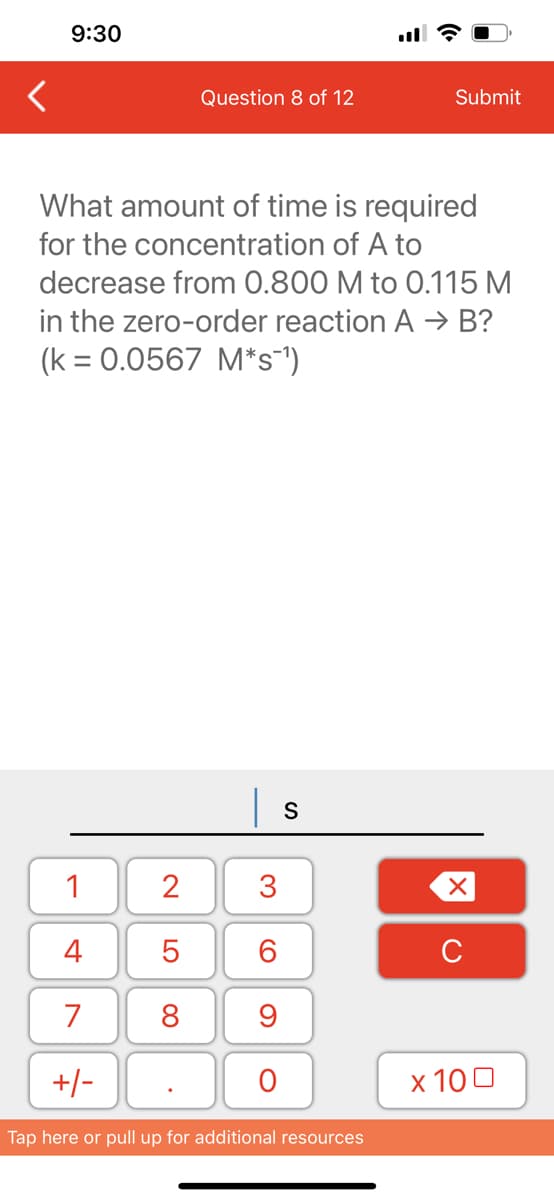
What amount of time is required for the concentration of A to decrease from 0.800 M to 0.115 M in the zero-order reaction A → B? (k = 0.0567 M*s¯¹)
Q: Design and implement class Patron It should
A: I have provided C++ CODE along with CODE SCREENSHOT and OUTPUT SCREENSHOT------------------
Q: Commonly used diagnostic and management tools for networks are available. If a workstation is having…
A: OSI: OSI stands for Open Systems Interconnection. It is a seven-layer model for communication…
Q: What should happen if the processor sends a request that hits the cache while publishing a block…
A: A computer is a digital electronic machine that can be programmed to automatically perform a series…
Q: Find out how technology and data are used to solve the problems experienced by data systems.
A: Introduction : A data system is a collection of data, hardware, and software components that are…
Q: What precisely does it require to change the regulations governing software configuration…
A: To change the regulations governing software configuration management, the following steps may be…
Q: Give an example of how a firewall has helped to protect your company. When compared to one another,…
A: Network security:- Network security is the process of protecting a network and its resources from…
Q: What can you do to make sure your model gets all the data it needs? What benefits can problem…
A: In model creation we need correct data to give accurate results.
Q: Consider a multi-granularity locking system, with lock modes S, X, IS, IX, and SIX as in lecture and…
A: For the scenario described, T3 would need to obtain an IX (Intention Exclusive) lock on file-level…
Q: Make an algorithm for using an ATM to withdraw money.
