inputs and outputs and UTIL scanner methods

