Show that there is no formal proof of p → qFp.
Q: ufferInfo method des
A: Syntax of GetConsoleScreenBufferInfo: BOOL WINAPI GetConsoleScreenBufferInfo( _In_ HANDLE ...
Q: ləgunu u rerted to armatted
A: The program code provided below opens a file named number_file.txt and for each section that begins...
Q: It's important to know what a heuristic is and how it's different from an algorithm, so we're going ...
A: The problem is based on the basics of algorithms.
Q: Let us know what this function does and why it's so important to u
A: Given To know about the function and it's uses
Q: Which of the following is not a problem that could be caused by disabling STP in a switched network?...
A: We are going to understand which problem can not arise if we disable STP in a switched network.
Q: Task1:In the driver file (main.cpp), perform the following sub-tasks.1.Create two objects of this cl...
A: “Since you have asked multiple questions, we will solve the first question for you. If you want any ...
Q: Find all solutions to cach of the following linear equations: a. 3x4 (mod 5) b. 4x4 (mod 6) c. 9x 12...
A:
Q: 2. Write a program that returns the minimum of a single-variable function g(x) in a given region [a,...
A: Step 1 INTRODUCTION: Python is a strong general-purpose and high-level programming language. It is u...
Q: ive at least two example questions you would want to answer as an analyst that relates to Inu + Neko...
A: Lets see the solution.
Q: Network Address 172.85.26.0/23 Chippendale LAN 12 Hosts Chippendale Ultimo LAN Glebe LAN 45 Hosts 85...
A: Given Network address is 172.85.26.0/23 IP address is 32 bits and 23 are network id bits. Host id bi...
Q: ) Define the term of methodologies, techniques, and tools?
A: Methodologies, tools and techniques are different terms, although they look similar but meaning of e...
Q: What is cold email software and how does it work
A: SUMMARY: -Hence, we discussed all the points.
Q: After learning the history of computer and the different computer generations, I want you to choose ...
A: - Solving the first three subparts according to the guidelines. - We have to talk about facebook. - ...
Q: respectively. Multiply the numbers stored in registers $1 and $s2. Save the lower 32bit in $t1 a upp...
A: l
Q: The goal of this assignment is to solve problems that involve flow of control with conditional state...
A: Here, I have to provide a C++ solution to the above question.
Q: What are the 3 layers that make up SDN? a. 1) The physical layer, 2) The network layer, and 3) The ...
A: - We need to talk about the three layers of SDN. - SDN has a defined layered architecture. It has th...
Q: Write a python code to build regression models using the following learning algorithm
A: import matplotlib matplotlib.use('GTKAgg') import matplotlib.pyplot as plt import numpy as np f...
Q: Switches make forwarding decisions: a. Using a routing table which maps IP addresses to specific po...
A: We know that whenever a packet arrives at a Router, destination IP address is examined of a received...
Q: What are virtual educational environments (VLEs)?
A: INTRODUCTION: In the given problem we are asked what are the virtual educational environments. So we...
Q: lication w
A: Web ApplicationsA web application is a client-side and server-side software application that is run ...
Q: Annotated Bibliography (APA) List ten sources (APA) To inform college students on how to pre...
A: APA clarified list of sources An explained book index is an extraordinary sort of catalog that gives...
Q: What kind of rule protect every right when we use each other content?
A: The rule to protect every right when we use each other content is Fair use. It is the rule which def...
Q: When you use GRETL, how do you run a model for a generalised least squares guess?
A: INTRODUCTION: GRETL is an open-source statistics tool that focuses on econometrics. For example, GN...
Q: Create a class called Distance containing two members feet and inches. This class represents distanc...
A: “Since you have posted a question with multiple sub-parts, we will solve first three subparts for ...
Q: ou are given two sequences, each of this X = (X[1]X[N]) and YYY One operation consists of the follow...
A:
Q: algorithms are used to solve what kinds of problems.
A: Introduction: Algorithms: In the ninth century, Persian mathematician Muhammad ibn Musa al-Khwarizm...
Q: Which network architecture model merges the core with the distribution layer? a. Distributed Ne...
A: Network architecture is design of the computer networks.
Q: How do I import a image file, for example a flower.png with the image of a sunflower, to a java prog...
A: How do I import a image file, for example a flower.png with the image of a sunflower, to a java prog...
Q: What does the facebook reveal about the culture and time period in which it was invented and used? H...
A: Given: What does the invention and usage of Facebook tell about the society and historical period in...
Q: In the context of DHCP what is the purpose of an IP helper address? a. The gateway for the comp...
A: In the context of DHCP what is the purpose of an IP helper address is below explained.
Q: Write a php script to display 1! 2! 3! 4! 5! 6! 7! On one line There is no! At starting and ending p...
A: Algorithm: Start Iterate through the loop from x=1 to x=7 If x<7, print "$x!" Else print "$x" St...
Q: Write a program that inputs a sequence of non negative numbers terminated by a negative value and sh...
A: Since no programming language is mentioned, I am using python. Algorithm: Start Read a sequence of ...
Q: ***** *本本本本本*本本 事**本事*本事*本本容* ********* *****
A: give more information for question 2
Q: Write the statements to sum the odd integers between 1 and 99 by using a for statement. Assume that ...
