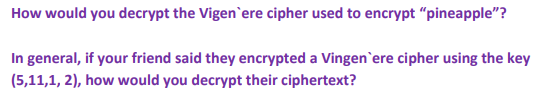
How would you decrypt the Vigen`ere cipher used to encrypt "pineapple"? In general, if your friend said they encrypted a Vingen`ere cipher using the key (5,11,1, 2), how would you decrypt their ciphertext?
Q: If U is encrypted as B by shift cipher transformation then decrypt the message WMPGLY using the same…
A:
Q: Suppose that the ciphertext ERC WYJJMGMIRXPC EHZERGIH XIGLRSPSKC MW MRHMWXMRKYMWLEFPI JVSQ QEKMG was…
A:
Q: Digital signatures have a potential weakness due to lazy users. In e-commerce transactions, a…
A: digital Signatures: To provide authenticity for a report or a virtual message, a unique…
Q: Encrypt the message AT FOUR AIR STRIKE ON TARGET using a tabular transposition cipher with…
A: The objective is to encrypt the message AT FOUR AIR STRIKE ON TARGET using a tabular transposition…
Q: Encrypt the message KILLTHEBEAST using shift cipher with K=18.
A: We have K=18 Now, in KILLTHEBEAST, the letters correspond to numbers in the English alphabet. K I…
Q: Use the Vigen`ere cipher with key BLUE to encrypt the message SNOWFALL.
A: A =0, B =1, C =2, D = 3, E = 4, F = 5, G = 6, H = 7, I = 8, J =9, K = 10, L = 11, M = 12, N = 13, O…
Q: Hill Cipher for m=2, then correct key is
A: This is a problem of Cryptography, Number Theory, and Modular Arithmetic. Therefore it is a problem…
Q: Encipher these messages using a Rosicrucian cipher: 1. SWIM 2. BASEBALL 3. НОСКEY 4. FOOTBALL 5.…
A: Rosicrucian Chipher : For ciphering the alphabets consider the boxes and the dots corresponding to…
Q: What is the Plaintext of the following Ciphertext, based on Caesar cipher algorithm, if the KEY=5?…
A:
Q: (b) Cindy wants to send the message m = 53 to Dan. Use the public key for this cryptosystem to…
A: Algo: 1) Find Alice public key (n, e) Where n=p.q 2) Find remainder C when Me is divided by n. 3)…
Q: Queston 2 only please
A: The given Caesar encryptions is OKBDRZBYFSNOCOXYEQRDYCKDSCPIOFOBIWKXCXOONCLEDXYDOFOBIWKXCQBOON.In…
Q: 5. (a) Encipher the message HAVE A NICE TRIP using a Vigenère cipher with the keyword МАТНH. (b) The…
A:
Q: Mr. Basset finally got a new lock to keep people from stealing things from his gym locker! While…
A: In this question we have to find the possibility of 4 digit code from 1 to 20 .
Q: Encrypt the message ATTACK using the RSA system with n = 43 · 59 and e = 13, translating each letter…
A:
Q: A supermarket send codes for $0.25 off a bag of chips to its rewards members. Each coupon code will…
A: Number of letters allowed = 24 Number of digits allowed = 7 Each coupon code will have one digit…
Q: In the use of RSA Cryptography, for the public key (11, 65), what is the decrypted original message…
A: Solution :-
Q: Decrypt these messages that were encrypted using the Caesar cipher.a) EOXH MHDQVb) WHVW WRGDBc) HDW…
A:
Q: Express the Vigen`ere cipher as a cryptosystem.
A:
Q: Assume they are used for an encryption in Hill ciphers. In each case, find two plaintexts that…
A: The matrices given are as follows: 1322 and 131242351 For 1322 Let x1y1 and x2y2 be two plain…
Q: a) What is the difference between a public key and a private key cryptosystem? b) Explain why using…
A:
Q: What is the secret message produced from the message “MEET YOU IN THE PARK” using the Caesar cipher?
A:
Q: Use the Caesar cipher (shift of 3 places) to encrypt BRAVE
A: Since, A=0 O=14B=1 P=15C=2 Q=16D=3 R=17E=4…
Q: 12 13 Suppose a company needs temporary passwords for the trial of a new timè management software.…
A:
Q: Encrypt the message AT TEN HEAD NORTH TO TRENCHES using a tabular transposition cipher with rows of…
A:
Q: Suppose each license plate in a certain state has two digits, followed by two letters, followed by…
A:
Q: Encrypt the message AT FOUR SURVEILLANCE ON TARGET using a tabular transposition cipher with…
A:
Q: Suppose (n, d) = (55, 3) is the private key of an RSA cryptosystem. If the received ciphertext is C…
A:
Q: The message NOT NOW (numerically 131419131422) is to be sent to a user of the EIGamal system who has…
A:
Q: Once the length of the key string of a Vig`enere cipher is known, explain how to determine each of…
A: The length of the key's known. Let its k. therefore the text is going to be divided into groups of k…
Q: The ciphertext OIKYWVHBX was produced by encrypting a plaintext message using the Vigen`ere cipher…
A:
Q: Suppose a company needs temporary passwords for the trial of a new payroll software. Each password…
A: The company new password has 4 places to fill .First two places has to be filled by 25 capital…
Q: Suppose we decide to use Data Encryption Standard (DES) for data encryption. Given the initial…
A:
Q: Let us say that we are going to create five letter passwords from a set of 23 letters (all of the…
A:
Q: Explain why in any cryptosystem the number of possible ciphertexts must exceed the number of…
A: In order to have the cryptosystem perfectly secret, the number of possible ciphertexts must exceed…
Q: 2. Assume that the letters of the English alphabet will be converted to numerical forms as follows:…
A: The following steps are used to encrypt a message. Assign numbers to the alphabets. Replace the…
Q: A supermarket wants to send codes for $0.25 off a bag of chips to its rewards program members. Each…
A: Given, a supermarket wants to send codes for $0.25 off a bag at chips to its rewards program…
Q: If the given encrypted text is " VTXDUH" then the decrypted text using Caesar cipher will be, O…
A: The correct option is SQUARE. Use the given options to decrypt the given text. All the options has…
Q: If the given encrypted text is " PDWULA" then the decrypted text using Caesar cipher will be,
A: According to historical records, Caesar always used a shift of 3. As long as message recipient knew…
Q: How lany passwords can be created with two letters followed by two digits, if no letter or a digit…
A:
Q: 1. Develop a system (other than Substitution cipher, Transposition cipher, or Vigenère cipher) that…
A: Here, we discuss the Hill cipher method.
