
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Concept explainers
Question
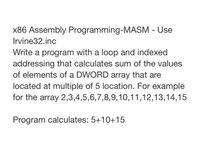
Transcribed Image Text:x86 Assembly Programming-MASM - Use
Irvine32.inc
Write a program with a loop and indexed
addressing that calculates sum of the values
of elements of a DWORD array that are
located at multiple of 5 location. For example
for the array 2,3,4,5,6,7,8,9,10,11,12,13,14,15
Program calculates: 5+10+15
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution
Trending nowThis is a popular solution!
Step by stepSolved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Write an assembly language(intel x86 32bit) program with the following features An array with 10 numbers The program searches for the smallest number in the array The program then prints the number and its position in the arrayarrow_forwardIf in an integer array the base address is 100, what will be memory address of array value at index 4.arrow_forwardIn C#, how would you compile a program that declares a 5 element double array that uses a loop to read values for each element from the user. The program should then use an additional loop to compute and output the sum of the elements in the array.arrow_forward
- Code in C Code in the file IO: /************************************************************* This program prints a degree-to-radian table using a for- loop structure. The results are printed to a file and the the screen. *************************************************************/ #include <stdio.h> #define PI 3.141593 #define FILENAME "tableD2R.dat" int main(void) { /* Declare variables. */ double radians; FILE *fileout; /* Open file. */ fileout = fopen(FILENAME,"w"); if (fileout == NULL) printf("Error opening input file. \n"); else { /* Print radians and degrees in a loop. */ printf("Degrees to Radians \n"); for (int degrees=0; degrees<=360; degrees+=10) { radians = degrees*PI/180; printf("%6i %9.6f \n",degrees,radians); fprintf(fileout,"%6i %9.6f \n",degrees,radians); } /* Exit program. */ }arrow_forwardMASM x86 classarrow_forwardIn c language Consider this array unsigned int data [ ] = { 0xA3A4A5A6, 0x12131415 } write a for loop to print the array values in this order 0x1415 0x1213 0xA5A6 0xA3A4arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education