
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
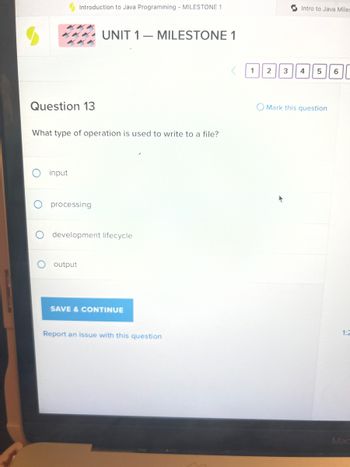
Transcribed Image Text:### Introduction to Java Programming - Milestone 1
#### UNIT 1 — MILESTONE 1
---
**Question 13**
What type of operation is used to write to a file?
- input
- processing
- development lifecycle
- output
**Options:**
1. □
2. □
3. □
4. □
5. □
6. □
---
- **Mark this question**
- (Check to mark the question for review)
- **Save & Continue**
- (Button to save the current progress and proceed to the next question)
- **Report an issue with this question**
- (Link to report any issues encountered with this question)
#### Diagram Explanation:
On the right side of the question, a sequence of numbered boxes (1 to 6) is present. These represent navigation between different questions or sections, with the ability to mark questions for review.
---
**Note:** Ensure to choose the correct option before proceeding to the next question. In this case, the correct answer would be "output," as writing a file involves output operations in programming.
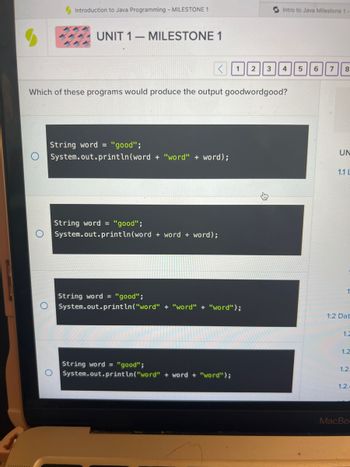
Transcribed Image Text:### Introduction to Java Programming - Unit 1 Milestone 1
#### Question:
Which of these programs would produce the output `goodwordgood`?
##### Option A:
```java
String word = "good";
System.out.println(word + "word" + word);
```
##### Option B:
```java
String word = "good";
System.out.println(word + word + word);
```
##### Option C:
```java
String word = "good";
System.out.println("word" + "word" + "word");
```
##### Option D:
```java
String word = "good";
System.out.println("word" + word + "word");
```
---
#### Analysis:
1. **Option A**:
- Code Explanation:
```java
String word = "good";
System.out.println(word + "word" + word);
```
- This option assigns the string `"good"` to the variable `word`.
- The `System.out.println()` statement concatenates the value of `word`, the string `"word"`, and again the value of `word` and outputs it to the console.
- Output: `goodwordgood`
2. **Option B**:
- Code Explanation:
```java
String word = "good";
System.out.println(word + word + word);
```
- This option assigns the string `"good"` to the variable `word`.
- The `System.out.println()` statement concatenates the value of `word` three times and outputs it to the console.
- Output: `goodgoodgood`
3. **Option C**:
- Code Explanation:
```java
String word = "good";
System.out.println("word" + "word" + "word");
```
- This option assigns the string `"good"` to the variable `word`.
- The `System.out.println()` statement concatenates the string `"word"` three times and outputs it to the console.
- Output: `wordwordword`
4. **Option D**:
- Code Explanation:
```java
String word = "good";
System.out.println("word" + word + "word");
```
- This option assigns the string `"good"` to the variable `word`.
- The `System.out.println()` statement concatenates the string `"word"`, the value of `word`, and the string `"word"`
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution
Trending nowThis is a popular solution!
Step by stepSolved in 4 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- What benefit does using the Open and/or Save As dialog boxes in a file-related application provide?arrow_forwardTo read the first 10 characters of a file file.read(10) file.readline(10) file.readlines(10) None of the abovearrow_forwardWhat are the three steps involved when a piece of software utilizes a file?arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education