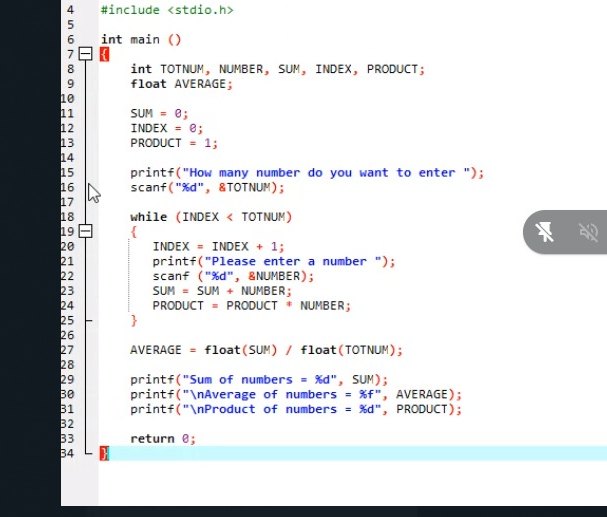
#include int main () int TOTNUM, NUMBER, SUM, INDEX, PRODUCT; float AVERAGE; SUM - e; INDEX = e; PRODUCT - 1; printf("How many number do you want to enter "); scanf("%d", &TOTNUM); while (INDEX < TOTNUM) INDEX = INDEX + 1; printf("Please enter a number "); scanf ("%d", &NUMBER); SUM = SUM + NUMBER; PRODUCT = PRODUCT * NUMBER; AVERAGE = float(SUM) / float(TOTNUM); printf("Sum of numbers = %d", SUM); printf("\nAverage of numbers = xf", AVERAGE); printf("\nProduct of numbers = %d", PRODUCT); return e;
#include int main () int TOTNUM, NUMBER, SUM, INDEX, PRODUCT; float AVERAGE; SUM - e; INDEX = e; PRODUCT - 1; printf("How many number do you want to enter "); scanf("%d", &TOTNUM); while (INDEX < TOTNUM) INDEX = INDEX + 1; printf("Please enter a number "); scanf ("%d", &NUMBER); SUM = SUM + NUMBER; PRODUCT = PRODUCT * NUMBER; AVERAGE = float(SUM) / float(TOTNUM); printf("Sum of numbers = %d", SUM); printf("\nAverage of numbers = xf", AVERAGE); printf("\nProduct of numbers = %d", PRODUCT); return e;
Chapter2: Using Data
Section: Chapter Questions
Problem 12PE
Related questions
Question
Rewrite the program with a little bit of changes in the codes
Transcribed Image Text:4
#include <stdio.h>
6
int main ()
int TOTNUM, NUMBER, SUM, INDEX, PRODUCT;
float AVERAGE ;
8
10
11
12
13
14
15
16
17
18
19E
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
SUM - 0;
INDEX = e;
PRODUCT = 1;
printf("How many number do you want to enter ");
scanf ( "%d", &TOTNUM);
while (INDEX < TOTNUM)
名
INDEX
INDEX + 1;
printf("Please enter a number ");
scanf ("%d", &NUMBER);
SUM = SUM + NUMBER;
PRODUCT = PRODUCT * NUMBER;
AVERAGE = float(SUM) / float (TOTNUM);
printf("Sum of numbers = %d", SUM);
printf("\nAverage of numbers = %f", AVERAGE);
printf("\nProduct of numbers = %d", PRODUCT);
return e;
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 4 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781305480537
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781305480537
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning