
Computer Networking: A Top-Down Approach (7th Edition)
7th Edition
ISBN: 9780133594140
Author: James Kurose, Keith Ross
Publisher: PEARSON
expand_more
expand_more
format_list_bulleted
Question
I know you guys are using AI . Don't you dare give me AI generated answer or plagiarised answer. If I see these things I'll give you multiple downvotes and will report immediately.
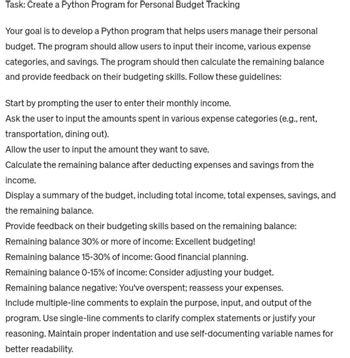
Transcribed Image Text:Task: Create a Python Program for Personal Budget Tracking
Your goal is to develop a Python program that helps users manage their personal
budget. The program should allow users to input their income, various expense
categories, and savings. The program should then calculate the remaining balance
and provide feedback on their budgeting skills. Follow these guidelines:
Start by prompting the user to enter their monthly income.
Ask the user to input the amounts spent in various expense categories (e.g., rent,
transportation, dining out).
Allow the user to input the amount they want to save.
Calculate the remaining balance after deducting expenses and savings from the
income.
Display a summary of the budget, including total income, total expenses, savings, and
the remaining balance.
Provide feedback on their budgeting skills based on the remaining balance:
Remaining balance 30% or more of income: Excellent budgeting!
Remaining balance 15-30% of income: Good financial planning.
Remaining balance 0-15% of income: Consider adjusting your budget.
Remaining balance negative: You've overspent; reassess your expenses.
Include multiple-line comments to explain the purpose, input, and output of the
program. Use single-line comments to clarify complex statements or justify your
reasoning. Maintain proper indentation and use self-documenting variable names for
better readability.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 4 steps with 3 images

Knowledge Booster
Similar questions
- Your employer's new security policy requires all employees to use fingerprint readers instead of login and passwords to access their computers. You cut your finger when logging in over the weekend. That's why your computer can't read your fingerprint. This causes your computer unable. What's your dream?arrow_forwardplease answerarrow_forwardPhishing is one type of electronic con, and it can be used in combination with fraud and other methods. There may also be other ways to do it. You can also use phishing on its own. What are the best ways to stop scams like phishing and faking from happening, and how can they be done?arrow_forward
- There is a possibility that you may get emails alleging that someone has stolen your identity or compromised the information associated with your account. Consider the repercussions of your actions.arrow_forwardYou are going to get an email from the mail server at work informing you that your password has been changed and that you need to confirm this information. There is a strong likelihood that you haven't changed the password in a while. What caused the password to be different? Malware that was installed on the computers that successfully changed the password may have been utilized by an attacker.arrow_forwardYou are going to get an email from the mail server at work informing you that your password has been changed and that you need to confirm this information. There is a strong likelihood that you haven't changed the password in a while. What caused the password to be different? Malware that was installed on the computers that successfully changed the password may have been utilized by an attacker.arrow_forward
- What are the undeniable signs that you are putting yourself in danger by passively smelling, and what can you do to protect yourself from being a victim of one of these situations?arrow_forwardInstead of providing a username and password, workers at your organization must now sign in using a fingerprint reader as a security measure. You cut your finger while trying to sign in over the weekend, and as a result, your computer no longer recognizes your fingerprint. So, you can't get into your computer. What's next for you?arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON
Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science
Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning
Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning
Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education
Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY
Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY

Computer Networking: A Top-Down Approach (7th Edi...
Computer Engineering
ISBN:9780133594140
Author:James Kurose, Keith Ross
Publisher:PEARSON

Computer Organization and Design MIPS Edition, Fi...
Computer Engineering
ISBN:9780124077263
Author:David A. Patterson, John L. Hennessy
Publisher:Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:9781337569330
Author:Jill West, Tamara Dean, Jean Andrews
Publisher:Cengage Learning

Concepts of Database Management
Computer Engineering
ISBN:9781337093422
Author:Joy L. Starks, Philip J. Pratt, Mary Z. Last
Publisher:Cengage Learning

Prelude to Programming
Computer Engineering
ISBN:9780133750423
Author:VENIT, Stewart
Publisher:Pearson Education

Sc Business Data Communications and Networking, T...
Computer Engineering
ISBN:9781119368830
Author:FITZGERALD
Publisher:WILEY