Q: If the given plain text is "METHOD " then the encrypted text using Caesar cipher will be, O PHWIRG O…
A:
Q: 1. Encrypt and decrypt the sentence “Pay more cash" using Hill Cipher with the key: 17 17 5 21 18 21…
A: First we convert given plaintext to 3x1 vectors then we use the key matrix to find the corresponding…
Q: If the Caesar cipher produced KDSSB ELUWKGDB, what is the plaintext message?
A: The encrypted message given is "KDSSB ELUWKGDB". Caesar cipher is a method to encrypt messages which…
Q: Determine the encryption and decryption codes of the indicated messages. A) Apply Shift Cipher to…
A:
Q: The message VAADENWCNHREDEYA was encrypted using the 2 3 4 [1 [2 4 1 Decrypt it. permutation a =
A: Given: Word- VAADENWCNHREDEYA
Q: In a lengthy ciphertext message, sent using a linear cipher C = a P +b (mod 26), the most frequently…
A:
Q: a. Given p=23, q=7, and e=5, generate the public key (n,e) and the private key (n,d) using RSA Key…
A:
Q: Suppose that you know that a ciphertext was produced by encrypting a plaintext message with a…
A:
Q: Suppose that when a string of English text is encrypted using a shift cipher f (p) = (p + k) mod 26,…
A:
Please explain and show step by step
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 2 images

- a. Excluding the identity cipher, how many different translation ciphers are there using an alphabet of n "letters"? b. Excluding the identity cipher, how many different affine ciphers are there using an alphabet of n "letters," where n is a prime?Suppose that in a long ciphertext message the letter occurred most frequently, followed in frequency by. Using the fact that in the -letter alphabet, described in Example, "blank" occurs most frequently, followed in frequency by, read the portion of the message enciphered using an affine mapping on. Write out the affine mapping and its inverse. Example 2 Translation Cipher Associate the letters of the "alphabet" with the integers. Let and define the mapping by where is the key, the number of positions from the plaintext to the ciphertext. If our alphabet consists of through, in natural order, followed by a blank, then we have "letters" that we associate with the integers as follows:Suppose that the check digit is computed as described in Example . Prove that transposition errors of adjacent digits will not be detected unless one of the digits is the check digit. Example Using Check Digits Many companies use check digits for security purposes or for error detection. For example, an the digit may be appended to a -bit identification number to obtain the -digit invoice number of the form where the th bit, , is the check digit, computed as . If congruence modulo is used, then the check digit for an identification number . Thus the complete correct invoice number would appear as . If the invoice number were used instead and checked, an error would be detected, since .
- The ciphertext OIKYWVHBX was produced by encrypting a plaintext message using the Vigen`ere cipher with key HOT. What is the plaintext message?Use the Caesar cipher (shift of 3 places) to encryptBRAVEOnce the length of the key string of a Vig`enere cipher is known, explain how to determine each of its characters. Assume that the plaintext is long enough so that the frequency of its letters is reasonably close to the frequency of letters in typical English text.
- Express the Vigen`ere cipher as a cryptosystem.a) What is the difference between a public key and a private key cryptosystem? b) Explain why using shift ciphers is a private key system. c) Explain why the RSA cryptosystem is a public key system.A department store wants to send codes for $15 off a $75 purchase to the subscribers of its e-mail list. The coupon code will have three letters, followed by one digit, followed by one letter. The letters P , Q , and R will not be used. So, there are 23 letters and 10 digits that will be used. Assume that the letters can be repeated. How many such coupon codes can be generated?
- Suppose that the most common letter and the second most common letter in a long ciphertext produced by encrypting a plaintext using an affine cipher f (p) = (ap + b) mod 26 are Z and J, respectively. What are the most likely values of a and b?Consider the affine cipher with key k = (k1, k2) whose encryption and decryption functions are given by (1.11) on page 43. Alice and Bob decide to use the prime p = 601 for their affine cipher. The value of p is public knowledge, and Eve intercepts the ciphertexts c1 = 324 and c2 = 381 and also manages to find out that the corresponding plaintexts are m1 = 387 and m2 = 491. Determine the private key and then use it to encrypt the message m3 = 173.A burger chain wants to send codes for a free small drink to the members of its kids club. The coupon code will have one letter, followed by two digits, followed by two letters. The letters R , S , T , and U and the digit 3 will not be used. So, there are 22 letters and 9 digits that will be used. Assume that the letters and digits can be repeated. How many such coupon codes can be generated?