A: The solution to the given problem is below.
Q: 1. Design a User Interface (UI) in visual basic programming to calculate a service charge of 2.5% o...
A: Using JavaScript, user experience: The element of your program that's also observable to a specific ...
Q: the for..next, do..loop and wh
A: We need to read in user input and compute the Vowel count and display the result.
Q: because, even though we may not be able to understand them, they can help us figure out how to solve...
A: The answer is given below.
Q: Starting with an Empty descendent-Sorted Singly-Linked List draw its status after each operation. a...
A: 1. Starting with empty list 2. add(20) 20 3. sortedInsert(10) 20 10
Q: Activities 1. Transform a 1-D array into 2-D array with 3. Start with: Al = np.array ([1, 2, 3, 4, 5...
A: In Python, we have reshape(n,m) method which convert a 1-D array into a 2-D array of required dimen...
Q: Given an array nums of size n, return the majority element. The majority element is the element that...
A: PROGRAM INTRODUCTION: Start the definition of the function to find the majority element from the ar...
Q: In the code editor, you are provided with an initial code in the main() that asks the user for the e...
A: #include <stdio.h> void flex2D(int[][5]);int main() { int matrix[5][5]; printf("Ente...
Q: Some diseases cannot be spread unless there is a direct contact with the infected person. Using inf...
A: Code: #include <iostream> using namespace std;void contact(int p,int q,int a[]);int main(){ ...
Q: Using C (not C++ or C#) I need help in solving the following problem. So I have the persisting code ...
A: Your C code is given below as you required with an output.
Q: Which wildcard mask could be used to describe network 192.168.32.0/27
A: A wildcard mask is a mask of pieces that shows what portions of an IP address are accessible for ass...
Q: Finding subtotals is a three-step process that begins with spell-checking. True False
A: Finding subtotals is a three-step process that begins with spell-checking. True False
Q: What is the meaning of deep web and dark web? In your opinion which is more advantageous the dark we...
A: What is the meaning of deep web and dark web? In your opinion which is more advantageous the dark ...
Q: Suggest the most appropriate generic software process model that might be used as a basis for managi...
A: Software Processes is an integrated set of tasks for defining, designing, implementing and evaluatin...
Q: Write an anonymous block to read two numbers from the keyboard, then find out what's the maximum bet...
A: Code: declare a number; b number;begin a:= &a; b:= &b; if a>b then dbms...
Q: decision tree with n² leaves always has height 0(log( an algorithm can finish before it reaches a le...
A: Lets see the solution.
Q: The data structures help mostly to: b)Debug programs c)Create inheritance hierarchies a)Organize ...
A: The data structures help mostly to:
Step by step
Solved in 2 steps

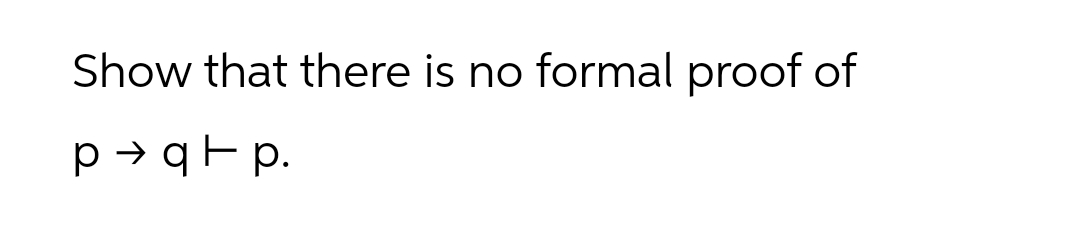
- Give a constructive proof to show that a DFA Mk = (Qk, Σk, δk, q0, Fk) exists that recognizes each Lk = {w: w ends in k 1’s} (for all k > 0) over Σ = {0, 1.Let R=ABCDEGHK and F= {ABK→C, A→DG, B→K, K→ADH, H→GE} . Is it in BCNF? Prove your answer.Prove that (p →(q →r)) → ((p →q) →(p →r)) ≡ T for all propositions p, q, r.
- Let L = { <M> | M is a TM that accepts sR whenever it accepts s } . Show that L is undecidable.Prove that if X is an answer set of a traditional program P so that for some rule A0 ← A1,...,Am, not Am+1,...,not An in P, it holds that {A1,...,Am} is in X and the intersection of {Am+1,..., An} and X is empty, then A0 is in X.For f (a, b) = (a | b) | b(a) Simplify f (a, b).(b) Find DNF for f (a, b).(c) Is f (a, b) satisfiable?
- Show that ∼ p ∧ (p ∧ q) is a contradiction.Match the following sentence to the best suitable answer: - A. B. C. D. for the linear congruence ax=1(mod m), x is the inverse of a, if__________ - A. B. C. D. What is -4 mod 9 ? - A. B. C. D. The solution exists for a congruence ax=b(mod m) such that GCD(a,m)=1 and - A. B. C. D. (107+22)mod 10 is equivalent to :_________ A. 5 B. c divides b C. GCD(a,m)=1 D. 9 mod 10Show that P is closed under union

