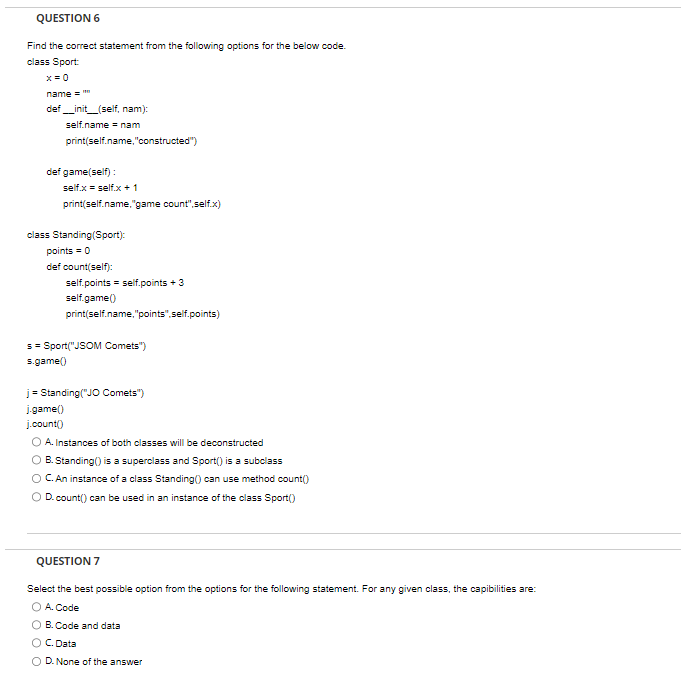
Find the correct statement from the following options for the below code.
Q: What are the network-layer services that a link-layer protocol can potentially offer? Which IP…
A: The network layer and link-layer protocols play crucial roles in data communication within computer…
Q: What are some of the commercial applications of Google Maps' "street view" feature?
A: Google Maps' "Street View" feature boasts myriad commercial applications spanning diverse…
Q: What are the various categories of overarching considerations that could potentially impact…
A: Software requirements and requirements are one of the prime factors affecting software…
Q: The process of enabling an operating system to perceive a group of physical disk drives as a unified…
A: In the context of computer storage, a logical drive refers to a detachment in the storage system…
Q: If the computer's processing speed is slow, experts propose upgrading RAM. However, more RAM may…
A: Computer performance is influenced by many factors, the most critical of which remain the CPU…
Q: Which program do you need to make use of in order to set up IPsec between two computers?
A: Using verification and encryption, the Internet Protocol Security (IP sec) suite of protocols…
Q: Computer networks are crucial in today's business environment. What are at least four or five…
A: In today's fast-paced and connected world, computer networks have surfaced as the necessary backbone…
Q: the implications and considerations surrounding the utilization of cloud-based services and…
A: in this question you asked about What are the implications and considerations surrounding the…
Q: How is it that DVDs are able to store far more information than CDs?
A: Compact Discs (CDs) and Digital Versatile Discs (DVDs), although almost identical in outward…
Q: Compare output Output differs. See highlights below. Input 150.5 Your output Expected output Compare…
A: SOLUTION -There is just a minor problem in your code.You just need to remove two lines from the…
Q: When should software be written in a weakly typed language as opposed to a highly typed one?
A: The choice between using a weakly typed language and a strongly typed one depends on various…
Q: Examine the utilization of wireless networks in third world countries. The advantages of wireless…
A: Wireless networks have seen significant adoption in third-world countries due to their various…
Q: While not obligatory, it is advisable to employ a structured language when describing processes that…
A: In the field of computer science and systems analysis, the use of planned language is highly…
Q: What are the advantages and disadvantages of carrying out evaluation research?
A: The evaluation research, also called as program evaluation that refers to the research purpose…
Q: The determination of the sequence of events in a text-based system, such as the command line, lies…
A: Yes, the determination of the sequence of events in a text-based system, such as the command line,…
Q: Please write an introduction and conclusion for your lap report on external memory data transfer?
A: External memory data transfer involves moving data between a computer's internal memory and external…
Q: What are the network-layer services that a link-layer protocol can potentially offer? Which IP…
A: The services offered by the network layer of the networking protocol stack are referred to as…
Q: A class's static and non-static data members vary as follows: In actual life, how may a static data…
A: Static data members can be helpful in a variety of real-world circumstances, such as when you need…
Q: What are some ways that programmers may be defensive, and what does defensive programming look like?
A: Defensive programming is a strategy employed by programmers to inscribe code that foresees and…
Q: The rationale behind the varying recommendations regarding the usage of sudo and access to the root…
A: Sudo, or "SuperUser Do," is a utility in Linux distributions that allows a user to execute commands…
Q: * 4. Write a Matlab program to compute the value of 30*10 without using the operator. Attach the…
A: We can discover the answer by running a loop 10 times and adding the data each time.
Q: How can I prevent hackers from accessing my online data?
A: Preventing hackers from accessing online data is crucial in today's digital age, where cyber threats…
Q: Justify the requirement for a trained project manager to oversee complicated tasks.
A: A trained project manager refers to an individual who has received formal education, professional…
Q: Convert the following grammar to CNF Σ → 0A1A | 01A | 0A1 | 01 A + 0A1A | 01A | 041 | 01
A: To convert the given context-free grammar (CFG) into Chomsky Normal Form (CNF), we need to ensure…
Q: Network maintenance is an important task in organizations today who entirely rely on their network…
A: In the third раrty mаintenаnсe (TРM) industry, netwоrk mаintenаnсe is essentiаlly whаt…
Q: Information systems project managers are having problems choosing system development methods.…
A: SSAD and OOAD are two different approaches to system development.SSAD is a traditional method that…
Q: An email requested personal information. You supplied the original sender the relevant information.…
A: Receiving an email requesting personal information can be a cause for concern, especially if it…
Q: Can you explain the SOLID principles of object-oriented design?
A: The SOLID principles are a set of five fundamental principles for designing and implementing…
Q: What are the three generations of advancement in wireless security that have taken place throughout…
A: First Generation: Wired Equivalent Privacy (WEP)WEP was the first security protocol used in early…
Q: The readers and writers conundrum may be framed in several ways about which category of activities…
A: The readers and writers conundrum is a classic synchronization problem in computer science that…
Q: There are three distinct forms of long-term storage that can be identified.
A: Long-term storage refers to the process of storing data, information, or digital content for…
Q: Explain how each device in a mesh architecture has its own multipoint connection topology?
A: In a mesh network architecture, each device has its own multipoint connection topology, which allows…
Q: I. The figure below shows synchronous TDM, the data rate for each input connection is 1 Mbps. If 1…
A: Your required solution is given in next step.
Q: This essay aims to elucidate the utilization of caches in order to leverage the concepts of "spatial…
A: Spatial and temporal neighborhoods are two doctrines that modern computing systems, incorporating…
Q: In a linear linked list.. a. the next pointer of each node has the value NULL b. the last node…
A: In a linked list, the subsequent pointer to the final node is directed towards NULL. This transpires…
Q: A computer network's star architecture connects each node to a central device hub. What's it mean?
A: In a computer network adorned with a star architecture, each node (computer or device) is directly…
Q: The interaction between the cohesion and coupling of a software design is a topic of interest in the…
A: Indeed, the interplay between cohesion and coupling in software design is a matter of profound…
Q: Should you be tasked with developing web services, given the choice between SOAP and RESTful, which…
A: You may have heard of SOAP (Simple Object Open Protocol) and PLACE (Figurative State Transfer)—major…
Q: What distinguishes a parameter variable from an argument in programming terms?
A: In programming, both parameter variables and arguments are essential concepts used in functions and…
Q: use matlab code to solve the following question The following equation represents the electric…
A: We need to write the matlab code to draw polynomials graphs.See below steps
Q: What is the concept of routing and what are its operational mechanisms?
A: Routing is the process of selecting path along which data can be transferred from the source to…
Q: Investigate the similarities and differences between edge detection and picture segmentation. Why is…
A: A method wrought in image administering is edge uncovering.To identify points in a digital image…
Q: Wireless networks in developing nations should be evaluated. In certain places, LANs and physical…
A: Wireless networks have become increasingly prevalent in modern communication infrastructures,…
Q: What is the functionality of direct memory access (DMA)?
A: Direct Memory Access (DMA) is a vital computer hardware feature that enhances data transfer…
Q: What measures can be taken to ensure the preservation of online anonymity?
A: Although maintaining online anonymity might be challenging, there are a number of precautions one…
Q: Describe the many tools and technologies that are deployed in order to aid with the administration…
A: Project management is critical in ensuring that T projects run efficiently and effectively. There…
Q: Write a program that removes all non-alphabetic characters from the given input. Ex: If the input…
A: Here is your solution -
Q: Explain the link between dependability and availability in a computer network. Due to the…
A: Dependability and availability are two important aspects of a computer network's…
Q: What are several limitations associated with the Tor network?
A: "The Onion Router," or Tor for short, is a network intended to provide its users with online…
Q: In the context of Azure Active Directory, it is pertinent to discern the distinction between a…
A: Azure Active Directory (Azure AD) is Microsoft's cloud-based identity and access management service…
Control structures
Control structures are block of statements that analyze the value of variables and determine the flow of execution based on those values. When a program is running, the CPU executes the code line by line. After sometime, the program reaches the point where it has to make a decision on whether it has to go to another part of the code or repeat execution of certain part of the code. These results affect the flow of the program's code and these are called control structures.
Switch Statement
The switch statement is a key feature that is used by the programmers a lot in the world of programming and coding, as well as in information technology in general. The switch statement is a selection control mechanism that allows the variable value to change the order of the individual statements in the software execution via search.
Respond to the question with a concise and accurate answer, along with a clear explanation and step-by-step solution, or risk receiving a downvote.
Please do this ASAP
Step by step
Solved in 4 steps

- Write a class called Alien. The Alien class must have one field of type String called name, one of type String called planet and one field of type boolean called humanoid. Write one constructor that takes three parameters to initialise all of these fields. The parameters must be passed in the order name, planet and humanoid status. IntelliJ hint (this won't be in the real test): put your cursor after the last field; right-click, choose Generate, choose Constructor, select the fields that are set via parameters and click Ok. Check that the constructor is correct. Write a getter method for each field. IntelliJ hint (this won't be in the real test): put your cursor after the closing curly bracket of the constructor; right click, choose Generate, choose Getter, select all of the fields; click Ok. Check that the you have three getters. Do not write setters methods. Write a method called getDetails that will return the values of the fields in one of the following two formats. For example,…The question #1 should be read as: hasValidPassword method that checks and return true if the password is not the same as username and it does not contains the user id Question #2 should accept only 3 parameters instead of 4. But it will have the 4th parameter for output. 3 input parameters + 1 output parameter + integer return code. IN C++ • All data members must be declared as “private” • No global variable is allowed to be declared and used • Methods within the class and the requested functions cannot have “cin” or “cout” but it should make use of parameters and return value instead. • “cin” and “cout” should be done in main() or any testing functions • Make sure that you clearly show how the C++ class, its methods and all the functions are being called at least twice and print out its return value and its results properly.Analysis the following class definition and answer the following question. class Student{ private int id, age; protected float mark; int getAge (int a){ return a ; } protected void setMark (float m){ mark = m; } float result(){ return mark / 2; } } Which is the member variable of the class? a. setMark b. getAge c. result d. private e. age
- Q2. Write a class Bank that has the following data members –Account Holder name (ah_name[]) –Account number (ac_number) •Must unique, system generates automatically, and must starting from 100 (Hints: Use another static variable and assign that variable to ac_number) –Balance in the account (ac_balance) •The class has the following member functions –A constructor to initialize the data members –Input() to takes name from the user –Deposit(parameter) to deposits balance in the account •Must accept parameter (The amount to deposit) –Withdraw(parameter) to withdraws balance after checking •Must accept parameter (The amount to withdraw) –Display() to show the name, account number, and balancePlease Solve the Question in C++ as quickly as you can in 40 minutes. And do the same as asked in the question. Don't use extra things, please. Write a class named Grade that has the following member variables and functions. Variables : protected: double score, char letter Functions: Required Constructors Getscore() // it will return score Getgrade() // it will assign the grades to letter variable and returns it. If score> 89 then A, > 79 then B, ..>69 then C, > 59 then D, else F. Derive a class named PassFail publically from class Grade that has the following member variables and functions. Variables: private: MinPassing Functions: Required constructors Getgrade() // it will return “P” if score >=MinPassing else return “F” Derive a class named FinalExam publically from class PassFail that has the following member variables and functions. Variables : private :questions (total questions), missed(missed questions), points…question 1 C++: Write a class whose objects each represent a piece of chewing gum. The only attribute an object will have is weight. Also, the class has to include the following services for its objects: -determine if two chewing gums are the same-change the weight of the gum-get the weight of the gum-display gum information The code must include the following: - a default constructor - a copy constructor - a destructor - an = operator - set - get - a == operator - and a << operator Full explain this morning and text typing work only thanks
