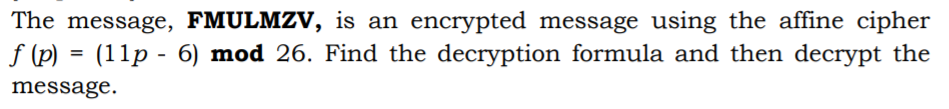
The message, FMULMZV, is an encrypted message using the affine cipher f (p) = (11p - 6) mod 26. Find the decryption formula and then decrypt the message.
Q: Decrypt the message XUPPWFIDD which was encrypted using the athine cipher f(p) = (15p + 6) mod 26…
A:
Q: Decrypt the message ORWWPGDII which was encrypted using the affine cipher: f(p) = (11p + 5) mod 26…
A:
Q: The following parameters are chosen to generate the public and private keys for the RSA…
A:
Q: Without using Calculator or other mechanical tools, find the Decryption function of the following…
A: Given encryption function is : fp=7p+3 mod26
Q: Suppose that the ciphertext ERC WYJJMGMIRXPC EHZERGIH XIGLRSPSKC MW MRHMWXMRKYMWLEFPI JVSQ QEKMG was…
A:
Q: [11 3. Consider the Hill 2-cipher with the encryption matrix decrypt the message you just received…
A: Consider the Hill 2-Cipher with the encryption matrix 11152. The aim is to solve decrypt the message…
Q: Consider the affine cipher with encryption function c(x) = 3x – 1 mod 26. a) What is the decryption…
A: Properties of modular function : Here a,b∈ℤ and n∈ℕ . ax≡b mod n is equivalent to b≡ax mod n.…
Q: The affine cipher E is given by E(x) ≡ 15x − 7 (mod 26). The conversion table for letters and…
A: E(x) = 15x - 7 (mod 26) Therefore, the decryption is given by D(y) = 7•(y+7) (mod 26)
Q: 1. A long-winded, encrypted transmission has been intercepted. Frequency analysis of the entire…
A: As per our guidelines we are supposed answer only one question and rest can be reposted
Q: Construct an affine cipher that uses only uppercase letters of English alphabet encoded as elements…
A:
Q: Show that the cipher text of HOUND using an affine cipher with key K=(7,3) is AXNQY. Encrypt the…
A: 16) Given the cipher text of HOUND and key k=7,3 Assigning the numbers, we haveHOUND71420123
Q: Describe the family of shift ciphers as a cryptosytem.
A:
Q: In a public key cryptosystem using the RSA algorithm, a user uses two prime numbers 11 and 17. He…
A: Given In a public key cryptosystem using the RSA algorithm a user uses two prime number 11 and 17.…
Q: Hill Cipher for m=2, then correct key is
A: This is a problem of Cryptography, Number Theory, and Modular Arithmetic. Therefore it is a problem…
Q: Encipher these messages using a Rosicrucian cipher: 1. SWIM 2. BASEBALL 3. НОСКEY 4. FOOTBALL 5.…
A: Rosicrucian Chipher : For ciphering the alphabets consider the boxes and the dots corresponding to…
Q: (b) Cindy wants to send the message m = 53 to Dan. Use the public key for this cryptosystem to…
A: Algo: 1) Find Alice public key (n, e) Where n=p.q 2) Find remainder C when Me is divided by n. 3)…
Q: 5. (a) Encipher the message HAVE A NICE TRIP using a Vigenère cipher with the keyword МАТНH. (b) The…
A:
Q: encryted using a shift cipher with C(x) = (P(x) – 12)( mod 26). Decrypt the The Ciphertext below was…
A: The given encrypt function is Cx=Px-12 mod 26. Decrypt the chiphertext XIZWIGQOSGOF. From the…
Q: which memory location is assigned by hashing function h(k)=k mod 101 social security number…
A: Which memory locations are assigned by the hashing function h(k) = k mod 101 to the records of…
Q: Express the Vigen`ere cipher as a cryptosystem.
