
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Topic Video
Question
Implementing in Java the Aho Corasick
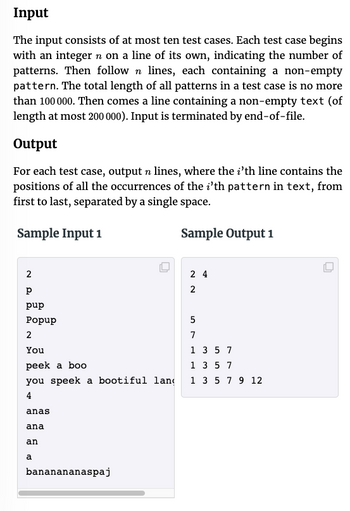
Transcribed Image Text:Input
The input consists of at most ten test cases. Each test case begins
with an integer n on a line of its own, indicating the number of
patterns. Then follow n lines, each containing a non-empty
pattern. The total length of all patterns in a test case is no more
than 100 000. Then comes a line containing a non-empty text (of
length at most 200 000). Input is terminated by end-of-file.
Output
For each test case, output n lines, where the i'th line contains the
positions of all the occurrences of the i'th pattern in text, from
first to last, separated by a single space.
Sample Input 1
Sample Output 1
2
Р
pup
Popup
2
You
peek a boo
you speek a bootiful lan
4
anas
ana
an
a
O
bananananaspaj
24
2
5
7
1 3 5 7
1 3 5 7
1 3 5 7 9 12
O
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 4 steps with 5 images

Follow-up Questions
Read through expert solutions to related follow-up questions below.
Follow-up Question
What would the implementation regarding the input section look like in Java?
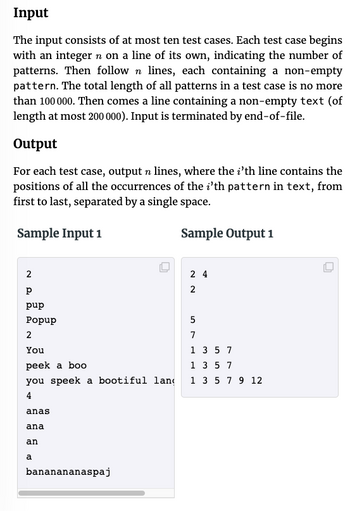
Transcribed Image Text:Input
The input consists of at most ten test cases. Each test case begins
with an integer n on a line of its own, indicating the number of
patterns. Then follow n lines, each containing a non-empty
pattern. The total length of all patterns in a test case is no more
than 100 000. Then comes a line containing a non-empty text (of
length at most 200 000). Input is terminated by end-of-file.
Output
For each test case, output n lines, where the i'th line contains the
positions of all the occurrences of the i'th pattern in text, from
first to last, separated by a single space.
Sample Input 1
Sample Output 1
2
Р
pup
Popup
2
You
peek a boo
you speek a bootiful lan
4
anas
ana
an
a
O
bananananaspaj
24
2
5
7
1 3 5 7
1 3 5 7
1 3 5 7 9 12
O
Solution
by Bartleby Expert
Follow-up Questions
Read through expert solutions to related follow-up questions below.
Follow-up Question
What would the implementation regarding the input section look like in Java?
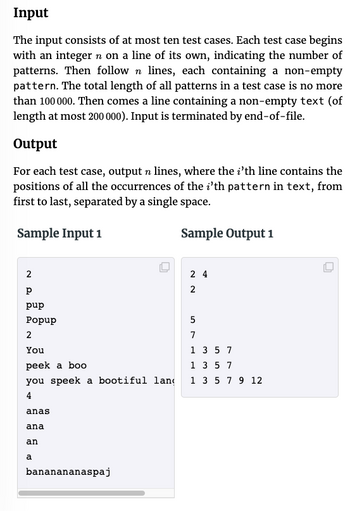
Transcribed Image Text:Input
The input consists of at most ten test cases. Each test case begins
with an integer n on a line of its own, indicating the number of
patterns. Then follow n lines, each containing a non-empty
pattern. The total length of all patterns in a test case is no more
than 100 000. Then comes a line containing a non-empty text (of
length at most 200 000). Input is terminated by end-of-file.
Output
For each test case, output n lines, where the i'th line contains the
positions of all the occurrences of the i'th pattern in text, from
first to last, separated by a single space.
Sample Input 1
Sample Output 1
2
Р
pup
Popup
2
You
peek a boo
you speek a bootiful lan
4
anas
ana
an
a
O
bananananaspaj
24
2
5
7
1 3 5 7
1 3 5 7
1 3 5 7 9 12
O
Solution
by Bartleby Expert
Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Regular expression of language part 1: EVEN-EVEN part 2: ODD-EVEN part 3: EVEN-ODD part 4: ODD-ODDarrow_forwardDoes Python recommend any particular actions to do out?arrow_forwardThe words prefix, infix, and postfix notation should be defined. What does the term "Cambridge Polish notation" mean? Two programming languages that use postfix notation should be mentioned.arrow_forward
- What are Loops in Java? What are three types of loops?arrow_forwardLisp and Python are dynamically typed languages, while C++ and Java are statically typed languages. Discuss the benefits and drawbacks of each typing method.arrow_forwardPlz make the UML diagram of Food ordering register in Javaarrow_forward
- MAKE A SUMMARY ON DEBUGGNG IN PYTHON MAKE THREE CODE AND EXPLAIN ITarrow_forwardCould I get this code explained to me in java. I have the general grasp but would love to have it explained in a language im more famaliar with.arrow_forwardIs it possible for the coding to be done in python?arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education