
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
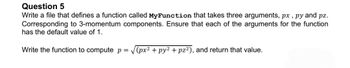
Transcribed Image Text:Question 5
Write a file that defines a function called MyFunction that takes three arguments, px, py and pz.
Corresponding to 3-momentum components. Ensure that each of the arguments for the function
has the default value of 1.
Write the function to compute p = √(px² + py² +pz²), and return that value.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 3 steps with 2 images

Follow-up Questions
Read through expert solutions to related follow-up questions below.
Follow-up Question
could you do this in python??
Solution
by Bartleby Expert
Follow-up Questions
Read through expert solutions to related follow-up questions below.
Follow-up Question
could you do this in python??
Solution
by Bartleby Expert
Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Write a function getQuestions that accepts a single parameter: filename, which is the name of a txt file. Your function should assume that the text file is formatted in the following way, as a series of questions and answers, with a question on one line, and the answer to the question on the following line, as below ---Sample File--- Why is the sky blue? Because air is blue. How long does it take light to reach Earth from the Sun? About eight minutes. What is the dumbest question you've ever been asked? That one. ---End Sample File--- Your function should create and return a dictionary where the keys are the questions and the values are respective answers (so the above sample file would result in a dictionary with three key-value pairs, one per question).arrow_forwardpls code in pythonplagiarism: This Boolean function takes two filenames. If any line occurs in both files, return True.If not, return False. I suggest using nested loops. With nested loops, we call the loop that is in thebody of the other loop, the "inner loop". The loop that contains the inner loop is the "outer loop". Openthe second file inside the outer loop:for line1 in file1:file2 = open(fname2)for line2 in file2:Python only lets you read the file once per open, so you need this order of instructions. Make sure yourreturn False is outside of both loops. Otherwise, you will only compare the first two lines of thefiles. Make sure you close the file that gets read repeatedly after the inner loop but still inside the outerloop.Here is some (more complete) pseudocode to get you started:open file 1for line1 in file 1open file 2for line2 in file 2:if line1 == line2:return Trueclose file 2return Falsearrow_forwardI need help on my python assignment.arrow_forward
- Write a Python function ‘AVGCSV’ that reads a .csv file that includes ‘n’ rows and ‘m’ columns, it calculates the average of each row and writes it at the end of the row, and it calculates the average of each column and writes it at the end of the column. The function should modify the .csv file and save it after adding all the averages.arrow_forwardWrite a python code for the following question. Your program will read data from the provided CSV file into a DataFrame. The data file has 6 columns: A, B, C, D, E, and F, where A and B are categorical, and the rest are numeric. Write functions to normalize the data in each columnusing the following methods. Apply these functions on column C.(a) Min-max normalization that transforms the values onto a given range, forexample, [−1.0, 1.0].(b) Z-score normalization.(c) Decimal scaling normalization.arrow_forwardPlease I want a python program for this using CSV write a function that takes a list of strings as inputs, and returns a single string created by joining all the input strings together, with a comma separating them. Now write another function that takes a list of lists of strings, applies the operation from question 1 to each list, and writes the result as a row of an output file. The function should return the path to the file where the strings were written. 3. Now, write the reverse of question 2: write a function that takes in a filename (which we will assume is a CSV), and returns a list of lists of strings, where one row in the file corresponds to one list in the output list (and each value between the commas in the file row is one element in the list).arrow_forward
- Implement the following functions. Each function deals with null terminated C-Style strings. You can assume that any char array passed into the functions will contain null terminated data. Place all of the functions in a single file and then (in the same file) create a main() function that tests the functions thoroughly. You will lose points if you don't show enough examples to convince me that your function works in all cases. Please note the following: You may not use any variables of type string. This means that you should not #include <string>. Also, you may not use any c-string functions other than strlen(). If you use any other c-string functions, you will not get credit. Note, however, that functions such as toupper(), tolower(), isalpha(), isspace(), and swap() are NOT c-string functions, so you can use them. Also note that this prohibition is only for the functions that you are assigned to write. You can use whatever you want in your main() function that tests the…arrow_forwardWrite a complete C program that inputs marks of a student in 5 courses using any loop and writes these marks into an output file named txt. After that, it reads scores from myElements.txt and computes the grades based on the table below using a programmer-defined function char computeGrade(double score), and displays the grades on screen. (Attach your code and sample outputs) Score Grade >= 90 A 80-89 B 70-79 C 60-69 D <= 59 Farrow_forward8. You have a file quotes.txt containing quotes, one per line, on security. Write a functionquote() that takes a piece of text (i.e., a string) as input and prints any quote thatcontains that piece of text.>>> quote('watch')'Who will watch the watchmen.' Juvenal >>> quote('who')'Anyone who considers arithmetical methods of producingrandom digits is, of course, in a state of sin.' John VonNeumann>>> quote('is')'The price of freedom is eternal vigilance.' ThomasJefferson'Anyone who considers arithmetical methods of producingrandom digits is, of course, in a state of sin.' John VonNeumann'And so it often happens that an apparently ingenious ideais in fact a weakness which the scientific cryptographerseizes on for his solution.' Herbert Yardleyarrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education