A: Money-withdrawal algorithm at an ATM: Let's now examine how to use an ATM to withdraw cash. Put ATM…
Q: WRITE CODE 1) To begin your assignment, find the src/homework/01_data_types folder. In this folder:…
A: Algorithm of the code: 1. Create a function called multiply_numbers that takes an int parameter…
Q: In what ways is the dissemination of version control software distinct from the application of…
A: The version control system is a device cluster responsible for controlling revisions to, among other…
Q: lid understanding of both the end objective and the processes involved in a release process. What…
A: Version control The ability to handle and trace each version of a file from a centralized location…
Q: It is essential to have a solid understanding of what a release process is and how it operates. What…
A: Version control is a system that helps track changes made to a set of files over time. It enables…
Q: Do you believe that improved communication across departments will lead to increased performance in…
A: Reverse logistics can help you identify ways to reuse, resell or recycle materials that would…
Q: What's the difference between software that's centralized and that which is distributed to manage…
A: The main distinction between centralized and distributed version control is how the source code is…
Q: The microkernel of the operating system is accessible for any design criteria that may be required.…
A: Microkernel Approach: The microkernel approach is a design strategy that separates the essential…
Q: following my code without using std::, This is what it produced. 1: Compare outputkeyboard_arrow_up…
A: The correct code is given below without using std::
Q: When it comes to the management of software, what is the primary difference between distributed and…
A: The version control system is a device cluster responsible for managing changes to various…
Q: Basis for Comparison Memory / Cache Number of cores Clocking frequency (GHz) Size (length & width in…
A: CPU: CPU stands for Central Processing Unit. It handles all main function of a computer. GPU: GPU…
Q: The storage methods used by distributed and centralized version control systems are distinct from…
A: When dealing with several developers on the same project, many of us are acquainted with version…
Q: When we say "operating system," what exactly do we mean? Determine the OS's two primary roles.
A: Introduction: A software component known as an RTOS, or real-time operating system, gives the…
Q: What exactly is meant by the term "release method" when it comes to the creation of software? Why is…
A: "Release method" refers to the process of making a new version of software available to the public…
Q: What kind of repercussions does a data breach have for the security of the cloud? In order to combat…
A: Data loss in the Cloud A data breach is the purposeful or accidental disclosure of secure or…
Q: I need this program writted in Python and exactly like the examples attached, please! Thank you!…
A: The code uses a for loop to iterate through the numbers from 100 to 200 (inclusive). For each…
Q: The issue:Some functions produce results that should never be disregarded. For instance, there is no…
A: No, there is no method to make people use a function's return value against their will. It is the…
Q: LTE . The classes Name and Date are separate classes used as properties in the Employee class. 9:59…
A: The classes Name and Date are separate classes used as properties in the Employee class. Class…
Q: What kind of equipment are you attempting to connect to? Do you have access to tools and programs…
A: Which device do you want to connect to? What tools and apps for cloud-based synchronization are…
Q: As below drawing, how to explain in details the attributes and operations of the two class diagrams…
A: Below is the complete solution with explanation in detail for the given question about various…
Q: Write a MATLAB code for computing the following functions in one program: x ≥ 2 and y = 0.5 x210 and…
A: The following are steps that need to be taken for the given program: We ask the user to input the…
Q: Use a comparison chart to compare the capabilities, advantages, cost, and usability of commercial…
A: Sense Nonsense Untangle A BSD-based firewall called Sense is compatible with both Windows and…
Q: In this lesson, we will go through the top ten current threats to computer systems, networks, and…
A: Introduction: IT's biggest problem nowadays is cyber and database security. If not encrypted and…
Q: Names of two different virtual private network (VPN) protocols should be provided. It is important…
A: In this question we need to name two Virtual Private Network (VPN) protocols. We also need to…
Q: How do you carry out an assessment to see whether an implementation impacts the effectiveness of…
A: The answer is given in the below step
Q: Imagine that you had to make an operating system from scratch. Indicate for each service if user…
A: The list of common operating system services and whether user-space programs can provide that…
Q: It is essential to have a solid understanding of both the end objective and the processes involved…
A: Introduction: What is a release process for, and how does it operate? Why is version control…
Q: Please elaborate on the risks to computer security that a system failure poses.
A: When a computer's system fails, it can leave it open to a number of security risks. System failures…
Q: ime might vary greatly. In-depth research and the creation of preventative techniques are needed to…
A: Cybercrime:Cybercrime is any criminal activity involving a computer, a networked device, or a…
Q: Differentiate between an OS with system calls and one without system calls. There are several…
A: Operating System: The OS doesn't make system calls. The operating system runs its code, drivers,…
Q: What function does cloud computing serve within the larger context of an organization's structure…
A: Introduction: Due to characteristics like virtualization, scaling up or down to handle higher…
Q: The DHCP lease has to be explained. What is the procedure for getting it? What role does it play?…
A: Getting DSCP (Dynamic Host Configuration Protocol) Lease Period for Configuration Protocol): The…
Q: What exactly does it mean for a piece of software to be "configured"? Is it possible to have a…
A: Software configuration management, often known as SCM or S/W CM, is a position in programme…
Q: Write your own function that illustrates a feature that you learned in this unit. The function must…
A: Here's a function I created that calculates the total number of seconds a person has lived based on…
Q: Analyze how well and how often your social skills were put to play throughout the preparation and…
A: INTRODUCTION: Communication skills, speaking, listening, walking, looking, personality, mood, and…
Q: Do system analysts ever face moral conundrums in their work?