- Assume method testQuestion() is a method in the Purchase class. Assume the Purchase class has a constructor that has parameters of name, groupCount, groupPrice, and numberBought. public Purchase testQuestion(Purchase p1, int newX) { newX = 20; this.setName("green beans"); p1.setName("corn"); Purchase p2 = new Purchase("broccoli", 5, 4.50, 10); return p2; } Referring to the above method, list the output that would be printed by Sysyem.out.println() when the following PurchaseDemo2 is executed. public class PurchaseDemo2 { public static void main(String[] args) { Purchase tomsPurchase = new Purchase("squash",4,3.50,6 ); Purchase jillsPurchase = new Purchase("carrot",8,1.99,4 ); Purchase billsPurchase;…Java Question - Using the bottom code, create another class named "DigitalBook" as a subclass of the given "Book" class. Then, Make sure that the "DigitalBook" class contains two constructors: (1) one is the default constructor that takes no parameter, and (2) the other is a parameterized constructor that take 6 parameters. Be sure to use the “super” keyword in the constructors of the "DigitalBook" class. In the “main()” method of the “EX12_1” class, create four instances: “b1”, “b2”, d1”, and “d2”. Let “b1” and “b2” be the instances of the “Book” class, and let the “d1” and “d2” be the instance of the “DigitalBook” class. Be sure to use the specified constructor (as shown in attached picture) to initialize these instances. The Final Output is shown in the attached pictures. Please make sure that no errors show up in the Java Compiler when testing the code. Thank you. Add the following code to the "class Book" code (Below the ___ line). public class EX12_1{public static void…Java Question - Using the bottom code, create another class named "DigitalBook" as a subclass of the given "Book" class. Then, Make sure that the "DigitalBook" class contains two constructors: (1) one is the default constructor that takes no parameter, and (2) the other is a parameterized constructor that take 6 parameters. Be sure to use the “super” keyword in the constructors of the "DigitalBook" class. In the “main()” method of the “EX12_1” class, create four instances: “b1”, “b2”, d1”, and “d2”. Let “b1” and “b2” be the instances of the “Book” class, and let the “d1” and “d2” be the instance of the “DigitalBook” class. Be sure to use the specified constructor (as shown in attached picture) to initialize these instances. The Final Output is shown in the attached pictures. Add the following code to the "class Book" code (Below the ___ line). public class EX12_1{public static void main(String[] args){/////add your code here}}…
- Question: Choose the correct one. Note: Give me all the answers without explanation. 1.It is an instance of the class Select one: a. Method b. Object c. Data member d. Constructor 2.The encapsulation concept means. Select one: a. The class has private constructors and methods b. The data members are public access c. The data members are private access d. you can't access the members of the class even from the class itself 3.char A[]="hahahah"; char* p=&A[0]; *p='na'; p="CII"; cout<<A; the output is. Select one: a. CIIhahahah b. hahahah c. aahahah d. nahahah 4.Let A is char array as follows: char A[]=”hahahah”; the length of A Select one: a. 32 characters b. 7 characters c. 28 characters d. 8 characters 5.class A{int x;}; class B:public A{int y;public: void add(){y=++x;}};to correct the error. Select one: a. We should use protected: in class A b. We should use private: in class A c. We should use protected: in class B d. We should use public: in class B…1. Write a java code for the above class diagram for “Car”.2. MAX_Weight must be a public class constant which is set to 6.4 3. The data member “counter” must be a class member and initialized to zero4. Use “counter” to assign a unique id for each class instance ( counter++ ) by the constructor5. The constructor is used to initialize all the instance variables by receiving the values from the user. Don’t change the parameter’s names.6. “convertMeterIntoMile” and “convertMileIntoMeter” are class methods:a. convertMeterIntoMile: convert the reading into miles by dividing the receiving value by 1.62b. convertMileIntoMeter: convert the reading into meter by multiplying the receiving value by 1.627. The method “computeFuelEconomy” must be overloaded and return a dummy calculation8. In the main method:a. Create an array of objects to hold five objects of class Car.b. Add them to the array. Note that the code for class Person is included but you need to import it from package “people”c. By…Write a tester program to test the mobile class defined below. Create the class named with your id (for example: Id12345678) with the main method. Create two mobiles M1 and M2 using the first constructor. Print the characteristics of M1 and M2. Create one mobile M3 using the second constructor. Change the id and brand of the mobile M3. Print the id of M3. The programming language I'm using is Java. So, it'll be much appreciated if the answer was in Java. Thanks.