A:
Q: Assume they are used for an encryption in Hill ciphers. In each case, find two plaintexts that…
A: The matrices given are as follows: 1322 and 131242351 For 1322 Let x1y1 and x2y2 be two plain…
Q: What is the secret message produced from the message “MEET YOU IN THE PARK” using the Caesar cipher?
A:
Q: Decrypt the message ''EOXH MHDQV Using the shift cipher f(p)=(p+3)mod26
A: Solution by using shift cipher as follows :
Q: 2. Encrypt the following message using RSA cryptosystem. Message : THIS , with n=2633 and e=29. R
A:
Q: The affine cipher E is given by E(x) ≡ 15x − 7 (mod 26). The conversion table for letters and…
A:
Q: Encrypt the message AT FOUR SURVEILLANCE ON TARGET using a tabular transposition cipher with…
A:
Q: Suppose (n, d) = (55, 3) is the private key of an RSA cryptosystem. If the received ciphertext is C…
A:
Q: Suppose that the most common letter and the second most common letter in a long ciphertext produced…
A:
Q: The message NOT NOW (numerically 131419131422) is to be sent to a user of the EIGamal system who has…
A:
Q: Once the length of the key string of a Vig`enere cipher is known, explain how to determine each of…
A: The length of the key's known. Let its k. therefore the text is going to be divided into groups of k…
Q: Alice wants to send to all her friends, including Bob, a message using the RSA cryptosystem. She…
A: a Number of ways Alice can choose an encryption key n,e is the number of ways Alice can choose e as…
Q: Suppose we decide to use Data Encryption Standard (DES) for data encryption. Given the initial…
A:
Q: 3. (a) Suppose that you have an alphabet of 26 letters how many possible simple substitution ciphers…
A:
Q: (7) Which of the following formulas represent the process of encryption in Caesar Cipher? (Choose…
A: Option B M=(C-3)mod26
Q: Bob wants to send Alice the message, "JAW," which he plans to encrypt using Alice's RSA cypher with…
A:
Q: Suppose an RSA cryptosystem is used to send the plaintext "4" with public key (n, e) = (33, 3). What…
A: RSA algorithm is an encryption method that uses two types of keys namely private and public and,…
Q: Ξ. Σ Suppose = {0, 1, 2, 3, ..., 34} is the alphabet for the affine cipher. Find the size of the…
A: Given, ∑=0, 1, 2, 3, . . . ,34 is the alphabet for the affine cipher.
Q: 2. If the Caesar cipher produced RDSSB ELUWKGDB, WIlal Is uic plumno 3. (a) A linear cipher is…
A:
Q: Recall that an affine cipher, fa,b(n) = an + b( mod 26), where a, b ∈ {0, 1, 2, . . . , 25}, is said…
A: For the encryption, use the following conversion table for the English alphabet: 0 1 2 3 4 5 6 7…
Q: Having chosen primes p and q, and suitable integers d and e, what is the public-key of our RSA…
A: There are primes p and q and integers d and e, the public-key of RSA cipher is: n,e=pq, e
Q: Use the RSA cipher with public key n = 713 = 23 · 31 and e = 43. Decrypt the given ciphertext…
A: To decrypt the ciphertext 476 089 048 129 and find the original message. When given n = 713 = 23 ·…
Q: Apply the affine cipher formula C=(5P + 2) mod 26 to encript "LASER PRINTER". JGNSA DUNTXNA JSNAS…
A:
Q: 1. The following sentence was encoded using the Cesar Cipher, your job is to decode it: KRZ DUH BRX.
A: 1. The following table is used to decrypt the message.
