
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
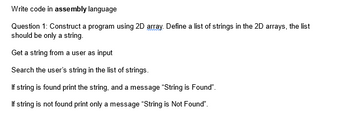
Transcribed Image Text:Write code in assembly language
Question 1: Construct a program using 2D array. Define a list of strings in the 2D arrays, the list
should be only a string.
Get a string from a user as input
Search the user's string in the list of strings.
If string is found print the string, and a message "String is Found".
If string is not found print only a message "String is Not Found".
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 4 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Code following instructions using pyhton: 1. Write a function that accepts a list as an argument (assume the list contains integers) and returns the total of the values in the list 2.Draw a flowchart showing the general logic for totaling the values in a list. 3.Assume the names variable references a list of strings. Write code that determines whether 'Ruby' is in the names list. If it is, display the message 'Hello Ruby'. Otherwise, display the message 'No Ruby'.arrow_forward1 - Write a Python function that will do the following: 1. Ask the user to input an integer that will be appended to a list that was originally empty. This will be done 5 times, meaning that when the input is complete, the list will have five elements (all integers). a. Determine whether each element is an even number or an odd number b. Return a list of five string elements "odd" and "even" that map the indexes of the elements of the input list, according to whether these elements are even or odd numbers.For example: if the input sequence is 12, 13, 21, 51, and 30, the function will return the list ["even", "odd", "odd", "odd", "even"].arrow_forwardplease solve in python and give code. thankzzarrow_forward
- Implement the following function: Code should be written in python.arrow_forwardUsing C++ Language Write a program to implement the following: • Declare two C-strings str1 and str2 of appropriate sizes. • Use strcpy() to copy the string “Hello World.” into str1 • Using a suitable message, read the user input into str2. The user may enter more than one word. • Determine and store the length of both char arrays using strlen() • Check if both char arrays are the same length using the stored lengths o If they are the same length, tell the user they are the same length o If they are not the same length, tell the user the strings are different and end the program using a return statement. • Compare both strings using strcmp to check if they are the same string. o If they are the same string, inform the user of this o If they are not the same string, inform the user of this o Note that you compare only if they are of the same length, hence the return statement in the earlier step.arrow_forwardpython LAB: Subtracting list elements from max When analyzing data sets, such as data for human heights or for human weights, a common step is to adjust the data. This can be done by normalizing to values between 0 and 1, or throwing away outliers. Write a program that adjusts a list of values by subtracting each value from the maximum value in the list. The input begins with an integer indicating the number of integers that follow.arrow_forward
- Review the Wireshark TCP data flow shown here: Host A -- SYN --> Host B Seg =0 Ack = 919412342 Host A Host B Seq = 1 Ack = 1 Host A PSH, ACK Len: 512 --> Host B Seg = 1 Ack = 1 --- Host A Host B Seg = 901 Ack = 1342 --- Host A Host B Seq = 901 Ack = 2992 --- Host A <--- ACK Len: 1452 --- Host B Seq = 2992 Ack = 901 Which of the following statements is correct and represents the next appropriate acknowledgment from Host A? C. Sequence number 4444, Acknowledgment number 901 Selected Answer: Answers: A. Sequence number 2993, Acknowledgment number 901 B. Sequence number 901, Acknowledgment number 2993 C. Sequence number 4444, Acknowledgment number 901 Activate D. Sequence number 901, Acknowledgment number 4444 Go to Settiarrow_forwardUsing c++ Contact list: Binary Search A contact list is a place where you can store a specific contact with other associated information such as a phone number, email address, birthday, etc. Write a program that first takes as input an integer N that represents the number of word pairs in the list to follow. Word pairs consist of a name and a phone number (both strings). That list is followed by a name, and your program should output the phone number associated with that name. Define and call the following function. The return value of FindContact is the index of the contact with the provided contact name. If the name is not found, the function should return -1 This function should use binary search. Modify the algorithm to output the count of how many comparisons using == with the contactName were performed during the search, before it returns the index (or -1). int FindContact(ContactInfo contacts[], int size, string contactName) Ex: If the input is: 3 Frank 867-5309 Joe…arrow_forwardexercise5.py 1 Your code goes here... Guide Collapse Strings -> Coding Exercises - Strings Exercise 5 Exercise 5 Problem Write a program that captures input from the user. Then, swap the letters two at a time in the string. The first two characters change places, the third and fourth characters change places, etc. Assume that the user will only input strings with an even number of characters. Important, do not put a prompt when asking for user input. Just use input(). Adding a prompt will cause your program to not pass the tests. Expected Output • If the user inputs home, then the output is ohem . If the user inputs cars then the output is acer Code Visualizer TRY IT Reminder, do not put a prompt when collecting user input. Just use input() Check It! (1 left) TTTarrow_forward
- Python EXERCISE 1. GENERATING AND PLOTTING A FUNCTION 1. Generate a list or ndarray of values from 0 to 4 with a spacing of 0.1 2. Calculate and plot the function x²-x² 635 025 020 015 630 005 0:00 00 laarrow_forwardSimple Python Coding Exercise Code your program according to the following algorithm 1. Prompt the user for a string of words on one line separated by spaces.2. Convert the input string a list of words called input_list. (Hint: use split())3. Create a new empty list called output_list (i.e., output_list=[])4. Scan input_list to find the smallest word. When the smallest word is found, append that word to output_list and remove it from input_list.5. If input_list still has words in it, go to step 4.6. When input_list is empty, convert output_list into a string of words separated by spaces. (Hint: use join())7. Print the string.arrow_forwardrun the program and please attach the screenshot of the outputarrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education