
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
I need to create a function using GitHub.
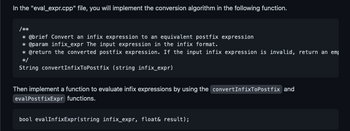
Transcribed Image Text:In the "eval_expr.cpp" file, you will implement the conversion algorithm in the following function.
/***
* @brief Convert an infix expression to an equivalent postfix expression
* @param infix_expr The input expression in the infix format.
* @return the converted postfix expression. If the input infix expression is invalid, return an emp
*/
String convertInfixToPostfix (string infix_expr)
Then implement a function to evaluate infix expressions by using the convertInfixToPostfix and
evalPostfixExpr functions.
bool evalInfixExpr(string infix_expr, float& result);
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution
Trending nowThis is a popular solution!
Step by stepSolved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- MUST BE IN C AND UTILIZE USER DEFINED FUNCTION. THANK YOU UDF should take an argument, which needs to be an array, and return the average to the mainfunction. The average should be displayed by a printf() within the main (). Create a script that will find the average of {-100, 97, 83, 21, -50, 20, 101, 30}, {12, 21, 57, 28, 108,30}, {10,20,30,40, 50, 60, 70, 90, 100, -110, -120, -130,-140}, or ANY SET OF NUMBERS![THE USER SHOULD BE PROMPTED TO TYPE IN THE SIZE OF ARRAY. THEN, EACH FOLLOWING NUMBERTHAT USER TYPES IN SHOULD BE STORED IN THIS ARRAY. Whole computation must be done by accessingelements in the array.)arrow_forwardProblem D. Find URLsHTML is a language for representing documents designed to be displayed by a web browser. In many browsers, you can see the HTML source code by right-clicking somewhere on the page and clicking “View Page Source”. If you try this on a web page with links to other websites, you’ll notice that the URL of the link is usually formatted in the following way: href="https://some.website.com/subfolder/more_stuff.txt" Write a function find_url(html) that takes in a string of html text that contains exactly one external link URL formatted as above, and returns just the URL string (in the above example, that would be https://some.website.com/subfolder/more_stuff.txt). You can assume that the only place in the string where the substring href=" occurs is right before the URL, and that the next quotation mark after that point denotes the end of the URL. Hints: ● The .find method and string slicing will likely make this easier. ● Remember that in order to use a double quote…arrow_forwardThis is the program i have been given. I have to change it to meet the following criteria but can only change the body of the show_flashcard function # IMPORTANT# Q2 (a)(iii) Make changes only to# -- the docstring for the program as a whole.# -- the docstring of the show_flashcard() function# -- the body of the show_flashcard() function. def show_flashcard(): """ Show the user a random key and ask them to define it. Show the definition when the user presses return. """ random_key = choice(list(word_list)) print('Define: ', random_key) input('Press return to see the definition') print(word_list[random_key]) # Set up the word_list word_list = {'black':'noir', 'red':'rouge', 'yellow':'jaune', 'orange':'orange', 'white':'blanc', 'green':'vert'} # The interactive loop exit = Falsewhile not exit: user_input = input('Enter s to show a flashcard and q to quit: ') if user_input == 'q':…arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education