Q: Decrypt the message EABW EFRO ATMR ASIN, which is the ciphertext produced by encrypting a plaintext…
A:
Q: Find all pairs of integers keys (a, b) for affine ciphers for which the encryption function c = (ap…
A:
Q: Use the RSA cipher with public key (n, e) = (713, 43) to encrypt the word "TEE." Start by encoding…
A:
Q: Construct an affine cipher that uses only uppercase letters of English alphabet encoded as elements…
A:
Q: Suppose that you know that a ciphertext was produced by encrypting a plaintext message with a…
A:
Q: which memory location is assigned by hashing function h(k)=k mod 101 social security number…
A: Given, Social security number =501338753 The formula for finding the memory location is, hk=kmod k
Q: Suppose that when a string of English text is encrypted using a shift cipher f (p) = (p + k) mod 26,…
A:
Please help me solve this question
Step by step
Solved in 2 steps with 2 images

- Suppose that in a long ciphertext message the letter occurred most frequently, followed in frequency by. Using the fact that in the -letter alphabet, described in Example, "blank" occurs most frequently, followed in frequency by, read the portion of the message enciphered using an affine mapping on. Write out the affine mapping and its inverse. Example 2 Translation Cipher Associate the letters of the "alphabet" with the integers. Let and define the mapping by where is the key, the number of positions from the plaintext to the ciphertext. If our alphabet consists of through, in natural order, followed by a blank, then we have "letters" that we associate with the integers as follows:Suppose that in an RSA Public Key Cryptosystem, the public key is. Encrypt the message "pay me later” using two-digit blocks and the -letter alphabet from Example 2. What is the secret key? Example 2 Translation Cipher Associate the letters of the "alphabet" with the integers. Let and define the mapping by where is the key, the number of positions from the plaintext to the ciphertext. If our alphabet consists of through, in natural order, followed by a blank, then we have "letters" that we associate with the integers as follows:Suppose that in an RSA Public Key Cryptosystem, the public key is e=13,m=77. Encrypt the message "go for it" using two-digit blocks and the 27-letter alphabet A from Example 2. What is the secret key d? Example 2 Translation Cipher Associate the n letters of the "alphabet" with the integers 0,1,2,3.....n1. Let A={ 0,1,2,3.....n-1 } and define the mapping f:AA by f(x)=x+kmodn where k is the key, the number of positions from the plaintext to the ciphertext. If our alphabet consists of a through z, in natural order, followed by a blank, then we have 27 "letters" that we associate with the integers 0,1,2,...,26 as follows: Alphabet:abcdef...vwxyzblankA:012345212223242526
- Suppose the alphabet consists of a through z, in natural order, followed by a blank and then the digits 0 through 9, in natural order. Associate these "letters" with the numbers 0,1,2,...,36, respectively, thus forming a 37-letter alphabet, D. Use the affine cipher to decipher the message X01916R916546M9CN1L6B1LL6X0RZ6UII if you know that the plaintext message begins with "t" followed by "h". Write out the affine mapping f and its inverse.Suppose that in an RSA Public Key Cryptosystem. Encrypt the message "algebra" using the -letter alphabet from Example 4. Use two-digit blocks. Use three-digit blocks. What is the secret key?Use the alphabet C from the preceding problem and the affine cipher with key a=11andb=7 to decipher the message RRROAWFPHPWSUHIFOAQXZC:Q.ZIFLW/O:NXM and state the inverse mapping that deciphers this ciphertext. Exercise 7: Suppose the alphabet consists of a through z, in natural order, followed by a colon, a period, and then a forward slash. Associate these "letters" with the numbers 0,1,2,...,28, respectively, thus forming a 29-letter alphabet, C. Use the affine cipher with key a=3andb=22 to decipher the message OVVJNTTBBBQ/FDLWLFQ/GATYST and state the inverse mapping that deciphers this ciphertext.
- Suppose that in an RSA Public Key Cryptosystem. Encrypt the message "pascal" using the -letter alphabet from Example 4. Use two-digit blocks. Use three-digit blocks. What is the secret key?What is the decryption function for an affine cipher if the encryption function is c = (15p + 13) mod 26?Suppose that the most common letter and the second most common letter in a long ciphertext produced by encrypting a plaintext using an affine cipher f (p) = (ap + b) mod 26 are Z and J, respectively. What are the most likely values of a and b?
- Find all pairs of integers keys (a, b) for affine ciphers for which the encryption function c = (ap + b) mod 26 is the same as the corresponding decryption function.Suppose that you know that a ciphertext was produced by encrypting a plaintext message with a transposition cipher. How might you go about breaking it?What is the secret message produced from the message “MEET YOU IN THE PARK” using the Caesar cipher?

