
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Concept explainers
Question
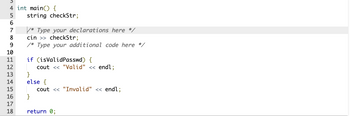
Declare a Boolean variable named isValidPasswd. Use isValidPasswd to output "Valid" if checkStr contains at least 4 letters and checkStr's length is greater than 7, and "Invalid" otherwise.
Ex: If the input is 58m6SF7w, then the output is:
Valid
Ex: If the input is NKXwLD2, then the output is:
Invalid
Note: isalpha() returns true if a character is alphabetic, and false otherwise. Ex: isalpha('a') returns true. isalpha('8') returns false.
Transcribed Image Text:3
4 int main() {
5 string checkStr;
6
7
8
9
10
11
12
13
14
15
16
17
18
/* Type your declarations here */
cin >> checkStr;
* Type your additional code here */
if (isValid Passwd) {
cout << "Valid" << endl;
}
else {
}
cout << "Invalid" << endl;
return 0;
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution
Trending nowThis is a popular solution!
Step by stepSolved in 2 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Declare a Boolean variable named goodPasswd. Use goodPasswd to output "Valid" if passwdStr contains at least 4 letters and passwdStr's length is greater than 7, and "Invalid" otherwise. Ex: If the input is xd43J1g8, then the output is: Valid Ex: If the input is Mvd2N51, then the output is: Invalid Note: Isalpha() returns true if a character is alphabetic, and false otherwise. Ex isalpha(a) returns true. Isalpha(B) returns false. 1 #include 2 using namespace std; 10 11 12 12 13 14 int main() { 16 17 18 10 3 string passudstr; * Type your declarations here "/ cin>> passudstr; /Type your additional code here / if (goodPassad) ( cout << "Valid" << endl; else { cout << "Invalid" << endl; } return 0; 2arrow_forward*Using IF Statements* 1. Conduct a quiz that contains 4 questions. Each question has 4 possible answers. Ask a user to choose the correct answer for each question. If the user choose the correct answer, add 1 point. Display the total points user earned at the end of the quiz. 2. Ask a user to enter 4 integers and display the largest integer the user entered.arrow_forwardThe Urinary operator ‘++’ is the special case when a variable is increased: True or Falsearrow_forward
- -Prompts the user to enter an integer x. Assume without error checking the user enters a positive integer. -The program then will print all the odd integers between 1 and x that are a multiple of 3. Sample: Enter an integer x: 15 3 is a multiple of 3 9 is a multiple of 3 15 is a multiple of 3arrow_forwardX609: Magic Date A magic date is one when written in the following format, the month times the date equals the year e.g. 6/10/60. Write code that figures out if a user entered date is a magic date. The dates must be between 1 - 31, inclusive and the months between 1 - 12, inclusive. Let the user know whether they entered a magic date. If the input parameters are not valid, return false. Examples: magicDate(6, 10, 60) -> true magicDate(50, 12, 600) –> falsearrow_forwardCan you help me to do this Java program please? Thank you!arrow_forward
- Question 18 Guessing Game Code a solution for the following problem. Post your program in the textbox below. (NOTE: Indenting matters.) • Hard-code an integer variable valid value from 1 to 10. Ask the user to guess your whole number and input that number. - Then compare the user's input to your literal number ani tell the user how they compare, is it greater than, less than or equal to each other. Extra: Send an error message if the value entered is not between 1 and 10. Edit View Insert Format Tools Table Ev Ev To E v V O Paragraph v BIU A ev T? v 12pt varrow_forwardWrite an expression that will cause the following code to print "Equal" if the value of sensorReading is "close enough" to targetValue. Otherwise, print "Not equal". Hint: Use epsilon value 0.0001. Ex: If targetValue is 0.3333 and sensorReading is (1.0/3.0), output is:Equal #include <iostream>#include <cmath>using namespace std; int main() { double targetValue; double sensorReading; cin >> targetValue; cin >> sensorReading; if (/* Your solution goes here */) { cout << "Equal" << endl; } else { cout << "Not equal" << endl; } return 0;}arrow_forward*Modify the program so that the user will error trap for only 1 and 0 as an input. *If the user enters an input other than 1 or 0 display an error message and request the user enter that input again. *Do this for all inputs in the code. # User defined function for logic OR# The function takes two parameters and returns a single intdef OR(a: int, b: int)->int:# If a is equal to 1 return 1if a == 1 :return 1# If b is equal to 1 return 1elif b == 1 :return 1# If a and b is equal to 0 return 0else :return 0 # User defined function for logic NOR# The function takes two parameters and returns a single intdef NOR(a: int, b: int)->int:# If a is equal to 0 and b is also equal to 0 return 1if a == 0 and b == 0 :return 1# If a is equal to 0 and b is equal to 1 return 0elif a == 0 and b == 1 :return 0# If a is equal to 1 and b is also equal to 0 return 0elif a == 1 and b == 0 :return 0# If a is equal to 1 and b is also equal to 1 return 0elif a == 1 and b == 1 :return 0 # User defined…arrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education