
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
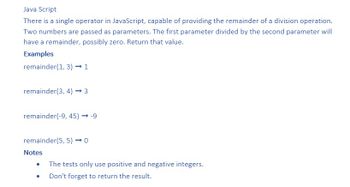
Transcribed Image Text:Java Script
There is a single operator in JavaScript, capable of providing the remainder of a division operation.
Two numbers are passed as parameters. The first parameter divided by the second parameter will
have a remainder, possibly zero. Return that value.
Examples
remainder(1, 3) → 1
remainder(3, 4) → 3
remainder(-9, 45) → -9
remainder(5, 5) → 0
Notes
The tests only use positive and negative integers.
Don't forget to return the result.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution
Trending nowThis is a popular solution!
Step by stepSolved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Microfost Visual C# 7th edition programming exercise 6-10. I need help, please. This problem relies on the generation of a random number. You can create a random number that is at least min but less than max using the following statements: Random ranNumberGenerator = new Random();int randomNumber;randomNumber = ranNumberGenerator.Next(min, max); Create a game similar to Hangman named GuessAWord in which a player guesses letters to try to replicate a hidden word. Store at least eight words in an array, and randomly select one to be the hidden word. Initially, display the hidden word using asterisks to represent each letter. Allow the user to guess letters to replace the asterisks in the hidden word until the user completes the entire word. If the user guesses a letter that is not in the hidden word, display an appropriate message. If the user guesses a letter that appears multiple times in the hidden word, make sure that each correct letter is placed. Figure 6-27 shows a typical game…arrow_forwardASSIGNMENT BRIEF Introduction Roulette is a popular casino game named after the French word for 'little wheel'. In the game, players may choose to place bets on single numbers or various groupings which will determine their payout. To determine the winning number a ball is spun in the opposite direction of a spinning wheel. As the ball loses momentum it comes to rest in one of the slots of the wheel. Winnings are then paid to anyone who places a successful bet. n 00 2. 1ST12 2ND12 3RD12 1T018 EVEN ODD |19то36 Figure 1: Layout of a European roulette table Numbers can be classified in several ways: 1. Red or Black 2. Odd or Even 3. High or Low - if a number is in the first half of the table it is considered low (1-18). If a number is in the second half of the table, it is considered high (19-36). 4. Dozens - a number can be in the first dozen(1-12), second dozen (13-24) or third dozen (25-36) 5. Columns - A number may be in any of the three columns of the table 6. Zero - the number '0'…arrow_forwardPlease help me to code this Python It is High/Low Card Game The pyex is example of outputarrow_forward
- uppose you have a certain amount of money in a savings account that earns compoundmonthly interest, and you want to calculate the amount that you will have after a specificnumber of months. The formula, which is known as the future value formula, is:F=P×(1+i)tThe terms in the formula are as follows:o F is the future value of the account after the specified time period.o P is the present value of the account.o i is the monthly interest rate.o t is the number of months.Write a program that prompts the user to enter the account’s present value, monthlyinterest rate, and the number of months that the money will be left in the account. Theprogram should pass these values to a function named futureValue that returns thefuture value of the account, after the specified number of months. The program shoulddisplay the account’s future value. i attached the screenshot of the output so the output should look like that. the coding should be in c++arrow_forwardJava coding platformarrow_forwardCharge Account Validation Using Java programming Create a class with a method that accepts a charge account number as its argument. The method should determine whether the number is valid by comparing it to the following list of valid charge account numbers:5658845 4520125 7895122 8777541 8451277 13028508080152 4562555 5552012 5050552 7825877 12502551005231 6545231 3852085 7576651 7881200 4581002These numbers should be stored in an array. Use a sequential search to locate the number passed as an argument. If the number is in the array, the method should return true, indicating the number is valid. If the number is not in the array, the method should return false, indicating the number is invalid.Write a program that tests the class by asking the user to enter a charge account number. The program should display a message indicating whether the number is valid or invalid.arrow_forward
- Computer Science Part C: Interactive Driver Program Write an interactive driver program that creates a Course object (you can decide the name and roster/waitlist sizes). Then, use a loop to interactively allow the user to add students, drop students, or view the course. Display the result (success/failure) of each add/drop.arrow_forwardPython Knapsack: you are carrying a knapsack with capacity to hold a total of weight C. You are selecting among n items with values A={a1, a2, ... , an} and associated weights W={w1, w2, ... , wn}. Here the weights and values are all positive. You wish to maximize the total value of the items you select not exceeding the given weight capacity, example, maximize sum_{a in A} such that sum_{w in W} <= C. Note that you can only select your items once. In Python, create function DP_K (C, A, W) as stated above. Input an array to the function to hold the backtrace. What is the best set of items for C = 30, A = [40, 110, 100] and w = [20, 30, 40]? This can be shown using auxiliary printing function.arrow_forwardPython Returning function function name: is_prime parameters: a number n returns: True if n is prime behavior: Check the values in the range [2, n) and return False if n is divible by any of them. function name: bound_0_to_100 parameters:a number grade returns: the grade with a minimum of 0 and a maximum of 100 behavior: In addition to exceeding 100, sometimes a grade will be so spectacularly bad that it falls below 0. In that case we want to normalize it to 0 so all grades fall into the range [0, 100]. ex: bound_0_to_100(75) returns 75, bound_0_to_100(103) returns 100, and bound_0_to_100(-5) returns 0 function name: bigger parameters: two values a and b returns: whichever of the two is greatest behavior: ex: bigger(3, 9) returns 9arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education