
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Concept explainers
Question
Don't give me AI generated answer or plagiarised answer. If I see these things I'll give you multiple downvotes and will report immediately.
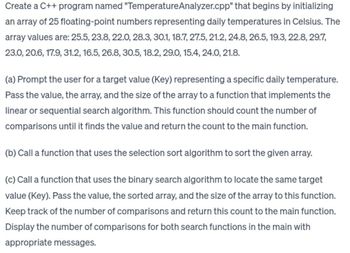
Transcribed Image Text:Create a C++ program named "TemperatureAnalyzer.cpp" that begins by initializing
an array of 25 floating-point numbers representing daily temperatures in Celsius. The
array values are: 25.5, 23.8, 22.0, 28.3, 30.1, 18.7, 27.5, 21.2, 24.8, 26.5, 19.3, 22.8, 29.7,
23.0, 20.6, 17.9, 31.2, 16.5, 26.8, 30.5, 18.2, 29.0, 15.4, 24.0, 21.8.
(a) Prompt the user for a target value (Key) representing a specific daily temperature.
Pass the value, the array, and the size of the array to a function that implements the
linear or sequential search algorithm. This function should count the number of
comparisons until it finds the value and return the count to the main function.
(b) Call a function that uses the selection sort algorithm to sort the given array.
(c) Call a function that uses the binary search algorithm to locate the same target
value (Key). Pass the value, the sorted array, and the size of the array to this function.
Keep track of the number of comparisons and return this count to the main function.
Display the number of comparisons for both search functions in the main with
appropriate messages.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 3 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- There were two types of erroneous results reported: false positive and false negative. Biometric authentication may be split up into subcategories. What makes biometrics safer than passwords, exactly? - Why? Is there a way for fraud to be committed via biometric authentication? Give me an explanation in your own words.arrow_forwardThe following are some examples of potential data confidentiality breaches: Afterwards, we'll talk about the many precautions that may be done.arrow_forwardIdentity theft, in which people steal other people's personal information, is still a big source of worry for both individuals and businesses. Let's pretend you're a database administrator for a large company with extensive online databases. What do you do? Are there any measures you'd take to prevent unauthorised access to a company's database?arrow_forward
- I'd be very grateful if you could elaborate on the goals of the authentication process. Think about the benefits and drawbacks of the various authentication methods now in use.arrow_forwardIn order to provide an additional degree of protection to the process of making electronic payments, certain credit card companies now supply their customers with credit card numbers that can only be used once. Customers need to go to the website of the entity that issued their credit card in order to get the one-time-use number. Compared to the conventional means of using credit card numbers, what are the benefits of applying this technology instead? What are the benefits and drawbacks of using this method as opposed to authenticating yourself using an electronic payment gateway?arrow_forwardIf you're going to talk about data manipulation, forgeries, and online jacking, you may as well provide some examples.arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education