
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
Please only do rec_sum_digits function in python using only recursive and no loop
Transcribed Image Text:**Problem A: Implementing Digit Sum Functions**
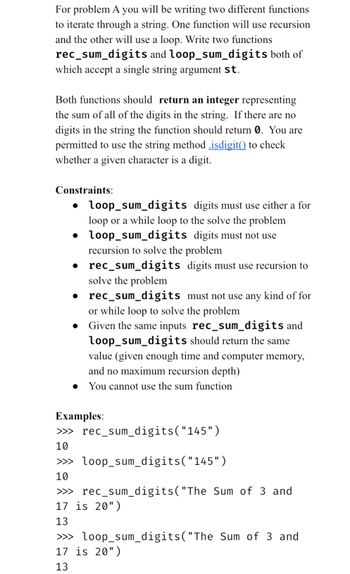
For this task, you will write two different functions to iterate through a string. One function will use recursion, while the other will use a loop. Your goal is to implement two functions: `rec_sum_digits` and `loop_sum_digits`, both accepting a single string argument `st`.
### Function Requirements
Both functions should return an integer representing the sum of all the digits in the given string. If there are no digits, the function should return `0`. You can use the string method `.isdigit()` to check if a character is a digit.
### Constraints
- **`loop_sum_digits`:**
- Must use either a `for` loop or a `while` loop to solve the problem.
- Must not use recursion.
- **`rec_sum_digits`:**
- Must use recursion to solve the problem.
- Must not use any kind of `for` or `while` loop.
Given the same inputs, both `rec_sum_digits` and `loop_sum_digits` should return the same value, assuming there is enough time, memory, and no maximum recursion depth. Additionally, you cannot use the built-in `sum` function.
### Examples
```plaintext
>>> rec_sum_digits("145")
10
>>> loop_sum_digits("145")
10
>>> rec_sum_digits("The Sum of 3 and 17 is 20")
13
>>> loop_sum_digits("The Sum of 3 and 17 is 20")
13
```
In these examples, the functions correctly identify the digits within the strings and compute their sum.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution
Trending nowThis is a popular solution!
Step by stepSolved in 4 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- A recursive function must have a to end the recursion. recursive call base case O value boolean conditionarrow_forwardTRUE OR FASLE A recursive solution can be implemented within two function one that is recursive and one that is not C PROGRAMMING LANGUAGEarrow_forwardDefine a function is_prime that recieves an integer arguement and returns true if the arguement is a prime number and otherwise returns false. This function may be written with a for loop, while loop or using a recursion.arrow_forward
- Write the recursive function based on the following formula in Visual Basic code: if n=0 f(n) = 1 if n = 1 F(n- 1) + F(n – 2) if n>1arrow_forwardRecursive formula for 2, 5, 10, 17, 26 in the form of a_n = a_n-1 + Cn + Darrow_forwardWhen a recursive function is run, there is an additional demand placed on the memory of the computer and the amount of time it takes to run the programme.arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education