A: Yes, system analysts may face moral conundrums in their work, especially when they are involved in…
Q: 4. CREATE A C++ PROGRAM THAT THE USER WILL INPUT 3 COORDINATES AND THE OUTPUT IS TO DETERMINE THE…
A: To check the collinearity of points is to find area of the area of triangle formed by 3 points is 0…
Q: When a security breach occurs, what measures should be done by an organization?
A: Intro Security Breach: This occurs when an organization's basic security measures are disregarded,…
Q: It would be helpful to include an explanation of the DHCP lease. How exactly does one go about…
A: A device on a network may receive a temporary IP address assignment through DHCP (Dynamic Host…
Q: Make Algorithm to illustrates the quick sort procedure. The algorithm employs the Divide and Conquer…
A: Solution given below in next step.
Q: 1.Code so on for_A pure full Implement c/c++ to evaluate round robin algorithm. You must use the job…
A: Introduction Round Robin is an algorithm used for scheduling processes in a computer system. It…
Q: Do you know the most common ways that host software firewalls are used? Explain
A: Introduction: Host-based firewalls are software that acts on an individual computer or device…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- <Qs 45 > Consider the following pseudo-code: I = 0; J = 0; K = 8; while (I < K – 1) //while-1 { J = J + 1; while (J < K) //while-2 { if (x[I] < x[J]) { temp = x[I]; x[I] = x[J]; x[J] = temp; } } // end of while-2 I = I +1; } // end of while-1 The cyclomatic complexity of the above is ?11.Code so on for_A pure full Implement c/c++ to evaluate round robin algorithm. You must use the job list given here: Job (1) arrive at CPU cycle1 Job (2) arrive at CPU cycle2 Job (3) arrive at CPU cycle36 I/O (32) CPU (54) I/O (45) CPU (20) I/O (40) CPU (48) CPU (39) CPU (48) I/O (55) Your job list must contain CPU bust and I/O bust as above. Quantum time = [5, 10, 15, 20, 25, 30, 35, 40, 45, 50, 55, 60] The evaluation of the most suitable quantum time needs to consider the followingperformance metrics, but not limited to:(i) Turnaround time of the jobs;(ii) Waiting time of the jobs; and(iii) Number of interrupts incurred The code must able to read csv file format of the job list as input file. The code must able for user to input time quantum.. ..Consider the following code for a process P0 (assume turn has been initialized to zero): --- Etc. --- while (turn != 0) {} Critical Section /* … */ turn = 0; --- Etc. --- For process P1, the code is: --- Etc. --- while (turn != 1) {} Critical Section /* … */ turn = 1; --- Etc. --- Does the above code meet all the required conditions for a correct mutual-exclusion solution? Explain and justify your answer.
- I am working on a problem for my homework. I have to convert this C++ Code: int multiply(int x, int y){ int product=0;if(x>y) for(int i=0;i<y;i++) product+=x;if(y>x) for(int i=0;i<x;i++) product+=y;return product;} I have received the MIPS Code of: multiply(int, int): daddiu $sp,$sp,-48 sd $fp,40($sp) move $fp,$sp move $3,$4 move $2,$5 sll $3,$3,0 sw $3,16($fp) sll $2,$2,0 sw $2,20($fp) sw $0,0($fp) lw $3,16($fp) lw $2,20($fp) slt $2,$2,$3 beq $2,$0,.L2 nop sw $0,4($fp) b .L3 nop .L4: lw $3,0($fp) lw $2,16($fp) addu $2,$3,$2 sw $2,0($fp) lw $2,4($fp) addiu $2,$2,1 sw $2,4($fp).L3: lw $3,4($fp) lw $2,20($fp) slt $2,$3,$2 bne $2,$0,.L4…Using the banker’s algorithm, determine whether this is in a safe state, where the available resources are (for A, B, and C) 1, 2, and 1.Show that ∃x (P (x) ∧ Q(x)) is not logically equivalent to (∃x P (x)) ∧ (∃x Q(x)).
