
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
Write a java program. The program asks for an input of the name of a txt file. Then creates a Multiplication Table from 1 to 9, and writes the table into the file.
When you run your program, you may see the result like this:
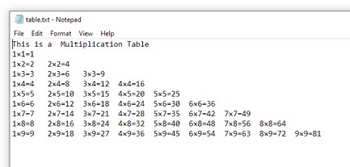
Transcribed Image Text:table.txt-Notepad
File Edit Format View Help
This is a Multiplication Table
1x1-1
1x2=2 2x2=4
1x3-3 2x3-6 3x3-9
1x4-4 2x4-8 3x4-12 4x4-16
1x5=5 2x5=10 3x5-15 4x5-20 5x5=25
1x6-6 2x6-12
4x6-24 5x6-30 6x6-36
3x6-18
1x7-7 2x7-14 3x7-21 4x7-28 5x7-35 6x7-42 7x7-49
1x8=8 2x8-16 3x8-24 4x8-32 5x8-40 6x8-48 7x8-56 8x8-64
1x9=9
3x9-27 4x9-36 5x9-45 6x9-54 7x9-63 8x9-72 9x9-81
![Problems Javadoc Declaration Console X
Data Hierarchy
<terminated > Lab5Q1 [Java Application] C:\Program Files\Eclipse Foundation\bin\javaw.
Enter a file name:
table.txt
putput file has been created: table.txt](https://content.bartleby.com/qna-images/question/c67e8434-279d-4a04-a977-2f743e81bdb3/445f7771-37a5-40e5-b9a1-ec460cb05545/6xosgl_thumbnail.png)
Transcribed Image Text:Problems Javadoc Declaration Console X
Data Hierarchy
<terminated > Lab5Q1 [Java Application] C:\Program Files\Eclipse Foundation\bin\javaw.
Enter a file name:
table.txt
putput file has been created: table.txt
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution
Trending nowThis is a popular solution!
Step by stepSolved in 2 steps with 4 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Turning ON/OFF a list of pins We want to create a program that repeats the following sequence continuously: Turn pin 5 ON Wait 1 second Turn pin 5 OFF Wait 1 second Turn pin 6 ON Wait 1 second Turn pin 6 OFF … // do the same for pins 7, 8, 9 Turn pin 10 ON Wait 1 second Turn pin 10 OFF Write the Ardiuno code with comments and compile the program by using arrays and for loops. Take a screen shot of your code and paste it below.arrow_forwardWrite a C++ program that depicts a multiplication table. your program should ask the user to enter the number of rows and columns. Sample output is something like the following: How many rows the multiplication table has? 3 How many columns? 4 your multiplication is the following: 1 2 3 4 1 1 2 3 4 2 2 4 6 8 3 3 6 9 12arrow_forwardWrite a program that reads a list of words. Then, the program outputs those words and their frequencies. The input begins with an integer indicating the number of words that follow. Assume that the list will always contain fewer than 20 words. Ex: If the input is: 5 hey hi Mark hi mark the output is: hey 1 hi 2 Mark 1 hi 2 mark 1 Hint: Use two arrays, one array for the strings and one array for the frequencies. 453086.3222312.qx3zqy7 LAB ACTIVITY HN356 10.16.1: LAB: Word frequencies 1 import java.util.Scanner; 3 public class LabProgram { 2 public static void main(String[] args) { Type your code here. */ LabProgram.java 0/10 Load default template...arrow_forward
- Write a program in python with a function timestable(n), which prints a multiplication table of size n. For example, timestable(5) would print: 12345 2 3 4 5 4 6 8 10 6 9 12 15 8 12 16 20 10 15 20 25Use the function in a program where you ask the user for n and you print the corresponding table.arrow_forwardI could really use some help with a problem I got for coding. A screenshot showing an example would help.arrow_forwardWrite a program that obtains the executiontime of external sorts for integers of size 6,000,000, 12,000,000, 18,000,000,24,000,000, 30,000,000, and 36,000,000. Your program should print a tablelike this:arrow_forward
- I need to write a program in Python which does the following. Using Python IDLE. Program Catch_The_Turtle:Set up turtle screenSet up list of 100 turtles in an arrayPlace the 100 turtles randomly on the screenCreate a function to move the 100 random turtlesIn a for loopMove the 100 turtles towards the turtle in front of itUpdate the turtle screenSet a timer to call the function recursively after 2 millisecond delayEnd.arrow_forwardWrite a program in java that will continue to prompt the user for numbers, storing them in an array, until they enter "Done" to finish, then prompts the user for a file name so that these values can be saved to that file. For example, if the user enters "output.txt", then the program should write the numbers that have been read to "output.txt".arrow_forwardI am having an issue with this program, I keep getting the number 15 everytime I type in a code. There is also the instructions for the module itself. //PSEUDOCODE //Write a program that prompts the user for a binary number //(from 3 to 8 bits) as a String and converts it to base-10 decimal value //There are several ways to do this in Java but your program must use a for loop and first principles to perform the conversion //Print the base-10 number when the loop ends public static void main(String args[]) { long sum = 0; System.out.println("Enter a binary number: "); Scanner scan = new Scanner(System.in); String s = scan.next(); long result = 0; for (int i = 0; i < s.length(); i++) { result = (long) (result + (s.charAt(1) - '0') * Math.pow(2, s.length()- i - 1)); scan.close(); } System.out.println(result); }}arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education