
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
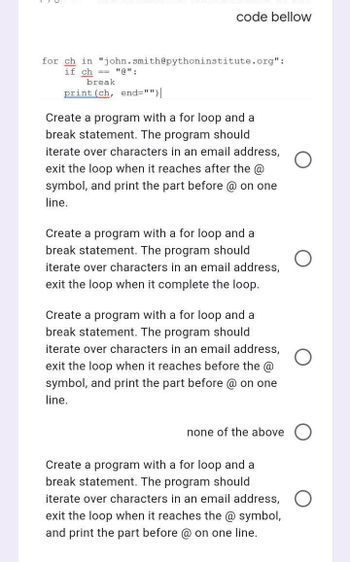
Transcribed Image Text:code bellow
for ch in "john.smith@pythoninstitute.org":
if ch == "@":
break
print (ch, end="")|
Create a program with a for loop and a
break statement. The program should
iterate over characters in an email address,
exit the loop when it reaches after the @
symbol, and print the part before @ on one
line.
Create a program with a for loop and a
break statement. The program should
iterate over characters in an email address,
exit the loop when it complete the loop.
Create a program with a for loop and a
break statement. The program should
iterate over characters in an email address,
exit the loop when it reaches before the @
symbol, and print the part before @ on one
line.
none of the above
Create a program with a for loop and a
break statement. The program should
iterate over characters in an email address,
exit the loop when it reaches the @ symbol,
and print the part before @ on one line.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution
Trending nowThis is a popular solution!
Step by stepSolved in 4 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- 14. Create a do while loop that uses controlling variable x. The loop shall generate and display one value per iteration from the variable x. The values are to be displayed using console.log. The expected output values are: 1-2 4-816arrow_forwardWrite a while loop that prints the multiples of 3 from 300 down to 3. The programming language is java.arrow_forwardGiven the code: int x, y: cout > x >> y: Write a loop to print all numbers that are factors of x and not factors of y. Example Output 1 Enter two integers: 12 30 4 12 Example Output 2 Enter two integers: 15 24 5 15arrow_forward
- True or False: C++ uses negative values to represent "False" and positive values to represent "True". It is possible that the body of a while loop may not execute at all.arrow_forwardConstruct a single for loop to print out the following lines. You may use as many variables as you wish, but you may not use multiple loops. 4 4 4 8 2 7 16 1 10 32 0.5 13 64 0.25 16arrow_forwardAccumulating Totals in a Loop Summary In this lab, you add a loop and the statements that make up the loop body to a Java program that is provided. When completed, the program should calculate two totals: the number of left-handed people and the number of right-handed people in your class. Your loop should execute until the user enters the character X instead of L for left-handed or R for right-handed. The inputs for this program are as follows: R, R, R, L, L, L, R, L, R, R, L, X Variables have been declared for you, and the input and output statements have been written. Instructions Ensure the file named LeftOrRight.java is open. Write a loop and a loop body that allows you to calculate a total of left-handed and right-handed people in your class. Execute the program by clicking Run and using the data listed above and verify that the output is correct.arrow_forward
- PrimeAA.java Write a program that will tell a user if their number is prime or not. Your code will need to run in a loop (possibly many loops) so that the user can continue to check numbers. A prime is a number that is only divisible by itself and the number 1. This means your code should loop through each value between 1 and the number entered to see if it’s a divisor. If you only check for a small handful of numbers (such as 2, 3, and 5), you will lose most of the credit for this project. Include a try/catch to catch input mismatches and include a custom exception to catch negative values. If the user enters 0, the program should end. Not only will you tell the user if their number is prime or not, you must also print the divisors to the screen (if they exist) on the same line as shown below AND give a count of how many divisors there are. See examples below. Your program should run the test case exactly as it appears below, and should work on any other case in general. Output…arrow_forward5. What will be the value of x after the following loop is executed? X = 0 For i = 1 To 2 For j = 1 To 3 X = X +i* j Next j Next iarrow_forwardAnswer True or False _____ 1. It is possible that the body of a while loop might not execute at all. _____ 2. Control structures alter the normal flow of control. _____ 3. The result of a logical expression cannot be assigned to an int variable. _____ 4. Every if statement must have a corresponding else. _____ 5. The expression ! (x > 0) is true only if x is a negative number. _____ 6. The while loop: j = 0; while (j <= 10) j++; terminates when j > 10. _____ 7. A loop is a control structure that causes certain statements to execute over and over. _____ 8. When a while loop terminates, the control first goes back to the statement just before the while statement, and then the control goes to the statement immediately following the while loop. _____ 9. In a do…while loop, the condition is checked at the bottom of the loop. _____ 10. A do…while loop may never execute.arrow_forward
- How do I write the while loop using a sentinel value to control the loop, and also write the statements that make up the body of the loop? Also including the calculations to compute the average rating.arrow_forwardWrite a do...while loop that uses the loop control variable to take on the values 0 through 10.arrow_forward3. Write a program called NestedLoop that prints the below. Use a for nested loop. No credit if nested loop is not used. (10 pnts) 1 22 333 4444 55555arrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education