- A pure full Implement c/c++ to evaluate round robin algorithm. You must use the job list given here: Job (1) arrive at CPU cycle1 Job (2) arrive at CPU cycle2 Job (3) arrive at CPU cycle36 I/O (32) CPU (54) I/O (45) CPU (20) I/O (40) CPU (48) CPU (39) CPU (48) I/O (55) Your job list must contain CPU bust and I/O bust as above. Quantum time = [5, 10, 15, 20, 25, 30, 35, 40, 45, 50, 55, 60] The evaluation of the most suitable quantum time needs to consider the followingperformance metrics, but not limited to:(i) Turnaround time of the jobs;(ii) Waiting time of the jobs; and(iii) Number of interrupts incurred The code must able to read csv file format of the job list as input file. The code must able for user to input time quantum..I don't need a code for these questions. I just need them answered Nine steel specimens were submerged in seawater at various temperatures, and the corrosion rates were measured. The results are presented in the following table:Temperature (OC)Corrosion(mm/yr.)26.6 1.5826 1.4527.4 1.1321.7 0.9614.9 0.9911.3 1.0515 0.828.7 0.688.2 0.59a. Construct a scatterplot of corrosion (y) vs. temperature (x). Verify that a linear model is appropriate.b. What is the least-square line (trendline/regression line) for predicting corrosion from temperature?c. Two steel specimens whose temperatures differ by 10OC are submerged in seawater. By how much would you predict their corrosion rates differ?d. Predict the corrosion rate for steel submerged in seawater at a temperature of 20OC.e. Construct a table with predicted values from the original dataset.f. Compute the residuals. Which point has the residual with the largest magnitude?g. What is the correlation between temperature and corrosion rate? What…> Now calculate the relativeperformance of adders. Assume that hardwarecorresponding to any equation containing only OR orAND terms, such as the equations for pi and gi on pageB-40, takes one time unit T. Equations that consist ofthe OR of several AND terms, such as the equations forc1, c2, c3, and c4 on page B-40, would thus take twotime units, 2T. The reason is it would take T to producethe AND terms and then an additional T to produce theresult of the OR. Calculate the numbers andperformance ratio for 4-bit adders for both ripple carryand carry lookahead. If the terms in equations arefurther defined by other equations, then add theappropriate delays for those intermediate equations,and continue recursively until the actual input bits ofthe adder are used in an equation. Include a drawingof each adder labeled with the calculated delays andthe path of the worst-case delay highlighted.
- Code so on for_A pure full Implement c/c++ to evaluate round robin algorithm. You must use the job list given here: Job (1) arrive at CPU cycle1 Job (2) arrive at CPU cycle2 Job (3) arrive at CPU cycle36 I/O (32) CPU (54) I/O (45) CPU (20) I/O (40) CPU (48) CPU (39) CPU (48) I/O (55) Your job list must contain CPU bust and I/O bust as above. Quantum time = [5, 10, 15, 20, 25, 30, 35, 40, 45, 50, 55, 60] The evaluation of the most suitable quantum time needs to consider the followingperformance metrics, but not limited to:(i) Turnaround time of the jobs;(ii) Waiting time of the jobs; and(iii) Number of interrupts incurred The code must able to read csv file format of the job list as input file. The code must able for user to input time quantum.. .Recall Pigou’s example discussed in class, where there are two roads that connect a source, s, and destination, t. The roads have different travel costs. Fraction x1 of the traffic flow on route 1, and the remainder x2 on route 2. Here consider the following scenario. • The first road has “infinite” capacity but is slow and requires 1 hour travel time, T1 = 1. • The second road always requires at least 15 mins, which then increases as a function of traffic density, T2 = 0.25 + 0.75x2. If drivers act in a “selfish” manner – the user optimal scenario – all the traffic will flow on the second path, as one is never worse off. Worst case scenario for path 2, both paths take one hour. So no one is incentivized to change their behavior. 1. Assume user optimal behavior, and calculate τ the expected travel time per car. 2. If instead we could control the flows, we could minimize the expected travel time. Using the expression in part (a), calculate the optimal allocation of flows x¯1 and ¯x2…Implement this algorithm in C program . Show the gantt chart as output. Round-robin (RR) is one of the algorithms employed by process and network schedulers in computing. As the term is generally used, time slices (also known as time quanta) are assigned to each process in equal portions and in circular order, handling all processes without priority (also known as cyclic executive).

