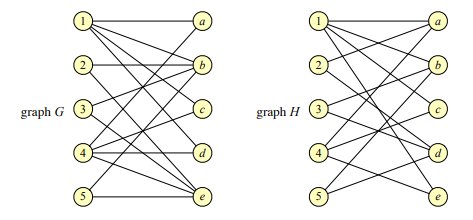
Determine whether the two bipartite graphs below have a perfect matching. Justify your answer, either by showing a perfect matching or using Hall’s theorem to prove that it does not exist
Q: What is communication technology? Elaborate your answer by using the type of communication technolog...
A: Answer : Communication technology : Communication technology is the technology which is used for the...
Q: What is the name of the table adapter method that uses a current copy of the data to populate the da...
A: Introduction: \The table adapter's Fill() function populates the dataset with a current copy of the ...
Q: With a statement, create an instance of the Transcript class.
A: Introduction: Creation of objects: A class is a collection of user-defined data structures that inc...
Q: If you mistakenly delete a file and want to recover it, you must do the actions outlined below.
A: Introduction: When you delete a file, the file itself is not deleted; instead, the reference to the ...
Q: Create an Algorithm Design A number divisible by 2 is considered an even number, while a number whic...
A: Pseudo code is an informal language code, which helps the person who is writing the code or the prog...
Q: What are the advantages of automating the testing process?
A: Introduction: Security testing, vulnerability testing, and cyber testing are all automated tests tha...
Q: What is the difference between a subsystem and a logical division, and why is it important?
A: Given: What is the distinction between a subsystem and a logical division, and why does it matter?
Q: Consider Case Study (2): World's Trend Catalog Division. If you know that the parent process (3)- PR...
A:
Q: What is it about zero-day vulnerabilities that makes them so dangerous?
A: Introduction: A zero-day exploit is a software security weakness that the programmed manufacturer is...
Q: Do the following without using a cal- culator or a computer, but check your answers with a calculato...
A: Given :- Do the following without using a calculator or a computer, but check youranswers with a cal...
Q: Q1: K3,3+ P3 is a planar graph * yes No Q2: Every face bounded by at least three edges * O yes No Q3...
A: A graph G is called a planar graph if it can be drawn in a plane without any edges crossed.
Q: hello, below i done a coding on visual studios but theres an error that keeps showing which is under...
A: Corrected code in next step -
Q: What is an Object Repository, and how does it work? In Selenium, how can we make an Object Reposito...
A: Introduction: What is an Object Repository, and how does it work? In Selenium, how can we make an O...
Q: your ow
A: As per guidelines, we can only solve one question at a time. Hence resubmit the question for further...
Q: describes a relationship in which each piece of data in one entity is represented by only one instan...
A: There are three distinct sorts of relationships between entities, They are as follows: Relationships...
Q: orld is divided up into four different zones. In each zone there are three different pods of mythica...
A: def main(): mythicalPods = ["Fairies", "Elves", "Cyclops", "Unicorns", "Kelpie", "Dragons", "C...
Q: of the following is false in reference to python ? Dictionary is an unordered collection of key-valu...
A: Solution:
Q: draw and explain generic block diagram of an IoT device. explain in what circumstances you will pref...
A: IoT devices are the nonstandard computing devices that connect wirelessly to a network and have the ...
Q: #include using namespace std%3; class fraction{ float d,s; public: fraction() { d=0; s=1%3B } fracti...
A: Please refer below for your reference: Language used is C++ Also please check your code as in the ma...
Q: Is it possible to safeguard communications using message secrecy and integrity security? Is it the ...
A: Introduction: Because smart objects frequently communicate data across insecure communication medium...
Q: One of the primary distinctions between microprocessors and microcomputers is the absence of I/O dev...
A: Introduction: A microprocessor is the central processing unit of any contemporary computer. It is ma...
Q: The ImageList control is found in which part of the Toolbox?
A:
Q: Explain how to turn the letters A, B, and C into decimal numbers.
A: Introduction: Decimal Number System The decimal number system is a base-ten system. It has ten sym...
Q: What are the most notable distinctions between computers from the fourth and fifth generations?
A: Solution:-
Q: Problem #1 - Initializing and summing an array using for loops Write a program which creates a one d...
A: As per our company guidelines we are supposed to answer only one question. Kindly repost other quest...
Q: Why is it critical to understand how a business process operates while developing a new information ...
A: Introduction: Each data frame is intended to further develop business somehow or another. Notwithsta...
Q: A message transportation in the network follows network protocol. Are messages sent as a whole from ...
A: No, messages are not sent as whole , rather messages are sent into form of chunks or segments which ...
Q: f "there is neither frame id nor frame name," which strategy should be used in the script?
A: Introduction: If "there is neither frame id nor frame name," which strategy should be used in the sc...
Q: Create a function to insert a new product into an existing order, include the product id, unit price...
A: SQL Query to add a product in the list
Q: A frame size 10 million bytes is being sent on a link with with bandwidth of 8 Mbps. The total trans...
A: Hi Dear!! Please give positive feedback!! Frame of size = 10 million bits = 10 × bytes = 10000000 ...
Q: In data warehousing, what is the "Hybrid Approach"?
A: Introduction: Data warehousing refers to the secure electronic storing of information by a business ...
Q: 3. In the C++ language, write a function that takes a vector as the parameter and reverses the vecto...
A: In the C++ language, write a function that takes a vector as the parameter and reverses the vector. ...
Q: What algorithm does HIDS use? O pattern matching misuse detection O shallow detection O protocol det...
A: Given :- What algorithm does HIDS use? pattern matching misuse detection shallow detection protocol...
Q: cuss possible safeguards against wireless credentials being intercepted by Man -Middle (MITM) attack...
A: A (MITM) man in the middle attack is a kind of eavesdropping assault in which attackers intercept co...
Q: 2.15 2.2, 2.5> Provide the type and hexadecimal representation of the following instruction: sw St3,...
A: Below is the answer to above question. I hope this will be helpful for you...
Q: Determine two methods for finishing the identical object, one of which employs a more technologicall...
A: Introduction: Plays are still a tremendous source of entertainment nowadays, but their medieval equi...
Q: What component does an application use instead of dealing directly with the database?
A: Introduction: Database: It is a collection of information that has been organised to allow for easy ...
Q: What is wrong with the following code? Why? How can you fix it? // Remove all the books which co...
A: There is at least one error in the given code; the sentence "booksList.remove(b);" is in the wrong l...
Q: What function does HDFS play in the Hadoop architecture?
A: Hadoop:An apache Hadoop system is a collection of open source software utilities that facilitates u...
Q: o an existing order, include the product id, unit price, quantity. The output of the function is the...
A: given - Create a function to insert a new product into an existing order, include the product id, un...
Q: Implement the Doubly Circular Linked List (you need to implement two classes, one for node and one f...
A: Following is a representation of a Circular doubly linked list node in C++ struct node{ int data;...
Q: Create a location-based/image tracking Augmented Reality Quiz game with AR.js and AFRAME.js. There s...
A: Create a location-based/image tracking Augmented Reality Quiz game with AR.js and AFRAME.js. There s...
Q: When the smart tag of a control is clicked in the Designer, what happens?
A: Introduction: When the smart tag of control in the "Designer" is clicked, the following happens: Dat...
Q: these statements if the domain of each variable consists of all real
A: 1) function is x+y {=}\mathllap{/\,} y+xx+y not equals to y+x is false because addition of real ...
Q: Question#5: Write a function, reverseDigit. The function will take an integer as a parameter and ret...
A:
Q: From the lists below, for each list, select three terms, concepts or analysis from each list (that’s...
A: List 1: Database Database management system (DBMS) Structured query language (SQL) List 2: Virus w...
Q: Task 1 The position s of an object moving in a straight path is defined by the function s = vot + (...
A: s = vot + (1/2)at2 Given that initial velocity (vo) = 1.5 m/s acceleration (a) = 2 m/s2 So, s = 1.5t...
Q: c. What is the instruction to compute 32-bit unsigned multiplication? Show an example where W = W1 *...
A: Answer: Given two 32-bit signed and unsigned number and we have to find how to do this and what will...
Q: How do you keep track of elements in a partially filled array that contain data?
A: Introduction: The array's length determines the number of items. We are frequently confronted with ...
Q: 1. Consider a binary number (10101110),. What base-10 number this binary number is equivalent to if ...
A: As given, we need to need to convert the given binary number (10101110)2 into decimal number. a) Fi...
Determine whether the two bipartite graphs below have a perfect matching. Justify your answer, either by showing a perfect matching or using Hall’s theorem to prove that it does not exist.
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- python 8.7 LAB: Writing append and search methods (singly-linked list)Given main.py and a Node class in Node.py, complete the LinkedList class in LinkedList.py by writing the append() and search() methods. The search() method should return the Node whose data value matches a given key, and None if the key is not found. The search() method should also set the position of each Node searched in the LinkedList, starting with 1. Ex: If the input is: 12 23 59 37 923 212the output is: 12 found in list at position 1.If the input is: 12 23 59 37 923 268the output is: 68 not found in list.3) Implement the if __name__ == "__main__" : block at the bottom of this file to do the following: 3a) The if main block at the bottom should get the name of the highway graph file from the command line arguments. See the video in Python that explains how to get command line arguments. 3b) Call your parse_highway_graph_file function to parse that file, and to construct a WeightedGraph object from it. 3c) Write some code that outputs (with print statements) the degree of each vertex. You can have one vertex per line, indicating its id (just its 0-based index) followed by its degree. IMPORTANT: Your parse_highway_graph_file function should NOT produce any output. You will have code in your if main block that will have the print statements. The WeightedGraph class has a degree method, inherited from Graph that will return to you the degree of a vertex.Q.2. Implement a single linked list. Elements of this linked list should be of integer type, user would provide values as input for elements of this linked list. Which does not allow insertion of duplicate value to the list.
- 6.3.25 Develop a pair of TOY functions that implement a pushdown stack, passing the values to push and pop in R[B] and the address of the stack in R[A]. This question was taken from Computer science an interdisciplinary approach. NOTE: I don't need an answer with java or high-level language code but the TOY code as described in the book which has a specific set of opcodes in hexadecimal for eg 18AB; means that adding results of R[A] and R[B] and store them in R[8]. and so on...Java - Given list: ( 0, 8, 10, 16, 23, 49, 61, 74, 96 )**11.18** Java Solve (ArrayList of Character) Using the following header, create a method that produces an array list of characters from a string: toCharacterArray public static ArrayListCharacter> (String s) ToCharacterArray("abc"), for example, returns an array list containing the characters 'a', 'b', and 'c'.
- Write down a C++ program to implement the link list in the following way. a) Create an array taking 10 values from the user.b) Create a link list and fill it (insert nodes) with the array values.c) Display the link listd) Run the 9 commands given in the table on slide 9.e) Create functions for the following and implement these in order(i) Insert a new node in front of the list and display the list.(ii) Insert a new node at the end of the list and display the list(iii) Delete the first node from the list and display the list.(iv) Search for a value in the list (user entered). Note: The program must be well structured and properly commented.1. Implement a function insertBook(Book newBook) to add a book at the end of thelinked list.a. Ask the librarian to input all the necessary book information.b. Use the information to create a Book objectc. Pass through the Book object as the parameter to the functiond. Store the Book object into the Node objecte. “Link” the object with the rest of the linked list2. Implement a function insertBefore(Book newBook, int bookID) to add a book infront of another book given its bookID.a. Ask the librarian to input all the necessary book information.b. Use the information to create a Book objectc. Pass through the Book object and bookID as the parameter to the functiond. Search for the matching Book objecte. Store the Book object into the Node objectf. “Link” the object with the rest of the linked list3. Implement a function searchBook(int bookID) to search for a book by its bookIDcode and return the book object.a. Ask the librarian to input the bookID.b. If the book doesn’t exist display an…C programming fill in the following code #include "graph.h" #include <stdio.h>#include <stdlib.h> /* initialise an empty graph *//* return pointer to initialised graph */Graph *init_graph(void){} /* release memory for graph */void free_graph(Graph *graph){} /* initialise a vertex *//* return pointer to initialised vertex */Vertex *init_vertex(int id){} /* release memory for initialised vertex */void free_vertex(Vertex *vertex){} /* initialise an edge. *//* return pointer to initialised edge. */Edge *init_edge(void){} /* release memory for initialised edge. */void free_edge(Edge *edge){} /* remove all edges from vertex with id from to vertex with id to from graph. */void remove_edge(Graph *graph, int from, int to){} /* remove all edges from vertex with specified id. */void remove_edges(Graph *graph, int id){} /* output all vertices and edges in graph. *//* each vertex in the graphs should be printed on a new line *//* each vertex should be printed in the following format:…
- please complete the following in JAVA Implement the graph ADT using the adjacency list structure. thanks! also posting a similar question for adjacency matrix. have a good day!5. Construct a function C(V) that counts the number of basic operations for the following algorithm. Then place the algorithm in a time efficiency class. State any assumptions you make. public static ArrayList topologicalSort(Graph dag) { Queue q = new LinkedList(); ArrayList sortOrder = new ArrayList(); int[] inEdgeCounts = new int[dag.size()]; for(int i = 0; i < inEdgeCounts.length; i++) { inEdgeCounts[i] = 0; } for(int i = 0; i < inEdgeCounts.length; i++) { dag.getAdjList(i).stream().forEach((x) -> inEdgeCounts[x]++); } // Identify sources for(int i = 0; i < inEdgeCounts.length; i++) { if(inEdgeCounts[i] == 0) { q.add(i); } } while(!q.isEmpty()) { int currVertex = q.remove(); sortOrder.add(currVertex); ArrayList adjList = dag.getAdjList(currVertex); // Remove edges for this node for(Integer adjVertex:…PYTHON CODE: In order to beat AlphaZero, Grandmaster Hikaru is improving her chess calculation skills.Today, Hikaru took a big chessboard with N rows (numbered 1 through N) and N columns (numbered 1 through N). Let's denote the square in row r and column c of the chessboard by (r,c). Hikaru wants to place some rooks on the chessboard in such a way that the following conditions are satisfied:• Each square of the board contains at most one rook.• There are no four rooks forming a rectangle. Formally, there should not be any four valid integers r1, c1, r2, c2 (≠r2,c1≠c2) such that there are rooks on squares (r1,c1), (r1,c2 (r2,c1)and (r2,c2).• The number of rooks is at least 8N.Help Hikaru find a possible distribution of rooks. If there are multiple solutions, you may find any one. It is guaranteed that under the given constraints, a solution always exists.InputThe first line of the input contains a single integer T denoting the number of test cases. The first and only line of each test…

