Let's play a guessing game! Create a public class name Guesser that provides a single class method named guessValue. guessValue accepts a single Secret instance which provide guess method that accepts an integer. If the integer is not the secret value, guess will throw exception. Otherwise, it does not.
Let's play a guessing game! Create a public class name Guesser that provides a single class method named guessValue. guessValue accepts a single Secret instance which provide guess method that accepts an integer. If the integer is not the secret value, guess will throw exception. Otherwise, it does not.
Chapter12: Exception Handling
Section: Chapter Questions
Problem 6PE
Related questions
Question
Answer the given question with a proper explanation and step-by-step solution.
qns: In Java please! There is no solution on the Internet that works, please don't copy from other answers because I have checked those
Transcribed Image Text:Created By: Geoffrey Challen / Version: 2021.9.0
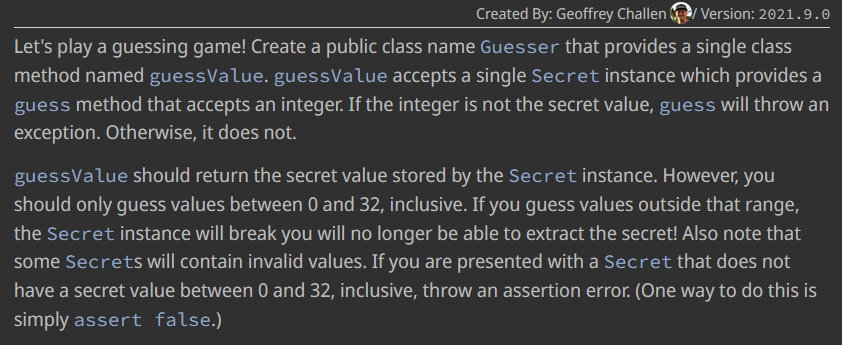
Let's play a guessing game! Create a public class name Guesser that provides a single class
method named guessValue. guessValue accepts a single Secret instance which provides a
guess method that accepts an integer. If the integer is not the secret value, guess will throw an
exception. Otherwise, it does not.
guessValue should return the secret value stored by the Secret instance. However, you
should only guess values between 0 and 32, inclusive. If you guess values outside that range,
the Secret instance will break you will no longer be able to extract the secret! Also note that
some Secrets will contain invalid values. If you are presented with a Secret that does not
have a secret value between 0 and 32, inclusive, throw an assertion error. (One way to do this is
simply assert false.)
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Follow-up Questions
Read through expert solutions to related follow-up questions below.
Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT