
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
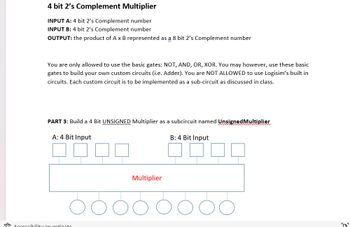
Transcribed Image Text:4 bit 2's Complement Multiplier
INPUT A: 4 bit 2's Complement number
INPUT B: 4 bit 2's Complement number
OUTPUT: the product of A x B represented as a 8 bit 2's Complement number
You are only allowed to use the basic gates: NOT, AND, OR, XOR. You may however, use these basic
gates to build your own custom circuits (i.e. Adder). You are NOT ALLOWED to use Logisim's built in
circuits. Each custom circuit is to be implemented as a sub-circuit as discussed in class.
PART 3: Build a 4 Bit UNSIGNED Multiplier as a subcircuit named Unsigned Multiplier
A: 4 Bit Input
Accessibility: Investigate
Multiplier
B: 4 Bit Input
''
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution
Trending nowThis is a popular solution!
Step by stepSolved in 2 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Need 2 different variations answers and with explanation please. Thank you.arrow_forward4. The following figure shows the four-bit Adder-Subtractor. Your inputs for this combinational circuit are A = 5, B = 6 and M = 1. What is the outputs S3, S2, S1, and S0? You have to show how to get the outputs by indicating each carry bit. (Note: You should show all the steps to receive full credits)arrow_forwardنه Construct the XOR operator using only AND, OR, and NOT gates. Construct the XOR operator using only NAND gates. Hint: xXOR y = (xy)(xy)arrow_forward
- 1. The following figure shows the four-bit Adder. Your inputs for this combinational circuit are A = 3 and B = 5. What is the outputs S3, S₂, S₁, and So? You have to show how to get the outputs by indicating each carry bit. (Note: You should show all the steps to receive full credits) CA A3 FA B3 S3 C3 A₂ B₂ FA S2 C₂ A₁ B₁ FA S₁ C1 Ao Bo FA So Coarrow_forwardPlease send me answer of a,b and c in details and i will give you like sure sir please.arrow_forward4 bit 2’s Complement Multiplier INPUT A: 4 bit 2’s Complement numberINPUT B: 4 bit 2’s Complement numberOUTPUT: the product of A x B represented as a 8 bit 2’s Complement number You are only allowed to use the basic gates: NOT, AND, OR, XOR. You may however, use these basic gates to build your own custom circuits (i.e. Adder). You are NOT ALLOWED to use Logisim’s built in circuits. Each custom circuit is to be implemented as a sub-circuit as discussed in class. PART 1: Build a 4 bit controlled 2’s Complement Inverter as a subcircuit named 4BitInverter PART 2: Build a 8 bit controlled 2’s Complement Inverter as a subcircuit named 8BitInverter PART 3: Build a 4 Bit UNSIGNED Multiplier as a subcircuit named UnsignedMultiplier PART 4: Using the 3 subcircuits you built in Parts 1-3, built a 4 bit 2’s Complement multiplier that uses the inversion method discussed in class. Name this circuit: SignedMultiplier HINTS: INVERSION METHOD: 1) If input A is negative, invert it. If input A is…arrow_forward
- 4 bit 2’s Complement Multiplier INPUT A: 4 bit 2’s Complement numberINPUT B: 4 bit 2’s Complement numberOUTPUT: the product of A x B represented as a 8 bit 2’s Complement number Do this:Build a 4 Bit UNSIGNED Multiplier as a subcircuit named UnsignedMultiplier use AND gate ,full and half adders for the circuitarrow_forwardDesign a combinational circuit using a Decoder and OR gates. The circuit accepts a 2-bitnumber and generates an output binary number equal to the square of the inputnumber.arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education