
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
Transcribed Image Text:令l.
16:56
Q SEARCH
& ASK 탄 CHAT
VX MATH SOLV
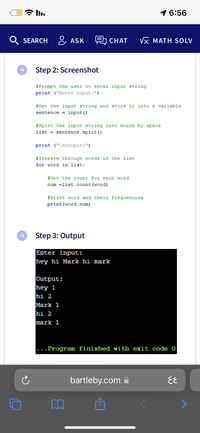
Step 2: Screenshot
#Prompt the user to enter input string
print ("Enter input:")
#Get the input string and store it into a variable
sentence = input ()
#Split the input string into words by space
list = sentence.split()
print ("\noutput:")
#Iterate through words in the list
for word in list:
#Get the count for each word
num =list.count (word)
#Print word and their frequencies
print (word, num)
->
Step 3: Output
Enter input:
hey hi Mark hi mark
Output:
hey 1
hi 2
Mark 1
hi 2
mark 1
...Program finished with exit code o
bartleby.com A
EE
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- exercise5.py 1 Your code goes here... Guide Collapse Strings -> Coding Exercises - Strings Exercise 5 Exercise 5 Problem Write a program that captures input from the user. Then, swap the letters two at a time in the string. The first two characters change places, the third and fourth characters change places, etc. Assume that the user will only input strings with an even number of characters. Important, do not put a prompt when asking for user input. Just use input(). Adding a prompt will cause your program to not pass the tests. Expected Output • If the user inputs home, then the output is ohem . If the user inputs cars then the output is acer Code Visualizer TRY IT Reminder, do not put a prompt when collecting user input. Just use input() Check It! (1 left) TTTarrow_forwardA variable named VOWELS=“aeiou”, the capitalization would indicate it is to used as a A. A list B. An int C. A constant D. A tuple arrow_forwardPythonarrow_forward
- prompt user to enter a number numthis num would be set as the range the user to enter other intergers.create a list and loop to populate it with each integer the user enters up to numprint the list. Example:if num entered as 4then prompt the user to enter 4 integers. 3 6 7 9then print the list as [3, 6, 7, 9] Thank youarrow_forwardWrite a program that uses 2 lists. Call the lists Items and Basket respectively. The first list will contain a list of at least 10 items (make up your own items) to select from. The second list will be used to add the selected items in the new list.(Basket) Your program should do the following in a Loop until the user exits the loop: Display the list (print out 1, 2, 3, 4, etc. before each item in the list (Hint: Use Index + 1) Prompt the user to select an item from the Items list. Add the selected item to the new list (Basket) (HINT: Use number entered - 1 for the Index) When the user selects 0, exit the loop and print out the new list of items (Basket)arrow_forwardFill in the second blank with a statement completing the program so that after the loop executes, the variable min_index contains the index in the list corresponding to the minimum temperature.arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education