
About leap year
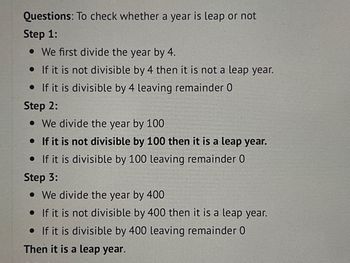
A typical year on the Gregorian calendar has 365 days. A "leap year" of 366 days is used once every four years to correct for the fact that a sidereal year, the amount of time needed for the Earth to complete one rotation around the Sun, is really 365.2425 days, as opposed to three short but typical years. A leap year is any year that divides evenly by 4; examples include 1988, 1992, and 1996.
There is, however, a slight inaccuracy that has to be taken into consideration. The Gregorian calendar mandates that a year that is equally divisible by 100 (for instance, 1900) be a leap year only if it is also evenly divisible by 400. This eliminates the mistake.
Due to this, the following years do not count as leap years:
1700, 1800, 1900, 2100, 2200, 2300
They are equally divisible by 100 but not by 400, which explains why.
leap years occur in the years 1600, 2000, and 24,000.
This is due to the fact that they may be divided equally by 100 and 400.
Step by stepSolved in 4 steps with 2 images

 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education





